Apple, Hackers And MSPs: 5 Questions With Addigy CEO Jason Dettbarn
Dettbarn, whose company specializes in Apple device management software, speaks with CRN about the recent iMessage exploit, Apple’s product announcements this week and Addigy’s expanded efforts with managed services providers.

Eye On Apple
In a busy week for Apple news, Addigy CEO Jason Dettbarn shared his perspective with CRN on the iMessage exploit that Apple patched on Monday and the announcements at Apple’s fall product event Tuesday. Miami-based Addigy is a maker of Apple device management software that covers Apple operating systems including macOS, iOS and iPadOS. The company has been growing fast thanks both to rising demand for Apple devices in businesses and to Addigy’s differentiators, such as capabilities to remotely push out configurations to Macs—a popular feature for hybrid workforces. “We’ve had our fourth consecutive record quarter in a row—breaking new records every quarter,” Dettbarn told CRN on Wednesday. “A key part of that is expansion with the MSP side of the house.”
To accelerate Addigy’s growth, the company in August announced a partnership with cloud-focused distributor Pax8. Speaking to CRN, Dettbarn discussed the push with managed services providers and Pax8 in addition to weighing in on the latest Apple news from the past week. He also offered his view at what’s coming next from Apple with the expected launch of M1X-powered MacBook Pro models within weeks.
What follows are Dettbarn’s comments on those topics shared with CRN.

Should the iMessage vulnerability be a concern for more than just specific targeted individuals?
It’s “guaranteed” that there are wider implications beyond just the impact on certain individuals who’ve been identified as targets, Dettbarn said.
On Monday, Apple released patches for iPhone, iPad and macOS devices that address an iMessage vulnerability reportedly used by spyware maker NSO Group. The Citizen Lab at the University of Toronto reported discovering the zero-day, zero-click iMessage exploit—which the research group says was used by NSO Group to infect a Saudi activist’s iPhone with its Pegasus spyware.
In a statement provided to CRN on Monday, Ivan Krstić, head of security engineering and architecture at Apple, confirmed that the exploit affected iMessage. However, Krstić’s statement indicated that this type of attack is “not a threat to the overwhelming majority of our users.”
“Attacks like the ones described are highly sophisticated, cost millions of dollars to develop, often have a short shelf life, and are used to target specific individuals,” Krstić said in the statement.
Dettbarn said he believes the exploit potentially has a broader impact, however.
“Nobody knows the full trajectory of these active exploits, because it’s never fully disclosed. And the proliferation of how to leverage the exploit goes out there very, very quickly,” Dettbarn said. It’s “absolutely not” just NSO Group that has likely made use of this iMessage vulnerability, he said.
“It’s always an ‘iceberg’ – what we see is just 10 percent of it. Anybody who thinks differently is just not wanting to look [deeper] into that,” Dettbarn said.

Could the redesigned iPad Mini find increased traction with businesses?
With the features included in the new iPad Mini, “that starts to break open even more [business] use cases for sure,” Dettbarn said.
For the sixth-gen model of the compact-size iPad, the display size has been increased to 8.3 inches, up from 7.9 inches previously. The iPad Mini form factor is not getting any larger, though, thanks to a reduction in the bezels around the display.
Apple is also introducing 5G support for the first time with the new iPad Mini, and the tablet is getting a major performance boost with the inclusion of the same processor as in the iPhone 13 — the A15 Bionic. The chip will offer a 40-percent increase in CPU performance along with 80-percent faster graphics for the iPad Mini, Apple said.
“We are always seeing new use cases for the iPad in business,” Dettbarn said—and the new iPad Mini should only further that. The combination of the portable form factor with boosted performance and 5G connectivity could make a stronger appeal to businesses, he said.

Do you think Apple has put more into the iPhone 13 Pro models than usual on the Pro models?
That does appear to be the case, Dettbarn told CRN. Apple saved many of the biggest upgrades for 2021 for its pro-level iPhone models—the iPhone 13 Pro and iPhone 13 Pro Max. For starters, the smartphones will major display update that has been long requested—a 120Hz refresh rate for smoother display motion. The models are also configurable with up to a massive 1 TB of internal storage (up from a maximum of 512 GB previously) and will include faster graphics and longer battery life than the standard iPhone 13.
While there were no “exponential” updates with the iPhone 13 Pro lineup, the range of updates for the Pro models represented a bit of a departure from past years, Dettbarn said. Previously, “the Pro iPhones were always viewed as ‘a better camera,’ and not much more than that,” he said.
Of course, the triple rear camera system on the iPhone 13 Pro models will also get some major updates, Apple announced Tuesday. The updates include a larger Wide sensor and larger aperture on the Wide camera—enabling up to a 2.2X improvement in low-light environments—as well as a wider aperture on the Ultra Wide camera.
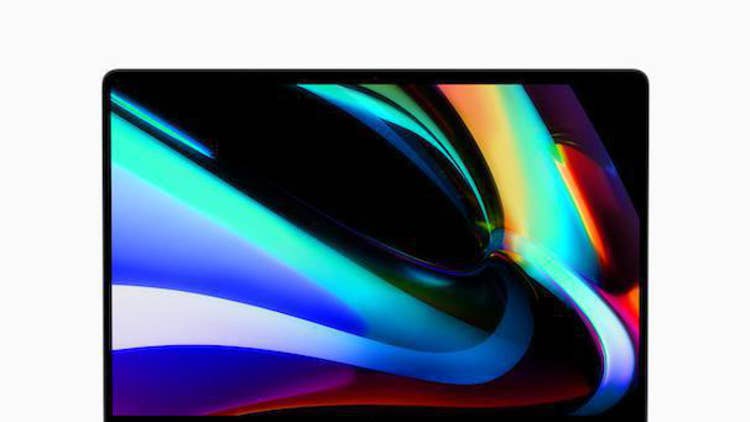
What are your expectations for the forthcoming M1X MacBook Pro models?
Dettbarn said he expects incredible performance and increased demand from employees and businesses for the new MacBook Pro. He’s expecting Apple to unveil new MacBook Pro models featuring the next-generation Apple Silicon processor—rumored to be known as the M1X—within two weeks to a month.
Apple’s first-generation Arm-based Mac processor, the M1, has been a massive success for the company and “exceeded everyone’s expectations,” Dettbarn said. Apple has reported that the inclusion of the M1 in models such as the MacBook Air and entry-level MacBook Pro has been the key to driving increased Mac sales in recent quarters.
Now, it appears Apple is set to launch an even faster in-house chip for its higher-end MacBook Pro lineup—and Dettbarn said he’s “expecting extraordinarily great performance” from the M1X MacBook Pros.
For businesses—especially those with employee choice programs about which devices to use—“I think you’ll see [Mac] expand at an even faster rate than it has the last couple of years,” he said. “I’m expecting this is going to create an even larger divide [with the PC] in terms of employee choice. People are going to choose the Mac more than ever before.”

How is Addigy working more closely with MSPs?
Addigy has been ramping up its efforts with managed services providers in recent years, and MSPs already accounted for 50 percent of the company’s revenue even before the Pax8 agreement announced in August, Dettbarn said. And with that agreement, “I’m very bullish about what this means for our MSP channel,” h said. “Pax8 gives us that extended reach into MSPs.”
Addigy offers the “only multi-tenant remote monitoring and management (RMM) and mobile device management (MDM) tool available for Apple devices,” and Addigy “ offers MSPs an affordable option to expand their Apple business,” Pax8 said in a news release in August.
Ultimately, working with Pax8 and MSPs is a “great way to ensure that we’re expanding with SMBs at a fast rate,” Dettbarn said. “We expect the Apple ecosystem to be growing in the SMB space, arguably, at an even faster rate than in enterprise. We feel like our investment [in MSPs] is going to be continuing to pay off for the next decade.”