5 Ways To Manage BYOD And Protect Sensitive Healthcare Data

The BYOD Phenomena
Employees are buying smartphones and tablets in record numbers and in some cases are insisting that they can use their personal devices to connect to corporate systems. According to the federal government's HealthIT.gov website, healthcare organizations need to decide whether those mobile devices can be used to access patient health information or used as part of the organization's internal systems.
From assessing the security risks involved to developing a strategy and establishing BYOD and mobile device policies and procedures to training and communicating with staff and patients on those policies, here are five tips to help manage BYOD and protect sensitive healthcare data within your organization.

Identity Management
According to Pricewaterhouse Coopers (PwC) Health Research Institute's January report, "Top Health Industry Issues of 2013: Picking up the pace on health reform," hospitals need to address identity management issues for patient and employee mobile access to information. BYOD password policies should insist on strong passwords -- no dictionary words -- and be void of personal information. Passwords should be eight characters in length and use a combination of upper and lowercase letters with at least one number and one character. Consider using multifactor authentication. PwC touts a role-based system that tightly manages privileges based on each employee use case. Care must be taken to assign staff to the correct roles and then to set the access permissions for each role correctly with respect to the need to know. The system needs auditing and reporting capabilities.
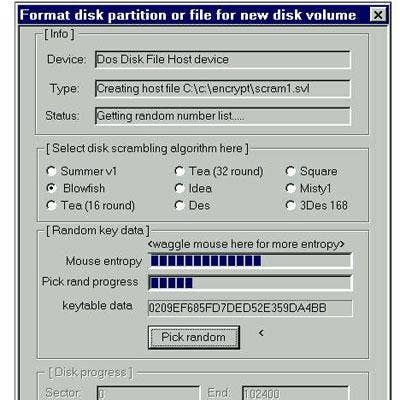
Encryption For Data Protection
The federal government's "meaningful use" program calls for encryption on end-user devices. The program provides financial incentives for the use of certified electronic healthcare records technology to boost health and efficiency goals. Under the program, organizations must use secure electronic messaging to communicate with patients; track medications from order to administration with assistive technologies and give patients the ability to view, download and transmit their health information in a timely manner online. Mobile devices that cannot support encryption should not be used. According to PwC, beginning in 2014, failure to comply will mean the loss of incentive payments and, in 2015, penalties.

Privacy And Security Policies
Privacy and security policies need to be communicated to both consumers and employees. As communication via email and text gains popularity, consumers will need to better understand the security controls in place to protect their sensitive data. Security policies also need to be reviewed and adjusted on a periodic basis. User awareness training for employees should be continuous and thought provoking, say experts.
Establish A Security Culture
Employees should be considered the first line of defense, but experts say they are also often considered the weakest link. The healthcare practice needs to show that it is willing to implement strong security policies, enforce them and put in place the proper safeguards to secure data. Employees should be trained on how to use newly implemented security systems. Executives and management must set a good example. Accountability and taking responsibility for data security should be one of the healthcare organization's core values.

Beware Of BYOD Costs
PwC explains that the costs of BYOD may outweigh what hospitals save in hardware costs. A 2012 study conducted by the Aberdeen Group found that BYOD, on average, costs companies 33 percent more than adopting a company-owned device policy. Additional policy concerns and new security controls could drive up the cost. For example, adding a mobile device management platform to add transparency and boost functionality across multiple device platforms will cut into any anticipated BYOD savings.