6 Steps To Address BYOD: A Security Management Roadmap
BYOD Timeline Begins With Assessment, Policy Creation
Managed security service provider Solutionary created a BYOD timeline in its 2013 Threat Report. Failing to address BYOD is one of 5 costly security weaknesses, according to the firm's report. The firm's timeline begins with policy creation, includes user education, policy enforcement and deploying some form of mobile antivirus. A policy to force data encryption and remote wipe capabilities should also be implemented, the firm said. The SANs institute, a security research and education organization, provides mobile security policy templates for further guidance.
1. Conduct A BYOD Assessment
Organizations can't create effective security policies if they are blind to exactly what needs to be protected, say security experts. A thorough assessment will help identify the types of devices already in use in the organization and the corporate systems and data that is already being accessed with them. Solutionary said that once a clearer picture has been established, policy can be developed with legal counsel. Obtaining executive support is vital to creating policies that are effective, the firm said.

2. Conduct User Awareness Training
Organizations that have BYOD policies need to communicate them effectively. That means providing training, preferably on a regular basis on the security threats that affect personal smartphones and tablet devices. While the focus is on corporate data policies, some experts believe that teaching employees how to protect themselves and their families from cybercrime can help create a more security-aware culture in the organization.

3. Keep Up With Patch Management
When new device firmware is pushed out and when applications receive an update it is a best practice to apply it as quickly as possible. Patching desktop devices is as important as patching desktop computers and servers, Solutionary said. Enterprises may need to limit the devices they support in order to handle the updates required, the company said.

4. Prohibit Jailbroken Devices
Jailbreaking a smartphone or tablet enables the owner to install a custom operating system and programs that have not been vetted by Google or Apple. While estimates vary, most experts say a small percentage of users jailbreak their device. Microsoft Exchange ActiveSync does not have functionality to detect jailbroken devices, forcing businesses to choose a Mobile Device Management product if they intend to enforce that policy. According to Solutionary, at a minimum, prohibit jailbreaking, limit third-party application resource and network access and require PINs or passwords to unlock devices.

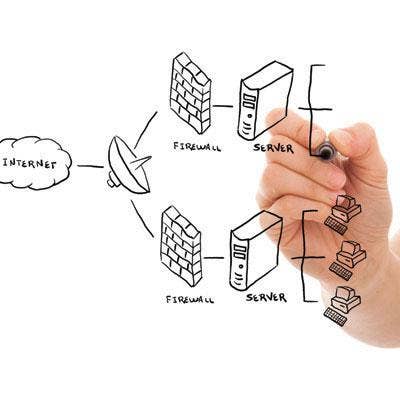
5. Restrict Corporate Network Access
Solutionary recommends that organizations consider network access control capabilities to restrict BYOD devices to separate networks or virtual local area networks (VLANs). Allow only the minimum access required to avoid putting sensitive data at risk, the company said.

6. Remote Wipe Is Necessary
A lost or stolen device is the No. 1 security problem with smartphones and tablets, far outpacing malware attacks and data leakage. Having the ability to remotely wipe a device is one of the minimum basic security measures necessary to address the problem. Use the features already built into Exchange ActiveSync (EAS) to enforce the policy. It can be used to enforce PINs on devices and force users to change them on a regular basis.