The 10 Biggest Security Stories Of 2008
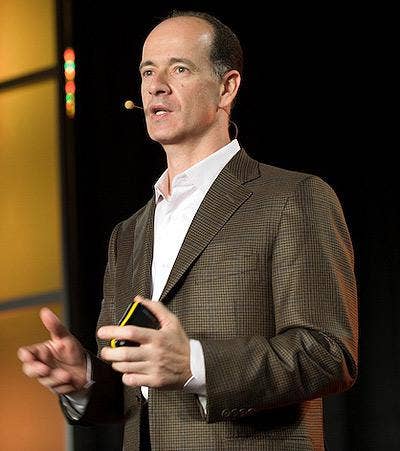
It was the "change" heard round the channel. Symantec rocked the IT world in July after COO Enrique Salem dropped the bombshell to a group of Wall Street analysts that the company planned to skim off the revenue from its top 900 customers by taking their deals direct, or at least giving them the option of doing so. Also among the proposed channel policy changes was an imminent migration from a two-tier to a one-tier distribution model and revamped subscription renewal policies for a spate of SMB customers.
The announcements elicited a firestorm of outrage and criticism from channel partners serving all market segments, many of whom had already started to notice Symantec's shift away from the channel. Despite the company's historic claims regarding its open and honest communication with its channel, partners said that the once 100 percent channel company fell considerably short by failing to mention any of these changes to their channel.
Warning: Everything You Do On The Internet Can Be Hazardous To Your Health. Dan Kaminsky, IOActive director of penetration testing, rocked the security community boat when he revealed that the Internet contained fundamental flaws that allowed hackers to exploit a Domain Name Server vulnerability, which paved the way for cyber attacks that affect Web surfers using search engines such as Google and Yahoo.
The error could be exploited by attackers to launch DNS cache poisoning attacks by creating fake messages accepted by the DNS that can trick the server into delivering an incorrect request. To exploit the flaw, all the hackers have to do is trick the DNS into accepting an incorrect domain, which will subsequently reroute the users to another malicious Web site unbeknownst to them. Once the user is redirected to the new site, the attacker could then install Trojans or keystroke loggers onto their computers to extract financial and personal data.
Unlike other vulnerabilities, the DNS flaw flung the door wide open for attacks across all platforms, including Mac and Linux. And in addition to cache poisoning attacks, Kaminsky revealed that this new type of vulnerability also allowed attackers to exploit IPSec VPNs, SSL certification, automatic software update systems, spam filters and VoIP systems. Yowza.

McAfee dropped a bombshell in late September with news that it planned to embark on a $465-million acquisition of Secure Computing, making the combined company one of the largest network security players in the industry. The merger married McAfee's endpoint and desktop security technologies with Secure Computing's gateway and firewall line, filling gaping holes in McAfee's perimeter security offerings while greatly enhancing the company's hardware offerings. The acquisition also allows McAfee's partners to enter new vertical markets, such as the federal sector, in which Secure Computing had dominant market share.

Symantec in October said it plans to acquire online messaging and Web security company MessageLabs for some $695 million in cash, placing the company as a viable competitor in both Software-as-a-Service and messaging security market segments -- two areas that have experienced rapid growth over the past year.
Partners saw the purchase as a good move, and one that would allow them to extensively broaden their own SaaS portfolios. And down the road, Symantec partners say they look forward to offering more of MessageLabs' managed services in data loss prevention, compliance, endpoint security and archiving, boosted by MessageLabs' expertise in SaaS sales, operations and support models.

The vast number of security executives that left their posts for other jobs or "took time off to spend more time with family" was staggering in 2008. Perhaps the most noteworthy was Symantec CEO John Thompson's announcement that he plans to retire early next year. Thompson's impending departure was preceded by a hasty exit by then-Vice President Of Global Channels Julie Parrish earlier in the week before the Symantec Partner Engage conference. The company has yet to name a replacement for Parrish's position.
But Symantec executives weren't the only ones playing their own version of musical chairs. McAfee's channel chief Dave Dickison was replaced by then-Vice President Of North America Channels Lisa Loe. Loe said that Dickison stepped down to take the position of vice president of channel operations in an effort to head a comprehensive channel project that aims to "rebalance" the channel. After just three months, however, Loe stepped down as channel chief as well.
In addition, Trend Micro President Of Operations Lane Bess jumped ship to head Palo Alto Networks. Bess' departure was shortly thereafter followed by that of Nancy Reynolds, Trend Micro vice president of channel and SMB sales for the Americas, who took a global channel position with the same company. Whew.
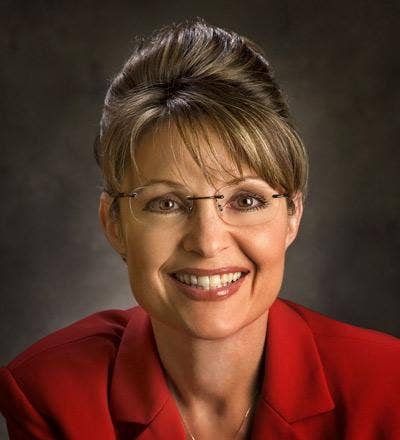
Forget the fact that this probably could have been avoided if Alaska Governor Sarah Palin had known to apply better password security practices. The vice presidential contender made headlines when a blogger on the 4chan forum/b/board admitted to breaking into Palin's Yahoo e-mail account and accessing her personal e-mails simply by using the password reset feature. All it took was deducing the answers to the Alaska governor's "secret question" -- complex inquiries such as her zip code, date of birth, and how she met her husband -- through simple Internet searches. Once the blogger came up with the correct answers, he was able to reset the password and enter Palin's account at will.
News of the hack kept Palin in the headlines for weeks, and underscored the need for providers like Google and Yahoo to radically enhance their security protocols. The hack also raised further questions and concerns about Palin's practice of conducting government business over a private e-mail account.

Internet Service Provider McColo was disconnected from its upstream providers earlier this year, rendering it without a huge portion of its Internet traffic. Why? Because, among other things, the ISP was known to host illegal child pornography sites, malware and copious spammers, and was found to carry some of the world's largest botnets, according to a scathing report compiled by numerous prominent security researchers. Shortly following McColo's takedown, researchers noted that spam levels dropped significantly -- as much as 60 percent to 80 percent in some cases -- in the lull before spammers found new providers.
Since then, many of the spammers and malware writers found alternate hosts to distribute their wares. Even though it was short lived, McColo's eradication was possibly one of the year's biggest successes for the security community, possibly implying that other nefarious hosts might be subject to the same fate.
It was Microsoft's first out-of-band patch in a year and a half. In October, Microsoft issued an emergency patch for a malicious Internet worm crawling around cyberspace and infecting unpatched computers. Researchers noticed that the exploit was loose in the wild, meaning that hackers were using the exploit code to launch attacks on unsuspecting users' data in calculated, targeted attacks.
The fact that Microsoft couldn't wait to include this fix in its monthly security bulletins, known as "Patch Tuesday," indicated just how severe this bug was.

OK, so it wasn't quite in the category of a TJX, but this data breach hit the headlines hard early in 2008. Hannaford Bros., a New England-based supermarket chain, was the victim of a hack that resulted in the loss of more than 4.2 million customer credit and debit card numbers. At least 1,800 cases of fraud had already been reported by the time the breach became public. Oh, but not to worry -- Hannaford executives reassured its customers that the stolen information was limited to card numbers and expiration dates, but did not include personal data such as names and addresses.
Just six days after Russia rolled into Georgia with tanks, the battle between the two nations was taken to the Internet in what appeared to be a coordinated cyber attack. During the conflict, hackers compromised several Georgian government Web sites with denial of service attacks and defacement, crippling the nation's ability to distribute information.
Specifically, hackers defaced the Georgian president's site by juxtaposing President Mikheil Saakashvili's image with that of Hitler's. The sabotage was followed by a DoS attack that left the site inaccessible. Meanwhile, Georgian news sites and other popular information forums were also blocked from user access during the attack.
Whether this was a cyber war or a series of "back-at-ya" skirmishes by rogue nationalists is up for debate. But in this cyber battle, both Georgia and Russia used the Internet to its fullest extent. And security experts say that the trend of taking warfare into cyberspace will likely continue.