CRN’s 2021 Products Of The Year
CRN staff compiled the top partner-friendly products that launched over the past year, then turned to solution providers to choose the winners.

The Best Of The Best
Our 2021 Products of the Year awards honor the leading partner-friendly products that launched over the past year—as chosen by the solution providers who are on the front lines of bringing these products to customers. To get things started, our editors selected product finalists in 30 technology categories among offerings that were launched or updated from September 2020 to September 2021. The categories ranged from AI and big data solutions, to cloud and collaboration platforms, to security, storage and devices. We then asked solution provider partners to choose winners based on how the products rate on technology, revenue and profit opportunities, and customer need.
The survey received more than 5,000 product ratings from solution providers, and the product receiving the highest overall score in each category was named the winner. Notably, five companies took home multiple top prizes in this year’s contest: HPE Aruba, Cisco and Microsoft had three category wins each, while HP Inc. and IBM each had two category wins.
What follows are the winners and finalists in CRN’s Products of the Year awards for 2021.
APPLICATION PERFORMANCE MONITORING
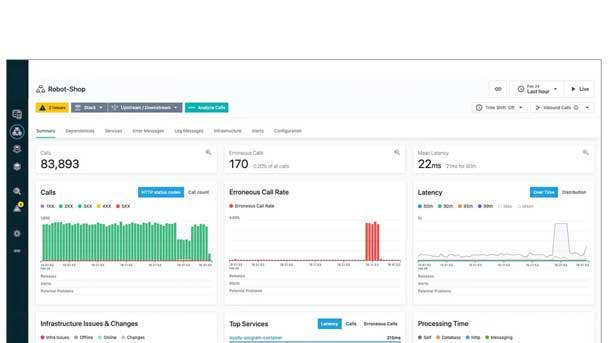
IBM OBSERVABILITY BY INSTANA APM
WINNER: OVERALL
With IBM’s acquisition of application performance monitoring provider Instana in December 2020, the company has made the IBM Observability by Instana platform available for enabling robust enterprise application performance monitoring. The offering is designed to manage microservices and cloud-native applications in multiple environments, including hybrid cloud and bare-metal machines, and provides a domain-specific AI engine to speed up issue resolution and improve event management. IBM also recently rolled out the ability to remotely monitor multiple IBM instances on the platform, a capability that supports agents including Linux, Windows and Unix OS on AIX. In addition, IBM has enabled inspection for nine additional languages and expanded Instana Host Agent installation to different Red Hat OpenShift configurations.
Finalist: AppDynamics
Cisco’s AppDynamics launched its Secure Application offering this year to simplify vulnerability management and protect against attacks in real-time. AppDynamics also announced an integration between Dash Studio and ThousandEyes, another Cisco solution, to give IT teams one place to visualize performance data for end users, hybrid cloud and the internet.
Finalist: Datadog APM
Datadog expanded its APM offering to connect Python and Node.js Lambda functions to AWS managed services in one trace, even if a request triggers multiple functions and servers. The company also released an extension for Azure App Service that allows users to capture request traces from .NET Azure web apps automatically and allows users a single platform to correlate APM data with logs. Datadog also introduced automatic faulty deployment detection and request flow mapping.
Finalist: New Relic One
Recently added features for the New Relic One observability platform include a new network performance monitoring feature and ways for users to remove monitoring gaps in Kubernetes environments. The company also updated the platform’s dashboards with more visualization options, reduced loading time and ways to bring over visualizations from other parts of the platform.
Finalist: Splunk Observability Cloud
Splunk recently launched its Observability Cloud to give users a full-stack, analytics-powered, enterprise-grade solution for APM, real user monitoring, infrastructure monitoring and log investigation. The APM feature gives users insights into cloud-native, microservice and monolithic apps, along with visibility into performance and trace data on any cloud and existing infrastructure.
ARTIFICIAL INTELLIGENCE – ENTERPRISE PLATFORM
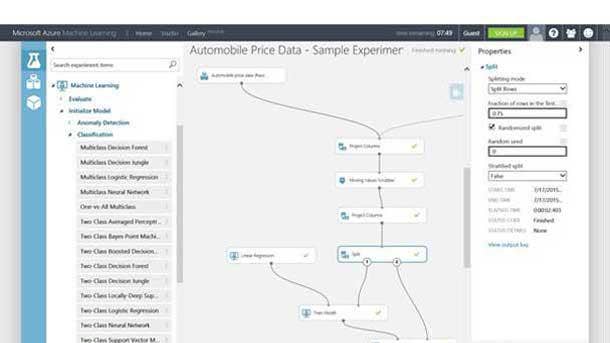
MICROSOFT AZURE MACHINE LEARNING
WINNER: OVERALL
Microsoft’s Azure Machine Learning platform offers enterprise-ready machine learning services that can be used to build models at significant scale. Azure Machine Learning supports large-scale distributed training and inference on CPU and GPU clusters, complete machine learning operations life-cycle automation, reproducible pipelines and data drift detection—as well as continuous integration and continuous delivery, comprehensive security and collaborative notebooks. Microsoft recently updated Azure Machine Learning to improve cross-location computing, enabling greater space efficiency and virtual machine SKUs for specific regions while removing the need for manual creation of individual models to produce hierarchy data forecasts.
Subcategory Winner—Revenue and Profit, Technology: Amazon SageMaker
SageMaker is Amazon’s tool to help machine learning engineers and data scientists build and operate models for business processes. Recent updates include giving users the option to explicitly list execution steps and the new support for registering and deploying inference pipelines with the model registry.
Subcategory Winner—Customer Need: Google Cloud Vertex AI
Google’s Vertex AI tool aims to help engineers build, deploy and scale ML models faster with pre-trained and custom tooling. Recent updates for the tool include expansion to the South Carolina region and general availability of access transparency, using VPC Service Controls, setting up VP Network Peering and using customer service accounts for custom training and prediction.
Finalist: HPE Ezmeral
Ezmeral from Hewlett Packard Enterprise brings cloud-native analytics and data lakehouse services to one platform. This year, HPE made Exmeral Data Fabric available as a standalone offering and a new technology ecosystem program and marketplace for offerings from independent software vendors.
Finalist: IBM Watson Studio
IBM’s tool to build and scale artificial intelligence on any cloud received several updates this year, including new job notifications and job retention support, the ability to add user groups as a collaborator in an analytics project and new connections to SQL Query, databases for MongoDB and Microsoft Azure File Storage.
BIG DATA
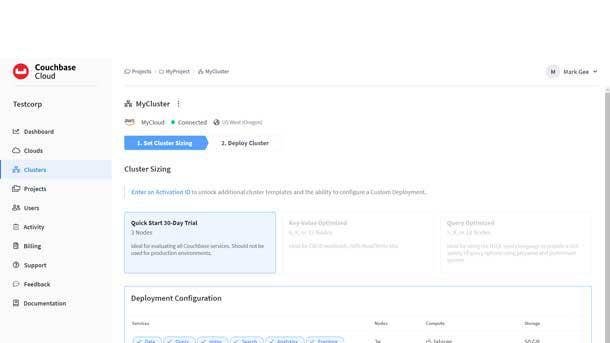
COUCHBASE CAPELLA
WINNER: OVERALL
Couchbase Capella, previously known as Couchbase Cloud, is a Database-as-a-Service offering that’s recently gained broader usability by becoming available for Microsoft Azure deployment. Couchbase recently made its Cloud API generally available with the goal of simplifying automation, enhancing data import functionality and improving the in-product support user experience. The company also made its full-text search indexes more available through a new ability to configure replicas with the control plane.
Finalist: Databricks Lakehouse Platform
The Databricks Lakehouse Platform unifies data, analytics and artificial intelligence workloads, with a recent update extending availability to Google Cloud. Databricks also announced a public preview of the Photon query engine on the Lakehouse Platform to coordinate work and resources and accelerate SQL and Spark queries.
Finalist: MariaDB SkySQL
Recent announcements for MariaDB SkySQL include a new partnership with Amazon Web Services to bring MariaDB SkySQL to the AWS cloud and make its Xpand distributed SQL database generally available in SkySQL, improving throughput and lowering latency.
Finalist: Oracle Autonomous Database
Oracle launched new self-service graph modeling and graph analytics capabilities, an AutoML no-code user interface and extended ability to query data in all popular cloud object stores with three new data lake capabilities as part of updates this year to the Autonomous Database suite of products.
Finalist: Snowflake Data Cloud
Among the features Snowflake rolled out this year to users of its Data Cloud are cloning performance improvements; an access history feature to see who queried which tables, views and columns in Snowflake; and connectivity to Snowflake internal stages using AWS PrivateLink.
BUSINESS INTELLIGENCE AND ANALYTICS
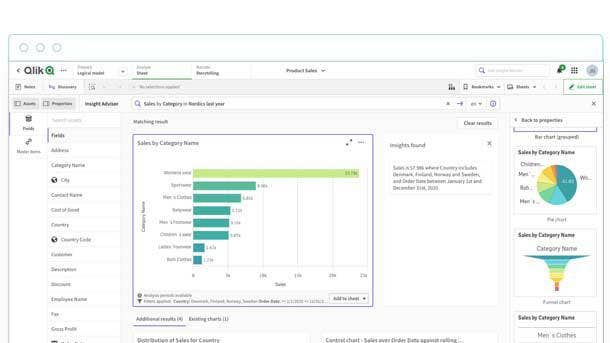
QLIK SENSE
WINNER: OVERALL
A provider of end-to-end business analytics and data integration software, Qlik’s flagship offering is the Qlik Sense self-service discovery, analytics and visualization platform. Recent enhancements to Qlik Sense have included additional functionality for the platform’s AI assistant, Insight Advisor, such as a new chat experience that uses natural language processing and natural language generation in order to better understand and respond to the user. Insight Advisor can also now be customized by users through the creation of business rules and metadata. Other new
features for Qlik Sense have included Collaborative Notes, which enables collaboration on analytics processes for a distributed team, and Hybrid Data Delivery, which allows data sets to be updated automatically as data sources change.
Subcategory Winner—Technology (tied with Qlik Sense): Tableau
Recently added Tableau features include Augmented Analytics, which offer AI-driven analytics that enable a user to interact with data inside their usual work context. Key capabilities include automated modeling and natural language queries, allowing users—even if they’re new to analytics—to discover insights from data.
Finalist: Looker 21
For its Looker 21 business intelligence platform, Google Cloud recently added support for Microsoft Azure hosting—creating a more-flexible environment. Other updates have included a new developer portal, which consolidates Looker’s developer resources including documentation, tutorials, sample code and examples.
Finalist: Microsoft Power BI
Recent Microsoft Power BI updates have included an analytics reports integration with Jupyter Notebook, an open-source development tool with documents that have live code, quotations, visualizations and narrative text. Power BI Embedded Analytics allows developers to explore data analytics and generate reports.
Finalist: SAP Business Technology Platform
SAP recently unveiled a number of new planning and data analysis capabilities and enhancements to the SAP Business Technology Platform, the vendor’s application and data integration, data management and data analysis hub. The updates include a data marketplace for SAP Data Warehouse Cloud—allowing organizations to consume, share and monetize data assets—as well as operational workforce planning capabilities and analytics.
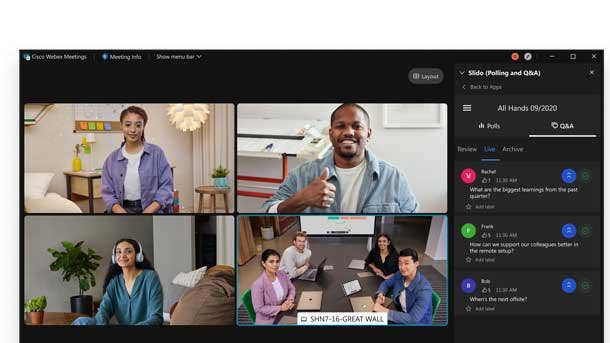
COLLABORATION - ENTERPRISE
CISCO WEBEX
WINNER: OVERALL
With a focus on improving meeting quality and productivity, Cisco Systems has introduced more than 800 new capabilities and features
over the past year for its flagship collaboration platform, Webex. In particular, the Webex platform—which brings together calling, meetings, messaging and events—has seen the addition of numerous features powered by artificial intelligence and machine learning technologies. The recently added AI-driven features include Webex Audio Intelligence and enhanced noise-cancellation technology for improved audio clarity; Gestures, which enables users to communicate non-verbally during meetings without the need for tapping an icon; and Real-Time Translations, which offers live translations from English to more than 100 languages.
Subcategory Winner—Technology: Zoom
Zoom released updates this year aimed at expanding use of its video communications platform—including Zoom Apps, which embeds third-party apps within Zoom Meetings and the desktop client experience, and Zoom Events, which helps with interactive and immersive virtual events creation.
Finalist: Google Meet
Along with a new layout for PC users, Google Meet users received new capabilities this year that include translated captions; the ability to mute all participants at once if hosting on iOS devices; and notifications to see the order and number of raised hands during a meeting.
Finalist: Microsoft Teams
Microsoft recently rolled out enhancements to its Teams collaboration app such as the ability to set automatic mic sensitivity adjustments; a feature to track meeting call quality; and an expansion of the number of available emojis to more than 800.

COLLABORATION – SMB
INTERMEDIA UNITE
WINNER: OVERALL
Intermedia Unite brings voice and videoconferencing together with team chat, contact center and file backup, with a focus on serving the collaboration needs of small and midsize businesses. Recent updates to the Intermedia Unite platform include the debut of new options for integrating Unite with the widely used Microsoft Teams collaboration app. With the Intermedia Unite for Microsoft Teams package, for instance, partners and customers can add Unite’s cloud-based phone system directly into Teams. Meanwhile, Intermedia Unite’s mobile capabilities include the ability for users to place and receive calls from their work number on their mobile device.
Subcategory Winner—Customer Need (tied with Intermedia Unite), Revenue and Profit: 8x8 XCaaS
8x8’s XCaaS (Experience Communications as a Service) offering combines features of unified communications and contact-center-as-a-service into one deployment model. The platform recently gained support for video meetings with up to 500 active participants.
Finalist: Cytracom
Recent Cytracom updates include the ability to merge two calls into a three-way conference from Cytracom Desktop; cleaner playback from call queues; and search-by-phone-number capabilities in the Autotask, HubSpot and ConnectWise apps in Cytracom Desktop.
Finalist: Nextiva Cospace
Designed with a simplified interface, Nextiva Cospace offers video and voice calls, screen sharing, chat and file sharing. The application also allows users to track and schedule tasks for their teams.
Finalist: RingCentral MVP
RingCentral’s MVP (Message Video Phone) cloud phone system includes RingCentral Video, which received a boost this year in video overlay, video virtual backgrounds, breakout rooms, picture-in-picture and other capabilities. Team messaging users also received upgrades to their personal folders, mobile app resource center and how they export message data.
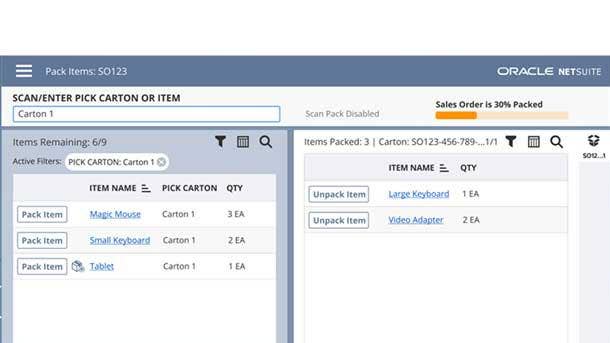
CRM/ERP
ORACLE NETSUITE
WINNER: OVERALL
Recent enhancements to NetSuite -- the Oracle-owned platform for cloud ERP, CRM and e-commerce tools -- have brought a focus on improving automation, efficiency, data analysis and management. New automation capabilities released this year include consolidating purchases across multi-subsidiary organizations, generating vendor payments from a single location, email approval for transactions and SuiteCommerce webstore pages, and the ability to add featured blogs to SuiteCommerce sites. SuiteAnalytics Workbooks gained native language support and new integrations with SuitePeople to improve employee performance tracking. And new inventory management capabilities have included adding an extra verification step and grouping orders with the same shipping routes.
Finalist: Microsoft Dynamics 365
Updates for Microsoft Dynamics 365 this year have included intelligent order management, which aims to improve business’ omnichannel from orchestration to fulfillment; real-time customer journey orchestration capabilities to build customer loyalty; and further integration with the Microsoft Teams collaboration app for event creation and management.
Finalist: Salesforce
Major features rolled out this year by Salesforce included customizable actions for recently viewed lists, like or dislike question embedding in email templates, as well as AI-powered personalized shopping experiences and new order management return features.
Finalist: SAP S/4HANA
As part of SAP’s updates to its SAP S/4HANA Cloud offering this year, the company rolled out a new end-to-end ERP-like transportation management solution and integrated two-tier-based predictive material and resource planning with scheduling agreement for more effective planning through simulations.
Finalist: ServiceNow Customer Service Management
ServiceNow’s Customer Service Management application received upgrades in 2021 including a way for human agents to temporarily transfer live chat control to a virtual agent; a new wrap up tool for updating record information and posting work notes; and more integrations with Field Service Management, Financial Management and other ServiceNow products.
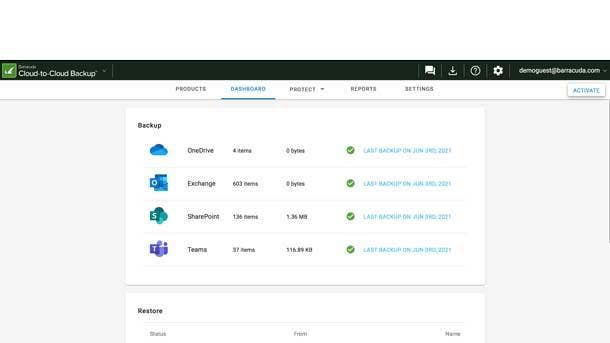
DATA PROTECTION AND MANAGEMENT
BARRACUDA CLOUD-TO-CLOUD BACKUP
WINNER: OVERALL
Offering protection of data in Microsoft 365 apps including Teams and SharePoint, Barracuda Cloud-to-Cloud Backup runs natively in the cloud and offers simplified management—enabling easier monitoring of backups and rapid restoration of data. And as a cloud-native platform, the offering provides massive scale and resiliency. Barracuda recently rearchitected its Cloud-to-Cloud Backup offering to provide enhanced performance for searching and restoring data; improved visibility via a redesigned user interface; additional data security functionality including data loss prevention and data classification; integration with Barracuda threat protection and other security services from the company; and capabilities to extend the offering to additional data sources, including new SaaS applications.
Subcategory Winner—Customer Need: Veeam Backup & Replication V11
With Veeam Backup and Replication V11, more than 200 enhancements for data protection across environments include improved disaster recovery with built-in continuous data protection; enhanced ransomware protection via immutable Linux repositories; and native support for Amazon S3 Glacier and Microsoft Azure Archive Storage.
Finalist: Axcient x360Recover Direct-to-Cloud
A business continuity and disaster recovery offering that doesn’t require hardware, Axcient x360Recover Direct-to-Cloud offers backup and cloud-based disaster recovery through a single solution with simplified management. Recently added features include faster pre-configured disaster recovery runbooks and enhanced security via single sign-on and multi-factor authentication.
Finalist: Commvault Metallic for MSPs
Commvault Metallic for MSPs is the company’s first SaaS-based data protection technology targeting SMB customers. The platform enables managed services providers to manage workloads, whether on-premises or in public clouds, with capabilities including flexible recovery, ransomware protection and immutable backups.
Finalist: StorageCraft ShadowXafe
Recent enhancements to StorageCraft ShadowXafe include the ability for partners and customers to use multiple cloud storage providers for their data backup and replication needs. The data protection solution has also been bolstered with improved centralized cloud management and new security measures including two-factor authentication.
Finalist: Zerto 9
Updates in Zerto 9 include a new feature for managing immutability settings on long-term data retention—enabling users to determine how long a backup can stay unaltered and ensuring that backups are kept safe in the cloud. Other key capabilities include new automated protection for virtual machines and a new instant restore feature, for easily restoring virtual machines directly into production.
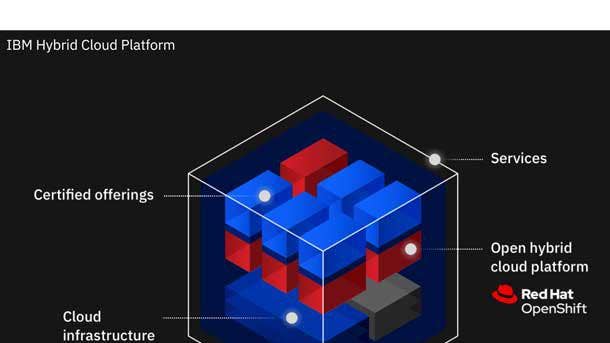
HYBRID CLOUD INFRASTRUCTURE
IBM HYBRID CLOUD PLATFORM
WINNER: OVERALL
IBM and its Red Hat subsidiary continue to advance the IBM Hybrid Cloud Platform with more capabilities around artificial intelligence and improvements to the RedHat OpenShift suite that powers the platform. A recent update to IBM’s Cloud Pak for Data can now provide answered distributed queries that are eight times faster than before, while IBM recently launched AutoSQL to automate data access, integration and management without the need for migration. Other recent updates have included the launch of Watson Orchestrate, a tool for business professionals with any coding skill level to automate scheduling, approvals, proposal planning and other routine tasks. Meanwhile, Red Hat updates have included a Red Hat Process Automation capability to enable deployed business decisions as containerized microservices in OpenShift and other cloud-native environments; the expansion of the Red Hat Insights predictive analytics offering to include OpenShift for use in multi-cluster environments; and general availability of the Red Hat OpenShift Service on Amazon Web Services.
Subcategory Winner—Revenue and Profit: HPE GreenLake
Hewlett Packard Enterprise unveiled GreenLake Lighthouse this year for running and managing workload-optimized solutions without waiting for new configurations. The company also introduced Compute Ops Manager to simplify infrastructure management from edge to cloud and expanded GreenLake Cloud Services for use with 5G, electronic medical records, financial services, data analytics and other uses.
Subcategory Winner—Customer Need: AWS Outposts
AWS Outposts is Amazon Web Services’ fully managed service for extending its infrastructure, services, application programming interfaces and tools to any on-premises environment or colocation space. The offering gained new support this year for Microsoft SQL Server, while users also gained the ability to make local snapshots of Amazon Elastic Block Store volumes for data residency and local backup requirements.
Finalist: Dell Technologies APEX Cloud Services
Dell Technologies APEX Cloud Services offer a secure, consistent and simplified IT experience for multi-cloud deployments. The offering enables the use of familiar solutions for compute, storage and data protection, while still providing access to the performance and features required by workloads across on-premises, colocation, public cloud or edge environments. Operations are unified by the self-serve APEX Console web portal.
Finalist: Lenovo TruScale Infrastructure Services
Lenovo TruScale Infrastructure Services recently received an expansion of available offerings, with new solutions for the platform built in partnership with VMware, Microsoft Azure, Intel and Deloitte. With the VMware Edge Cloud Solution, VMware edge cloud software—vSphere, vSAN and optional Tanzu and SD-WAN—runs on two ThinkSystem SE350 servers that are optimized for deployments at the edge.
Finalist: Microsoft Azure Stack HCI
Microsoft recently launched Azure Kubernetes Service on Azure Stack HCI for deploying containerized applications, and added an integration with Azure Defender for continuous threat monitoring. Azure Stack HCI also gained improved handling for high lookup volume and added support for Hyper-V’s Automatic VM Activation feature for Windows Server.
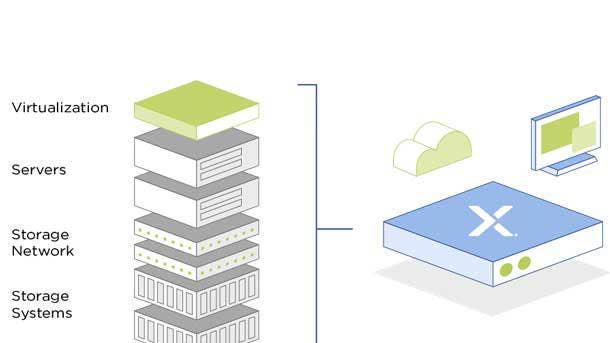
HYPERCONVERGED INFRASTRUCTURE
NUTANIX HCI
WINNER: OVERALL
Major updates to Nutanix HCI have included a new ability to run Google Cloud’s Anthos managed applications platform; an enhanced storage summary widget for improving consumption visibility; a configurable capacity alert threshold to increase efficiency; and a new rebuild progress indicator that shows administrators how long until clusters restore full resilience. Meanwhile, the launch of Nutanix’s AOS 6.0 has brought new disaster recovery capabilities, expanded workload support for big data and analytics applications and resiliency improvements. The capabilities include a native, always-on data loss offering for Nutanix HCI applications and Acropolis Dynamic Scheduling support for virtual machines with virtual GPUs. In addition, a new partnership between Nutanix and Microsoft now allows Azure management capabilities for Nutanix HCI on-premises Kubernetes clusters.
Subcategory Winner—Technology: Scale Computing HC3
Scale Computing recently introduced a video surveillance and security solution for video storage, management and analytics through its HC3 product. The company also announced new availability with Parallels Remote Application Server 18 to speed up virtual desktop infrastructure solution use.
Finalist: Cisco Hyperflex HX-Series
Cisco updated HX this year with new snapshot creation support, native iSCSI protocol support and a way to manage and monitor HyperFlex clusters from VMware vCenter Web UI. The company announced new full depth server offerings for HyperFlex Edge, new container storage interface support, new boot drives support and a new command-line shell, among other upgrades.
Finalist: Dell Technologies VxRail E Series
Aimed at smaller remote branch offices and edge locations, the Dell Technologies VxRail E Series offers hybrid and all-flash models. Dell Technologies enhanced the VxRail E Series this year with 50 percent more PCIe slots for more resources.
Finalist: HPE SimpliVity
Hewlett Packard Enterprise added new native integration for SimpliVity with the company’s Cloud Volumes service for more options in backup policy creation, virtual machine data restoration and backups management. The company added a bandwidth throttling mechanism to prevent off-site backups from saturating the wide area network. HPE also added a persistent volume feature to SimpliVity Container Storage Interface to help Kubernetes administrators.
Finalist: Lenovo ThinkAgile VX Series
Lenovo enhanced ThinkAgile VX Series this year to simplify deployment and management and allow faster HCI cluster deployment. The company also improved monitoring, troubleshooting, reporting and graphical mapping, as well as introducing full integration with VMware vSphere Lifecycle Manager for improved lifecycle management.

INDUSTRY-STANDARD SERVERS
CISCO UCS X-SERIES
WINNER: OVERALL
The Cisco UCS X-Series was designed with hybrid data center operations in mind, offering rack and blade systems that support workload versatility. The UCS X-Series was also designed to support future generations of technology in terms of processors, accelerators and computing interconnects. Crucially, the system is integrated with the Cisco Intersight cloud operations platform—enabling the use of tools such as the Intersight Cloud Orchestrator. The low-code automation framework simplifies complex workflows, allowing for easier orchestration of infrastructure and workloads and accelerated delivery of services. Ultimately, with its UCS X-Series, Cisco enables customers to transform their data center operations as they move resources to the cloud.
Subcategory Winner—Technology: Dell PowerEdge XE8545
The Dell EMC PowerEdge XE8545 server stands out by combining AMD and Nvidia technology designed for accelerated workloads. The server combines the maximum core counts of two third-gen AMD EPYC processors with four of the highest-performing NVIDIA A100 GPUs, making it ideal for machine learning, high-performance computing and GPU virtualization.
Finalist: HPE ProLiant DL345 Gen10 Plus Server
A new server line this year from Hewlett Packard Enterprise, the HPE ProLiant DL345 Gen10 Plus is targeted at applications such as structured/unstructured database management. The server is powered by third-gen AMD EPYC processors and provides up to 128 lanes of PCIe Gen4 to improve I/O throughput and reduce latency in a single-socket design.
Finalist: Lenovo ThinkSystem SR665
The Lenovo ThinkSystem SR665 is a two-socket server powered by AMD EPYC 7002 “Rome” and and AMD EPYC 7003 “Milan” processors—ultimately supporting up to 64 cores per processor and 128 Gen4 PCIe lanes to maximize server performance and decrease network bottlenecks for critical workloads.
Finalist: Supermicro A+ SuperBlade
Targeted at enterprise cloud and high-performance computing use cases, Supermicro’s A+ SuperBlade is available in 8U, 6U and 4U enclosures; supports third-get Intel Xeon Scalable or third-get AMD EPYC processors; and offers up to 48 DIMM slots, with up to 12 TB of DDR4-3200 memory per node.

IOT/EDGE
CISCO IOT GATEWAY SERIES
WINNER: OVERALL
With its recently launched IoT Gateway Series, Cisco enables IoT connectivity use cases—both for indoor and outdoor environments—at significant scale. The Cisco IoT Gateway Series also offers simplified setup, with the ability to easily connect to assets that hadn’t previously been connected. Notably, the IoT Gateway Series comes packaged with Cisco’s cloud-based IoT Operations Dashboard offering, which provides secure deployment and monitoring of industrial networking devices. Key features include zero-touch provisioning of devices, secure remote equipment access (without the need for added software installation) and support for operational workflows that can be used to configure IoT devices.
Subcategory Winner—Technology: Eaton 5P UPS
The Eaton 5P UPS is an enterprise-class backup power solution available as a tower UPS, wall mount UPS, and rackmount UPS – specifically made for edge computing use cases. The uninterrupted power supply offers flexibility in battery types with two models offering lithium-ion batteries. Customers pair the 5P UPS with an Eaton Gigabit Network card — the first in the industry to comply with the UL and IEC cybersecurity standards – as well as the Eaton Intelligent Power Management platform for seamless management of connected equipment at the edge.
Subcategory Winner—Revenue and Profit: HPE Aruba ESP
Aruba ESP is an intelligent architecture that helps partners and customers to manage their increasingly complex wired, wireless, SD-WAN and security infrastructures. Aruba Central, the network management and analytics platform that sits inside Aruba ESP, was recently enhanced with new AIops features, cloud-based authentication and policy capabilities, and an IoT operations service.
Finalist: Amazon Lookout for Vision
Amazon Lookout for Vision is a recently launched machine learning service that identifies defects and anomalies in visual representations. The service uses AWS-trained computer vision models to analyze images and video streams to find flaws and anomalies in manufactured products or production processes; damage to vehicles or structures; and defects in silicon wafers or any physical item where quality is important.
Finalist: Microsoft Azure Percept
Microsoft recently introduced Azure Percept, a combined hardware and software solution that allows for module deployment on the edge with video, audio and other cognitive feeds. The carrier board features an NXP iMX8m processor and Wi-Fi and Bluetooth connectivity, while the rest of the solution has an Intel Movidius Myriad X vision processing unit and RGB camera sensor.
Finalist: Schneider Electric EcoStruxure Micro Data Center R-Series
Schneider Electric’s R-series is built to withstand harsh indoor environments and applications, while providing users with remote management capabilities. The solution comes with access control, intrusion detection, security cameras and other security features.

LAPTOPS
HP ELITE DRAGONFLY MAX
WINNER: OVERALL
HP’s Elite Dragonfly Max debuted this year and—in addition to being the top pick of solution providers for our Products of the Year awards— the notebook ranked as our favorite business laptop of 2021 at the CRN Test Center. Along with offering a portable design and strong performance via 11th-gen Intel processors, the Elite Dragonfly Max stands out in the crowded laptop market with enhanced collaboration features. Those features include a 5-megapixel webcam and four wide-range mics optimized for conferencing, as well as a quad-speaker system driven by four amplifiers. Optional 5G connectivity and up to 16.5 hours of battery life are among the other great features for remote workers—as is the laptop’s 13.3-inch touch display with up to 1,000 nits of brightness and reduced blue light technology. And on portability, the notebook is both lightweight (at 2.49 pounds) and thin (at 0.63 of an inch)—while still allowing for work-friendly ports including USB-A and HDMI in addition to USB-C.
Subcategory Winner—Technology, Customer Need: Apple MacBook Pro (M1)
Apple’s entry-level, 13.3-inch MacBook Pro was among the first Macs to get the company’s high-performance, in-house M1 chip—which has delivered 2.8X better CPU performance and up to 5X improvement on GPU performance, versus the prior Intel-based version. Apple also promises up to 20 hours of video playback for the M1-powered MacBook Pro, doubling the promise of 10 hours for the previous model.
Finalist: Dell Latitude 9420
Available as a convertible QHD+ model or a clamshell FHD+ model, Dell‘s Latitude 9420 offers a 14-inch display with a 16:10 aspect ratio for a 5-percent larger viewing area and brightness of 500 nits. Key capabilities include optional support for 5G or LTE; a built-in speakerphone, dedicated mute and mic keys, and an enhanced webcam; and ExpressSign-in 2.0, which leverages Intel Visual Sensing Technology to enable faster auto-wake and auto-lock.
Finalist: Dynabook Satellite Pro L50
Dynabook Americas, formerly Toshiba America Client Solutions, recently revived Toshiba’s former Satellite Pro laptop series with new business-focused models including the Dynabook Satellite Pro L50. The notebook features a 15.6-inch FHD display, a 10th-generation Intel Core i7 processor, discrete Nvidia GeForce MX250 graphics, 16 GB of RAM and 512 GB of storage.
Finalist: Lenovo ThinkPad X1 Nano
Lenovo’s ThinkPad X1 Nano is the lightest ThinkPad to date, with a starting weight of just 2 pounds, while measuring just over a half-inch thick. The 13-inch display features a 16:10 aspect ratio that makes the display taller—providing a greater amount of usable workspace—while also offering sharp resolution (2,160 x 1,350) and high brightness (450 nits). Other features include up to 17 hours of battery life, four speakers and four mics, enhanced security (including a match-on-sensor fingerprint reader) and optional 5G.
Finalist: Microsoft Surface Laptop 4
Microsoft’s Surface Laptop 4 is offered with a choice of 13.5-inch or 15-inch touch displays and battery life of up to 19 hours for the 13.5-inch model, or up to 17.5 hours for the 15-inch model. The notebook also stands out by offering a choice of Intel or AMD CPUs, with options between 11th-gen Intel Core i chips or AMD Ryzen 4000 processors.

MULTIFUNCTION PRINTERS
XEROX ALTALINK C8100
WINNER: OVERALL
Xerox’s AltaLink C8100 color multifunction printers stand out with a tablet-like, intuitive user interface to speed up repetitive tasks, a native mobility feature for printing to any device and built-in security through Xerox’s ConnectKey Technology. Recent additions to the Xerox App Gallery for AltaLink printers include Touchless Access, which enables smartphone access to office devices through QR codes—avoiding local network connection—and new connections with Microsoft 365 and Google Drive. The AltaLink C8100 series devices bring a duty cycle of up to 300,000 images per month with print speeds of up to 70 pages per minute, and offer options including Xerox’s integrated RFID card reader
Subcategory Winner—Revenue and Profit: Lexmark MC3426adw
As part of Lexmark’s GO Line devices for SMBs, the MC3426adw offers strong speeds with a more-compact form factor to fit into smaller spaces. The device’s first-print-out time can reach as fast as 5.9 seconds, while color printing can reach up to 24 pages per minute and mono can reach up to 40 pages per minute.
Finalist: Epson WorkForce EC-C7000
With the WorkForce EC-C7000, Epson meets the needs of both at-home and in-office professionals with capabilities such as simplified wireless setup, prints of up to 13 x 19 inches in size, “instant-dry” pigment ink and a number of security features, such as secure data erase. The color A3 device also offers print speeds of up to 25 pages per minute, a 550-sheet paper capacity and a first-print-out time as fast as 8.5 seconds.
Finalist: HP Color LaserJet Enterprise MFP M480f
HP’s Color LaserJet Enterprise MFP M480f offers an enterprise-class experience in a compact size—with fleet-wide remote management and more than 100 embedded security features, such as run-time intrusion detection and self-healing from cyber attacks. The MFP also provides print speeds of up to 29 pages per minute, copying speeds of up to 28 pages per minute and two-sided scanning speeds of up to 49 pages per minute.
Finalist: Ricoh IM C6500
Aimed at high-volume offices, Ricoh’s IM C6500 is a color laser MFP that offers printing speeds of up to 65 pages per minute along with copy, scan and optional fax capabilities. Print resolution can reach up to 2,400 x 4,800 dpi, while the device features a paper capacity of up to 8,100 pages.
NETWORKING – ENTERPRISE
HPE ARUBA 630 SERIES WI-FI 6E
WINNER: OVERALL
As the first lineup of enterprise-grade Wi-Fi 6E access points on the market, the 630 series APs from Aruba Networks leverages the additional spectrum made available through the opening up of the 6GHz band. Offering Wi-Fi 6E provides customers with faster connections, lower congestion and broader channels. The Aruba 630 access points offer speeds of up 3.9 Mbps—using three dedicated radios, which cover the 2.4GHz and 5GHz bands in addition to 6GHz—enabling high bandwidth and low latency even for demanding services such as IoT, video and AR/VR. A part of the Aruba Edge Services Platform (ESP), the access points also benefit from Aruba ESP capabilities such as prediction and resolution of device issues before they become a problem; data analysis and identification of anomalies; and securing of unknown devices connected to the network.
Subcategory Winner—Technology: Cisco Catalyst 8000 Edge Series
Included in Cisco’s Catalyst 8000 Edge Series is the Catalyst 8500 Series Edge Platform, aimed at large-scale data center or colocation sites with integrated 40G and 100G Ethernet ports in a single rack unit. The 8500 is powered by Cisco’s proprietary ASIC for high-performance, scale and integrated security.
Finalist: CommScope Ruckus ICX 7550
CommScope’s Ruckus ICX 7550 switches bring connectivity at the edge for Wi-Fi 6 with up to 38 ports and 90 watts of 802.3bt Power over Ethernet per port. The switches offer 100-gigabit Ethernet uplinks to increase network capacity on existing optical wire infrastructure.
Finalist: Extreme Networks CoPilot
Extreme Networks CoPilot, a software feature that’s part of the ExtremeCloud IQ platform, provides automation that enables customers and partners to more easily execute time-sensitive tasks and monitor highly distributed network environments, while being 99 percent free of false alarms.
Finalist: Juniper Networks EX4400
Juniper Networks EX4400 is an access switch for the cloud that has security and performance meant for campus deployments, with Power over Ethernet, MACsec AES-256, microsegmentation using group-based policies, flow-based telemetry and EVPN-VXLAN to the access layer.

NETWORKING - SMB
HPE ARUBA INSTANT ON AP22
WINNER: OVERALL
With its Instant On AP22 access point, Aruba Networks is bringing fast Wi-Fi performance, lower latency and enhanced security to small businesses. The Wi-Fi 6 access point offers speeds of up to 1.7 Gbps and 4X capacity compared to 802.11ac APs—along with capabilities to simultaneously handle multiple clients on each channel, minimize interference from cellular networks and work with all legacy devices. Key security features include two-factor authentication to protect against compromised credentials; secure Wi-Fi access through WPA2/WPA3/OWE authentication; and embedded TPM for securely storing credentials and keys.
Finalist: Cisco Meraki MS120
Cisco’s MS120 switches come with layer 2 access meant for branch and campus deployments, with different models capable of 740 watts of power; a variety of port densities including small form-factor pluggable capable uplinks; and management and automatic firmware upgrades.
Finalist: Linksys Cloud Manager 2.0
Linksys’ Cloud Manager 2.0 -- built on Amazon Web Services micro-servers for real-time cloud management -- allows creation of unlimited organizations for network configuration segmenting while easing management, member removal and adding of members.
Finalist: Netgear WAX630
Netgear’s WAX630 promises high client density for small- to medium-sized business, with forward and backward compatibility with Netgear Insight Managed access points and Wi-Fi 6 and Wi-Fi 5 devices. The product is meant for open space environments with a large number of concurrent users, such as schools, warehouses and mid-sized offices.
Finalist: Zyxel Nebula
Zyxel Nebula offers remote management and monitoring, access to logs, advanced firmware scheduling and a Wi-Fi voucher. This year, the company added the USF Flex Firewall series to its Nebula solution to increase security capabilities.

POWER PROTECTION AND MANAGEMENT
EATON 9PX
WINNER: OVERALL
Power management firm Eaton has debuted a number of enhancements in its uninterruptible power supply (UPS) technology with the recent launch of its 9PX Lithium-ion UPS. The enhancements include improved battery lifespan and a smaller form factor—with an eye toward serving the needs of edge and light industrial environments. Eaton’s 9PX UPS offers a battery lifespan of up to eight to 10 years, compared to an average of three to five years for a comparable UPS that uses lead-acid batteries. The 9PX also offers a more-compact footprint, with a 1U form factor rather than 2U—as well as a 20-percent lighter rackmount model or 40-percent lighter extended battery module versus counterpart UPS models with lead-acid. The UPS also benefits from use with Eaton’s PredictPulse remote monitoring service, with capabilities including predictive analytics about potential component failures and remote diagnosis of issues.
Subcategory Winner—Revenue and Profit: CyberPower PFC Sinewave Mini-Tower UPS
The CyberPower PFC Sinewave Mini-Tower UPS provides battery backup and surge protection for desktop computers, workstations, networking devices and home entertainment systems in need of active PFC power source compatibility. Its multifunction control panel has a tiltable screen and the UPS comes with two USB charge ports for portable devices.
Finalist: Schneider Electric APC Smart-UPS Ultra
Schneider Electric introduced this 2kW, 1U, single-phase uninterruptible power supply earlier this year for small-footprint deployments. The UPS offers cloud-based monitoring, data-driven recommendations for performance optimization and visibility across multiple UPS devices.
Finalist: Tripp Lite S3M SmartOnline UPS
Tripp Lite’s S3M SmartOnline UPS series provides continuous 10kW to 100kW power in critical applications--with support possible for 480V and 600V environments--with a focus on small data centers of fewer than 20 racks. The S3M UPS series offers three-phase power, remote management and alerts.
Finalist: Vertiv Liebert PSI5
Vertiv Liebert PSI5, a lithium-ion, line-interactive, uninterruptible power supply suite, received an expansion this year that added a new 2200VA rack and tower model, as well as a 1500VA mini-tower configuration. The PS15 lithium-ion models cater to edge and distributed IT applications.

PROCESSORS
INTEL XEON SCALABLE, 3RD GEN
WINNER: OVERALL
Intel’s latest line of third-generation Xeon Scalable Processors delivers significant innovation in artificial intelligence, cryptography, high-performance computing and other workloads. The Ice Lake Xeon Scalable Processors are the first server chips to use Intel’s 10-nanometer manufacturing process, bringing an increase of Xeon’s maximum core count to 40 from 28 in the previous generation. By deploying Intel’s DL Boost instruction set and software optimizations, AI performance will be improved by 74 percent over the prior generation and offer significantly enhanced performance for cryptographic algorithms. For high-performance computing workloads, Intel said it will deliver up to 18 percent faster performance than competing processors on the Linpack benchmark that is used to measure the world’s top supercomputers. The Ice Lake lineup also promises speedier performance for a range of other workloads as well, such as cloud and 5G—with 50 percent faster performance for latency-sensitive workloads in the cloud over its predecessor and up to 62 percent faster performance for 5G network workloads.
Subcategory Winner—Revenue and Profit: AMD EPYC, 3rd Gen
AMD has brought major performance gains and new security features with its latest third-generation EPYC processors, code-named Milan. The processors feature up to 64 cores and 4.1 GHz in frequency, and leverage AMD’s Zen 3 core architecture—bringing a 19 percent increase in instructions per clock as well as a larger L3 cache in each chiplet of the processor. New security features include Secure Nested Paging, which provides new protection for a guest operating system against an untrusted hypervisor.
Subcategory Winner—Customer Need: Nvidia GeForce RTX 3090
Nvidia’s GeForce RTX 3090 graphics card offers a massive jump in performance with 10,496 CUDA codes, 24 GB in GDDR6X RAM and a boost clock of 1.7 GHz. The card also comes with silencer technology, featuring a design that is 10X quieter than the previous Titan RTX while keeping the GPU significantly cooler, as well.
Finalist: Apple M1
Apple‘s first in-house Arm-based processor, the M1, has brought performance gains of up to 3.5X for the MacBook Air and up to 2.8X for the entry-level MacBook Pro, compared with previous Intel-based models. On battery life, the M1-powered MacBook Pro doubled its potential battery life to 20 hours, while the MacBook Air with M1 can gain six hours with up to 18 hours of usage.
Finalist: Xilinx Alveo SN1000
Xilinx Alveo SN1000 is a composable SmartNIC for accelerating a variety of storage, network and security workloads typically handled by the CPU. The Alveo SN1000 comes with a low-latency Xilinx XCU26 FPGA, a 16-core Arm processor, dual-QSFP ports for 10/25/100 GB/s connectivity and a 75-watt power envelope.

PUBLIC CLOUD
MICROSOFT AZURE
WINNER: OVERALL
Microsoft’s Azure public cloud platform received the highest overall rating from solution providers who voted in CRN’s Products of the Year awards for 2021, sweeping the three subcategories of Technology, Revenue and Profit, and Customer Need. The high marks follow similar results in CRN’s inaugural Cloud Barometer survey earlier this year, where Azure got the highest partner satisfaction rating to beat out Amazon Web Services and Google Cloud. Azure is “superior to AWS and Google” because of Microsoft’s partner-friendly program and business model, said Reed Wiedower, global alliances leader and CTO for the Cognizant Microsoft Business Group, an Azure Expert Managed Services Provider. At Logicalis Group, another Azure Expert MSP, CEO Bob Bailkoski said that the growth opportunity with Azure is larger than it is with AWS. “Microsoft’s articulation of the opportunity that’s available with Azure is much easier for our customers to understand— especially in the C-suite—than it is perhaps with AWS, which is a slightly more technical, developer-style solution,” he said.
Finalist: Amazon Web Services
In CRN’s 2021 Products of the Year survey of solution providers, Amazon Web Services ranked at No. 2 overall among the five public cloud providers included in the survey. AWS ranked at No. 2 in the Technology and Customer Need subcategories, while ranking at No. 3 in Revenue and Profit.
Finalist: Google Cloud
In CRN’s 2021 Products of the Year survey, solution providers gave Google Cloud the No. 3 overall ranking among public cloud providers. Google Cloud ranked at No. 3 in the Technology sub-category, and at No. 4 in the Customer Need and Revenue and Profit sub-categories.
Finalist: IBM Cloud
IBM Cloud received the No. 4 ranking in CRN’s 2021 Products of the Year survey of solution providers. In terms of sub-categories, IBM Cloud’s best showing was in Revenue and Profit, getting the No. 2 ranking in that sub-category. The platform ranked at No. 3 in Customer Need and at No. 4 in Technology.
Finalist: Oracle Cloud Infrastructure
Oracle Cloud Infrastructure was ranked by solution providers at No. 5 overall in Public Cloud in CRN’s 2021 Products of the Year survey. The platform ranked at No. 5 in all three sub-categories in the survey for Public Cloud.
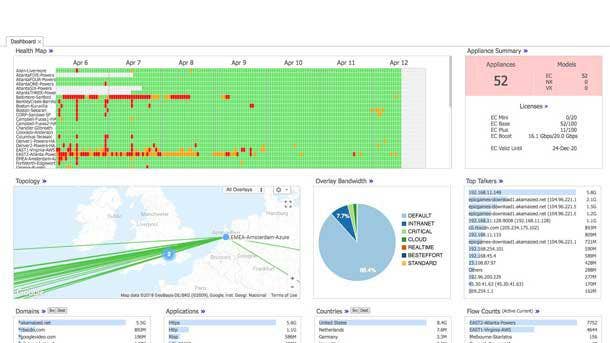
SD-WAN
HPE ARUBA EDGECONNECT
WINNER: OVERALL
Following the acquisition of Silver Peak, HPE Aruba has made the Aruba EdgeConnect SD-WAN platform available to partners and customers while enhancing the offering through integration with Aruba management and security offerings. Key capabilities for Aruba EdgeConnect include application-specific routing—with automatic programming for app routing, performance and security policies to all sites—as well as centralized SD-WAN management via Aruba Orchestrator, consistent application experience and continuous adaptation based on real-time conditions. Recent integrations include with the Aruba ClearPass Policy Manager— offering an automated way of defining roles that are enforced across the network—as well as with Aruba Threat Defense, extending capabilities for advanced intrusion detection and prevention to EdgeConnect appliances.
Finalist: Cisco SD-WAN
Recent updates to the Cisco SD-WAN offering include an extension of the secure SD-WAN fabric from Cisco Meraki MX appliances into Cisco Umbrella. The appliances now provide a unified solution for optimal SD-WAN connectivity that brings together on-premises security and cloud-driven security intelligence.
Finalist: Masergy SD-WAN Secure
Recent enhancements to the Masergy SD-WAN Secure solution have included updated AIOps capabilities for automation of network management and boosted performance for cloud apps. The AIOps functionality enables capabilities such as prediction and prevention of service outages.
Finalist: Palo Alto Networks CloudGenix SD-WAN
Formerly CloudGenix SD-WAN, Palo Alto Networks Prisma SD-WAN provides visibility, policy and path decisions at Layer 7; automation powered by data science and machine learning; and cloud-delivered branch services. The company recently enhanced Prisma SD-WAN with an updated web interface, app switcher and new time series features.
Finalist: Versa Titan
Versa Titan aims to deliver SASE services for branch and network edge management and security, bringing cloud-aware and software-as-a-service that’s accelerated for direct-cloud access with major cloud operators. Titan also has a mobile app that enables monitoring, configuration, troubleshooting and other actions on-the-go.
Finalist: VMware SD-WAN
VMware SD-WAN offering brings together capabilities including WAN edge, edge compute and cloud-based security. The offering has received a number of recent enhancements, including in the realm of security—with the platform seeing the addition of capabilities such as Secure Web Gateway and Zero Trust Network Access.

SECURITY-CLOUD
CISCO SECUREX
WINNER: OVERALL
With a focus on simplifying security for partners and customers, Cisco’s cloud-native SecureX platform provides a unified and customizable dashboard, automation of routine tasks, threat response capabilities, integrations with third-party solutions and comprehensive device insights. Recent enhancements include capabilities to reduce the dwell time for security operations while bringing automation to tasks related to detection and remediation of threats. The capabilities include automated workflows for phishing investigations and threat investigations—dramatically reducing the time needed to detect and remediate threats. Other updates have included capabilities to simplify the transition from EDR to XDR with improved orchestration capabilities as well as additional pre-built workflows and integrations.
Subcategory Winner—Technology: CrowdStrike Falcon Horizon
Recently launched features for Falcon Horizon leverage CrowdStrike’s telemetry to deliver indicators of attack for the cloud control plane and provide DevOps tools for faster detection and remediation. The new capabilities include continuous threat detection, as well as monitoring and correlation across cloud and on-premises environments to help security teams cut through the noise of a multi-cloud environment.
Finalist: Check Point CloudGuard Cloud Native Security
A recent expansion of Check Point’s CloudGuard Cloud Native Security offering has brought new capabilities for application-first workload protection via the CloudGuard Workload Protection solution. The solution protects cloud workloads with tools for fully automated security across applications, APIs and microservices.
Finalist: McAfee Enterprise MVision Unified Cloud Edge
With the McAfee Enterprise MVision Unified Cloud Edge, customers can define a single data protection or threat prevention policy and consistently apply the rules across the device, the network and the cloud. The offering has been bolstered with first-of-its-kind integrated remote browser isolation technology, unified data loss prevention and incident management across devices, networks, web and the cloud.
Finalist: Microsoft Cloud App Security
As Microsoft’s cloud app security broker (CASB) solution, Microsoft Cloud App Security provides visibility across multi-cloud apps, finds shadow IT, protects sensitive information in the cloud, protects against cyber threats, assesses compliance and manages security posture across clouds. Recent updates have included a new app governance capability that allows users to monitor, protect and govern Microsoft 365 apps and identify risky behaviors.
Finalist: Palo Alto Networks SaaS Security
Palo Alto Networks SaaS Security, a recently launched CASB solution, proactively protects both on-premises and cloud-hosted applications. It automatically discovers and prevents risks with thousands of new Software as a Service applications before they become an issue—using techniques including continuous identification, categorization and granular risk-based control of known and previously unknown SaaS applications.
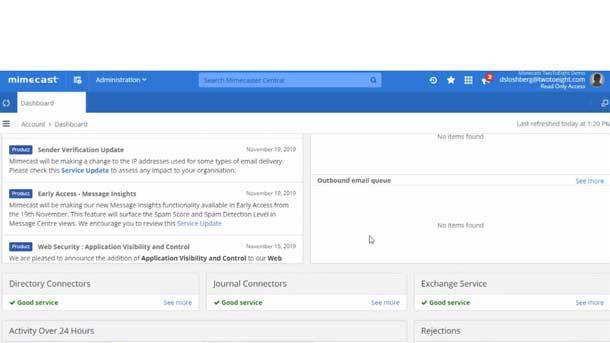
SECURITY-EMAIL
MIMECAST EMAIL SECURITY WITH TARGETED THREAT PROTECTION
WINNER: OVERALL
Mimecast’s Email Security offering—augmented with Targeted Threat Protection capabilities—brings security at the email perimeter and network, as well as beyond the perimeter. The company’s Secure Email Gateway offers cloud-based protection against malware, spear-phishing spam and zero-day attacks with a combination of applications, policies, detection engines and security intelligence feeds. The company’s Targeted Threat Protection offerings guard against targeted email attacks such as ransomware, impersonation and spear phishing. Capabilities include URL protect (which checks for website security at the time of click); attachment protect (using analytics and sandboxing to block malicious attachments); impersonation protect (which secures against sender and domain spoofing attempts); and browser isolation (enabling users to click on embedded URLs and use the web safely with all phishing attempts and malware blocked).
Subcategory Winner—Revenue and Profit, Technology: Zix Secure Cloud
Key capabilities in the Zix Secure Cloud include automatic email encryption using proven content filters, secure file share and email threat protection using advanced link protection, quarantine, attachment sandboxing and message retraction.
Finalist: Barracuda Total Email Protection
Barracuda Total Email Protection offers prevention of email attacks using email gateway defenses, inbox defense and security awareness training. The solution also provides detection of suspicious email and email threats, as well as automated response and rapid recovery.
Finalist: Check Point Harmony Email & Office
A part of Check Point’s Harmony unified offering to secure internet connections and devices, Check Point Harmony Email & Office provides protection for Office 365 and Google Workspace with capabilities such as blocking of phishing attacks and malware, data loss prevention and prevention of account takeover.
Finalist: Proofpoint Email Security and Protection
Major features in Proofpoint Email Security and Protection including protection against email fraud attack with accurate classification of impostor and phishing emails, malware and spam using machine learning technology. Other capabilities include Advanced BEC Defense to find and stop Business Email Compromise attacks using an AI-driven detection engine.

SECURITY - ENDPOINT PROTECTION
SENTINELONE SINGULARITY
WINNER: OVERALL
SentinelOne Singularity seamlessly fuses together the data, access, control and integration planes of its endpoint protection, endpoint detection and response, IoT security and cloud workload protection into a centralized platform. With Singularity, organizations gain access to back-end data across the company, providing a cohesive view of their network and assets by adding a real-time autonomous security layer. Singularity detects, responds and hunts in the context of all enterprise assets, allowing organizations to see what has never been seen before and control the unknown.
Finalist: CrowdStrike Falcon
In a major expansion of the CrowdStrike Falcon endpoint protection platform, the company recently introduced CrowdStrike Falcon Fusion to streamline incident investigation, response and remediation using repeatable and consistent workflows. The solution allows incident triaging and incident response to be accelerated through configuration of custom actions and notifications, leveraging contextual insights from endpoints and workloads.
Finalist: McAfee Enterprise MVision XDR
Recent enhancements to McAfee Enterprise MVision XDR include unified score, offering a single view of security posture; threat profiling, which provides context on threat groups in order to accelerate both investigation and resolution; and universal search, offering a “Google-like” search experience for threat intelligence information.
Finalist: Microsoft Defender for Endpoint
Microsoft Defender for Endpoint, the company’s “cloud-powered” endpoint security offering, provides vulnerability management, endpoint protection and endpoint detection and response, as well as mobile threat defense. The offering was recently expanded to support Windows 10 on Arm devices as well as unmanaged devices running Windows, macOS, Linux, iOS or Android.
Finalist: Sophos XDR
Sophos XDR is an extended detection and response solution that synchronizes key security components—endpoint, firewall, server and email protection—to offer a holistic view of an environment, rich data and deep analysis. The solution ultimately enables enhanced threat detection, investigation and response.
Finalist: VMware Carbon Black Cloud Endpoint
Recent updates for VMware Carbon Black Cloud Endpoint have included the introduction of vulnerability management. The new module provides enhanced visibility and prioritization of risks—enabling security teams to focus on addressing the most exploitable vulnerabilities.
SECURITY - IDENTITY AND ACCESS MANAGEMENT
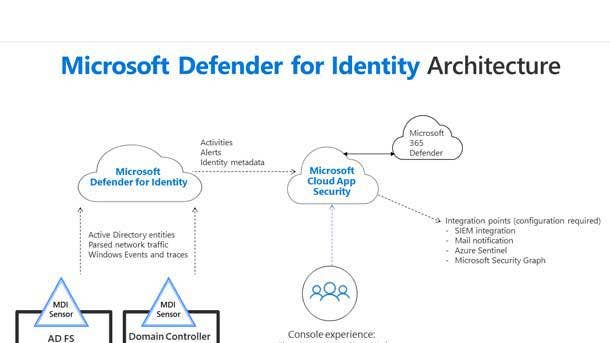
MICROSOFT DEFENDER FOR IDENTITY
WINNER: OVERALL
A centerpiece of Microsoft’s security strategy, the Microsoft Defender for Identity offering—previously Azure Advanced Threat Protection—enables protection of on-premises identities and correlation of signals with the Microsoft 365 productivity suite. Key capabilities include eliminating on premises vulnerabilities to proactively halt cyberattacks, as well as threat assessment to enable security operations teams to focus on the biggest legitimate threats. Using analytics and data intelligence to prioritize threats, Microsoft Defender for Identity allows security teams to rapidly respond to incidents, investigate the riskiest users (using a score that’s based on their behavior and previous incidents) and efficiently hunt for threats with advanced queries.
Subcategory Winner—Customer Need: Okta Identity Cloud
Key updates have included the launch of an access gateway to easily connect on-premises legacy and custom-built applications to the Okta Identity Cloud. Okta has also expanded its portfolio with the rollout of Okta Devices SDK, letting developers enable passwordless authentication through branded push notifications with biometric capabilities.
Finalist: CyberArk Identity Security Platform
The CyberArk Identity Security Platform provides secure access for all applications and across both cloud and on-premises environments. Recent updates to the platform have included new offerings such as Dynamic Privileged Access for provisioning access hybrid and cloud workloads that is “just in time,” lowering the risk of standing access.
Finalist: ForgeRock Identity Cloud
The ForgeRock Identity Cloud recently received enhancements focused on minimizing downtime and modernizing DevOps practices while enabling secure digital experiences for users. New cloud- and AI-driven capabilities have been added to help simplify identity journeys so that users can more quality access what they’re looking for.
Finalist: ThycoticCentrify Platform
With the recent merger of Thycotic and Centrify, ThycoticCentrify offers privileged access management solutions for cloud-driven identity security. Recent enhancements have included the addition of new privilege management security capabilities for the Thycotic Privilege Manager solution, expanding protections for workstations and streamlining reporting for security and compliance across operating systems.
SECURITY - MANAGED DETECTION AND RESPONSE
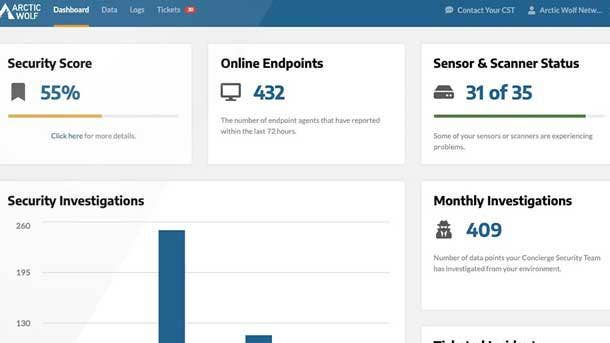
ARCTIC WOLF MANAGED DETECTION AND RESPONSE
WINNER: OVERALL
With 24/7 monitoring of networks, endpoints and cloud workloads, Arctic Wolf’s flagship Managed Detection and Response offering enables advanced threat detection along with response to and recovery from attacks—including sophisticated evolving threats. In addition to 24/7 monitoring that’s delivered by a dedicated concierge security team, key detection capabilities include broad visibility and analysis of massive amounts of security data to find advanced threats. Meanwhile, response capabilities for Arctic Wolf MDR include managed investigations, log retention/search and rapid incident response. Recovery capabilities include guided remediation, root cause analysis and personalized engagement via regular meetings to optimize a customer’s security posture.
Finalist: Cybereason Managed Detection and Response
With its Security Operation Centers, Cybereason Managed Detection and Response delivers proactive hunting, analysis and remediation of threats on a 24/7 basis. The offering also provides a scoring and triage system to bring deeper correlations of malicious operations across all endpoints on a network.
Finalist: Mandiant Managed Defense
The Mandiant Managed Defense service—which provides frontline detection along with incident response expertise—was recently updated to add support for Microsoft Defender for Endpoint. The support enables integration of Mandiant expertise into the Microsoft Defender for Endpoint solution to enhance security for joint customers of the companies.
Finalist: SentinelOne Vigilance Respond
With 24/7 monitoring, SentinelOne Vigilance Respond provides in-house experts that review and act upon identified threats. The service offers a rapid, 18-minute MTTR (mean time to respond)—mitigating and resolving threats quickly and following up with forensic deep dives and targeted threat hunting.
Finalist: Sophos Managed Threat Response
Sophos Managed Threat Response offers a fully managed and customizable approach to finding and stopping cyber threats. Key additions to the offering over the past year have included Sophos Rapid Response, a remote incident response service that activates a 24/7 team to halt in-progress attacks—such as ransomware—and eliminate attackers from the network.

SECURITY – NETWORK
PALO ALTO NETWORKS NEXT-GENERATION ML-POWERED FIREWALLS
WINNER: OVERALL
Palo Alto Networks’ Next-Generation ML-Powered Firewalls expand protection up to the hyperscale data center, internet edge and campus segmentation deployments—and down to a desktop form factor. The PA-400 series is built for the distributed enterprise and offers up to 10X more performance with security services and decryption compared with the previous generation. The PA-400 firewall also offers easier and flexible deployment, including zero-touch provisioning to simplify rollout to branches, even at large scale. In addition, the firewall offers a quiet, compact design with multiple mounting options for a range of scenarios. Meanwhile, the PA-5450 firewall secures traffic that is nearly fully encrypted and is purpose-built to apply decryption and machine learning-powered security to stop zero days as well as known threats. The firewall offers 120-Gbps performance with security services enabled, offering 4X the performance of the previous generation.
Subcategory Winner—Technology: Cisco Umbrella
Cisco Umbrella enables securing of internet access and control of cloud app usage—across networks, remote workers and branch offices—by integrating multiple security functions into a unified cloud service. The platform brings together secure web gateway, cloud-delivered firewall, DNS-layer security, remote browser isolation and cloud access security broker capabilities to provide robust threat protection.
Finalist: Fortinet FortiGate 3500F
Designed to protect organizations with hybrid data centers, Fortinet’s recently launched FortiGate 3500F next-generation firewall offers multiple high-speed interfaces as well as high throughput and port density. Key elements include purpose-built security processors for high-performance IPS, strong SSL inspection performance and advanced threat protection capabilities.
Finalist: SonicWall NSa Firewalls
For Gen 7 of its Network Security appliance (NSa) Series, SonicWall offers strong performance and port density along with capabilities such as malware analysis, inspection of encrypted traffic and URL filtering. Additional networking features include high availability, dynamic and virtual routing, and SD-WAN.
Finalist: Sophos Firewall XGS Series
Recent updates to Sophos Firewall include the debut of new XGS Series appliances offering enhanced protection against zero-day threats. Among the key capabilities is improved TLS inspection of encrypted traffic—including native TLS 1.3 support—offering a 5X boost on speed.
Finalist: Zscaler ZPA Private Service Edge
Zscaler ZPA Private Service Edge was recently unveiled to securely broker users to private applications, removing the need for on-premises network segmentation. The solution provides local brokering between on-prem users and on-prem apps, speeding up the experience for users while lowering complexity and risk.

STORAGE – ENTERPRISE
PURE STORAGE FLASHARRAY//X90
WINNER: OVERALL
FlashArray//X90 is the top-of-the-line model in Pure Storage’s FlashArray//X portfolio of all-flash, all-NVMe arrays. The FlashArray//X90 offers a 5:1 data reduction average, up to 3.3 PB of effective capacity, ultra-low latency (as low as 150 microseconds), 99.9999 percent availability and artificial intelligence-powered management. Pure Storage recently updated the Purity software used by the FlashArray//X series with improvements that include acceleration of Windows applications and reduced downtime from ransomware. The reduced downtime comes through the addition of SafeMode snapshots—which provide immutable snapshots, retention-based policies (which can secure data for as long as 30 days) and the ability to rapidly restore expired data.
Finalist: Dell EMC PowerStore 9000
Dell EMC’s PowerStore 9000 is the company’s most powerful storage solution, providing a unified platform for block, filed and vVol data, with intelligent scale-up and scale-out capability of appliance clusters. The PowerStore 9000 contains up to four Intel CPUs, NVMe, and capacity of 11.5-TB. The storage platform has automated management of resources across the cluster for top-notch storage utilization and simplified administration.
Finalist: HPE Alletra 9000
With its all-NVMe HPE Alletra 9000 storage system, Hewlett Packard Enterprise offers a cloud-native data infrastructure that is managed by the company’s Data Services Cloud Console for unified data management across hybrid cloud deployments. Alletra offers more than 99.9999 percent guaranteed availability and provides the architectural flexibility needed to run any application with strong performance, efficiency and resiliency.
Finalist: IBM FlashSystem 9200
The IBM FlashSystem 9200 combines flash performance and end-to-end NVMe with IBM FlashCore and IBM Spectrum Virtualize, enabling low latency, predictive storage management and proactive support. The 2U all-flash array is enabled for hybrid cloud with data resilience and access to IBM Storage Expert Care.
Finalist: NetApp AFF A700
NetApp recently introduced back-end NVMe storage for the A700 to support low latency and simplify NVMe SSD technology adoption. A700 systems can connect to high-speed 100GbE and 25GbE host networks, and they come with self-encrypting disk technology for data-at-rest encryption in all deployments.

STORAGE – SMB
LENOVO THINKSYSTEM DM5100F
WINNER: OVERALL
Unveiled last December as the newest member of Lenovo’s ThinkSystem storage array line, the ThinkSystem DM5100F offers all-flash storage at a price point that’s ideal for SMBs while still providing strong performance and minimal latency. The all-NVMe array offers raw storage capacity of up to 737 TB and a 45 per cent performance improvement over its predecessor model. Other updates include improved data protection and native management of object storage. The enhancements enable management and analysis of all types of data on one storage platform to reduce costs of infrastructure and accelerate analytics processing.
Subcategory Winner—Revenue and Profit: HPE MSA Gen 6
HPE’s Modular Smart Array (MSA) Gen 6 offers hybrid-flash storage with enhancements including automatic tiering to accelerate data access; new data protection capabilities, which minimize the time an array is vulnerable or degraded; and an integration with HPE Cloud Volumes Backup, offering a simpler path to cloud-based data protection that also reduces costs.
Finalist: Dell EMC PowerStore 500
Targeted as a lower-priced all-flash storage array, the Dell EMC PowerStore 500 nonetheless brings enterprise-level performance and storage services. The array comes in a 2U form-factor chassis with capacity of up to 1.2 petabytes, and supports up to 2.4 million SQL transactions per minute and 1,500 virtual desktops per appliance.
Finalist: IBM FlashSystem 5200
A part of the second generation of IBM‘s entry-level, all-flash storage series, the IBM FlashSystem 5200 provides up to 1.7 petabytes of capacity in a 1U chassis and supports 21 GBs per second throughput, which is 40 percent greater than its predecessor. Other features include IBM’s HyperSwap capability, providing 100-percent availability with as few as three flash modules.
Finalist: Pure Storage FlashArray//X10
Pure Storage’s all-NVMe FlashArray//X10 offers up to 73 TB effective capacity, 22 TB raw capacity and latency of less than 1 millisecond. The FlashArray//X10 recently gained the ability to populate with the software-defined DirectFlash module for boosted performance and density.
STORAGE - SOFTWARE-DEFINED
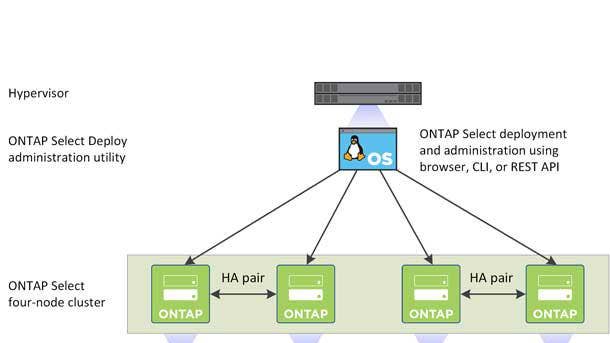
NETAPP ONTAP SELECT
WINNER: OVERALL
With Ontap Select, NetApp offers software-defined storage that can be deployed on commodity hardware and provides capabilities for data protection and resilience—as well as simplified management and movement of data across hybrid environments. It leverages NetApp’s Ontap 9 storage operating system and benefits from Snapshot copies and remote backup to protect data, and uses NetApp Volume Encryption for data at rest. Ontap Select can co-locate with application virtual machines to optimize hardware use and allows users to consolidate network file system, common internet file system and internet small computer system interface applications and workloads on local and remote hosts.
Finalist: DataCore Swarm
DataCore’s Swarm object storage software is a tool for deployment streamlining, self-healing and self-managing symmetric architecture and web-based multi-tenant management, with backup and disaster recovery for any S3-enabled service or device. Swarm can handle terabyte-sized video storage and streaming.
Finalist: Dell EMC PowerFlex
Recent updates to Dell EMC PowerFlex have brought enhancements to automation and workload execution, including added Nvidia GPU options; support for OpenShift v4.6 with CoreOS; broader support for Kubernetes distributions and workloads; and VMware NSX-T support for PowerFlex appliances.
Finalist: HPE Cloud Volumes
Within Hewlett Packard Enterprise’s Cloud Volumes suite, HPE Cloud Volumes Block is a multi-cloud/hybrid cloud storage solution that supports Amazon Web Services, Microsoft Azure and Google Cloud--offering enhanced durability compared to using public cloud storage alone. Meanwhile, HPE Cloud Volumes Backup provides cloud backup for on-premises, edge and cloud workloads--and was recently integrated with HPE SimpliVity solution to provide edge sites with easier backup directly to the cloud.
Finalist: IBM Spectrum Fusion
IBM Spectrum Fusion brings users general parallel file system technology and data protection software in one product. Spectrum Fusion includes an integrated HCI appliance for containers and Red Hat OpenShift virtual machines, global data access through active file management and the ability to scale to up to 20 servers.
Finalist: VMware vSAN
Improvements to VMware vSAN this year have included a new way for vSAN clusters to share capacity with non-HCI-based clusters; new support for stretched cluster deployments and two-node clusters; and increased scalability to more than 60 hosts.

TABLETS
HP ELITE X2 G8
WINNER: OVERALL
HP debuted the Elite x2 G8 this year featuring a number of updates and new capabilities. The tablet offers options for its 13-inch touch display including a model with 3,000 x 2,000 resolution and up to 450 nits of brightness. It can also be configured with a 1,920 x 1,280 resolution display, featuring the Sure View Gen 3 integrated privacy screen and up to 1,000 nits of brightness. On performance, the tablet offers a choice of 11th-gen Intel Core processors. The Elite x2 G8 has a built-in kickstand and is made from CNC aluminum and can attach to a full-size backlit keyboard.
Subcategory Winner—Technology: Microsoft Surface Pro 7+ for Business
Business-friendly updates with Microsoft‘s Surface Pro 7+ include optional LTE Advanced connectivity and a removable SSD to help enhance security and data retention -- as well as longer battery life (up to 15 hours on a charge, compared to 10.5 hours on the Surface Pro 7). The 12.3-inch tablet also moves up to 11th-gen Intel Core processors, for a performance boost of more than 2X.
Subcategory Winner—Customer Need: Apple iPad Pro (M1)
Apple’s iPad Pro update for 2021 adds the company’s Arm-based M1 chip, enabling up to 50-percent faster CPU performance over the previous model. The iPad Pro is available in 11-inch and 12.9-inch display sizes, with other upgrades including support for 5G and a new “Liquid Retina XDR” display with up to 1,600 nits of brightness on the 12.9-inch model.
Finalist: Dell Latitude 7320 Detachable
Dell’s Latitude 7320 Detachable features a new 13-inch display size with FHD+ resolution and 500 nits of brightness, along with an enhanced webcam and a newly designed folio keyboard with a faux suede design. On performance and connectivity, the tablet offers up to the 11th-gen Intel Core i7 with vPro as well as support for WiFi 6 and optional LTE connectivity.
Finalist: Lenovo ThinkPad X12 Detachable
Lenovo’s ThinkPad X12 Detachable features a 12.3-inch FHD+ display with a 3:2 aspect ratio, 400 nits of brightness and Gorilla Glass 5 for durability. The device includes 11th-gen Intel Core processors (up to Core i7 vPro), up to 10 hours of battery life and always-on responsiveness, allowing users to resume working within less than a second of waking the device.