Palo Alto Networks Launches XSIAM 2.0: The Key Updates
With the second generation of the AI-driven security operations platform, Palo Alto Networks has improved visibility and added support for custom machine learning models, an executive tells CRN.

Just over a year after its release, Palo Alto Networks’ AI-driven security operations offering, XSIAM, is on track to be its fastest-growing product to date. Now, the cybersecurity giant is looking to keep up the momentum with the unveiling of the second generation of XSIAM (extended security intelligence and automation management).
With XSIAM 2.0, Palo Alto Networks is not delivering a major overhaul because it doesn’t need to, given the success of the product since its debut in October 2022, according to Gonen Fink, senior vice president of Cortex products. But the company does have a number of major improvements that partners and customers should benefit from, including around the user experience and support for custom machine learning (ML) models.
“We did not rewrite the product,” Fink said in an interview with CRN. “It was working very well, but we put in additional visibility to [show] what it’s doing for you.”
[Related: Cisco-Splunk Will Face Huge Challenge Vs. Palo Alto Networks: Analysis]
The updates come as Palo Alto Networks reports strong traction around displacing existing providers of SIEM (security information and event management) technologies, and with Cisco planning to acquire SIEM stalwart Splunk for $28 billion.
Since the launch of XSIAM, the “autonomous SOC” (Security Operations Center) platform had more than doubled Palo Alto Networks’ goal for its first year — surpassing $200 million in bookings — in just three quarters, the company said in August.
“We really feel we hit a very, very important problem with a very strong technology that combines AI and automation to really shift the way security operations are done,” Fink said.
XSIAM leverages Palo Alto Networks’ deep expertise in AI and machine learning for security — as well as its massive trove of cybersecurity data — which put together are unmatched by other vendors, said Shailesh Rao, president of Palo Alto Networks’ Cortex business, in a recent interview. The results are dramatically improved outcomes for cybersecurity and a compelling replacement for SIEM, he said.
“We have seen customers transition from their existing SIEM over to XSIAM,” Rao said. “We’re starting to see that already.”
And while the initial target customers for XSIAM are large organizations with mature SOC and data science teams, the product does have the potential to meet the needs of a wider range of customers over time, according to Fink. This includes midmarket companies, where service providers might utilize XSIAM to develop customized solutions for the customers, he said.
What follows are the key updates to know about with Palo Alto Networks’ launch of XSIAM 2.0.
XSIAM Command Center
From the start with XSIAM, one of the things customers have appreciated is how the product improves their understanding of what’s actually going on in the SOC environment, Fink said.
“Traditional tools in the SOC were very complicated — you had multiple monitors and screens,” he said. “And the reality is that none of them actually provide you a comprehensive view of what the system is doing.”
With the debut of XSIAM 2.0, Palo Alto Networks is introducing further improvements to this visibility for partners and customers through the launch of the new XSIAM Command Center.
The Command Center provides a single view of all activities within an organization’s SOC — from the data ingestion and analytics to rule creation and alert detection, according to Fink.
XSIAM Command Center also shows how detections are being grouped into incidents, as well as the automated response and remediation that is taking place to address those incidents, he said.
“This is becoming the one screen that you’re using to understand what’s going on in your environment,” Fink said.
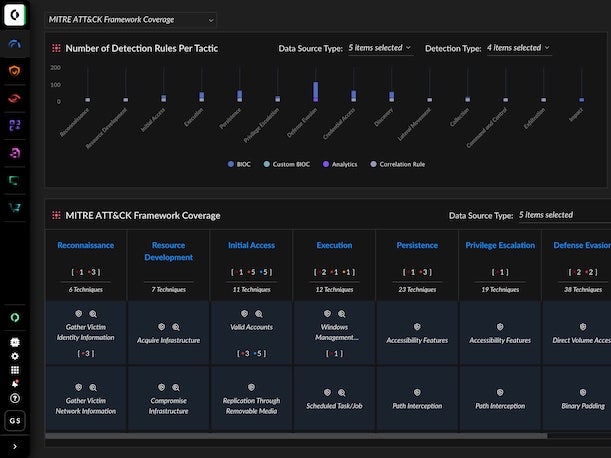
MITRE ATT&CK Coverage Dashboard
Another enhancement to visibility that’s arriving as part of XSIAM 2.0 is the new MITRE ATT&CK Coverage Dashboard, Palo Alto Networks said.
MITRE ATT&CK has become the standard framework used to describe the stages of typical cyberattacks, as well as many of the common tactics and techniques utilized by threat actors. The framework is used widely within the cybersecurity industry, since it allows vendors to show how their products can be used to address specific stages or techniques of an attack.
“Today, customers are measuring their protection against that,” Fink said. “You need to actually know how well you’re protected, based on the different data sources that you’re ingesting.”
From its inception, XSIAM has already come with numerous out-of-the-box detections, so that customers don’t have to write their own rules, he noted. From there, the offering uses machine learning to adapt to the evolving techniques of adversaries, Fink said.
With the new MITRE ATT&CK Coverage Dashboard in XSIAM 2.0, Palo Alto Networks is providing visibility around how well a customer is covered against each of the different elements of the framework, he said.
“That’s very powerful,” Fink said. In addition to showing how real-world protections are aligning to the ATT&CK framework, the new dashboard also helps customers to “for the first time understand what is in XSIAM,” he said.
“The fact that XSIAM comes with built-in detection and machine learning models — thousands of AI-based detections for the various aspects of the MITRE framework — it’s part of what customers buy this for,” Fink said. But now with the new ATT&CK Coverage Dashboard, “customers are actually seeing them,” he said.
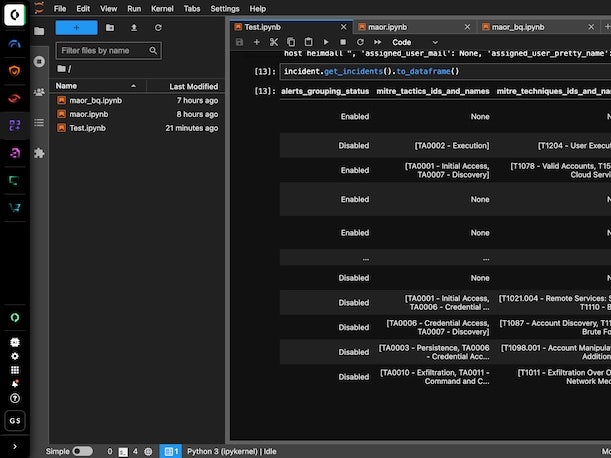
Bring Your Own ML
XSIAM 2.0 also introduces the new capability to “Bring Your Own ML” to the platform, Palo Alto Networks announced.
That means that partners and customers are now longer required to replicate their data into another data lake in order to utilize their own custom ML models, the company said.
Bring Your Own ML is primarily aimed at large customers that have unique needs as well as data science capabilities, Fink said. Additionally, third-party service providers can now use XSIAM to deliver specialized tools or services to their clients — particularly in areas that aren’t directly covered by XSIAM, such as fraud detection for instance, he said.
Other Updates
XSIAM 2.0 includes a number of additional improvements, as well, such as a new in-product assistant that provides easier access to product help and documentation.
The new release also delivers enhanced protection and detection through the introduction of several modules — including for early detection of macOS ransomware, Kubernetes and master boot record threats, according to the company.
Other updates include NDR (network detection and response) coverage, “advanced” local analysis for macOS and Linux, a simplified text search system and additional attack surface management policies.
Availability
XSIAM 2.0 is generally available now for partners and customers, according to Palo Alto Networks.
Ultimately, Fink noted that XSIAM’s AI-driven approach is not intended to replace human intervention or expertise, but instead to automatically resolve the vast majority of incidents and enable analysts to focus on the most-critical threats.
“Cyber analysts and cyber experts can actually focus on and quickly respond to those things that require human intervention,” he said. “The results have been simply amazing.”
https://main--crn--thechannelcompany.hlx.page/authors/kyle-alspach
https://main--crn--thechannelcompany.hlx.page/authors/kyle-alspach