16 Hottest Network And Endpoint Security Products Unveiled At RSA San Francisco
Here's a look at 16 products released around RSA San Francisco that boost security by doing everything from modernizing enterprise networks for cloud adoption to autonomously responding to threat actors on the endpoint.

Fortifying The Base
Vendors attending RSA San Francisco have made significant advancements around network and endpoint security, adding detection and response capabilities to their portfolio, protection against emerging threats like DDoS attacks, and embracing software-defined infrastructures.
Cybersecurity companies have doubled down on everything from protecting against memory-based attacks to carrying out secure access management using a single pane of glass to leveraging machine-learning and behavioral analytics to monitor and isolate endpoint attacks.
SD-WAN has been coming into its own in the network security space, with a handful of security-focused companies rolling out their own offerings to deliver network performance optimization and help branch employees connect to applications in the cloud with greater security and reliability.
Here's a look at what 16 RSA San Francisco network and endpoint security vendors are doing to modernize enterprise networks for cloud adoption, autonomously respond to threat actors, and gain more visibility and insight into advanced threats.

Forcepoint Dynamic Edge Protection
Forcepoint Dynamic Edge Protection provides an integrated network security offering that supports the modernization of enterprise networks for cloud adoption. The tool will provide converged capabilities for SD-WAN connectivity as well as next-generation firewall-as-a-service with security for web and cloud.
Forcepoint said Dynamic Edge Protection will deliver security that works everywhere employees are, taking advantage of new advances such as behavior-centric, risk-adaptive security without on-site updates or redeployment.
Highly distributed organizations such as retailers, financial institutions, hospitality providers, and government agencies can use Forcepoint Dynamic Edge Protection to significantly reduce the cost and complexity of connecting their hundreds or thousands of remote locations in a highly secure and manageable way. The tool can replace disparate hardware appliances deployed at each site.

SentinelOne ActiveEDR
SentinelOne ActiveEDR allows security teams to quickly understand the story and root cause behind threat actors and autonomously respond without any reliance on cloud resources. Everyone from advanced SOC analysts to novice security teams can automatically remediate threats and defend against advanced attacks using ActiveEDR, according to SentinelOne.
ActiveEDR reduces the cost and time required to bring value to the complicated and overwhelming amount of data provided by EDR tools, SentinelOne said. The technology allows security teams to focus on the alerts that matter and leverage technology to assist in what before had been human-mandated tasks.
The autonomous AI powered agent in ActiveEDR functions like a SOC analyst on each and every endpoint, raising high-quality, prioritized alerts when threat behavior is observed, according to SentinelOne. At machine speed, ActiveEDR is able to prevent, detect, and respond to advanced attacks regardless of delivery vectors, whether the endpoint is connected to the cloud or not.

SonicWall Capture Client 2.0
SonicWall Capture Client 2.0 increases administrators' response time, visibility and insight into advanced threats, giving organizations active control of their endpoint health with advanced endpoint detection and response capabilities.
Administrators now have the ability to track threat origins and intended destinations, kill and quarantine as necessary, and roll back endpoints to their last-known healthy state in the event of an infection.
External USB drives have posed a serious threat to network security, SonicWall said, potentially delivering malware, ransomware and viruses to vulnerable endpoints. In response, SonicWall said a new Capture Client feature helps organizations reduce their attack surface by locking out unknown or suspicious devices.

Virsec Application Memory Firewall
The Virsec Application Memory Firewall detects deviations in application execution caused by memory-based attacks and takes immediate action to stop applications from being corrupted or hijacked without requiring code changes, patches or signature updates.
The firewall delivers protection capabilities that secure the critical juncture between applications and process memory. Specifically, the company said it detects and stops advanced fileless and zero-day techniques including buffer overflow attacks, stack smashing, DLL injections, return-oriented programming, side channel attacks and corruption of configuration data.
The technology automatically maps the legitimate execution of an application, according to Virsec. If there is any deviation during execution, the company said this is a positive sign of compromise, and the Application Memory Firewall stops the exploit within microseconds.

Untangle Network Security Framework
The Untangle Network Security Framework provides IT teams with the ability to ensure protection, monitoring and control for all devices, applications, and events, enforcing a consistent security posture across the entire digital attack surface. The framework includes two new products: a Micro Firewall and SD-WAN Router.
The Micro Firewall is a purpose-built, lightweight, containerized firewall with an AI-based routing service that predetermines network traffic routing paths based on historical patterns and machine learning. Predictive routing can detect malicious activity and enforce network policies, dropping traffic that can cause harm, or routing traffic to a remote or cloud-based security service for further processing.
Untangle's SD-WAN Router provides both advanced routing capabilities to deliver network performance optimization, plus a built-in, intelligent firewall to ensure the network is always secure, the company said. It accelerates the performance of WAN connectors and links, using advanced, configurable routing techniques to ensure that traffic is sent across the local network and over the internet efficiently.

Citrix SD-WAN
New capabilities within Citrix SD-WAN will enable enterprises to easily administer user-centric policies and connect branch employees to applications in the cloud with greater security and reliability.
Citrix SD-WAN helps enterprises deliver a reliable, high-performance workspace experience when accessing SaaS apps, cloud workloads, virtual apps and desktops, or traditional data center resources. Companies using the product can simplify branch networking by converging WAN edge capabilities and defining security zones to apply different policies for different users.
By integrating with a series of third-party APIS, Citrix enables enterprises to establish tunnels between branches and security enforcement points for traffic inspection and threat prevention with high availability. The tool also applies controls automatically to protect users and applications whether they are connecting to SaaS applications or services over the internet.

Pulse SDP
Pulse SDP (Software Defined Perimeter) offers secure connectivity only after successful user, device and security state verification including geo location and behavior-based anomaly detection. As a result, Pulse Secure said organizations gain accessibility while streamlining access provisioning, improving performance, and reducing the visible attack surface.
Dual-mode VPN and SDP architectures provides enterprises with a single pane of glass for secure access management as well as operational visibility across the public cloud, private cloud and data center. Extensive multi-factor authentication and authorization options, meanwhile, ensures that users, their devices, and the applications they access are continuously verified before and during the transaction.
Uniform policy management enables consistently provisioned secure connections that increase usability and security while reducing configuration errors, policy drift and gateway sprawl, according to Pulse Secure. And granular access enforcement aligns business and compliance requirements with on-demand, application-level access that supports preferred devices.
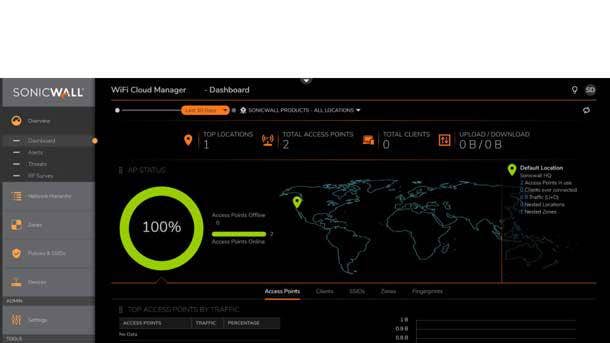
SonicWall WiFi Cloud Manager
The SonicWall WiFi Cloud Manager simplifies wireless access, control and troubleshooting across networks of any size or region with single sign-on access provided by the cloud-based Capture Security Center to ensure proper security measures are taken.
Provisioning new wireless hardware can often be time-consuming when taking adequate measures to ensure employees receive secure, high-performance wireless connectivity, according to SonicWall. Pairing the SonicWall WiFi Cloud Manager with SonicWall Zero-Touch Deployment and wireless mesh networking allows wireless expansion to be accomplished within minutes.
Administrators can also leverage the intuitive, easy-to-use SonicWall WiFi Planner surveying capabilities to design and deploy secure wireless networks that enhance the user experience and ensure workforce productivity.

SentinelOne Full Remote Shell Capabilities
The SentinelOne Full Remote Shell Capabilities provide security and IT operations teams unparalleled technology in identifying, assessing and remediating endpoint attacks across the enterprise regardless of the compromised endpoint's location.
The new capabilities allow authorized administrators to access managed endpoints directly from the SentinelOne console UI and establish a full remote shell session to investigate attacks, understand attack context and remediate breaches by troubleshooting end user issues in real-time.
By providing full, native shell capabilities, SentinelOne said they've greatly alleviated the prior constraints of remote endpoint management while increasing operational productivity and cost savings. The company has implemented stringent procedures to ensure that optimal security posture is present along with usability throughout the remote shell process.

Alert Logic Extended Endpoint Protection
Alert Logic Extended Endpoint Protection leverages machine-learning and behavioral analytics to monitor and isolate endpoint attacks at the earliest opportunity, It helps thwart multiple attack techniques that try to compromise endpoints, gain access to resources, and detonate payloads thanks to real-time deep visibility across endpoints, OS and CPU.
The expanded attack surface coverage enriches Alert Logic's offering with even greater detection and protecting support along with enhanced visibility across environments and workloads, the company said. This allows resource-constrained security buyers to address more of their needs without having to purchase an SIEM tool.
Customers can use Alert Logic alongside existing anti-virus and endpoint security tools to gain an additional layer of defense, the company said. Extended Endpoint Protection is currently available for select customer release and generally available in Alert Logic Essentials in the second quarter.
SparkCognition DeepArmor v2.0
DeepArmor 2.0 adds support for Linux OS with a new agent and machine learning detection engine for malware attacks. The headless agent will operate seamlessly in the background, matching existing Mac and Windows capabilities that protect against zero-day malware, script, and weaponized document attacks, according to SparkCognition.
DeepArmor is expanding telemetry and adding autonomous alert handling to its cloud-based management console, the company said. These features leverage DeepArmor's cloud intelligence engine to reduce the workload of the security analyst by automatically taking action on some alerts and reducing false positives.
This enables security operations teams to make informed decisions based on system information at the time of the event and key data points extracted during static file analysis, according to SparkCognition. DeepArmor also continues to improve deployment, manageability, and scalability to meet the requirements of large enterprise customers.

Palo Alto Networks Traps 6.0
Traps endpoint protection and response now includes a Behavioral Threat Protection engine that stops advanced threats in real-time by stitching together a chain of events to identity malicious activity. The product acts as the ultimately data collection sensor for Cortex Data Lake, gathering the most comprehensive endpoint security data in the industry.
In conjunction with Cortex XDR, Palo Alto Networks customers can use Traps to extend their prevention capabilities to include detection and response across their entire digital infrastructure with a single agent. Traps 6.0 is currently available to customers worldwide.

Infoblox NIOS 8.4
Infoblox NIOS (Network Identity Operating System) 8.4 adds support for the Google Cloud Platform and single sign-on to provide customers with an improved network security experience.
The addition of the Google Cloud Platform builds upon Infoblox's existing cloud ecosystem, which includes support for AWS and Microsoft Azure. IT administrators can gather tenants, virtual machines, and network data and automatically register DNS records for new virtual machines spinning up in GCP, AWS or Azure.
Customers can additionally log into NIOS 8.4 through a single platform, improving ease-of-use without compromising network security, according to Infoblox. The ability to delegate identity management to a single sign-on application eases administrative efforts and ensures customers are able to get the most from their network infrastructure.

Bugcrowd Traffic Control 2.0
Bugcrowd Traffic Control 2.0 provides customers additional coverage assurance, access control and compliance-ready reporting thanks to several new credential management, ticketing, messaging, and workflow integrations. These enhancements drive greater efficiencies between security, risk, and development teams, the company said.
Traffic Control enables organizations with a secure gateway to easily manage and control access, as well as see what targets are being tested, according to Bugcrowd. And enriched credential management and identification provides customers with a trusted source for testing traffic for vulnerabilities, the company said.
All told, Bugcrowd said validated coverage analysis and advanced reporting demonstrate compliance to auditors and a return to investment to stakeholders for the ultimate in coverage assurance.

A10 Networks Thunder 14045 TPS
Capacity enhancements to the Thunder 14045 TPS will make it easier for service providers to build profitable DDoS mitigation services that protect both subscribers' networks as well as their own. The threat protection system delivers attack traffic mitigation capabilities while building scalable DDoS defenses that meet the challenge of emerging attacks.
With 500 Gbps mitigation capacity per Thunder TPS device, A10 Networks said they continue to drive innovation in the fast-growing DDoS market, leaving legacy suppliers behind. The device provides intelligent automation, granular protection capabilities and zero-touch operation to accelerate responses and ensure optimal, efficient protection, according to A10 Networks.
Thunder TPS additionally incorporates global intelligence from A10 Networks DDoS weapons research to improve security posture and real-time insights into emerging threats. All told, A10 Networks said offering high performance in a small form factor allows for fast detection and mitigation while lowering costs, reducing complexity, and increasing reliability in the field.

SonicWall SOHO 250 And TZ350 Series Firewalls
SonicWall's new SOHO 250 and TZ350 series firewalls are designed for small, mid-sized and distributed enterprise organizations with remote locations. They integrate essential networking features and industry-validated high-security effectiveness to protect data and connected devices, including IoT.
The new firewall range combines high-speed threat prevention and software-defined wide area networking technology with an extensive range of networking and wireless features. It also offers simplified deployment and centralized management capabilities, according to SonicWall.
SonicWall Secure SD-WAN technology reduces costs by replacing expensive MPLS technology with lower-cost internet access, the company said. And the deployment of SOHO 250 and TZ350 firewalls is greatly simplified with SonicWall Zero-Touch Deployment.