Security Stays Strong
Nearly 52 percent of solution providers project that the security market will grow at an increased rate over the next 12 to 18 months, while nearly 41 percent said the growth rate will remain steady. Only 3 percent said they expect the growth rate to cool.
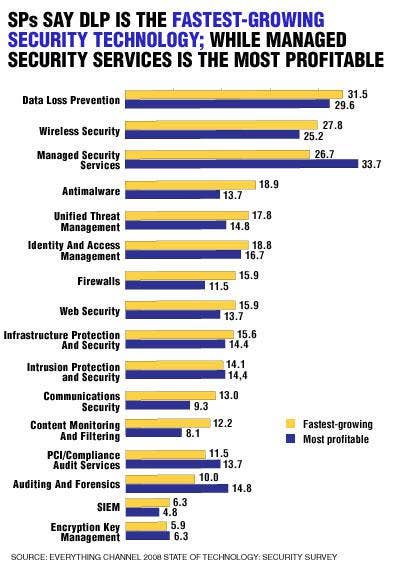
A number of factors are spurring sales of high-end solutions, said solution providers, including customers' desire to avoid data breaches and malware attacks, and regulatory compliance requirements. Solution providers said the fear of data loss and breaches is justifiable, putting it at the top of the list of biggest security threats currently facing customers. Channel partners named sales of data loss prevention as their fastest-growing technology area and as their No. 2 most profitable technology. Following closely on the list of top threats is malware such as Trojans, keyloggers and botnets, with internal threats rounding out the top three.
Another area where solution providers see big opportunity is in the managed security services space. Roughly 44 percent of respondents have seen managed security services growth between 5 percent and 24 percent in the past 12 months, according to the survey. Solution providers named managed security services and Software-as-a-Service as the top two services they plan to add within the next 18 months. VPN services topped the list of managed/hosted security offerings.
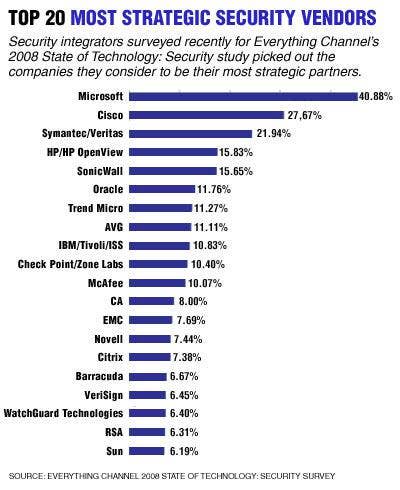
As far as vendors, solution providers chose Microsoft Corp., Cisco Systems Inc., Symantec Corp., Hewlett-Packard Co. and SonicWall Inc. as their top five most strategic partners. Meanwhile, over 88 percent of solution providers said it's more important for security professionals to be knowledgeable in multiple platforms now than it was two years ago.
Next: Data Loss Prevention
DATA LOSS PREVENTION
It's tough for a week to go by without reading a few news headlines about companies losing sensitive data. Whether it's a disgruntled worker stealing digital files or an employee leaving a laptop loaded with customer records in the back seat of a car, there are many ways businesses can get burned by data loss.
So it's no surprise that data loss prevention (DLP) is fast becoming one of the security industry's hottest technologies. Partners responding to Everything Channel's 2008 State of Technology: Security survey selected data loss as the No. 1 security threat today and the No. 2 threat over the next 12 to 18 months. More than two-thirds said they sell DLP products.
For many companies, the fear of making news headlines is reason enough to invest in DLP technologies, such as data recovery and backup, encryption, database security and storage security. But compliance and the threat of shareholder litigation are just as powerful, said Chris Labatt-Simon, president and CEO of D&D Consulting, a solution provider in Albany, N.Y.
DLP is one of D&D's fastest-growing businesses, and the solution provider has created several best-practice solutions for customers to quickly deploy the technology, Labatt-Simon said.
DLP solutions bring VARs healthy product and services revenue. Nearly 30 percent of surveyed VARs expect DLP to be the most profitable technology over the next year, second only to managed security services, and 32 percent think DLP will generate the fastest-growing sales of any technology over the same period.
According to Ryan English, vice president of products and services for Vigilar Inc., an Atlanta-based security solution provider, DLP sales are quite profitable, with deals typically starting at $250,000. "DLP is definitely a very young market, and there's still a ton of opportunity there," he said.
Next: Access Control/Authenication
ACCESS CONTROL/AUTHENICATION
Solution providers looking for a greenfield opportunity will have to get creative in the maturing IT security market, but they could do worse than building an access control/authentication portfolio.
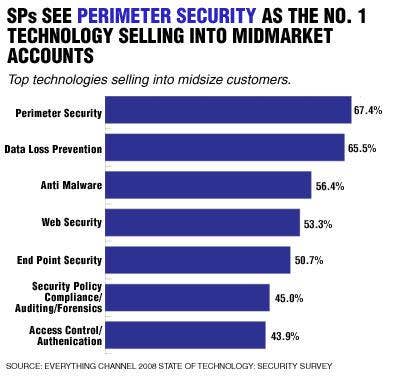
It's a market that seems to be catching solution providers' attention. Only 35 percent of surveyed partners said they currently offer access control products including NAC, identity management and authentication technologies such as password management and biometrics, putting it at the bottom of the list of the top seven technologies currently driving security sales. But when VARs look to the future, access control and authentication technologies topped the list of offerings they plan to add over the next 18 months.
It makes sense. Respondents list data loss/breaches and internal threats as two of the top three security issues their customers face. Controlling who has access to sensitive data is seen as both a profitable and fast-growth IT security arena.
Steve Stratton, vice president at Honolulu-based solution provider Commercial Data Systems Inc., said firms looking to make a move in access control and authentication have an opportunity that's rare in the IT security game: a chance to bring truly innovative new products and services to market.
Stratton, who works closely with the U.S. Department of Defense, said mobility has added a whole new dynamic to access control. That means plenty of opportunities for the channel to develop new solutions.
It's not the size of the business that drives access control and authentication needs but rather the business processes customers use, Stratton added.
Next: Antimalware
ANTIMALWARE
The venerable computer virus remains a top IT security threat and probably the one most recognized by the general public.
The fact is, malware covers a whole lot of nasty territory. Among the most pressing IT security concerns named by survey respondents are such lovely, malware-associated threats as viruses, info-stealing keyloggers, fast flux botnets, Trojans, Zero-day exploits and, of course, the organized cybercrime networks that deploy all of the above.
It's no surprise that antimalware products remain as huge a part of most solution providers' security portfolios as they have for years. But a few new wrinkles have been added to the antimalware story in recent times.
"People are being compromised by drive-by spyware, botnets and malicious sites, in general, all leading to data loss," said Kevin Pouche, COO of IT security firm K logix Corp., Brookline, Mass. "It's a very confusing market right now, and I think the Web is the No. 1 vector that companies are getting hit the hardest by."
Pouche thinks that vendors with a strong focus on Web-based malware proliferation have the brightest future.
One emerging security segment that solution providers said will grow quickly is Unified Threat Management with appliances that pack in multiple security technologies and typically go heavy on antimalware. Pouche called UTM appliances "tailor-made" for small to midsize business, but cautioned against trying to sell larger companies such all-in-one IT security solutions.
"On unified threat management, there can be a false security thing," he said. "I tell my customers, your biggest problem is always going to be your users."
Next: Perimeter Security
PERIMETER SECURITY
No doubt, perimeter security is a staple for any network environment, and channel sales are still going strong. But partners say that perimeter solutions could face some challenging times as security vendors struggle to keep firewalls and other products fresh and competitive.
According to respondents to Everything Channel's State of Technology: Security survey, perimeter security comprises about 20 percent of partners' total product revenue. Meanwhile, at more than 63 percent, perimeter security ranked third on the list of top technologies currently offered by partners.
Yet despite its solid presence in the industry, perimeter security might be facing an uncertain future with a saturated market and lack of truly innovative technologies. Only 11.5 percent of partners maintain that products like firewalls are their most profitable revenue source, and just under 7 percent of partners plan to add perimeter security offerings within the next 18 months.
"The firewall market is very mature, but there's a lot of stuff that firewalls really don't do and protect against," said Peter Bybee, president of Network Vigilance, an IT security and risk management VAR based in San Diego.
As a result, partners say that security vendors must redefine and refresh their perimeter security offerings to stay competitive in a market that has remained stagnant for a while.
"Margins are lower than they were before and vendors have to be more targeted in order to compete," said Robert Koran, vice president of Mark Enterprises Inc., an El Segundo, Calif.-based VAR.
Despite its stagnancy in some of the high-end market segments, growth of perimeter security has significantly outpaced other technologies in the SMB space, particularly as the technology becomes less expensive and easier to install.
In addition, partners also maintain that lower-tiered markets, which once enjoyed a hack-free existence because of their relative obscurity, are also becoming more aware of increasing security threats that could attack their networks and potentially devastate their business.
"Now they can afford it," Koran said. "Before you had best-of-breed of enterprise firewall. Now it's not just a firewall—they're getting a lot more features with their purchase," he said.
Next: Web Security
WEB SECURITY
Web security may not be flashy, but it's still managing to make steady contributions to VARs' bottom lines. Web security products, including Web application security, denial of service prevention, and content filtering are well entrenched. Nearly 46 percent of solution providers responding to the State of Technology: Security survey said they sell them, putting Web security in the list of the top five security technologies currently offered by the channel. However, only 11.3 percent of VARs said they plan to add Web security to their product mix in the next 18 months, and only 14 percent expect it to be their most profitable offering over the next year.
According to the survey, solution providers that currently sell or plan to add Web security products to their portfolios in the next 18 months expect to see the strongest demand from small and midsize businesses with between 100 and 499 employees. However, VARs don't see much interest in Web security products in companies with more than 5,000 employees, or from state, local and federal governments.
But while the buzz around Web security isn't as strong as it is around other technologies, the category does account for a lot of replacement business, said Greg Hanchin, a principal at security solution provider DirSec, Centennial, Colo. Demand for content filtering continues to be particularly healthy, and these products currently account for around 20 percent of DirSec's business, Hanchin said. "We still find there are a lot of 500- to 1,000-seat organizations that don't have content filtering, so this is still a good business to be in," he said.
Some VARs said most applications still have large security holes, so the Web security space will continue to be a viable one for the channel.
There's a big push going on right now for application testing, said Andrew Plato, president at Anitian Enterprise Security, a security specialist in Beaverton, Ore.
While content filtering is becoming commoditized, it's still an important technology that needs to be part of every company's security plans, solution providers said. "You cannot have a decent security strategy without some type of Web content filtering," Plato said.
Next: Compliance
COMPLIANCE
Blame it on TJX and Hannaford. While security policy compliance and auditing are still in their infancy as niche technologies, significant growth is expected as customers aim to avoid becoming the next data breach victim.
Across the board, partners said that compliance and auditing products and services have become increasingly important to customers as regulatory compliance deadlines loom and data breaches become an everyday occurrence in the headlines. About 40 percent of partners responding to the survey said compliance and auditing tools are one of the top products fueling sales, placing it sixth on the list of technologies currently offered by the channel.
And partners say that number could grow. Nearly 13 percent of partners surveyed said that they plan to add security compliance and auditing tools to their portfolio of offerings within the next 18 months, making it the second most popular technology area the channel plans to enter in the near future.
A possible reason for this upward growth trend in security compliance could be that more auditing tools are already baked into myriad security products.
"Most of this is being fueled by the appliances that are doing more integration with [Microsoft's] Active Directory. It's made it easier for us to be able to hook in everybody in the company," said Roy Miehe, CEO of AA Antivirus, a security VAR based in Campbell, Calif.
Miehe said that despite impending compliance deadlines, he hasn't seen a high interest in compliance tools from customers.
Other partners echoed the idea that demand for auditing and compliance tools has actually waned, despite the rash of data breaches in the headlines and the abundance of regulatory compliance deadlines—an assertion corroborated by the fact that just 11 percent said they view compliance and auditing as the fastest-growing technology area. And of the security products on the market, only 13 percent of partners say that security compliance and auditing are currently their most profitable offering.
One partner said that lag could be due, in part, to a growing awareness from customers who are already finding ways to meet their compliance objectives.
"A couple years ago, it was scaring a lot of people. The knowledge wasn't there, the deadlines were looming but they didn't know what compliance meant," said Eric Anderson, CTO of Netanium Network Security Inc., an information security consulting partner based in North Chelmsford, Mass. "They now know what their deadlines are. They know what they have to do to meet them. A lot of the craziness has subsided. There's not as much kneejerk."
Meanwhile, partners also maintain that the modest statistics could likely change in the near future as security threats become more sophisticated and target a wider array of market segments. "There's no doubt in my mind, the companies are going to have to start spending money," Miehe said. "The hackers out there, the virus writers and malware writers have gotten so good—they can sneak it through e-mail and an open port and get it to you."
Next: End Point Security
ENDPOINT SECURITY
Endpoint security tools such as antiphishing, antispam and communications security continue to give VARs a financial edge, according to the Everything Channel State of Technology: Security survey.
According to the results, 47 percent of solution providers said endpoint security tools are the top security products that fuel sales, putting endpoint security products fourth just behind data loss prevention products, antimalware and perimeter security.
But despite endpoint security being a sales catalyst, it still has a ways to climb. Just 11 percent of respondents said they plan to add an endpoint security product offering to their arsenal over the next 18 months.
Other facets of endpoint security are gathering steam. Communications security, for example, is creeping up and generating growing sales, with 13 percent of solution providers indicating they expect communications security to grow fastest in the next year. Another 9.3 percent of solution providers said they see communications security becoming the most profitable in the next month. Meanwhile, nearly 15 percent said unified threat management, which typically includes some endpoint security features, will become more profitable within the year.
The expected growth potential for endpoint security over the next 12 to 18 months will be most dominant in small to midsize companies of 100 to 499 employees, with about 38 percent of VARs that serve that market noting it has the greatest growth potential, the highest for companies of that size. Endpoint security also shows strong growth potential in small companies of 20 to 99 employees and midsize to large companies of 500 to 999 employees.
Solution providers' plans for endpoint security solutions could be attributed to the evolving threat landscape targeting devices. For example, 37.5 percent of VARs said phishing/social engineering is the biggest security threat now, and 27 percent of solution providers feel it will remain the largest security threat within the next 12 to 18 months. Vishing, social engineering that utilizes VoIP, is also gaining some recognition, with 9 percent of solution providers predicting it will be a huge threat in the next year to 18 months.
Ladi Adefala, security practice manager for World Wide Technology Inc., a St. Louis-based solution provider, said the evolving threat landscape, along with other factors, are contributing to the growing interest in endpoint security.
"Solution providers are still enjoying the revenue growth and profitability in this area because these solutions typically tie back into other infrastructure pieces, which gives visibility to other customer needs and initiatives."
Next: Services
SERVICES
Managed security services are set to explode, according to Everything Channel's State of Technology: Security survey.
That's not to say that solution providers weren't already finding great success with services in general. Deployment and installation topped the list of security services solution providers are currently offering, followed closely by network security assessments. Wireless security assessments, security architecture and managed security services round out the top five.
Within the next 18 months, 15.5 percent of solution providers will add managed security services to their roster, the top planned addition. Plus, nearly 27 percent of solution providers indicated that over the next year, managed security services will produce the fastest-growing sales.
Security solution providers also said managed security services will generate the strongest profits in the next year, with nearly 34 percent citing them as having the potential to be the most profitable. And the proof is in the pudding: Solution providers said margins from managed security services and security Software-as-a-Service (SaaS) have grown from 29.8 percent last year to 34.9 percent now.
Overall, respondents said they generate more revenue from security services than they do security products, with 57 percent of revenue coming in from services. More than 35 percent of solution providers also noted that managed security services offer the highest returns among high-end solutions.
Despite the positive outlook, however, survey results indicate managed security services have a ways to go. Currently, they make up 19.5 percent of security services revenue, trailing other security services. Regardless, nearly 52 percent of respondents said the security market will grow at an increasing rate, which is already evidenced in the managed security services or security SaaS spaces. Since 12 months ago, just over 12 percent of solution providers said their managed security or security SaaS client base has grown 100 percent or more, while 22 percent said their services client base in those areas grew 10 percent to 24 percent.
Gary Cannon, president of Advanced Internet Security Inc., a Colorado Springs, Colo.-based solution provider, said his company is looking into managed security services, mostly in response to the potential revenue and margins. Cannon said the time is right to build a managed security services practice.
"We are seeing that there are increased margins," he said. "Years ago, it wasn't worth the level of effort and all of the work it took to offer managed services. But now with increased margins, we're investigating it again and looking into programs that would fit."
Advanced Internet Security deals mostly in the midmarket, an area Cannon said benefits most from a managed services offering. Smaller companies, he said, have small IT staffs that struggle to handle all of the requirements, and security has a lot of moving parts that make it more complicated in the midmarket. "People don't have the time to devote themselves to all of the security they need to deploy," Cannon added.
—Stefanie Hoffman, Kevin McLaughlin, Damon Poeter, Andrew R. Hickey and Jennifer Hagendorf Follett contributed to this report.