The 2017 Tech Innovator Awards

Tech Innovators
The future of IT can be glimpsed right now, if you know where to look: It's being implemented by cutting-edge solution providers around North America on a daily basis. But choosing future-ready IT solutions for customers is no easy task, given the vast number of options on the market.
To narrow the field, this year's Tech Innovator Awards honor groundbreaking vendors in 32 categories, with the winners and finalists chosen from among 216 applicants.
The ability to translate a future-facing view of technology into reality today is the crowning achievement of this year's Tech Innovator winners. Here's who has provided that spark this year.
BUSINESS INTELLIGENCE AND ANALYTICS
WINNER:
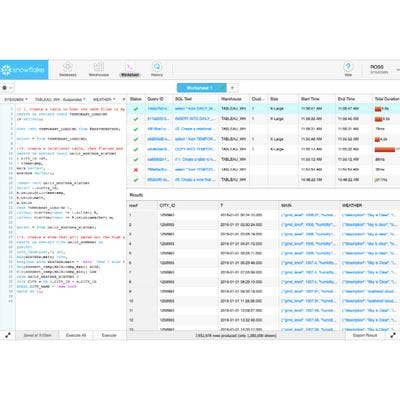
Snowflake Computing Data Sharehouse
With its Data Sharehouse offering, Snowflake Computing is providing a less-burdensome method for enterprises to share the massive quantities of data they are producing. The end goal is to eliminate barriers to gaining crucial insightsfrom enterprise data, by supplanting typical data-sharing methods such as email and FTP. Snowflake Computing's Data Sharehouse enables enterprises to offer read-only, secure access to everything from a narrow slice of data up to their entire data warehouse. Key features include one-time, native storage of all data; easy cloud sharing; and an ideal payment structure, wherein data recipients only pay for the computing resources they use during data-sharing process.
BUSINESS INTELLIGENCE AND ANALYTICS
FINALISTS:
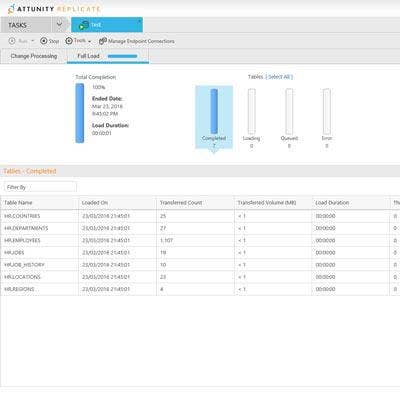
Attunity Replicate 5.5
Replicate 5.5 is Attunity's data replication and ingestion offering for delivering more-accurate data -- more quickly -- ultimately improving analytics and business insight. Replicate 5.5 offers key features including automation of the data integration process to reduce the need for coding.
Cisco AppDynamics Business iQ
AppDynamics' Business iQ brings together application monitoring and business monitoring to help customers quickly understand how product updates, new online initiatives, and other major events affect key business metrics -- such as sales, order sizes and number of customers.
IBM SPSS Modeler
SPSS Modeler, an IBM platform for data science and predictive analytics, is aimed at solving typical business problems with predictive intelligence. SPSS Modeler offers a drag-and-drop interface for performing text analytics, automated modeling, and other functions to enable improved decision-making and outcomes.
Reltio Insights
To provide quick access to critical predictive analytics, Reltio Insights connects data within Reltio Cloud to the Apache Spark data processing engine. The offering consolidates data from sources including master profiles, interactions and transactions -- as well as from social media and other public sources.
CLOUD APPLICATIONS
WINNER:
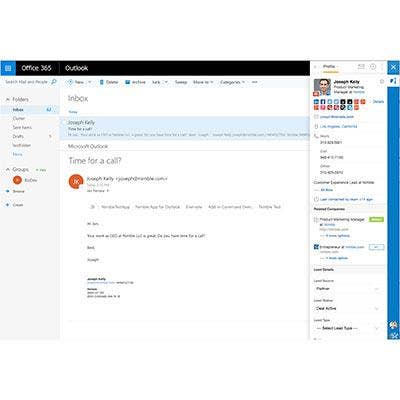
Nimble CRM
Nimble CRM boosts the capabilities of Microsoft Office 365 and Google G Suite by seeding those productivity suites with data from social media sites and leading CRM platforms. The software draws data from social platforms such as LinkedIn; from CRM systems such as Salesforce and Dynamics; as well as from inboxes, calendars and previous contact records. Nimble CRM thus delivers to small businesses a consolidated and detailed view of customers through tools they're already using. In July, Nimble CRM launched a channel program to align with more solution providers in the Microsoft and Google channels.
CLOUD APPLICATIONS
FINALISTS:
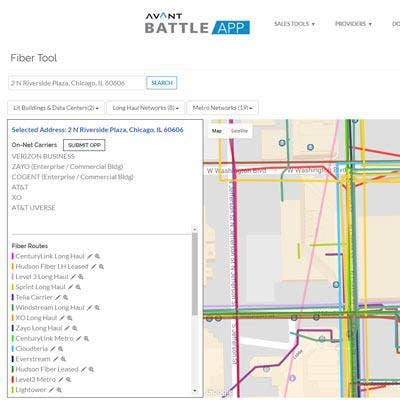
Avant BattleApp
Avant Communications launched its Avant BattleApp web application to make it easier for channel partners to sell IT solutions to customers, by showcasing their technology offerings via features such as the Data Center Locator and Fiber Locator.
Binary Tree Power365
Power365 is Binary Tree's offering for Office 365 integrations between multiple tenants. The Software as a Service is targeted at enabling collaboration and productivity at organizations in the wake of M&A, through cross-tenant integration and migration.
Impartner PRM
The Partner Relationship Management application from Impartner aims to make setting up a partner portal faster and simpler, along with providing a range of customization options and tools such as price quoting and deal management capabilities.
SAP S/4HANA Cloud
The S/4HANA Cloud from SAP is a cloud-based "intelligent ERP" that leverages machine learning and predictive analytics -- with the goal of making advanced ERP possible in the public cloud, even without a large up-front financial investment or major changes to infrastructure.

CLOUD BACKUP/DISASTER RECOVERY
WINNER:
Rubrik Alta 4.0
With Alta 4.0, Rubrik is aiming to provide a simple, fast way to back up and recover critical business data -- which also scales more easily than traditional products. The offering doesn't require the sort of tedious implementation and operation processes found with legacy backup, such as substantial application/storage forecasting, architectural planning, and post-implementation tuning. Alta 4.0 can be up and running within 15 minutes of deployment, according to Rubrik, and its integration with cloud services is a major advantage over legacy products. The offering is compatible with operating environments including Amazon Web Services, Microsoft Azure, VMware, Hyper-V, Nutanix AHV, Linux and Windows.

CLOUD BACKUP/DISASTER RECOVERY
FINALISTS:
Arcserve Unified Data Protection 8000
Along with offering highly expandable storage capacity (protection for up to 240 TB of raw source data) and advanced deduplication capabilities, Arcserve's Unified Data Protection 8000 Appliance supports offsite backup and disaster recovery in two of the largest public cloud services, Amazon Web Services and Microsoft Azure.
Atadata Ataguard
Aimed at enterprise customers with multi-cloud and hybrid-cloud data deployments, Atatdata's Ataguard offers both automated failover (to any physical, virtual or cloud environment) and automated failback (enabling not just disaster recovery, but also planned events such as maintenance and testing).
Imanis Data 3.0
Imanis Data 3.0 aims to differentiate its data backup and recovery offering by providing recovery of massive data sets at an estimated five to 10 times faster than other available offerings. The product also provides advanced security features, such as early detection of ransomware attacks.
CLOUD MANAGEMENT
WINNER:
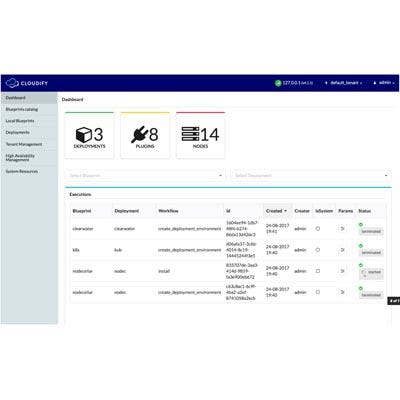
Cloudify 4.0
For enterprises with workloads in the cloud, Cloudify provides a platform to orchestrate, manage and automate application processes regardless of the cloud network's underlying complexity. While Cloudify has its roots as a DevOps tool, the launch of Cloudify 4.0 marks the product's arrival as a cloud management platform capable of complete application and network management. Key features in the 4.0 release include the introduction of multiple tenants in a single Cloudify Manager; clustering capabilities for multiple Cloudify Manager instances; and improved Lightweight Directory Access Protocol (LDAP) integration. The release also provides enhanced support for containers via the Kubernetes, Docker Swarm and Mesos orchestration platforms.

CLOUD MANAGEMENT
FINALISTS:
DH2i DxEnterprise v17
Using its Virtual Host technology, DH2i's DxEnterprise v17 release provides capabilities that enable workload portability between any hosts -- both for databases and containers. That simplifies management in part by decoupling instances and containers from their underlying infrastructures.

CLOUD STORAGE
WINNER:
HPE Nimble Cloud Volumes
As a new wave of applications move to the cloud -- placing increased demands on storage -- Hewlett Packard Enterprise's Nimble Storage offers enterprise-grade availability and performance not typically found in other cloud storage options. The offering, Nimble Cloud Volumes, also makes it easy for customers to switch between multiple clouds. The block solution enables businesses to use multiple clouds without getting locked into any of them, by storing data on Nimble flash storage and then tying the data to Microsoft Azure or Amazon Web Services. Nimble Cloud Volumes is also less expensive than other approaches to moving between multiple clouds, since data can be moved between cloud providers or moved back to an on-premises environment without data egress charges.

CLOUD STORAGE
FINALISTS:
Archive360 Archive2Azure
Built on Microsoft Azure Services, Archive360's Archive2Azure is an offering for dramatically reducing on-premises data storage and management costs while also meeting regulatory compliance requirements. The solution enables migration, collection, retention, and management of unstructured data in a secure and compliant format.
Igneous Hybrid Storage Cloud
With high-performance protection for large enterprises file systems, the Igneous Hybrid Storage Cloud offering provides data backup that runs without interrupting the work of end users -- while also delivering easy archiving and restoration of data.
Scality RING7
Scality's RING7 provides a multi-site file and object cloud with a focus on preventing security breaches, through advanced encryption and other features. The offering provides full control to users over where their data is stored and provides replication to the AWS S3 cloud.
WekaIO Matrix
WekaIO's cloud-native file system, Matrix, provides massive scalability along with flash-level performance. The software-based offering features a simple management interface, easy deployment, and a minimal utilization of Amazon Web Services compute instance resources so that more resources are available for running customer applications.

CONTAINER TECHNOLOGY
WINNER:
Platform9 Managed Kubernetes
As more enterprises gravitate toward containers, Platform9's Managed Kubernetes is a Software-as-a-Service offeirng that works across both public cloud and on-premises server infrastructure. The offering doesn't require the sort of operational overhead associated with other options, such as extensive monitoring and troubleshooting. It also provides a simplified approach to migrating and managing workloads in cloud environments, overcoming many of the obstacles faced by enterprises in adopting Kubernetes container orchestration. Ultimately, Platform9's Managed Kubernetes offering enables enterprise IT and DevOps teams to focus on tackling business problems, while helping to empower enterprises to establish multi-cloud deployments.

DATA CENTER INFRASTRUCTURE
WINNER:
HPE ProLiant Gen10
The latest generation of Hewlett Packard Enterprise's ProLiant server line, Gen10, excels in key areas such as security by creating a tight bond between the silicon and firmware. HPE develops and maintains its own firmware, and ties the firmware into custom silicon -- with the result being enhanced protection of the servers all the way from the production process to the customer's final location. Meanwhile, as part of Gen10, servers such as the popular HPE ProLiant DL380 add the latest in storage and memory technologies. Those include HPE's new persistent memory for improved scaling of high-performance computing workloads.
DATA CENTER INFRASTRUCTURE
FINALISTS:
APC by Schneider Electric Connected Smart-UPS
With Smart-UPS, APC is bringing together cloud capabilities with advanced uninterruptible power supply technology. The product allows users to stay up to date on the status of their UPS via a web-accessible portal, and enables customers to manage their UPS using an intuitive interface.
Dell EMC VxRail Appliance
Dell EMC's latest edition of its VxRail Appliance offers major enhancements around flexibility, scalability and performance. Dell EMC provides a massive number of new configurations for version 4.0 of the hyper-converged appliance, as well as increased flash storage and CPU performance.
NetApp FlexPod SF
With NetApp's FlexPod SF, users get the benefits of NetApp SolidFire all-flash, cloud-connected storage, combined with Cisco Unified Computing System B-Series servers and Cisco Nexus switching. The end result is an infrastructure offering that' ideal for supporting data-intensive workloads.
Pivot3 Acuity
Pivot3's Acuity brings an innovative design that enables users to provision and prioritize performance to each application, regardless of what's going on in the system. That means the end of unpredictable performance for applications or the need to configure the entire offering for a single workload.
DATA MANAGEMENT
WINNER:
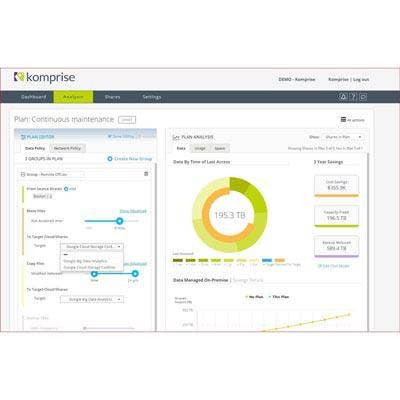
Komprise Data Management Grid
In contrast to the complexity and high cost of traditional data management options, Komprise's Data Management Grid is an offering for efficient, simplified management of data. It uses intelligent automation, scale-out architecture, and analytics-driven visibility across infrastructure in order to dramatically cut storage costs. The Data Management Grid works by archiving and replicating data to a cost-efficient cloud or object storage solution -- a process that doesn't require any proprietary interfaces or storage agents. Komprise also removes complexity through deploying as a virtual appliance without the need for hardware, as well as through removing the need for hard-to-manage central databases.

DATA MANAGEMENT
FINALISTS:
Actifio 7.1
With version 7.1 of Actifio's enterprise data-as-a-service offering, the company is providing simplified, highly scalable data management for Linux systems. Key capabilities include efficient backups, instant recovery and virtual data provisioning for massive databases. And the offering works for Linux systems across physical servers, virtual machines and public cloud.
Archive360 FastCollect for Archives
FastCollect for Archives from Archive360 offers data migrations that are accurate, efficient and secure -- and achieved quickly, too. The offering integrates with existing archive storage offerings and meets regulatory compliance requirements, while also allowing users to pay only for the resources they use.
NetApp Ontap 9.2
The latest version of NetApp's data management software, Ontap 9.2, adds advanced capabilities around management, acceleration and protection of data. Important new features include FabricPool, which offers automatic tiering of inactive data to the cloud, as well as expanded inline deduplication across storage pools.

DISPLAY – LCD/SIGNAGE/PROJECTION/GPU
WINNER:
Cisco Spark Board
Cisco's Spark Board is a collaboration display that integrates 4K cameras, microphones, voice-tracking technology, Spark APIs and an interactive whiteboard. Spark Board is available in 55-inch and 70-inch touch screen versions, and includes messaging, conferencing and telepresence capabilities. The product automatically connects to any laptop, PC, Mac or mobile device. And there's no Wi-Fi, network connection, or Bluetooth required, thanks to Cisco's ultrasound wireless pairing technology. In addition, no remote controls are needed, and the interactive whiteboard feature -- which includes a drawing pen -- can be accessed simultaneously by users in virtual rooms.
DISPLAY – LCD/SIGNAGE/PROJECTION/GPU
FINALISTS:
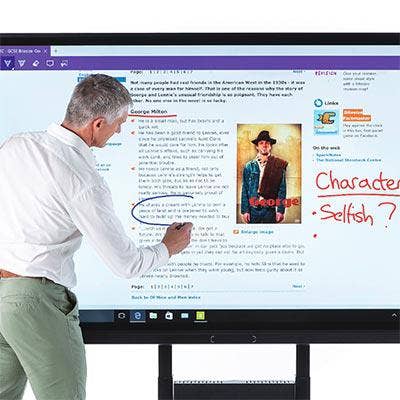
AVer CP754i Interactive Flat Panel
Aver's CP754i is a 75-inch interactive display featuring 4K resolution and running Android, with key verticals including K-12 education. The display easily connects with students' devices, and works with Aver's MyndShare software, which offers more than 70 teaching tools and apps.
Avocor F-7510
Avocor's F-7510 is a 75-inch interactive conferencing display that runs a full version of Windows 10, and is capable of working with any major unified communications or videoconferencing software. The 4K display is also integrated with Intel' Open Pluggable Specification, which allows users to easily get the latest computing technologies by plugging a new PC into the OPS slot.
LG Wallpaper OLED
LG's Wallpaper OLED is a 55-inch commercial display that provides superior picture quality -- with colorful, lifelike images and wide viewing angles. The display also weighs less than 13 pounds and offers flexibility with the option to mount it either vertically or horizontally.
INTERNET OF THINGS
WINNER:
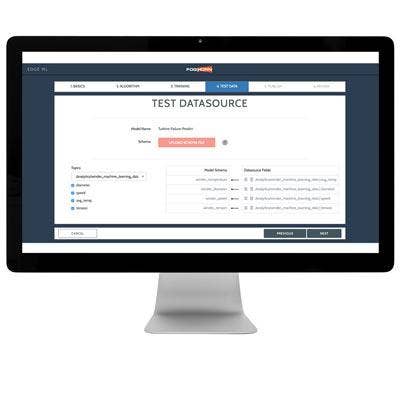
FogHorn Lightning ML
Lightning ML is FogHorn's industrial IoT software platform, providing integrated machine-learning capabilities, advanced analytics and universal compatibility across all major industrial IoT systems. The platform is aimed at enabling applications for on-premises edge use cases such as advanced monitoring and diagnostics, asset performance optimization, operational intelligence and predictive maintenance. Lightning ML works by pulling data from IoT sensors and operations technology systems, and then cleaning, formatting and sending the data in real time through FogHorn's complex event processing analytics engine. The systems-agnostic platform leverages commonly used ARM Cortex-A processors, thus supporting edge intelligence for the majority of industrial IoT environments.
I NTERNET OF THINGS
FINALISTS:
IBM Plant Performance Analytics
With Plant Performance Analytics, IBM offers advanced analytics for improving performance of manufacturing plants. The application works by predicting potential losses and productivity constraints -- identifying issues from the plant level down to the machine level -- and then prescribing remedies.
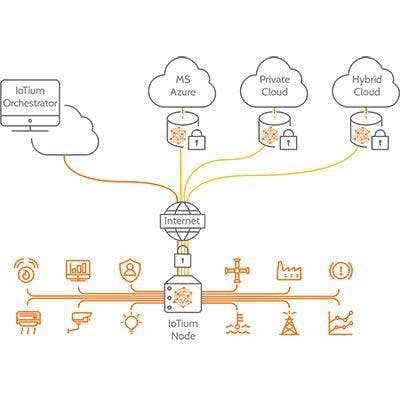
IoTium Network as a Service Solution
For industrial operations seeking remote connectivity -- securely and at a large scale -- IoTium's Network-as-a-Service solution leverages software-defined networking to solve connectivity issues. The solution connects legacy on-site systems to cloud-based applications for enabling improvements to efficiency, preventative maintenance and specialized analytics.
MapR Edge
Ideally, data from industrial IoT devices can be captured, processed and analyzed near where it's created -- which is exactly what MapR's Edge software enables. The software processes the data locally and aggregates insight for real-time business intelligence and improved decision-making.
Rigado IoT Gateway
Rigado's IoT Gateway is a highly customizable gateway offering, providing a range of wireless protocols, edge compute, and connectivity options to choose from. Users pay only for the capabilities they need, while the IoT Gateway offering also includes Rigado applications for device management and firmware updates.

MOBILE DEVICES
WINNER:
Samsung Galaxy Book
A 12-inch Windows tablet with a detachable keyboard, the Samsung Galaxy Book includes major upgrades over past Samsung 2-in-1 devices. The company has redesigned the keyboard cover for the Galaxy Book so that the keystrokes are deeper, the key pitch is wider, and the keyboard is now backlit. Samsung also stays true to its reputation for excellent displays with the bright and colorful Super AMOLED, FHD+ screen on the Galaxy Book. In addition, the tablet comes with a digital pen, and features plenty of horsepower with a seventh-gen Intel Core i5 processor and 8 GB of RAM.

MOBILE SOFTWARE
WINNER:
Capriza Platform's Universal Micro Apps Capriza's Universal Micro Apps software provides an easier-to-implement approach to creating mobile app solutions for enterprise workforces. The software uses pre-built workflows -- for common processes such as invoices and requisitions -- to bridge the gap between legacy business applications and mobile devices. The software stands out by enabling existing pieces of business app functionality to be quickly turned into simple "micro" apps, without a need for coding or APIs. Instead of taking all pieces of functionality that go together in a particular enterprise application and turning them into a mobile version, enterprises can use Universal Micro Apps to just create experiences for the pieces of functionality that are needed on mobile -- ultimately enabling businesses to accelerate key operations.

MOBILE SOFTWARE
FINALIST:
Kony AppVantage
AppVantage is Kony's solution for enterprise app creation and deployment, with options for choosing pre-built apps and components, as well as tools for quickly building custom apps with advanced features. The solution also enables apps to be modified down the road as new technologies emerge in areas such as chatbots and virtual reality.

MSP SOFTWARE
WINNER:
BitTitan MSPComplete
BitTitan's platform for powering delivery of managed services, MSPComplete, helps legacy partners convert their practices to capture cloud-based revenue streams. The platform includes migration and management tools used by solution providers, and the latest version adds a range of automation capabilities. MSPComplete works by streamlining projects and workloads, empowering partners to sell more Office 365, Azure, and complementary services; to more quickly on-board cloud products and workloads; and to better service customers with intelligent cross-sell/upsell reports and 24/7, white-label customer support. MSPComplete ultimately provides a cloud-based "business in a box" for channel partners that are looking to transition into becoming modern MSPs.

MSP SOFTWARE
FINALISTS:
Atera IT Management Platform
Atera's cloud-based IT Management Platform is focused on providing IT automation for MSPs, by bringing together remote monitoring and management (RMM), professional services automation (PSA), and remote access solutions. The result is that MSPs are empowered to improve service quality, cut costs and boost profits.
Pulseway
Pulseway offers IT monitoring and management software that's focused on meeting the needs of on-the-go IT administrators in the MSP and SMB markets. The software enables remote monitoring and management (RMM) of IT infrastructure -- including real-time status, system resources, logged-in users and network performance -- from any device.
NETWORKING – ENTERPRISE
WINNER:
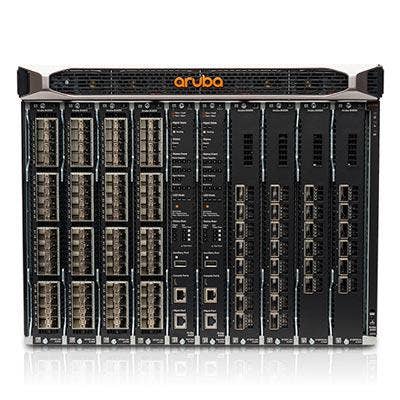
HPE Aruba 8400 Switch
The Aruba 8400 Core Switch, from Hewlett Packard Enterprise's Aruba Networks, brings automation and software intelligence to organizations looking for alternative options at the network core. The switch provides modern dynamic software capabilities for the enterprise network, developed specially for the changing traffic patterns created by cloud and mobile business applications. The Aruba 8400 Core Switch is powered by the new ArubaOS-CX operating system, which simplifies and automates many critical and complex network tasks. The 8400 is also fully programmable with a built-in Python interpreter and REST-based APIs for every function. Ultimately, the campus networking solution extends Aruba's advanced intelligence from the edge to the core.
NETWORKING – ENTERPRISE
FINALISTS:
128 Technology - 128T Networking Platform
The 128T Networking Platform from 128 Technology is a software-based, distributed routing solution geared toward enterprises with complex networks. The platform uses secure routing to simplify network architectures; provides end-to-end control and visibility without disrupting existing infrastructure; and enables customers to build networks that are session-based, software-defined and services-centric.
Cisco Catalyst 9300 Series Switches
With the Catalyst 9300 Series Switches, Cisco delivers enhanced security, programmability and performance via custom ASICs and software layers. The switches work in tandem with Cisco's recently introduced Network Intuitive platform, a networking system that anticipates actions, stops security threats, and continues to evolve and learn.
LogicMonitor LM Config
LM Config is LogicMonitor's offering for service providers looking to integrate configuration monitoring and management with infrastructure monitoring. The offering provides users with automated alerting on device configuration changes, for improved visibility and compliance even inside highly distributed environments.
Ruckus Multi-Gigabit Networking Solution
To address connectivity issues and maximize network access performance, Ruckus launched its Multi-Gigabit Networking Solution, which integrates a Wave 2 wireless access point and network switch with 2.5 GbE multi-gigabit connectivity. The solution is ideal for high-density environments such as enterprise and hospitality settings.
NETWORKING – WIRELESS
WINNER:
HPE Aruba Asset Tracking
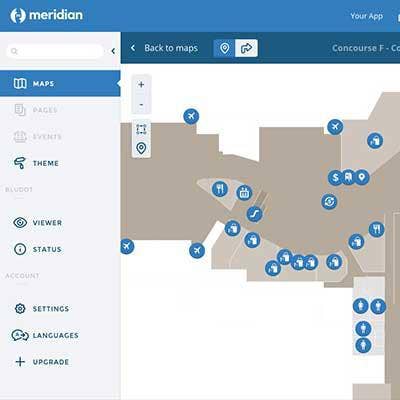
HPE Aruba's Asset Tracking offering provides location-based tracking of assets, with major benefits around ease of use, functionality and price performance. It includes new Bluetooth Low Energy tags, an asset tag configuration application, and advancements in the ArubaOS software. Organizations can track assets -- such as chairs and IV pumps -- using either a map-based mobile app or by integrating with existing tracking solutions. The offering also includes new features for the Meridian AppMaker, such as a new SDK and APIs for third-party integration, allowing customers to create their own tracking app for iOS or Android. Notably, the offering is fully integrated into Aruba Networks' wireless infrastructure, eliminating the need for a separate network.
NETWORKING – WIRELESS
FINALISTS:
Cradlepoint NetCloud
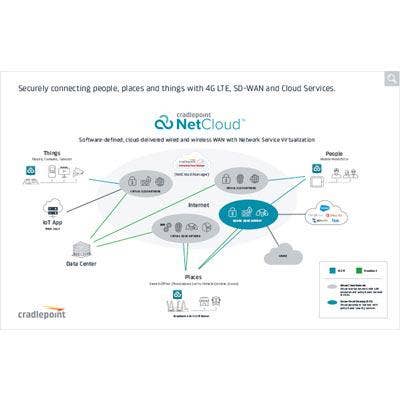
Cradlepoint's software-defined, cloud-delivered NetCloud platform enables enterprises to build, deploy and manage a WAN in simplified fashion. The platform powers LTE-enabled routers that are aimed at markets such as IoT, transportation and small branch locations.
Datto Networking Appliance
For MSPs serving SMBs, Datto's Networking Appliance serves as a routing and firewall platform with advanced features. Along with high-performance network edge routing and firewall, capabilities include Wi-Fi, intrusion detection and prevention, traffic shaping and LTE failover.
Extreme Networks WiNG AP 7612
With the WiNG AP 7612, Extreme Networks offers an enterprise-grade indoor access point with Wave 2 Wi-Fi connectivity, easy installation, and a wall plate form factor. Focused on the hospitality segment, key features include network application visibility analytics and management of bandwidth based on guest application requirements.
Zyxel Wall-Plate Unified AP
Zyxel's Wall-Plate Unified AP is a Wave 2 access point that uses smart antenna and beamforming technologies to provide users with easy accessibility to fast wireless service, with data speeds of up to 1.2 Gbps. Targeted at multi-unit buildings such as offices and hotels, the access point is also designed to be low-profile with mounting options on wall plates, walls or desks.

NETWORKING – VOICE/DATA/UC
WINNER:
Cisco Business Edition 4000
Designed for small businesses, Cisco's Business Edition 4000 is an office IP phone system aimed at enabling easy management and savings on communications costs. The phone system is fully managed via the cloud and comes with the option of pre-configuration prior to shipment. In addition, the Business Edition 4000, which supports up to 200 devices, is typically installed by partners in less than a day. Tools for IT administrators provide simplified management for tasks such as adding new users and phones. Customers can also reuse their Cisco IP phones if their business grows and they need to upgrade to a larger Business Edition platform or migrate to Cisco Spark.
NETWORKING – VOICE/DATA/UC
FINALISTS:
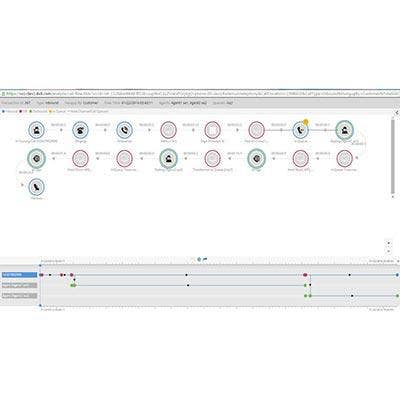
8x8 Virtual Contact Center
For organizations looking to manage a distributed team of agents, 8x8's Virtual Contact Center offering provides advanced contact center capabilities, workforce optimization, business phone and collaboration services, and unified communications. The cloud-based offering ultimately enables business continuity and customer service resiliency across locations.
Sennheiser MB 660
Sennheiser's MB 660 is a wireless, noise-canceling headset with a touchpad integrated into the right earphone. Features include the ability to halt the noise-canceling function with a double tap on the earphone. In addition, the noise cancellation automatically adjusts to the level of ambient noise that's happening around the user.

PC – LAPTOPS/CONVERTIBLES
WINNER:
HP EliteBook x360
The HP EliteBook x360 is a 2-in-1 notebook built with the needs of the business power user in mind. Along with a foldable touch-screen display, key features include long battery life (up to 16.5 hours on a charge); a premium touchpad and keyboard; and a range of work-friendly ports (USB-A, HDMI, USB-C, microSD, smart card reader). The 13.3-inch laptop is also just about as thin as possible -- 0.59 of an inch thick -- hile still having room for those ports. Other business-friendly elements include security features such as HP's self-healing Sure Start technology, as well as dedicated keys for launching Skype for Business and other collaboration functions.

PC – LAPTOPS/CONVERTIBLES
FINALISTS:
Acer Chromebook Spin 11
The Chromebook Spin 11 from Acer offers both student-ready ruggedness along with a convertible 11.6-inch touch-screen display. Durability features include military-standard drop protection and a spill-resistant keyboard, while the Chromebook also comes with a Wacom digital stylus.
Lenovo ThinkPad X1 Yoga
With the second-generation model, Lenovo's ThinkPad X1 Yoga remains the only 14-inch OLED notebook available. The latest X1 Yoga adds seventh-generation Intel Core processors and two Thunderbolt 3 ports, while the convertible touch-screen laptop can also be used with the re-designed ThinkPad Pen Pro.
Panasonic Toughbook 33
Key features of Panasonic's Toughbook 33 rugged laptop include a 12-inch display that's aimed at easier use on-the-go. The screen comes with a 3:2 aspect ratio, which enables a larger viewing area, while the display also detaches from the keyboard for use as a tablet.

PC – SERVERS
WINNER:
Dell EMC PowerEdge R740
Designed to serve as the workhorse of the PowerEdge line, Dell EMC's PowerEdge R740 is aimed at environments where flexibility, storage and I/O performance are key. The R740 features up to three 300W accelerator cards in a 2U, 2-socket system, with Intel Xeon Scalable processors providing massive horsepower. Features include integration with the OpenManage Power Center, a systems management tool that enables data center operators to monitor and track power consumption by virtual machine. The R740 also offers storage performance and density for applications such as software-defined storage, and is ideal for cloud service providers, big-data users and co-location hosting.

PC – SERVERS
FINALIST:
Lenovo ThinkSystem SR950 Server
With the ThinkSystem SR950, Lenovo is offering an enterprise rack server designed for workloads requiring high performance, uptime, and I/O capability. The server supports Intel Xeon Scalable processors, 12 TB of memory, 24 storage bays, 19 I/O card slots and advanced RAS capabilities.

PC – WORKSTATIONS/DESKTOPS/AIOS
WINNER:
IGEL UD Pocket
The UD Pocket is IGEL's paper clip-size, universal desktop thin client aimed at enabling productivity with mobile workforces. The UD Pocket allows users to boot from IGEL Universal Desktop or the local operating system on a PC, laptop, or other compatible endpoint. The micro client device connects to the internet via the IGEL Cloud Gateway, then automatically integrates into the company's endpoint management software -- the IGEL Universal Management Suite. That provides growing organizations with the ability to unify the management of all end-user devices in one place, and manage those devices with a simple drag-and-drop interface.

PC – WORKSTATIONS/DESKTOPS/AIOS
FINALISTS:
Dell Wyse 3040
With the Wyse 3040 thin client, Dell has introduced its smallest and lightest desktop virtualization endpoint so far, with a weight of 0.53 of a pound. The Wyse 3040 also provides improved performance as the first entry-level thin client to include Intel's Atom X5 quad-core processor.
Lenovo ThinkStation P320 Tiny
Dubbed "the world's smallest workstation" by Lenovo, the ThinkStation P320 Tiny weighs less than three pounds while supporting up to seventh-generation Intel Core i7 processors, up to 32 GB of RAM, Nvidia Quadro P600 graphics, and connections to up to six displays.
PRINTING & IMAGING
WINNER:
HP A3 PageWide
HP's new line of copier-size A3 PageWide printers bring together advanced functionality with reduced costs for color and a design aimed at empowering managed print services. The A3 PageWide lineup includes proven HP security capabilities for monitoring threats, detecting intrusions and validating operating software. The printers also offer impressive speed with up to 60 pages per minute for professional printing and up to 80 pages per minute for general office printing. Along with providing low-cost color printing thanks to the PageWide technology -- which enables reduced costs for supplies and power -- the HP A3 PageWide line requires less maintenance than other printers in its class, thanks to the inclusion of fewer parts in the printers.

PRINTING & IMAGING
FINALISTS:
Epson WorkForce Enterprise WF-C20590
The WorkForce Enterprise WF-C20590 features print speeds of up to 100 pages per minute for simplex printing, which Epson says makes the printer the fastest in its class. The MFP also includes a simpler design than comparable laser printers, meaning that it needs to be serviced less frequently.
Xerox VersaLink C405
Along with color or black printing speeds of up to 36 pages per minute, the Xerox VersaLink C405 multifunction printer comes with useful features for mobile device connectivity (such as Wi-Fi Direct and NFC tap-to-pair) and cloud connectivity (with native apps for uploading to Google Drive, Microsoft OneDrive and Dropbox).

SECURITY - CLOUD
WINNER:
Cisco Umbrella
Cisco Umbrella is a cloud-delivered security platform that serves as the first line of defense to protect employees both on and off the corporate network. The Secure Internet Gateway provides customers with safe access to the internet anywhere that users go, even when they're not on the virtual private network. Cisco Umbrella halts current and emerging threats over all ports and protocols, while blocking access to malicious domains, URLs, IP addresses and files before a connection is established or a file downloaded. Ultimately, Cisco Umbrella protects enterprises as mobility increases and as cloud services are adopted.
SECURITY - CLOUD
FINALISTS:
Armor Anywhere
Armor Anywhere is a solution to provide data security across all varieties of infrastructure, including cloud infrastructures from Amazon Web Services and Microsoft Azure. Capabilities include managed security, visibility, controls, threat intelligence, patch monitoring, log management, malware protection, file integrity monitoring and external vulnerability scans.
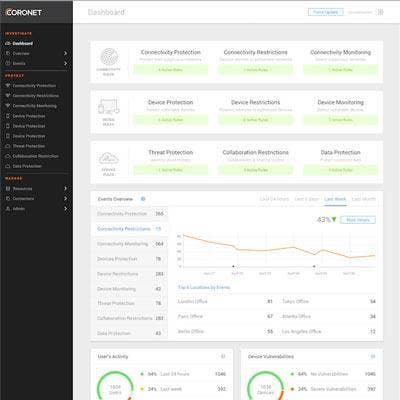
Coronet SecureCloud
Featuring support for more than 100 cloud services, including Office 365 and Salesforce, Coronet's SecureCloud automatically controls which applications, activities, and data that users that are allowed to access. The solution works by continuously identifying risks and threats in users' behavior, as well as devices and networks in use.
RedLock Cloud 360
RedLock's Cloud 360 platform offers a new way for companies to see what's inside their cloud infrastructure, providing a common control point for workload discovery, continuous monitoring and cloud forensics. Companies can use the solution to detect anomalies, perform risk scoring and compliance reporting and set security controls.
SECURITY - ENDPOINT
WINNER:
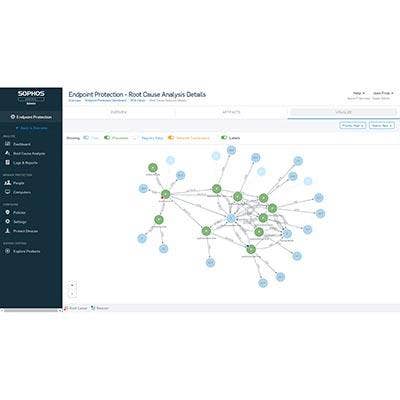
Sophos Intercept X
Sophos has extended its next-generation endpoint security portfolio with Intercept X, an offering to provide added detection, protection, and remediation capabilities to partners and customers on the endpoint. Intercept X can be sold as an add-on to existing Sophos offerings or independently. It offers signature-less threat and exploit detection; CryptoGuard anti-ransomware capabilities to both block and remediate ransomware; root cause analysis to map attacks and provide recommendations for future; and Sophos Clean to clean up spyware and malware in an environment. Among the recently added features is ransomware protection for Windows servers, along with prevention of attacks that target the master boot record and volume record.
SECURITY - ENDPOINT
FINALISTS:
CrowdStrike Falcon Platform
Recent enhancements to CrowdStrike's flagship Falcon offering add new capabilities for machine learning and advanced endpoint protection. New features include CrowdStrike Falcon Prevent for behavioral analytics-based anti-virus replacement, as well as CrowdStrike Falcon Discover for monitoring of privileged user accounts and application usage.
CylanceProtect Home Edition
Though targeted at consumer security with features such as artificial intelligence to block unknown variants of malware, CylanceProtect Home Edition is sold through the channel with the same margin structure as the CylanceProtect corporate version, according to Cylance. That gives partners a broader portfolio to offer to customers from Cylance, the company said.
McAfee Dynamic Endpoint Threat Defense
With Dynamic Endpoint Threat Defense, McAfee provides a comprehensive context of potential threats along with single-click remediation. The offering uses insight aggregated from multiple sources and the combination of malware signatures, real-time reputation scoring, application containment, and machine-learning and EDR capabilities.
Palo Alto Networks Traps 4.0
In contrast to traditional endpoint protection approaches -- which involve detecting and responding to security incidents after a breach has occurred -- Palo Alto Networks' Traps 4.0 is a multi-method prevention offering that pre-emptively blocks both known and unknown cyberthreats from compromising endpoints.
SECURITY - IDENTITY MANAGEMENT
WINNER:
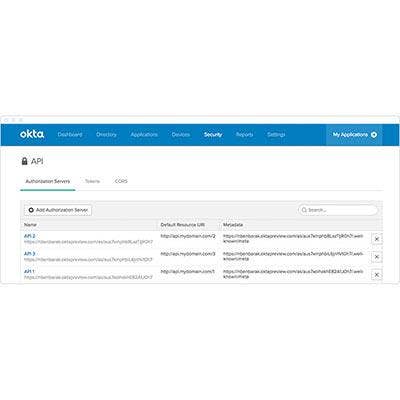
Okta API Access Management
Okta's API Access Management solution sets itself apart by managing access based on the user, group membership, network zone or device -- rather than by application. Integrated into the Okta One Identity cloud, the offering allows for the creation, maintenance and audit of API access policies. The offering includes OAuth 2.0 API authorization along with an identity-driven policy engine, centralized control across APIs, and integration with other API management offerings (including Mulesoft and Apigee). Ultimately, the offering positions Okta and its partners to take a hand in the digital transformation of customers -- both by offering new web and mobile application experiences with back-end integration, and/or by selling access to core APIs and services.

SECURITY - IDENTITY MANAGEMENT
FINALISTS:
BeyondTrust PowerBroker
With the PowerBroker Privileged Access Management Platform, BeyondTrust brings together capabilities that other vendors offer as individual tools as a way to enable visibility and control over all privileged accounts and users. Benefits of the approach include simplified deployments, lower costs and reduced privilege risks.
Ivanti Identity Director
Using a central identity warehouse that determines an employee's identity from existing systems, Ivanti's Identity Director enables IT to automatically deliver services to individuals as needed, while also supporting employees to use self-service with automated workflows.
One Identity Safeguard 2.0
One Identity's Safeguard 2.0 brings automation and control to the process of granting access to privileged accounts, with capabilities to provide access to the password itself or to enable privileged access through a session with full recording and replay.

SECURITY - IOT
WINNER:
ForeScout CounterAct
Using its pioneering agentless approach to IoT security, ForeScout's CounterAct provides visibility and control of devices as soon as they connect to the network. CounterAct provides a broad range of network access controls for IoT, automating policy-based access control as well as enforcement of devices, users, and applications. The offering enables organizations to limit access to appropriate resources, automate guest on-boarding, find and fix endpoint security gaps, and meet regulatory compliance requirements. Recent enhancements to CounterAct include a new user interface, enhanced scalability and resiliency, and customized classification of devices -- which works across IoT, OT, mobile and virtual endpoints.
SECURITY - IOT
FINALISTS:
Armis IoT Security Platform
Armis offers an agentless IoT security platform that lets enterprises see and control any device or network. The platform -- which integrates with existing IT infrastructure -- offers capabilities such as stopping devices from connecting to an inappropriate network, regardless of whether those devices are managed by IT or not.
Claroty Platform
Claroty offers a security platform that provides protection for granular operational technology network elements in industrial workplaces. The platform enables engineers and operators to protect their OT networks using measures such as monitoring, alerting and management for factory floors.
CyberX ICS Attack Vector Prediction
CyberX's Industrial Control System Attack Vector Prediction technology helps industrial companies predict and prevent security attacks as they connect their operational technology to the Iiternet. The tool works by validating precisely which mitigation measures -- such as network zoning or stronger authentication -- can eliminate the highest-risk attack vectors.
ZingBox IoT Guardian
ZingBox's IoT Guardian is a detection tool that works by understanding each IoT device's "personality." The tool leverages machine-learning capabilities to discover and assess risk and baseline normal behavior, detect anomalous activities, and provide real-time monitoring across customers' IoT devices.

SECURITY - MOBILE
WINNER:
Samsung Knox 2.9
Key updates in Knox 2.9, the latest edition of Samsung's mobile security platform, serve to the enhance the protection of personal data and device features. Among the new capabilities are remote backup to the user's Secure Folder (enabling users to access or wipe the Secure Folder's data if the device is lost) and App Permission Monitor (for getting notifications when background apps try to access the camera, microphone, video recorder or SMS). Meanwhile, Knox 2.9 includes an updated Customization SDK to assist developers with creating vertical-specific apps for Samsung devices.

SECURITY - MOBILE
FINALIST:
Zimperium Advanced App Analysis
Advanced App Analysis is Zimperium's solution for rating mobile apps on privacy and security risk. The solution works by using a parallel processing engine to collect and correlate data from numerous sources, and then performing multivariate tests and validations to proactively generate intelligence around app risks.
SECURITY - NETWORK
WINNER:
RedSeal Platform
RedSeal's network modeling and risk-scoring platform enables customers to create a unified model of their complex network, which can include on-premises, cloud and virtualized environments. The platform provides a detailed understanding of the current state of a company's hybrid data center while enabling queries across all individual networks. A recent update of the platform expanded integrations with products including Splunk's Enterprise Security SIEM, Rapid7's Nexpose vulnerability management software, and ForeScout's IoT-focused CounterAct solution. RedSeal also unveiled the expansion of its platform with the ability for modeling of software-defined networks in VMware NSX and Amazon Web Services Virtual Private Clouds.

SECURITY - NETWORK
FINALISTS:
Cisco Stealthwatch
As large enterprises expand their digital networks, Cisco's Stealthwatch enables improved visibility and security by collecting and analyzing network infrastructure data to uncover possible cyberattacks. Stealthwatch also integrates with the Cisco Identity Services Engine to pinpoint the exact user and device responsible for anomalous network activities.
Infoblox ActiveTrust Suite
With its ActiveTrust Suite, Infoblox automatically stops insecure device communications using command-and-control methods. The offering, which collects and distributes threat intelligence to remediate and prevent attacks, halts DNS-based data exfiltration by leveraging streaming analytics and machine learning.
Juniper Sky Advanced Threat Prevention
Recent enhancements to Juniper Networks' Sky Advanced Threat Prevention made the cloud-based threat detection and prevention offering available on the vSRX Virtual Firewall as well as across Juniper's SRX Series Services Gateways -- thus allowing partners to extend their malware protection across virtual and physical firewalls.
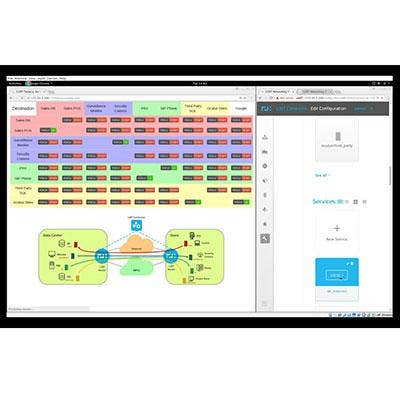
ProtectWise Grid
The ProtectWise Grid provides capabilities such as visibility and automated threat detection by bringing the advantages of the cloud to network security. Cloud-enabled features include an unlimited retention window and automated retrospection--as well as fast, highly scalable deployment.
SECURITY - THREAT ANALYTICS
WINNER:
Exabeam Security Intelligence Platform
Exabeam's Security Intelligence Platform extends the company's user behavior analytics offering to disrupt the legacy SIEM (security information and event management) market. The offering includes five products: Exabeam Log Manager, Exabeam Advanced Analytics, Exabeam Incident Responder, Exabeam Threat Hunter, and Exabeam Cloud Connectors. Combined, the products transform Exabeam into an SIEM replacement -- although the platform distinguishes itself from traditional SIEM offerings by allowing for unlimited security data collection, and by supplementing log collection with analytics and incident-response capabilities. Exabeam's Security Intelligence Platform is aimed at the midmarket, while most legacy SIEM vendors focus on the enterprise.

SECURITY - THREAT ANALYTICS
FINALISTS:
Illusive Core Solution
In situations where cyberattackers are successful at penetrating an organization's defenses, the Illusive Core Solution can intervene to prevent further damage with deception technology. Illusive's deceptions lure attackers to activate fake objects inside the system, then collect data that can be used to determine the most effective actions to take in response.
IntSights Threat Intelligence
IntSights' advanced threat intelligence platform brings together threats from across the Iiternet, then uses machine learning and artificial intelligence to deliver both tailored and generic threat intelligence to enterprise security analysts. This approach vastly improves the consumption of threat intelligence for businesses, according to the company.
RiskLens Cyber Risk Quantification Suite
With the Cyber Risk Quantification Suite, RiskLens offers a cyber risk analytics platform with capabilities spanning environment modeling, risk scenario development, simulations, and generation of risk analytics reports. The platform brings together features including risk scoping, data input and calibration, and a quantitative analysis engine.
ThreatQuotient ThreatQ 3.1
ThreatQuotient's ThreatQ 3.1 platform aims to serve as a highly relevant source of threat intelligence, thanks to features such as The Threat Library (which automatically prioritizes threat data); The Adaptive Workbench (which enables analysts to erich data); and The Open Exchange (which can export the platform's data to third-party tools).

SECURITY - WEB/EMAIL/APPLICATION
WINNER:
Mimecast Internal Email Protect
Mimecast's recent expansion of its email protection portfolio adds crucial new capabilities to protect against threats from internally generated emails, a fast-growing security risk for companies. Mimecast Internal Email Protect, part of the Targeted Threat Protection (TPP) service portfolio, introduces features to detect and remediate email threats that start from an internal email source. These capabilities are necessary to protect against social engineering and CEO spoofing attacks, as well as compromised accounts or insider threats. Mimecast Internal Email Protect is an add-on subscription to existing TPP licenses, which offers the opportunity for partners to generate additional subscription revenue.
SECURITY - WEB/EMAIL/APPLICATION
FINALISTS:
Aqua Container Security Platform
With the Aqua Container Security Platform, DevOps and security teams are empowered to bake security into their application delivery life cycle, rather than having to bolt it on later. The platform thus allows for embedding and automating security controls throughout the development process, as soon as container images are pulled from a registry.
Barracuda Sentinel
Powered by an advanced artificial intelligence engine, Barracuda Sentinel protects against spearphishing attacks and cyber fraud in Office 365 (which doesn't have native security features to stop such attacks). The offering works by learning the unique communication patterns of each organization, and then blocking spearphishing attacks in real time.
Twistlock 2.1
Aimed at securing containers from advanced threats, Twistlock 2.1 includes features such as a cloud native app firewall that automatically protects customers' apps -- without customers needing to change the way the apps are built or run. The offering also provides enterprises with a view of the largest security risks in their unique environment.
SOFTWARE – ENTERPRISE MANAGEMENT
WINNER:
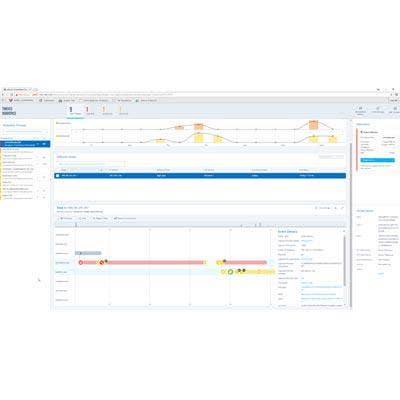
Turbonomic 5.9
With Turbonomic 5.9, the company says its offering is the only software platform to provide workload monitoring and automation across on-premises and public cloud environments in real time. Turbonomic 5.9 lets customers see all of their workloads simultaneously regardless of whether they're on-premises, or in Amazon Web Services or Microsoft Azure environments. The latest release also automatically scales public cloud workloads; optimizes resources in real time to make sure applications get exactly the resources they need; and enforces compliance policies across hybrid cloud environments. In addition, the new platform addresses cost by adding budget control, cost forecasting and cost-management capabilities.
SOFTWARE – ENTERPRISE MANAGEMENT
FINALISTS:
Cisco Digital Network Architecture Center
A key piece of Cisco's recently debuted Network Intuitive platform, the Digital Network Architecture Center provides solutions for transitioning customers to an intent-based networking approach for their systems. Benefits include faster alignment with business needs, lower costs, and improved security as a result of segmentation and prioritization.
HPE OneView 3.1
With version 3.1 of Hewlett Packard Enterprise's OneView IT infrastructure management software, the offering now enables IT teams to control resources through a unified API for easier integration with workflow orchestration and management tools. Overall, OneView 3.1, which supports HPE's Gen10 servers, brings improved automation and streamlining to compute, storage and fabric resources.
Splunk IT Service Intelligence 2.4.1
Splunk's IT Service Intelligence 2.4.1 brings improvements to the monitoring of IT services using machine data, with capabilities to provide deep insight about the health and performance of services in real time. The offering detects root causes and pinpoints areas of impact using Splunk's advanced analytics, powered by artificial intelligence and machine learning.
Samsung Knox Configure
Starting with the Galaxy S8 and S8 Plus smartphones, Samsung debuted its cloud-based Knox Configure service, which offers over-the-air bulk configuration of devices to businesses. For enterprises that wants users in the field to share the same configuration and setup process on their device, Knox Configure allows for that level of control.
SOFTWARE – IT AUTOMATION
WINNER:
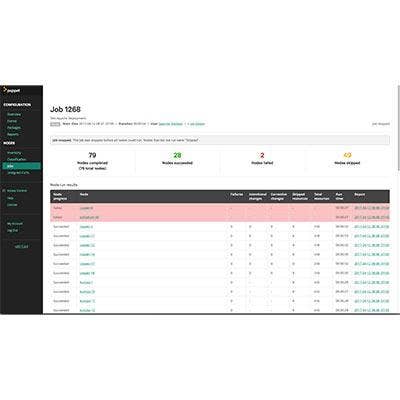
Puppet Enterprise 2017.2
Puppet's software brings IT infrastructure automation to the enterprise by using a common language for defining applications and infrastructure -- leading to a standard way to manage all infrastructure such as private and public cloud, containers, storage and networking. Key capabilities include automatic delivery, updating, monitoring and security of applications. With Puppet Enterprise 2017.2, new features include package inspection, which gets users up and running with automation more quickly, by uncovering packages that ought to be managed automatically. Another new capability, visual orchestration workflows, let users orchestrate deployments of infrastructure and applications from inside Puppet Enterprise's web user interface.
SOFTWARE – IT AUTOMATION
FINALISTS:
Red Hat Ansible Tower
The focus of Ansible Tower, Red Hat's agentless IT automation platform, is on enabling improved management of IT systems as well as optimized deployments. The offering -- which adds control, security and delegation capabilities -- can automate repetitive tasks using a simple language that anyone on an IT team can understand.
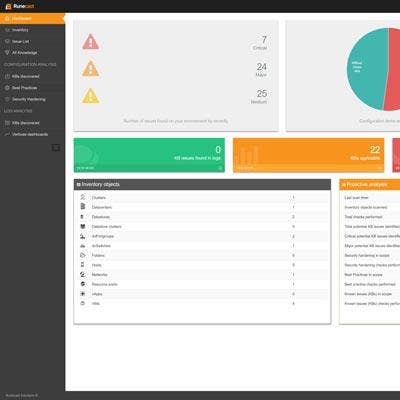
Runecast Analyzer 1.5
Runecast Analyzer is an automated solution for proactively monitoring VMware environments and correlating the findings with resources such as the VMware Knowledge Base and Security Hardening Guide. The result is that virtual infrastructure stays optimized, secure, and compliant -- ultimately reducing service outages and troubleshooting.

STORAGE
WINNER:
Pure Storage FlashArray//X
FlashArray//X from Pure Storage is a 100 percent NVMe all-flash array for the enterprise market, with capabilities to help meet the high performance required by web-scale applications and advanced analytics. Innovations underpinning the FlashArray//X solution include new Purity DirectFlash Software, which implements global flash management with higher performance and improved flash utilization; in-house-designed NVMe DirectFlash Modules that make all of a module's flash available to the FlashArray; and //X70 Controllers that provide NVMe communication within the FlashArray's midplane and chassis. Ultimately, FlashArray//X is ideal for improving the performance of mission-critical databases and flash deployments, and for consolidation of Tier 1 applications.
STORAGE
FINALISTS:
Dell EMC VMAX 250F
Targeted at providing enterprise-class features at midmarket prices, Dell EMC's VMAX 250F provides high availability, low latency and flash performance with a minimal footprint. Achievable performance reaches more than 1 million IOPS, and the solution offers enhanced storage efficiency using inline compression and data-reduction capabilities.
IBM DS8886F
With low response times and high availability (99.9999 percent), as well as strong performance (570,000 IOPS), IBM's DS8886F is ideal for mission-critical environments. The offering is based on the IBM Power Systems server, and IBM says its storage and mainframe teams collaborated over several years to develop it.
Intel Optane
Aimed at dramatically improving system responsiveness, Intel's Optane memory technology leverages the company's 3D XPoint memory technology -- NVMe that fits between higher-performance but expensive DRAM memory and lower-cost NAND technologies. Optane offers five to eight times the performance of NAND SSDs, with up to 60 times lower latency.
VMware vSAN 6.6
Improved security, cost efficiency and performance are three of the major IT priorities met by VMware's vSAN 6.6 release. The version is the first to include native hyper-converged infrastructure security, and adds a number of new analytics and site protection features while boosting performance by up to 50 percent over past releases.
EDITOR'S CHOICE
The Editor's Choice awards for 2017 honor two vendors whose innovations do not fit neatly underneath any of the categories in the contest -- a cybersecurity platform that cuts across security categories and a processor series that's sure to underpin many other technology advancements in the future. We felt they were deserving of an award for their work in pushing the envelope in crucial areas of IT.
WINNERS:
FireEye Helix
With the Helix platform, FireEye brings together its security products under a single, integrated platform -- a move that helps partners move away from point solutions to provide an overall better security outcome. The platform combines FireEye's network, endpoint, threat analytics, advanced threat intelligence, and Security Orchestrator offerings into a unified system with a single user interface. From there, customers can also add email, FireEye-as-a-Service, and additional threat intelligence and orchestration capabilities, as well as integrate third-party threat intelligence streams and alerts. In addition, FireEye distinguishes itself with substantial automation capabilities, along with threat intelligence from Mandiant and iSight.
Intel X-series
Intel this year unveiled a new desktop processor family, the X-series, offering dramatically enhanced performance. Leading the lineup is the Core i9 processor, which features 18 cores and 36 threads at the very top level (the Core i9 Extreme Edition 9-7980XE). Intel is also offering four lower tiers of Core i9 processors, ranging between 10-core and 16-core versions. Ultimately, Intel said the Core X lineup packs up to 10 percent faster multi-thread performance over its previous generation of chips. Meanwhile, Intel also introduced Core i7 X-series processors, such as an eight-core, 16-thread model, along with a quad-core, eight-thread model.