10 Hot New Cloud Security Products Announced At RSA 2018

Securing Data No Matter Where It Resides
Vendors attending the 2018 RSA Conference have rolled out products that smooth over the differences between public cloud and on-premises from a security standpoint, providing stronger visibility and protection for applications and data on Amazon Web Services, Microsoft Azure and Google Cloud.
The investments, though, go well beyond the public cloud. Companies are hard at work adding additional layers of security around everything from Microsoft SharePoint and OneDrive to Software as a Service and cloud sandboxing.
Here’s a look at what 10 major players are doing to address who can access company applications and data in the cloud.
Kaspersky Hybrid Cloud Security
Kaspersky Hybrid Cloud Security protects applications and data in physical, virtual and cloud workloads. The offering provides API-based integration with AWS and supports the Microsoft Azure cloud platform.
Kaspersky Hybrid Cloud Security streamlines and automates response to advanced cyberthreats, while delivering full visibility and manageability across the entire hybrid cloud environment. This provides IT security teams with full control over those who can access corporate data on-premises and in the cloud.
The offering provides customers with machine learning-assisted protection, allowing security systems to catch, block and remediate potential threats before they harm businesses. By leveraging exploit prevention, vulnerability assessment and automated patch management, the product ensures attackers can’t leverage flaws in legitimate popular software or compromise corporate data in the cloud.

SonicWall Capture Cloud Platform
The SonicWall Capture Cloud Platform tightly integrates security, management, analytics and real-time threat intelligence across the company’s portfolio of network, email, mobile and cloud security products.
Machine-learning algorithms are used to analyze data and classify and block known malware before it can infect the network. Unknown files are sent to the SonicWall Capture Cloud Platform, where they are analyzed using hypervisor analysis, emulation and virtualization technology, blocking zero-day malware in near-real-time.
One of the cornerstones of the platform is the SonicWall Capture Security Center, which allows for the governing of SonicWall's security operations and services from a single pane of glass.

Pulse Secure Appliance
The latest cloud-based Pulse Secure Appliance allows enterprises to address changing application environments that blend together data center, IaaS and SaaS offerings.
By using an adaptable access security framework, Pulse Secure helps enterprises move applications to the cloud and leverage IaaS and SaaS to reduce operational costs and expedite new end-user services. The new appliance extends proven data center security policies to applications hosted by AWS and Microsoft Azure.
The Pulse Secure Appliance is designed to meet the access challenges of any enterprise with appliances that scale from 200 to 25,000 concurrent sessions and form factors that accommodate data center, office and cloud environments.

Gigamon GigaSecure Cloud for Microsoft Azure
GigaSecure Cloud enables organizations with mission-critical applications deployed in Microsoft Azure to acquire, optimize and distribute selected traffic to security and monitoring tools, ensuring business-critical data in the cloud is protected and monitored by security operations.
GigaSecure Cloud's centralized platform complements security monitoring of all Azure virtual networks by acquiring and sending the right data to the right security tools. Tight integration with Azure APIs, meanwhile, enable the platform to automatically detect changes in Azure Virtual Networks.
The security tool's performance is optimized through the generation of summary flow records from network traffic, which helps determine IP source, destination of traffic, class of service, and causes of congestion.

Fidelis Elevate
The latest release of the Fidelis Elevate platform can protect cloud assets by deploying and managing deception defenses in cloud environments. By creating active decoys that mimic an organization’s critical cloud assets and luring attackers to the deception environment through breadcrumbs placed on real assets, organizations can ensure a strong first line of defense on-premises and in the cloud.
The product continually analyzes internal network traffic and automatically adapts decoys to match an organization’s network and cloud environment as changes occur. Organizations can self-manage deception defense in the cloud or have Fidelis manage it for them, reducing their investment in on-premises infrastructure.
The Fidelis Elevate platform includes Fidelis Deception, Fidelis Network and Fidelis Endpoint, all of which are available on-premises or in the cloud.

Tripwire Cloud Management Assessor
Tripwire Cloud Management Assessor now features file integrity monitoring capabilities for addressing publicly exposed data in the cloud, and its core secure configuration management functionality now supports all major cloud providers, including Google Cloud Platform.
Tripwire file integrity monitoring capabilities allow organizations to discover publicly exposed cloud instances. In light of several recent incidents where sensitive information was mistakenly left exposed on cloud servers, Tripwire Cloud Management Assessor can be used to ensure buckets are properly configured and data is kept secure.
These capabilities currently cover AWS S3 and Azure Blob and provide change monitoring of files stored in the cloud. They also provide alerts to public-facing files and flag suspicious or unauthorized changes.

Qualys CloudView
CloudView delivers topological visibility and insight about the security and compliance posture of customers' public cloud infrastructure for major providers including AWS, Microsoft Azure and Google Cloud.
The product discovers and tracks instances, virtual machines, storage buckets, databases, security groups, Access Control Lists, Elastic Load Balancers and users across multiple regions, accounts and cloud platforms in one central place.
CloudView also powers asset searches to help teams discover their threat posture based on attributes and relationships. It lets them find leaky storage buckets, ungoverned instances, as well as those scheduled for retirement.
Complex lookups, meanwhile, allow teams to identify assets that are at greater risk of attack, such as those that have high-severity vulnerabilities or that exist at the edge.

Untangle Firewall-as-a-Service
Untangle updated its next-generation firewall, making it possible for customers to deploy it in AWS as part of a bring-your-own-license model.
The product moves the network security processing and traffic analysis normally done by an on-premises, next-generation firewall or unified threat management system to the cloud, changing budgeting requirements from Capex to Opex. It offers rapidly scalable performance not limited by on-premises hardware, thereby enabling flexible capacity for changing environments.
The next-generation firewall can be deployed as software on a customer’s on-premises hardware, as a hardware or virtual appliance, or in the public cloud, ensuring a consistent security posture, administrative experience, and complete visibility regardless of deployment type.

Egnyte Protect
Egnyte Protect allows businesses to classify and monitor content across Windows File Servers, SharePoint and OneDrive, making it possible for customers to create classification policies, and enabling real-time policy violation and alert notifications.
Egnyte Protect and Microsoft customers can now centrally manage all the content that lives across multiple Microsoft environments, protecting content without sacrificing productivity.
Egnyte Protect is built from the ground up to help businesses comply with strict industry regulations like GDPR, HIPAA and PCI-DSS. The product allows businesses to monitor the exposure of sensitive data by identifying pre-defined markers such as personally identifiable information and empowering customers to properly quarantine the content to avoid fines or sanctions for noncompliance.
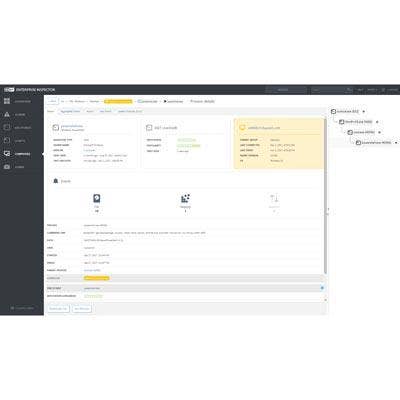
Eset Dynamic Threat Defense
Eset Dynamic Threat Defense provides off-premises cloud sandboxing, which leverages machine learning and behavior-based detection to prevent zero-day attacks.
All of Eset’s enterprise solutions integrate seamlessly into a single pane of glass and allow for visibility into threats like zero-days, APTs and botnets. But the use of machine learning to automate decisions and evaluate possible threats is only as strong as the people who stand behind the system, the company said.
Human expertise is paramount in providing the most accurate threat intelligence possible due to threat actors being intelligent opponents. Eset’s endpoint products contain a cloud reputation system that feeds relevant information about the most recent threats and benign files.