10 Hot New FireEye Tools Unveiled At FireEye Cyber Defense Summit
From automating attack simulations to monitoring malicious content in real time to finally running on AWS, here’s a look at 10 of the most interesting FireEye tools from FireEye Cyber Defense Summit 2019.

Reach For the Clouds
FireEye’s technology, services and intelligence all rely heavily on one another to gather top-of-the-line threat intelligence as well as front-line data about attacker behavior, according to Grady Summers, executive vice president of products and customer success.
This makes it possible for the Milpitas, Calif.-based platform security vendor to use its hundreds of thousands of sensors located around the world to determine exactly where a threat actor is operating from, Summers said during a media briefing at the FireEye Cyber Defense Summit 2019.
“Our technology gives us an advantage,” Summers said Tuesday. “We can respond more efficiently because of our tech foundation.”
From automating attack simulations to real-time monitoring of malicious content to finally being able to run on Amazon Web Services, here’s a look at 10 of the most interesting FireEye products and services from this week’s FireEye Cyber Defense Summit 2019 in Washington, D.C.
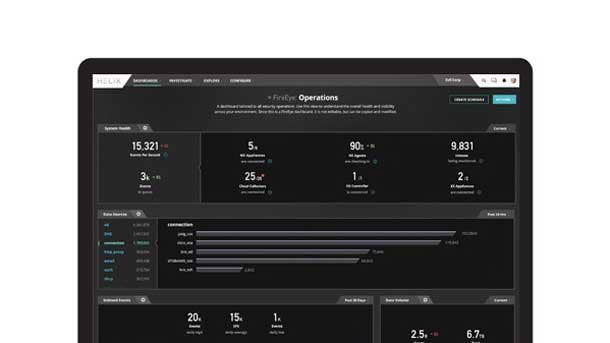
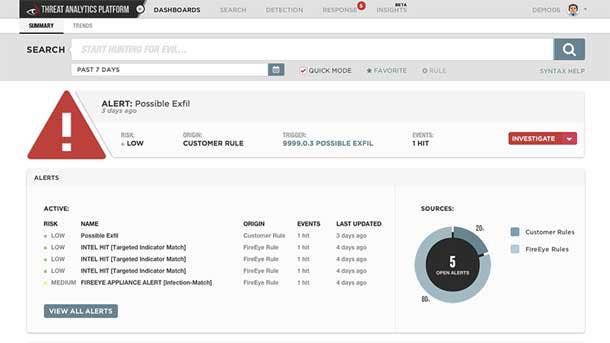
10. Helix Self-Service Portal And Cloud Log On-Boarding
Customers historically found it very difficult to get started with FireEye’s Helix platform since there was a lot of work involved and it was very technical, Summers said. But FireEye has now made it so that Helix customers can go to a cloud integration page and select from more than 20 Software-as-a-Service or Infrastructure-as-a-Service providers including Microsoft, Digital Guardian and CrowdStrike, according to Summers.
Cloud log on-boarding allows customers to get up and running in minutes since all they need to do to get access to a dashboard with real, live data is enter the API key to the access log, Summers said. FireEye can now integrate with any product that gives customers access to their logs from the internet via APIs, according to Summers.
Helix is also able to pull in logs from third parties like Sophos and provide more information around hashes or domain names that the company is familiar with, according to Summers. By applying FireEye’s knowledge to the logs, Summers said customers will be able to narrow down their alert funnel and more easily make decisions.
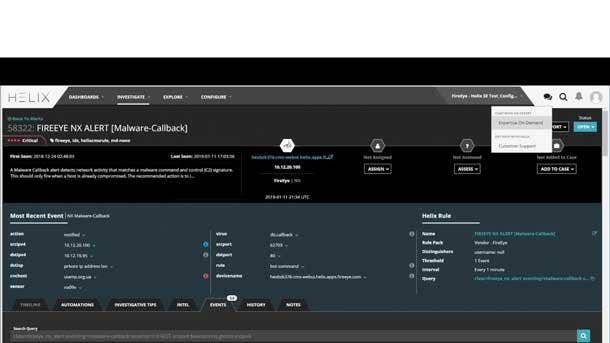
9. Helix Technical Integration And Expertise On Demand
Many customers are building workflows into Helix because it’s designed on an open ecosystem and has a complete API, Summers aid. Helix itself can take data from more than 350 log sources, Summers said, with the cloud log on-boarding portal allowing them to integrate information from their cloud properties.
FireEye is able to apply context and correlate and group together the data coming into Helix from tons of outside sources, according to Summers. For instance, Summers said FireEye would be able to determine that a user hit by a virus or malware had failed its Cofense test and was actively logging into its Google account.
Meanwhile, Summers said Expertise On Demand now makes it possible for customers to reach an expert directly within Helix. Customers with an Expertise On Demand subscription will be routed directly to an expert, Summers said, while customers without the subscription can chat online from a support perspective to better understand what they’re seeing.

8. Federated Helix And Threat Intelligence Context
MSSP partners loved Helix, Summers said, but struggled with having to manage a separate portal for each user. New functionality within Helix gives MSSPs or large, decentralized enterprises a master console where they can see all alerts and run searches across their entire customer base, according to Summers.
The parent-child relationship between consoles has received very good feedback from channel partners, Summers said.
Meanwhile, Summers said the top demand from FireEye’s customers is for the company to overlay its alerts with more threat intelligence. As a result, Summers said the company has created "battle cards" providing battle information about the malware, the threat actor it’s tied to, and the typical techniques and tactics this threat actor might use.
Customers with a subscription to FireEye’s threat intelligence are then provided with a link where they can get more details, Summers said.

7. FireEye Developer Hub
FireEye traditionally has had strong API support around its endpoint and Helix products, Summers said, and is now developing APIs into the company’s core network products. Although the company has had a rich set of APIs for clients to build into, Summers said FireEye hasn’t historically done a great job of informing customers how to do it.
The Developer Hub is a place for customers to collaborate, learn, build, share and sample, Summers said. The Hub is fairly basic right now, Summers said, and is focused primarily on showing customers how to use the Detection On Demand API.
FireEye’s new developer relations program and Developer Hub make the company’s third-party data and solutions effort real in a way that they’ve never been before, Summers said. The company also relaunched its tech partnership program earlier this year, according to Summers.
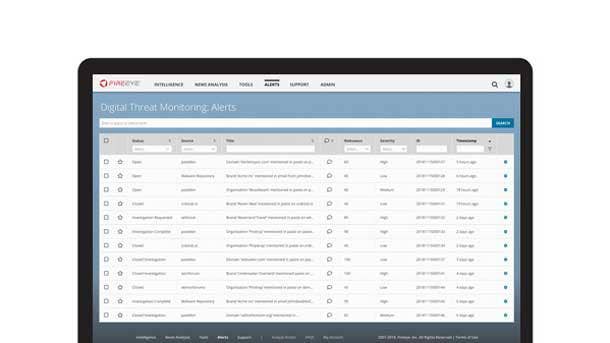
6. Digital Threat Monitoring
FireEye has access to the data coming from its devices, from the Mandiant incident response team and from its threat intelligence operations. The company, however, didn’t have a good way of getting that information to customers in real time, according to Jayce Nichols, vice president of threat intelligence at FireEye.
The new Digital Threat Monitoring offering allows FireEye to take in specific keywords or topic areas customers are interested in, monitor for those things in real time, and provide alerts in a dashboard and through the company’s portal, Nichols said. Customers can also request that analysts look at the alerts in greater depth to figure out if they’re actually a threat or not, according to Nichols.
Digital Threat Assessments are point-in-time reviews done over 30 days focused on identifying threats in a customer’s environment that they might care about, according to Nichols. Digital Threat Monitoring, meanwhile, provides continuous open and Dark Web monitoring, and bundles in analyst investigations for customers that upgrade to the advanced or enterprise offerings, Nichols said.
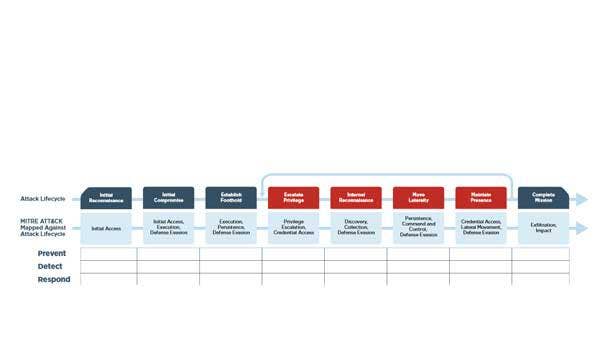
5. Purple Team Assessment
The Purple Team Assessments are a hybrid of FireEye’s red team adversarial simulations focused on attacking the customers and blue team friendly assessments focused on looking through a security team’s documentation, procedures and technical controls, Summers said.
The newly acquired Verodin platform can help FireEye automate some of the processes it does manually today with a red team so that customers are able to simulate attacks without any actual hands on a keyboard, he said. The assessment helps customers understand where in the Mitre Attack framework they’re vulnerable, as well as what techniques specific attackers could use to capitalize on that, he said.
FireEye can leave Verodin behind for clients after the formal purple team engagement so that customers are able to continue simulating attacks, Summers said. The company keeps the automated version of its red team up to date with the latest FireEye threat intelligence so that businesses can continue to practice defending themselves against the most recent threats, according to Summers.
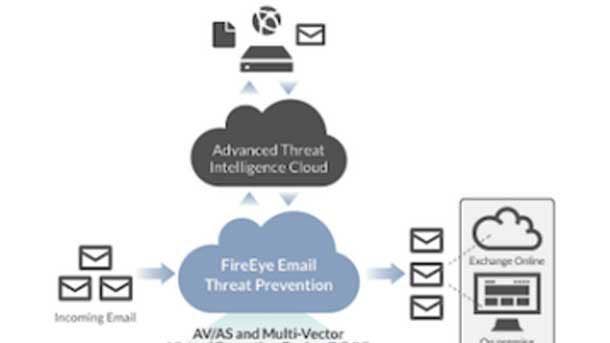
4. FireEye Cloud Security Offering
FireEye has experienced double-digit growth in its cloud revenue over the past several years, Summers said, and has found that roughly half of the breaches its Mandiant team currently responds to involve cloud infrastructure. Only between 10 percent and 15 percent of breaches handled by Mandiant just two years ago involved cloud infrastructure, according to Summers.
Customers are looking to take what FireEye does for them on-premises and make it available to them everywhere they go, Summers said. This has been a challenge for FireEye in the past, Summers said, with the company unable to follow customers that end up going to Amazon Web Services, Microsoft Azure or Zscaler.
Attackers go wherever the data and IT infrastructure are, and Summers said they’ve been moving out to the cloud rapidly. For instance, Summers said attackers go after Azure Active Directory not because it resides in the cloud, but because it’s where enterprises normally store their credentials or keys.

3. FireEye Network Security Plus Iboss
Iboss is cloud infrastructure for end users who are transmitting out to the internet and allows organizations to replace their on-premises proxy infrastructure, Summers said. Zscaler is the most well-known cloud proxy provider today, but Summers said FireEye ikes the Iboss offering thanks to its focus on security-conscious buyers.
Combining FireEye and Iboss means that customers are protected by the same conduit to the internet whether they’re on vacation, at the coffee shop or working from home, Summers said. Iboss appeals to customers that place a premium on security since it gives them a discrete network channel on the back end, with the lack of co-mingling allowing FireEye to place its network security technology, he said.
Much of Iboss’ competition in the cloud proxy space is multitenant, Summers said, meaning that the traffic from all customers flows together. The FireEye-Iboss partnership should appeal both to very large security-conscious customers as well as smaller customers who want to get out of the business of running an on-premises proxy infrastructure, according to Summers.
2. Network Security In AWS
Summers said he’s sat with FireEye customers of many years who were looking to move their protection out to Amazon Web Services or Microsoft Azure but simply had no way to run the security technology in a public cloud environment. FireEye pioneered virtualization and sandbox security, meaning that the company’s products needed to run on bare-metal right on a server in order to do that virtualization, Summers said.
Since both AWS and Azure are already virtualized environments themselves, Summers said FireEye wasn’t able to run virtualization on top of virtualization. But thanks to extensive work done over the past few years, Summers said FireEye can now run its core network security technology on AWS as well as its packet capture network forensics tool.
This is FireEye’s first offering on the AWS Marketplace, Summers said, meaning that customers will now be able to receive the license key and cloud formation template with the single click of a setup button. The FireEye offering focuses on client or end-user traffic coming out of Amazon for firms using Amazon’s virtual desktop product, as well as protecting AWS virtual servers from commonly seen threats.

1. Detection On Demand
For a long time, Summers said customers have wanted to put FireEye’s detection capabilities into their own custom web apps. Detection On Demand provides active, real-time detection, allowing clients to submit everything from customer files to Dropbox files to Amazon S3 buckets for real-time analysis, according to Summers.
The API capability allows customers to leverage FireEye’s detection capabilities wherever they are without having to buy a device or deploy a virtual machine, Summers said. Detection On Demand goes beyond FireEye’s previous ability to allow customers to embed intelligence into their SIEM (security information and event management) tool, according to Summers.
By building Detection On Demand into their Security Operations Center workflow or custom applications, Summers said companies can ensure that no one slips malware into their system. The offering has a browser plug-in that allows customers to get started really quickly and submit files directly from their browser, according to Summers.