10 Open-Source Security Products You Can Download Now

Open And Free
Despite their reputation for sometimes being substandard, open-source security products are becoming more technologically sophisticated, on par with some of the most advanced data security products on the market. In fact, it's not surprising many commercial products incorporate open-source technology under the hood. And in light of the increasing necessity for robust but affordable protective technologies, security products are at the top of the "hot" list for impending open-source innovation. Plus, you can't beat the price.
Here are a few of the open-source security offerings that caught our attention.
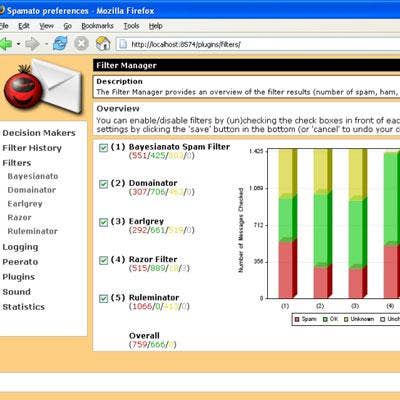
Spamato
Okay, it sounds like a highly processed liquefied lunch food. But this OS-independent open-source product provides a complete client-side spam filter that can integrate into popular e-mail clients such as Microsoft Outlook, or as an extension for other open-source e-mail clients such as Mozilla Mail and Thunderbird. It can also work as a standalone proxy component.
Written in Java, the open-source spam filter relies on numerous popular filtration algorithms, including Bayesian and Razor, and works across a multitude of platforms. It can also display the amount of blocked spam by geographic regions, to give IT administrators added visibility into their network environment.
Clam AntiVirus
The poster child for antivirus software, Clam AV is an open-source (GPL) anti-virus toolkit for UNIX, designed to scan e-mail gateways for viruses. It also provides a number of high-end functions including a flexible and scalable multithreaded daemon, a command line scanner and advanced tool for automatic database updates. At its core is an anti-virus engine available in a form of shared library.
Among its list of features are on-access scanning, an advanced database updater with support for scripted updates which issues updates multiple times per day. It also features built-in support for various archive formats and almost all mail file formats, as well as built in support for a range of executables and popular document formats, including Microsoft Office, MacOffice, HTML, RTE and PDF.
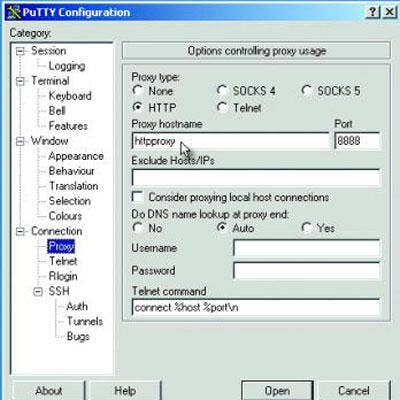
PuTTY
Essentially, PuTTY is a free implementation of Telnet and SSH client for Windows and Unix platforms, designed to run secure, remote sessions.
Originally the open-source client was written for Windows but now runs across various other operating systems, including some Unix-like platforms, as well as Mac OS X, in addition to mobile clients Symbian and Windows Mobile.
The latest version of PuTTy, version .60, was recently released, updating a myriad of bugs. Still in beta, PuTTY was written and is maintained primarily by Simon Tatham. The origins of the name "PuTTY" are not clear, although 'tty' is an abbreviation for a terminal in the Unix tradition, short for teletype.
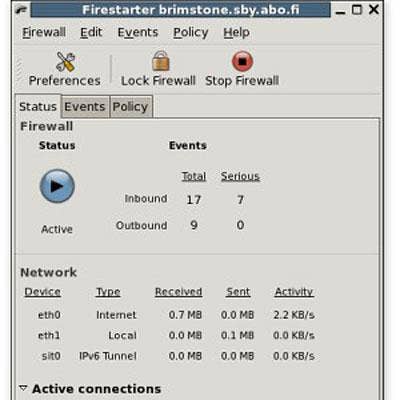
Firestarter
Firestarter, a free Linux firewall, can be used as a personal and server-side client. The open-source firewall comes equipped with an easy to use interface that can be applied to desktops, servers and gateways. It enables Internet connection sharing and allows users to define inbound and outbound access policies, with the option of whitelisting or blacklisting traffic.
Capabilities include monitoring traffic and firewall events in real time, which allow users to view active network connections, including any traffic routed through the firewall.
Snort
Users might recognize this open-source intrusion detection and prevention product by its signature mascot of a pudgy pink pig. But in actuality, Snort has three primary uses: a straight packet sniffer like tcpdump, a packet logger for network traffic debugging, or as a full-blown network intrusion prevention system.
At its core, Snort is an open-source network intrusion prevention and detection system (IDS/IPS), developed by Sourcefire, that combines signature, protocol and anomaly-based inspection. With millions of downloads and approximately 300,000 registered users, Snort is also one of the most widely deployed IDS/IPS technologies worldwide.
Its capabilities include performing protocol analysis and content searching/matching. It can also be used to detect a variety of attacks, such as buffer overflows, stealth port scans, CGI attacks, SMB probes, and OS fingerprinting attempts, among other things.
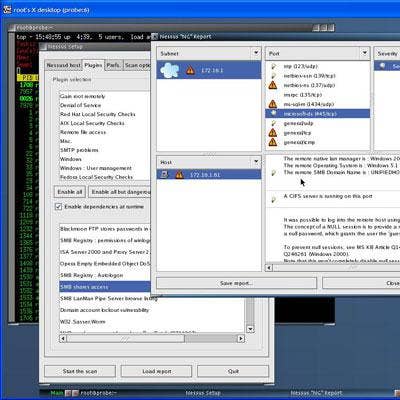
Nessus
This open-source vulnerability scanner comes with a slew of high-end features, including high speed discovery, configuration auditing, asset profiling, sensitive data discovery and vulnerability analysis of the security posture. The scanners can be distributed throughout an entire enterprise, including physically separate networks.
It even touts a Nessus iPhone application, available for free download at the App Store, featuring remote starting, stopping and pausing of network scans as well as the ability to analyze scan results from both the iPhone and iPod Touch. The mobility component aims at improving incident response times by allowing security professionals to respond to an incident to quickly by logging onto a Nessus scanner from their mobile device to find a vulnerability.
Wireshark
As an open-source project first developed in 1998, this network protocol analyzer is considered by many to be the standard across many industries and educational institutions.
Like its commercial counterparts, Wireshark has the ability to inspect hundreds of protocols and capture live data as well as conduct offline analysis running on Windows, Linux, OS X, Solaris, FreeBSD and NetBSD among others. It also touts a powerful display filter and can read data from just about anywhere, including a Ethernet, ATM, Bluetooth, USB, Token Ring and others. Network data can be browsed via a GUI, or via the TTY-mode TShark utility.
Additional capabilities include VoIP inspection, decryption support for a variety of protocols, and the ability to implement coloring rules for the packet list for easy analysis.
Kismet
No doubt, the wireless network serves as the entry point for some of the most common security threats and malicious exploits.
As such, wireless network detector Kismet aims to keep unwanted visitors out. The wireless scanner serves as a sniffer and intrusion detection system, identifying networks by passively collecting packets that detect standard named networks, hidden networks, and the presence of nonbeaconing networks via data traffic.
The open-source product can integrate with any wireless card that supports raw monitoring mode, enabling it to sniff out any malicious traffic. It also supports plugins that enable other media sniffing technologies such as DECT.
Altogether, the detector features a client/server architecture and includes PCAP file logging, multicard and channel hopping support, runtime WEP decoding, hidden SSID decloaking and XML logging, as well as support for Linux, OS X, Widows and BSD.
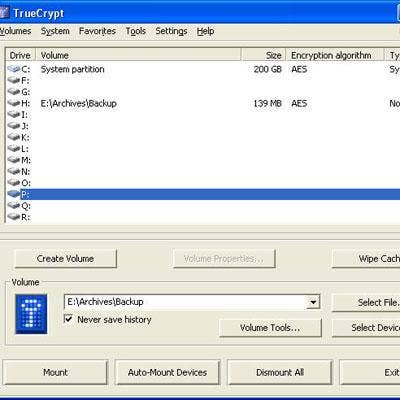
TrueCrypt
TrueCrypt is a free open-source software system for establishing and maintaining what its authors call "on-the-fly" encryption, which automatically encrypts or decrypts information right before it is loaded or saved, without any user intervention.
The product can encrypt every file system, such as file names, folder names and file contents, enabling users to only access the encrypted data with a correct password or encryption key. Files can be copied to and from a mounted TrueCrypt volume like any normal disk or drag and drop operation. Files can conversely be decrypted on the fly while they are being read or copied from an encrypted TrueCrypt volume.
Additionally, the product can create a virtual encrypted disk within a file, encrypt entire storage devices, such a USB flash drive or hard drive, and encrypt a drive with Windows installed. Encryption is conducted automatically and in real time, and can be hardware-accelerated on modern processors. Additionally, parallelization and pipelining functions allow data to be read and written fast.
BackTrack
It could be thought of as a free, one-stop-shop for whitehat hackers interested in breaking into wireless, exploiting servers, performing Web application assessments, or social engineering a client. BackTrack is in fact a Linux-based penetration testing arsenal, dedicated to aiding security professionals perform assessments in a purely native environment dedicated to (whitehat) hacking. The open-source product is dedicated to the penetration tester, but customized for every package, kernel configuration, script and patch.
BackTrack is intended for all audiences ranging from seasoned security professionals to newcomers. Funded by Offensive Security, the tool promotes a quick and easy way to find and update the largest database of security tools.
BackTrack originally started with earlier versions of live Linux distributions, initially conceived to be an all-in-one live CD used on security audits, crafted to leave no traces of itself on the laptop. It has since expanded to being one of the most widely adopted penetration testing frameworks in existence used globally by the security community.