10 Hot SIEM Tools To Know About In 2019
Here's a look at how companies like IBM, LogRhythm, and Splunk use SIEM tools to bring analytics and orchestration together to more effectively monitor threats and translate alerts into actionable intelligence.

Tackling Threats
Organizations worldwide have been adopting SIEM tools to effectively monitor threats, translate alerts into actionable intelligence, and respond to security incidents through an analysis of historical security data and real-time data collection. SIEM offerings typically incorporate data from network hardware, end-user devices, security systems, and servers and transmit it to a central intelligence unit for analysis.
However, disparate components within the SIEM ecosystem can pose a challenge at deployment and hinder complete enterprise adoption. Next-generation SIEM tools address this challenge by effectively engulfing individual security components such as advanced analytics, intelligence computing-based orchestration, and user entity and behavioral analytics (UEBA) into a unified security platform.
The next-generation SIEM market is expected to grow to $6.75 billion in 2023 as security gets smarter through the integration of UEBA, SIEM, and advanced analytics, according to ResearchAndMarkets.com. SIEM adoption is expected to grow at a significant rate over the next four years as more enterprises become cognizant about being security-centric from an IT perspective.
Here's a look at 10 SIEM tools that have really captured the market's imagination in 2019.
Exabeam Security Management Platform
The Exabeam Security Management Platform (SMP) collects unlimited log data, uses behavioral analytics to detect attacks, and automates incident response. The company's security data lake allows businesses to collect and quickly search all their data sources in a central repository without making compromises due to a lack of scalability or budget.
The company's User and Entity Behavior Analytics (UEBA) tool detects anomalous behavior and suspect lateral movements within an organization. Meanwhile, Exabeam said timelines of user and device behavior created using machine learning further reduce the time and specialization needed to detect attacker tactics, techniques, and procedures.
And Exabeam’s incident response offering allows teams to respond to security issues rapidly and with less effort than before. The tool uses graphical playbooks and prebuilt APIs that connect and integrate all of an organization's IT and security tools for an automatic response.

FortiSIEM
FortiSIEM is an all-in-one platform that lets users rapidly find and fix security threats and manage compliance standards. Fortinet said the platform reduces complexity, increases critical application availability, and enhances IT management efficiency.
The product enables unified data collection and analytics from diverse information sources including logs, performance metrics, SNMP Traps, security alerts and configuration changes, Fortinet said. FortiSIEM can also discover and map the topology of both physical and virtual infrastructure by simply using credentials without any prior knowledge of what the devices or applications are.
FortiSIEM offers out-of-the-box, pre-defined reports supporting a wide range of compliance auditing and management needs including HIPAA and PCI-DSS. The product can also collect, parse, normalize, index and store security logs at very high speeds, according to Fortinet.
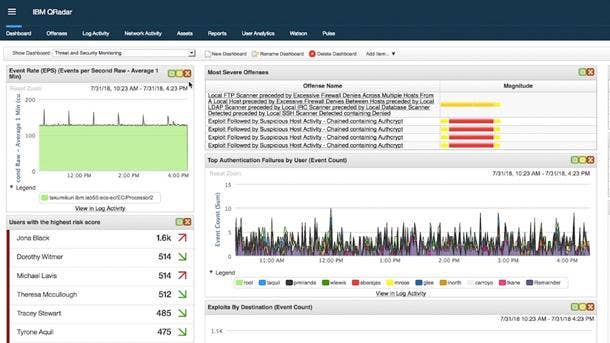
IBM QRadar SIEM
IBM QRadar SIEM helps security teams detect and prioritize threats across the enterprise, consolidating log events and network flow data from thousands of devices, endpoints and applications. QRadar SIEM correlates all this different information and aggregates related events into single alerts to accelerates incident analysis and remediation.
The product helps companies gain comprehensive visibility into enterprise data across on-premises and cloud-based environments from behind a single pane of glass. QRadar SIEM can detect both known and unknown threats, going beyond individual alerts to identify and prioritize potential incidents, and applying artificial intelligence to accelerate investigation processes by 50 percent, according to IBM.
QRadar SIEM provides closed-loop feedback to continuously improve detection, and is available both on-premises as well as in a cloud environment. IBM said businesses can use the time savings from automated security intelligence to proactively hunt threats and automate containment processes.

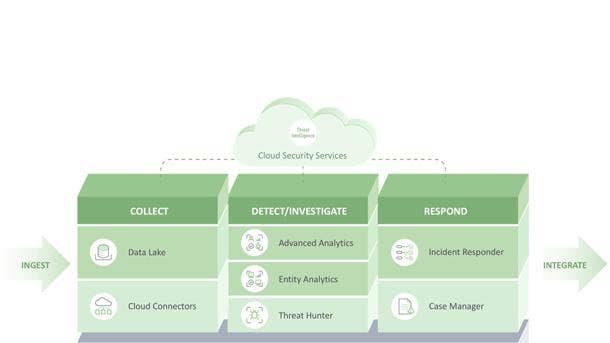
LogRhythm NextGen SIEM Platform
The LogRhythm NextGen SIEM Platform empowers teams to overcome resource constraints and quickly implement a capable and formidable security operation in support of rapid monitoring, detection, and response. The tool's robust functionality allows businesses to streamline operations and reduce total cost of ownership, according to LogRhythm.
The company's Threat Lifecycle Management detection and response framework helps organizations sift through the noise, investigate concerning incidents, and increase their security maturity, according to LogRhythm. The Threat Lifecycle Management framework reduces a company's mean time to detect as well as its mean time to respond, LogRhythm said.
The NextGen SIEM platform includes LogRhythm Enterprise, a scalable tool designed to help large organizations achieve enterprise-level monitoring and analytics capabilities. For smaller organizations, LogRhythm’s XM configuration meets their needs through a single efficient, affordable packaged tool.

McAfee Enterprise Security Manager
McAfee Enterprise Security Manager allows organizations to prioritize, investigate, and respond to hidden threats while meeting compliance requirements. It provides companies with complete and correlated access to the content and context needed for fast, risk-based decisions, so they can invest resources to best effect in a dynamic threat and operational landscape.
The product delivers a real-time understanding of threat data and reputation feeds, as well as a view of the systems, data, risks, and activities inside a company's systems. This is critical for investigating 'low-and-slow' attacks, searching for indicators of compromise, or remediating audit findings, according to McAfee.
McAfee Enterprise Security Manager also provides integrated tools for configuration and change management, case management, and centralized policy management to improve workflow and security operations team efficiency. And Content Packs available for McAfee Enterprise Security Manager offer prebuilt configurations for advanced security use cases that help simplify security operations.
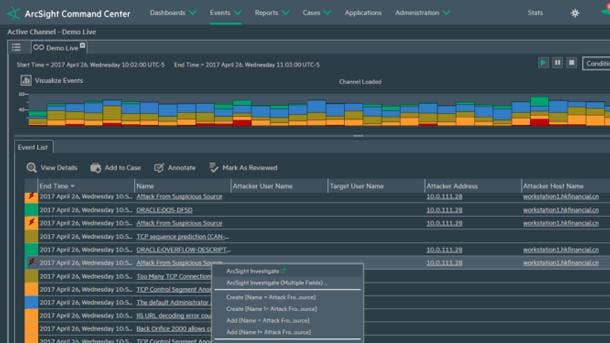
Micro Focus ArcSight ESM
Micro Focus ArcSight Enterprise Security Manager dramatically reduces the time needed to detect, react, and triage cybersecurity threats at scale. The product helps security teams detect and respond to internal and external threats, reduces response time from hours or days to minutes, and gives Security Operations Centers (SOCs) the ability to address more threats with no additional headcount.
The product is a comprehensive, real-time threat detection, analysis, workflow, and compliance management platform with increased data enrichment capabilities. It detects and directs analysts to cybersecurity threats, in real time, helping security operations teams respond quickly to indicators of compromise.
By automatically identifying and prioritizing threats, ArcSight ESM helps teams avoid the cost, complexity and extra work associated with being alerted of false positives. It also gives organizations the ability to have a centralized view into their multiple environments, creating workflow efficiency for streamlined processes.
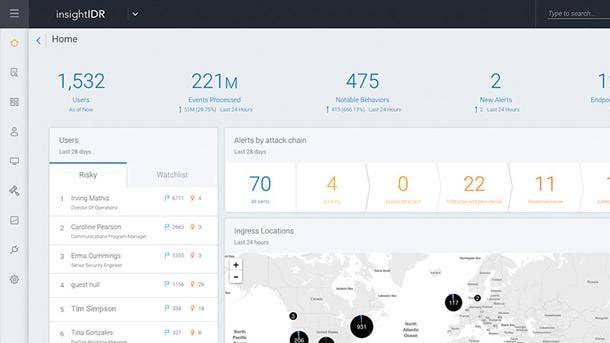
Rapid7 InsightIDR
Rapid7 InsightIDR provides incident detection and response, authentication monitoring, and endpoint visibility. The product identifies unauthorized access from external and internal threats, highlighting suspicious activity so that organizations don’t have to weed through thousands of data streams.
InsightIDR combines the power of endpoint forensics, log search, and sophisticated dashboards into a single offering, collecting data from existing network security tools, authentication logs, and endpoint devices. It then aggregates the data at an on-premises Collector or a dedicated host machine that centralizes your data.
Rapid7 runs analytics on this data to correlate users, accounts, authentications, alerts, and privileges. The analysis provides insight into user behavior while searching for known indicators of compromise, according to the company.
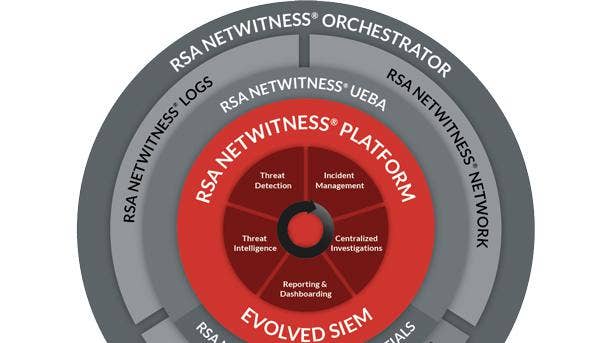
RSA NetWitness Platform
The RSA NetWitness Platform provides pervasive visibility across a modern IT infrastructure, enabling better and faster detection of security incidents with full automation and orchestration capabilities. The platform extends the traditional log-centric, compliance-focused approach to security to include threat analytics, user and entity behavior analytics (UEBA), and visibility into cloud, network and endpoints.
RSA NetWitness Logs and RSA NetWitness Network provide security visibility across the infrastructure, capturing real-time data from logs and network packets. RSA NetWitness Endpoint provides visibility into IT endpoints at the user and kernel level, to flag anomalous activity, provide machine/endpoint suspect scores and block/quarantine malicious processes.
RSA NetWitness Orchestrator is a comprehensive security operation and automation technology that combines full case management, intelligent automation and orchestration, and collaborative investigation capabilities. And RSA NetWitness UEBA Essentials leverages user, network and endpoint behavioral profiling to identify deviations from normal user behaviors.

Securonix Next-Generation SIEM
The Securonix Next-Generation SIEM combines log management, user and entity behavior analytics, and security incident response into a complete, end-to-end security operations platform. It collects massive volumes of data in real-time, uses patented machine learning algorithms to detect advanced threats, and provides artificial intelligence-based security incident response capabilities for fast remediation.
The company's open data platform is powered by Hadoop and ingests hundreds of terabytes per day to support economical long-term data retention. Built-in user and entity behavior analytics, meanwhile, stitch together a series of events over time using threat chain models in order to surface the highest risk events.
Securonix Spotter enables blazing-fast threat hunting using natural language search, allowing for threat actors and indicators of compromise to be identified simply by using visual pivoting. And Securonix Investigation Workbench allows organizations to rapidly investigate incidents by homing in on anomalous entities and tracing associated activities and events.
Splunk Enterprise Security
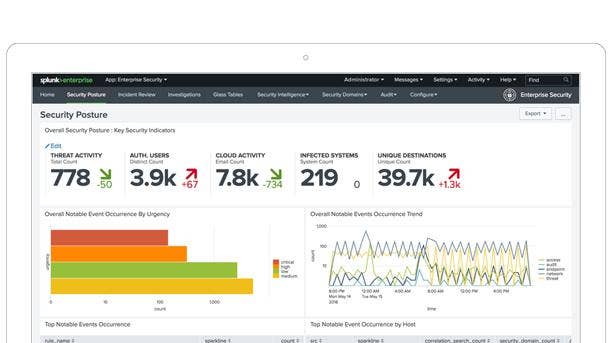
Splunk Enterprise Security provides organizations with the insight needed to minimize risk by simplifying threat management and quickly detecting and responding to internal and external attacks. The platform helps teams gain organization-wide visibility and security intelligence for continuous monitoring and incident response, providing executives with a window into business risk.
Enterprise Security provides insight from data generated from network, endpoint, access, malware, vulnerability and identity technologies, which is correlated using pre-defined rules or via ad-hoc searching. The product clearly visualizes security posture with dashboards, key security indicators, and static and dynamic thresholds.
The tool also allows businesses to optimize, centralize, and automate incident response workflows with alerts, centralized logs, and pre-defined reports and correlations. Splunk Enterprise Security is also capable of conducting rapid investigations using ad-hoc search and correlations to detect malicious activities.