9 Scary Halloween Malware Tricks

Dancing Skeletons
2007 was a year famous for all sorts of Halloween phishing tricks. Perhaps the most notorious was the Storm Trojan spam attack. The e-mail message lured Halloween lovers to a Web site where they could download an application that created the image of a dancing skeleton onto their desktop. However, while users might have been treated to a dancing skeleton, they also will be tricked into downloading malware. The Halloween.exe is part of a malicious botnet that allows remote attackers to take control of their computers and get a hold of their personal information. Some of the telltale subject lines were:
- 'For people with a sense of humor only'
- 'Halloween Fun'
- 'Happy Halloween'
- 'If your in your office, keep the speakers low, lol'
- 'Nothing is funnier this Halloween'
- 'Party on this Halloween'
- 'The most amazing dancing skeleton'
- 'This will make you laugh'
- 'You'll laugh your but off'
More Dancing Skeletons
Malware writers have a long history of exploiting holidays to launch social engineering attacks. And Halloween is no exception. Last year, Trend Micro discovered another version of the dancing skeleton after the Storm worm morphed once again. In this particular attack, the victim received an entertaining Dancing Skeleton game. Users are invited to move their curser over the image to make the skeleton move. Oooh boy!
Little do they know, of course, that while the skeleton is dancing away, malicious code is silently being installed on their computers.
And to add insult to injury, the Russian Business Network resurrected none other than Vengaboys' "Boom boom boom boom" as background music on the site.

Dancing Skeletons (With Benefits)
The Storm worm loves variations on a theme. And even at Halloween, sex continues to be a lure. Last year, the Storm worm adopted new tactics that blended eroticism with a high traffic holiday such as Halloween in its attempts to infect users with malicious code. And it worked. The first copies of the new Halloween emails began going out on October 30th, 2007. As with previous Storm emails, various subject lines and body texts were used to entice users to click on infected downloads.
Halloween en Espanol
Okay, forget for a moment that many Latin American countries celebrate Day of the Dead and not Halloween. In 2007, Websense discovered a phishing scam in the form of a Halloween greeting card. The file, called "hallowenDay.exe," enticed Spanish speaking users to click an image of a pumpkin to access what they thought would be a card.
Once they accessed the site and ran the file, a Trojan Horse was downloaded onto their machine designed to steal sensitive financial information.
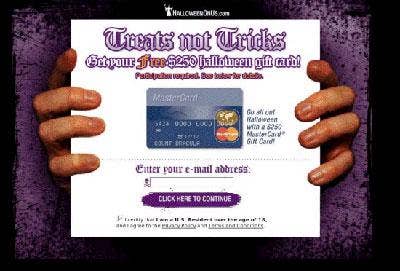
Halloween Gift Card With Your Malware
Last year, Sophos researchers detected this credit card scam with a Halloween twist. Capitalizing on users' constant need for new credit cards, especially in a lagging economy, this phishing scam promised a free $250 Halloween gift card (whatever that means) when users fill out the application.
Needless to say, it's likely that users will receive neither the gift card nor the credit card. However, once they enter their personally identifying and sensitive financial information online, there's a good chance they could get their computers compromised or become the victim of data theft.

Halloween Exploit
Users protected with antivirus and antimalware received security alerts like this when they attempted to click on a dangerous Halloween Web site hosting malicious code or a malicious link sent via spam message. While these Web sites might seem harmless, users' personal and financial data is likely to be exposed or stolen when visiting these sites.

Stormy Halloween
Storm botnet, displayed to the left, was among the most aggressively spread malware of 2008. It enabled the formation of one of the largest botnets in history, estimated at 2 million compromised computers around the world at its peak. And true to form, Storm diligently emerges on holidays and political events, capitalizing on the high volumes of Internet traffic to distribute malware. As in years past, Halloween remains a time for spammers to spread appropriately-themed spam.
According to MessageLabs security experts, malicious spammers are now advertising Halloween sales in the subject lines of traditional spam emails touting herbal remedies and sexual enhancement drugs. This type of spam is part of a larger campaign that made up about one percent of spam using the same body message in each case. Halloween was one of many subjects used in this campaign which originated from the Srizbi botnet, a derivative of the Storm worm.
Big Halloween Sale
To stay competitive, Storm likes to mix it up a little. Unlike previous years, Storm is embedding its Halloween lures in conventional spam messages that sell pharmaceuticals, diet pills and other herbal remedies.
In this spam message, Cisco researchers found that attackers enticed users with the word Halloween in the subject line. Victims will be enticed to click on malicious links after being tricked into buying items that are advertised with Halloween sales. Often the word Halloween is somewhere in the subject line. But when victims open links, anything they're likely going to get for a deal will be malware.
Meds For Halloween
This year, attackers are reeling victims in with a Halloween subject line in an attempt to sell fake merchandise and obtain users credentials. In this case, researchers at MessageLabs found a spam message advertising pharmaceutical meds.
But in an attempt to extract personal identifying information, the attackers ask that the user fill out a "questionnaire" in order to receive a shipment of medications by "licensed physicians." I don't know about you, but somehow the multi-colored print and grammatical errors in the message fail to instill a lot of confidence.