The Top 10 Security Stories Of 2009
No doubt, 2009 was a year for "new" security trends. New threats such as Conficker emerged, infecting a record 5 million PCs around the world, while social networking sites provided a new frontier for malicious attacks. And denial-of-service attacks, while not new, were used as a new tool for political activists to shut down commercial and government Web sites.
Meanwhile, Washington led a new charge against cyberthreats. On the channel front, security giants such as McAfee and Symantec appointed new leaders to improve stymied channel relations in the worst economic recession in 75 years.

One of the most highly publicized and prolific botnets in history came and went in relative peace.
Conficker first surfaced in October 2008 after its authors exploited a critical Microsoft vulnerability in the way the Server Service handles Remote Procedure Call (RPC) requests. Microsoft issued an emergency out-of-band patch in October 2008 repairing the vulnerability, but it appeared that not enough users diligently applied the patch before attack code was let loose in the wild.
Conficker made headlines during the first half of 2009 by infecting millions of PCs in a global botnet via USB sticks and peer-to-peer networks. Among its many talents, the prolific Internet worm had the capability to erase its own footprint, block access to several security vendors' Web sites and render numerous antivirus products useless. It also added numerous defensive measures designed to evade detection and removal by disabling Windows Automatic Updates and Windows Security Center.
Alarm about Conficker escalated in the weeks preceding an April 1 deadline, in which the worm was set to receive a new update mechanism that would allow it to communicate on its own with command and control centers, that ostensibly would enable the malware to more easily upload marching orders from its controllers to the botnet army and launch attacks at will. However, April 1 came and went silently, perhaps due to the extensive scrutiny generated from its high-profile media status.

Some call it the new TJX. In what could be the largest security breach in history, credit card processor Heartland Payment Systems suffered a massive data breach, which compromised more than 100 million credit and debit card accounts after malicious software was found in its payment processing system. The breach, which made headlines in early January, superseded the notorious hack of retail giant TJX, which had broken records with 45 million compromised accounts.
Heartland executives said they first learned of the actual security breach in October 2008 when credit card companies Visa and MasterCard alerted them to suspicious activity and card transactions. The company then released an official statement on Jan. 20, the day of President Barack Obama's inauguration, notifying customers that their account information might have been stolen and advising them to cancel credit cards and report suspicious activity to appropriate authorities.
Kicking off the year, the Heartland breach incident became the new poster child for security threats and served as a powerful reminder that no system -- regardless of how big -- is immune to malicious attack.
In what was deemed a revolutionary jump in cybersecurity efforts, President Obama launched a comprehensive 60-day review of federal cybersecurity initiatives and infrastructure, while appointing Melissa Hathaway to head the project as Acting Senior Director for Cyberspace for the National Security and Homeland Security Councils. At the time, officials thought Hathaway was the obvious pick for the new cyberczar post, created by the Obama Administration and intended to coordinate and oversee all federal cybersecurity efforts.
Spurred by growing security threats and an increasingly contracted and mobile workforce, the two-month review was designed to assess federal efforts to secure U.S. computer networks from cyberattacks.
Altogether, the resulting cybersecurity report offered a comprehensive action plan for the U.S. government to strengthen its digital systems by creating educational and expanding partnerships between the federal government and private sectors, and creating an effective incident response plan. But so far, resulting cybersecurity initiatives have yet to be implemented.
Federal cybersecurity efforts took a few steps backward when Hathaway resigned from her position -- citing personal reasons -- after only six months on the job. President Obama has yet to fill a position for the intended cyberczar.
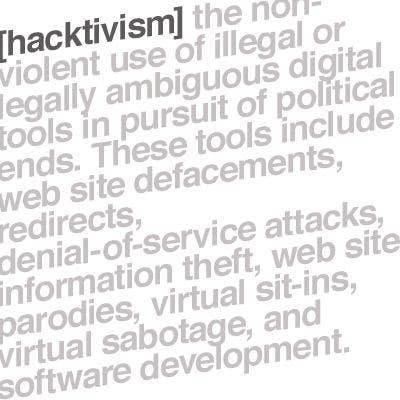
Political hacktivism took on a whole new meaning in 2009 as hackers shut down Web sites by flooding them with requests in an effort to make a political statement.
A spate of Korean denial-of-service attacks were among the most prominent and highly publicized political assaults this year. Security experts say that the hackers behind the denial-of-service attacks, which began over the July 4 weekend, leveraged at least 50,000 to 60,000 computers compromised in a global botnet. The attacks shut down and blocked access to at least 27 government and commercial sites in South Korea and the U.S., including those of the White House, the New York Stock Exchange, the Pentagon, the Department of Homeland Security, the Federal Aviation Commission, Secret Service and the Washington Post.
Meanwhile, "hacktivists" launched a coordinated series of denial-of-service attacks in an effort to sabotage Iranian government Web sites, claiming fraudulent presidential elections in Iran. The political activists used micro-blogging site Twitter to galvanize supporters into action by asking them to use simple hacking tools to flood the Iranian government's Web sites with junk e-mail, rendering many of them inaccessible. San-Francisco-based Twitter was forced to reschedule a planned maintenance in order to keep the channel of communication open for Twitter tweeters sending information to and from Iran.
During a Black Hat presentation, Apple researchers Charlie Miller and Collin Mulliner demonstrated to hundreds of IT professionals and amateur hackers the ease with which hackers could exploit a critical vulnerability in the Apple iPhone SMS. The vulnerability enables hackers to break into the devices to launch a denial-of-service or man-in-the-middle attacks without any user intervention.
Specifically, the vulnerability occurs in the way the iPhone receives and sends text messages via SMS, a protocol that enables users to send text messages. Attackers could take advantage of weaknesses in the binary code sent by SMS to an iPhone.
If exploited, the SMS flaw could be used by hackers to track a victim's location via GPS, execute malicious code to launch a denial-of-service, man-in-the-middle attack, or listen in on a conversation. Both Miller and Mulliner demonstrated a denial-of-service attack on the iPhone by flooding it with hundreds of malformed text messages.
Apple stepped up and repaired the flaw less than 24 hours after Miller's presentation, but not before millions of users around the world caught wind of Apple's glaring security shortcomings.

In April, then Symantec Chief Operating Officer Enrique Salem took the helm as the company's new president and CEO following the retirement of former CEO John Thompson.
Thompson announced his retirement in November 2008 after 10 years of heading the Cupertino, Calif.-based security company. During his tenure, Thompson took Symantec from a struggling antivirus company to a $6 billion security and storage giant that ultimately evolved into the fourth largest software company in the world.
Thompson handed the reins to Salem in the midst of the worst worldwide economic recession in three quarters of a century. And looking forward, Salem acknowledged that he would face numerous challenges in light of the downturn that had crippled budgets and bogged down IT sales across all product categories.
Salem told his channel base that among the numerous issues he planned to tackle as CEO, improved channel communication and ensuring smoother product integration were some of the highest priorities, adding Symantec's channel partners will become "an increasingly important part" of the company's business.

This year, McAfee stepped up channel efforts by filling some long-vacant channel posts while reiterating its commitment to its channel base.
McAfee hired Fernando Quintero to head McAfee North American channels in June followed by the appointment of Alex Thurber, who came on board from Cisco in August to take the role as the company's senior vice president of worldwide channel operations.
Both Thurber and Quintero filled positions that had been vacated for months by their predecessors. Dave Dickison, who once headed the Santa Clara, Calif.-based company's North America channels, departed McAfee rapidly in January. Dickison was replaced in September 2009 by Lisa Loe, who exited the company under mysterious circumstances in December 2008 -- just three months after she was hired.
Since then partners said that the holes left by Dickison's and Loe's absence, as well as high turnover with their channel reps, indicated a larger trend of structural instability and attrition at McAfee, which partners said ultimately served to undermine confidence in the security giant. McAfee solution providers say that the appointments of both Quintero and Thurber boded well for the company's overall channel strategy, but said that the company has a long way to go to regain trust and build a comprehensive and consistent channel strategy.
Hackers and cyberthieves were among the first to readily take part in the social networking craze with a slew of attacks exploiting popular sites like Facebook and Twitter. One of the most notorious attacks included the Koobface worm, which reared its ugly head throughout the year by hurling malware, phishing attacks and massive amounts of spam onto popular social networking sites such as Facebook, MySpace, Friendster, Hi5, Bebo, Fubar, MyYearbook and Tagged.
In the attack, the Koobface variant connected to a malicious server to acquire information details for its spam messages to be sent to contacts of infected users. Facebook and other social network users were then enticed to click on links embedded in socially engineered messages that appeared to come from someone on their contact lists. Once users clicked on the embedded links, they were redirected to a malicious Web sites that downloaded malicious Koobface variants designed to steal sensitive information and record keystrokes to obtain users' login credentials. Other variants also downloaded malicious files such as rogue antivirus software.
Social networks became a prime target for attackers in 2009 due to the fact that users voluntarily provide copious amounts of personally identifying information online. But security experts also contend that the Koobface worm and other attacks have been successful largely because of the inherent trust users put into social networking sites, especially if they think they're receiving a message from someone they know.

In what has been described as one of the largest hacking and identity theft case ever prosecuted, the renowned TJX hacker Albert Gonzalez, 28, was finally indicted in August. Among his high-profile corporate victims are TJX, Hannaford Brothers, 7-11 and credit card processor Heartland Payment Systems.
Gonzalez was the ringleader of an international hacking organization and the alleged mastermind behind some of the biggest data heists in the last few years. His defense attorney was on the verge of reaching a settlement when the prosecution introduced new charges, which subsequently launched a new round of investigations and scuttled his proposed plea deal. If convicted, Gonzalez faces life in prison.
Some of the charges on his record include gaining unauthorized access to computers, committing fraud in connection with computers, damaging computers and conspiracy to commit wire fraud. The indictments also detailed how Gonzalez planned to target an array of Fortune 500 companies, gain access to those companies' point-of-sale systems, and coordinate attacks using SQL injections, malware, sniffers and instant messaging from remote locations. Before the August indictment, the proposed plea bargain would have slapped the Miami resident with a 20-year jail sentence and put an end to investigation for his previous crimes.
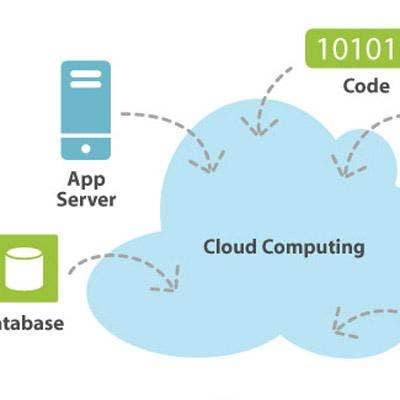
Some of the biggest security players further expanded their cloud-based solutions this year, responding to increased market demand as companies sought ways to cut costs and increase ROI. McAfee launched a cloud-based e-mail gateway in October following the acquisition of SaaS e-mail and Web security company MXLogic, which expanded McAfee's cloud-based portfolio with e-mail and Web security offerings, e-mail archiving and e-mail continuity services, along with the addition of 40,000 new customers and 1,800 channel partners.
Meanwhile, Tokyo-based Trend Micro attempted to secure the server from the cloud after releasing the latest version of Trend Micro Deep Security 7.0, distinguished by its ability to coordinate VMsafe API-based security applied to the hypervisor with additional protection on virtual machines for VMware environments. The new Deep Security product is aimed at addressing data breaches and malicious security threats, including SQL injection and cross-site scripting attacks, by providing an additional layer of security on any physical, virtualized or cloud-based server.