9 Hot Security Products At Interop Las Vegas

SonicWall: Re-assembly Free Deep Packet Inspection 8 (RFDPI)
Say this 10 times fast. SonicWall's Re-assembly Free Deep Packet Inspection. The new DPI offering provides IT personnel with even more visibility into inbound and outbound network content without compromising security or impeding performance. The new inspection engine is part of the company's overall Unified Threat Management strategy, incorporating a multi-layered security approach that addresses increasingly sophisticated and targeted security threats. The engine offers a unique combination of thorough insight and accelerated speed which makes it specifically suited to meet the bandwidth demands of Web 2.0.

Secure Computing: Security Gateway appliances
Secure Computing Corporation and VMware have joined forces to provide customers with security gateway virtual appliances for organizations that span the market segments. Specifically targeted to VMware environments, these security gateway appliances will provide customers with an easy way to implement and manage security for multiple virtual machines, or multiple applications within one virtual machine, through a single gateway. Altogether, the technology will enable customers to integrate the business benefits of VMware virtualization -- such as reduced capital and operating expenses, assured business continuity and a "greener" carbon footprint -- while ensuring enhanced security across the datacenter that exceeds security in a physical environment.
Through its relationship with VMware, all of Secure Computing's security gateway appliances can now be deployed as preconfigured virtual appliances onto new or existing hardware without the cost and space required of traditional security implementations. Customers can also deploy different Secure Computing appliances, each on their own virtual machine, on a single server.

Microsoft: Forefront Unified Access Gateway Microsoft has announced its next-generation secure remote access gateway product, Forefront Unified Access Gateway (UAG), the evolution of Microsoft's current solution, Intelligent Application Gateway (IAG 2007). The new UAG offering is designed to bring new features and functionality to make remote access easier than ever for all users and IT professionals. In addition, Microsoft has also launched an updated SharePoint Optimizer, providing enhanced functionality and manageability for secure remote access to SharePoint by all mobile users. The IAG 2007 SharePoint Optimizer will be available for download in May, while the UAG will be available in the first half of 2009.
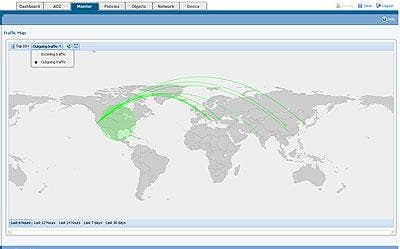
Palo Alto Networks: GeoScope
An up and comer in the security space, Palo Alto Networks, is jumping into Interop with three new security offerings. The GeoScope, the image featured here, displays a world view of traffic and threats flowing in and out of the network. Specifically, it provides a global view of application traffic based on origins and destinations, which enables IT administrators the ability to quickly and clearly identify anomalous activity leading to data theft or malware. The two other products include the new App-browser and the Application Command Center.
All three of the products offer enhance visibility, control and granularity with a new Application Taxonomy Dashboard, which can sort, categorize and apply policy on users and applications with specific behaviors, such as file transferring, tunneling and port hopping, as well as by categories such as peer-to-peer, IM and video. They also offer increased User ID capabilities, a captive portal view and expanded logging and reporting, which gives IT professionals the ability to track both application and user activities.
Hitachi ID Systems: ID-Archive
The new ID-Archive is an enterprise privileged password management software designed to manage thousands of administrator credentials. Specifically, the ID-Archive allows organizations to regularly randomize administrative passwords on workstations and servers, while giving IT staff the ability to retrieve current credentials when logging into devices. Connectors for more than 70 types of servers and applications are included with ID-Archive. ID-Archive prevents inappropriate retention of sensitive administrative access by current and former staff, while also mitigating risks created by malicious password cracking software.

Array Networks: WiFiProtect
WiFiProtect is a comprehensive, identity-based access control solution for WLAN networks. Virtualization technology automatically funnels all WLAN traffic through a scalable gateway that enables enterprises to provide customized wireless access for partners, guests and employees. By using standard browsers present on virtually every client device, the new WiFiProtect eliminates the need for IT intervention or a pre-installed client every time a guest or partner requires wireless access, thus cutting business costs by reducing staff time and resources.

eTelemetry: Metron 2.0
The Metron 2.0 provides enterprises peace of mind that their employees are productive, and that their resources are being used effectively, by ensuring that online business applications get the bandwidth priority before non-work related sites. Specifically, the Metron 2.0 offers multiple strategies to control access speeds to Web sites, including throttling down bandwidth available for websites that are not absolutely essential at the administrators' discretion.
In addition to controlling bandwidth, this new release adds bandwidth rate limiting, and Web site blocking and filtering capabilities to Metron, a plug-and-play network appliance that monitors individual and department-level bandwidth usage and network activity. Serving as the a network access solution, Metron 2.0 can also rate, limit, filter, and block access to Web sites by person or department.
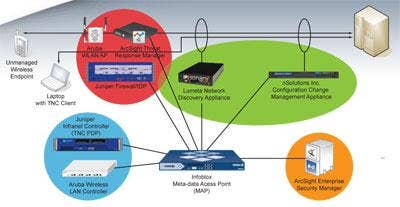
Trusted Computing Group: Trusted Network Connect
There's a major addition to the Trusted Network Connect (TNC) architecture -- TCG has now extended its offering by adding the Interface Metadata Access Control (IF-MAP), an addition designed to expand the TNC architecture to support standardized, dynamic flow of data throughout a wide variety of networking and security components. The expanded architecture now also enables customers to implement complex, multi-vendor systems in an effort to provide comprehensive, coordinated defense-in-depth.
Norman: Sandbox Analyzer
Addressing the time consuming and labor-intensive task of analyzing malware, Norman's new SandBox Analyzer product line provides the complexity, speed and infrastructure to required to drastically reduce the amount of time for file analysis. The Norman Sandbox Serving the function of a complete virus analysis lab, the Analyzer is a complete deep file analysis tool used for reverse engineering and debugging malware. The Analyzer's debugging capabilities include memory, registry, thread, and network socket monitoring, as well as API log and disassemble capabilities. The Pro version of the product line is a more interactive product, superbly suited to provide a step-by-step program check.