Storming The Breach: Payment Card Industry Trends To Watch
The data breach at TJX, which compromised the credit card information of nearly 45 million customers, is never far from the back of merchants' minds these days.
Fortunately, Payment Card Industry (PCI) standards are designed to prevent that very thing. Imposed by the credit card companies, the stringent list of requirements, phased in with staggered deadlines, is designed to reduce the number of data breaches and keep credit card data more secure for every business that processes credit card information from consumers.
And no doubt, PCI compliance has created a whole new market in the industry. Spurred on by looming deadlines, many businesses are beefing up security and incorporating new and creative compliance strategies into their corporate policies. However, for many businesses, PCI deadlines loom dark and threatening on the horizon as the economy lags and IT budgets tighten.
When it comes to PCI compliance and protecting data, some retailers are not just stopping with credit-card data. Not that businesses plan to protect credit-card data with less effort than before. Quite the opposite, in fact. But in addition to credit card numbers, businesses are also implementing strategies to protect data they once considered less important -- like Social Security numbers, birth dates and intellectual property.
Experts say that when PCI standards were established by the major credit card companies several years ago, businesses starting treating credit card data differently than other kinds of data. This was surprisingly problematic, because it created a liability when other kinds of sensitive and personal information were left exposed.
"The only problem was that all other data would include Social Security numbers," said David Taylor, director of research for the PCI Alliance. "They were implementing a higher level of security for credit card numbers."
"The definite trend is taking a more holistic approach," Taylor added.

Once upon a time, corporate IT staff, (or channel partner if it was a SMB) would be required to manually review, analyze and sign off on security logs for abnormalities.
Not so anymore, say security experts. And who has that kind of time these days, anyway? With the barrage of tasks that IT professionals are required to undertake to secure their corporate networks, automating as many processes as possible becomes a necessary evil.
"If you don't automate this stuff, if you don't have some sort of tool or set of tools to manage security environment, not only will Joe Bob the IT guy quit, but the next time you find out about a breach is when people have a fraud case on your hands," said Taylor. "What you don't want to do is wait until after you have a breach."
It's not as cheesy as it sounds. New tools designed to remove labor intensiveness have recently made their debuts onto the security stage. Security experts say that businesses will increasingly adopt technologies that combine both identity management and access control -- appliances that can often be easily deployed -- as they are forced to increase security functions with less IT staff and resources.
In a sense, experts say, technology has far outdistanced the requirements set by PCI standards. For businesses, this means that execs will have more ways to immediately deny personal access and remove permissions for employees who are terminated or leave the company.

As more and more companies start to become confident that they can protect their customers' data from external threats, they will begin to turn that same scrutiny inward, experts say.
It's no secret that insiders pose a huge threat to companies. And as the economy lags and people get laid off or are asked to take over the jobs of employees who are, protecting valuable information becomes even more dangerous.
A perfect example is illustrated in the 1999 film "Office Space." A few freshly laid-off employees decide to retaliate by conspiring with some disgruntled insiders to hack the company's systems and steal from corporate coffers.
As a result, businesses will consider more internal scanning technologies as part of their overall security strategy.

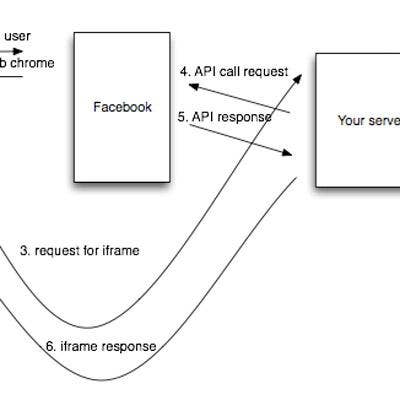
Call it a loophole, but if you're outsourcing your credit card processing technologies, then you're off the PCI hook. As IT budgets get cut, or remain static as the economy spirals downward, fewer businesses will have the capabilities to process the credit-card payments of their customers.
In light of enormous changes to become PCI-compliant, third- and fourth-tier businesses and other businesses with limited internal resources will increasingly rely on outsourced companies to handle their payments.
"Some of them decided to change the way they take payments," said Sumedh Thakar, PCI solutions manager for Qualys. "Budgets are tight. To do compliance on an ongoing basis, you have to have a staff and a team."
"As a CIO, your resources are limited. You have other options to take."
As tier-three and tier-four PCI deadlines come and go and as penalties stiffen, businesses will increasingly look to third-party auditors and assessors to find all their security holes before the PCI auditors do, security experts say.
But assessors won't only be relegated to the enterprise. Smaller businesses with limited budgets will likely form some sort of affiliation or partnership with Qualified Security Assessors that want to expand into new markets.
By the same token, expect to see an upsurge in consulting services and practices, experts say.
A list of QSAs can be already be obtained from the PCI Security Standards Council Web site.
"Merchants are being forced to take some sort of action," said Amer Deeba, CMO of Qualys. "If they are still taking some steps to do something that the standard talks about, in a sense that does improve their security situation."

Many businesses, even large retail chains, are dealing with infrastructure that is decades old. "They're using some databases developed in the early '90s or in some cases the '80s," said Deeba.
Needless to say, an awful lot of databases are storing critical information created long before most data-loss-prevention technologies existed -- making it that much harder for security solutions to be retrofitted to their network environment. As penalties stiffen, businesses that span the segments will be updating their infrastructure to include solutions such as encryption, intrusion prevention and access control technologies.
With the rash of data breaches that seem to appear daily in the papers, it's not surprising that merchants of all sizes increasingly want to protect their brand and reputation. In an effort not to become the next TJX or Hannaford, businesses will try harder than ever to secure customer data and keep their names out of the headlines.
An RSA survey showed that 36 percent of merchants said they are motivated to address PCI standards because of a desire to protect their customers' credit card data, while an additional 25 percent said that their motivating factor was protecting their company's image.
Whatever the reason, it will likely mean the PCI will enter the vocabulary of more and more businesses as deadlines approach.

Despite a lagging economy, business will actually spend more on PCI compliance -- that is to say, they will likely shift their IT budgets accordingly to accommodate looming PCI deadlines.
A recent Forrester State of Compliance survey indicates that more than half of business plan on spending between 2 percent and 4 percent of their IT budgets on credit card data protection -- which a vast majority said was an increase from 2007 budgets.
Not surprisingly, a whopping 72 percent of tier-one merchants rated PCI as a "very high priority" compared to 49 percent of tier-two merchants who did the same, according to Forrester.

A lot of businesses might want to be PCI compliant. But for many, even the big guys, the task is daunting.
Where businesses will need the most help will be in incorporating technologies like encryption and access management control. A Forrester State of Compliance Survey found that 27 percent of respondents said that data encryption was the biggest challenge while another 27 percent pointed to access management issues related to data classification and policy development as their biggest concern.
The same survey also said that businesses often keep way, way, way too much data, which they don't know how to locate, secure or store.
Perhaps coincidentally, data encryption and segregation are the most commonly deployed credit card data protection mechanisms, experts say.

OK, maybe suffer is a strong word. But face it, for many SMBs it's a big enough struggle just to meet overhead costs and make a profit without having to spend money that they don't have on security technology that they don't understand and aren't entirely convinced that they need.
Given their situation, it's no wonder then that less than 19 percent of Level 4 merchants said that they had reported PCI compliance, according to an RSA survey. And with the October deadline rapidly approaching, many small businesses will be feeling the squeeze.
Of course, businesses will have to become aware of what they're protecting their data from. And as they do, they will have to be up on the latest and emerging security threats, which have the potential to compromise their data and put them on the front pages.
Of the many threats that businesses now face, they must protect themselves from zero-day malicious threats; data theft using removal of large-capacity USB sticks and hard drives; data harvesting from hard drives that are improperly disposed of; data leakage via instant messaging; malware distributed from file sharing sites like Facebook and MySpace; and threats targeting mobile devices such as smartphones, BlackBerries and laptops that allow network access from numerous public vectors.