25 Hot Risk, Operations And Threat Intelligence Platforms At RSA 2020
Here's a look at 25 risk, operations and threat intelligence platforms released at RSA 2020 that help customers simulate realistic attacks and exploits, detect unknown threats and policy violations, and triage security incidents faster.

A Smarter Approach To Security
Vendors attending RSA 2020 have invested heavily in making it easier for customers and partners to detect unknown threats and policy violations, view correlated threats at an incident level, prioritize high fidelity threats, automate the analyst workflow, and automate investigations into the source of an outbreak.
From a risk and compliance standpoint, suppliers have doubled down simulating attacks and exploits on live networks, visualizing attackers’ potential lateral movement opportunities between assets, emulating the stages of a real-world nation-state or criminal attack, and illustrating to businesses their financial exposure to cyber risk.
As for threat intelligence platforms, vendors have been focused on automating manual threat research, identifying poor email practices used by third parties, triaging security incidents faster, and visualizing how security controls perform when they’re under duress.
Here's a look at what 25 key vendors are doing at RSA 2020 to gain more visibility into assets, formulate better business risks assessments, and enhance the effectiveness of their security programs.

Cisco SecureX
Cisco SecureX provides greater visibility across the entire security portfolio, delivering security analytics and automating workflows to speed threat detection and response. The platform unifies visibility across customers’ security portfolio in a cloud-native platform, Cisco said, delivering detection of unknown threats and policy violations via security analytics for more informed actions.
The platform automates common security workflows, including threat investigation and remediation, for more precise and efficient operations, according to Cisco. Cisco SecureX analyzes events and data across the enterprise, including from more than 150 million endpoints as well as network traffic from switches and routers, public clouds and private data center environments.
Within minutes, Cisco SecureX can identify who and what has been targeted and enable remediation using data enrichment across security products and threat intelligence feeds. The company said its new platform also brings the power of Cisco Talos threat analysts into the customer’s SOC to hunt for the latest threats.

FireEye Mandiant Threat Intelligence Suite
The FireEye Mandiant Threat Intelligence Suite offers incremental tiers of bundled offerings to help organizations advanced on their journey to intelligence-led security. The Intelligence Suite provides organizations with a significant decision advantage to help reduce security risk whether security is someone’s part time job or the organizations already has a dedicated threat intelligence team in place.
Organizations are increasingly looking to reduce their risk and augment their security with external threat intelligence services, FireEye said. However, many organizations don’t know where to start, FireEye said, while others have jumped right in without understanding what threat intelligence they need or how it should be used, which too often makes the process both ineffective and costly.
The Mandiant Threat Intelligence Suite is available in standard, advanced and enterprise tiered bundles, according to FireEye. The company said its Mandiant Threat Intelligence subscriptions and services are intended to give organizations visibility and actionable insights to improve their protection of assets, enhance the effectiveness of security programs and inform business risk assessments.
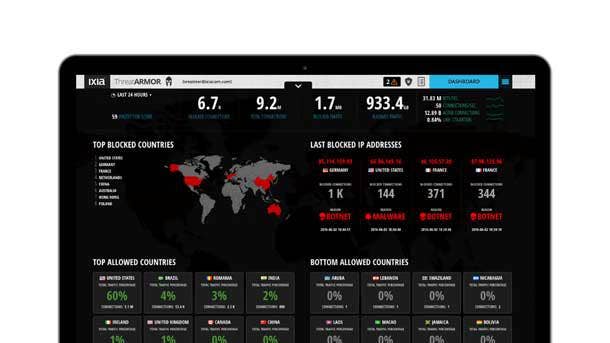
Keysight Breach Defense
The Keysight Breach Defense security operations (SecOps) platform is designed to help organizations measure and improve the effectiveness of their operational security. An element of the new platform is the Threat Simulator tool which enables network and security operations tools to measure the effectiveness of operational security by safely simulating the latest attacks and exploits on live networks.
Keysight’s Threat Simulator provides a continuous automated security assessment of end-to-end production network security infrastructures, enabling organizations to quickly spot gaps and environmental drift of security configurations. The tool uses a series of lightweight agents to simulate attacks on a live network without exposing production servers or endpoints to malware or attacks.
The Keysight Breach Defense platform also includes ThreatARMOR, a threat intelligence gateway which reduces the attack surface by blocking up to 80 percent of malicious traffic at the source. ThreatARMOR can block traffic from known bad IP addresses at line-rate speeds; block malicious IP addresses manually or automatically from SIEM tools; and block unassigned IP addresses and hijacked domains.

Recorded Future Security Intelligence Platform
The Recorded Future Security Intelligence Platform will enable collaborations across security functions and help security and IT professionals focus on specific pain points while still maintaining a holistic, long-term vision and providing a single authoritative source for all security needs.
The platform will include specific tools for SecOps and response, threat intelligence, brand protection, vulnerability management, third-party risk, and geopolitical risk, which will be made available throughout 2020. The SecOps and response module is designed for security operations analysts and incident responders to help triage security incidents faster and block threats at the network perimeter.
In addition, Recorded Future said its new risk rules are designed to identify poor email practices used by third parties that put organizations at higher risk for email scams, phishing, and spoofing. The rules also allow companies to tighten their web application security by measuring SSL certificate hygiene, which could help identify companies at greater risk of man-in-the-middle attacks or phishing scams.

Microsoft Threat Protection
Microsoft Threat Protection gives SecOps teams a correlated, incident-level view of threats so that they don’t have to manage individual alerts. The tool can investigate threats, respond to them, and restore affected assets to a secured state automatically while simplifying hunting across the landscape for signs of attack.
The product can also self-heal compromised user identities, endpoints, and mailboxes, allowing SecOps to focus on strategic projects and policies and put specialized knowledge to work across the threat landscape. Critical threat insights are shared in real time between Microsoft Threat Protection products to help stop the progression of an attack, according to the company.
The central Microsoft Threat Protection logic orchestrates and triggers actions on the individual projects like applying conditional-access policies when an identity-based threat is detected or cleaning impacted mailboxes, the company said.
Fortinet FortiAI
The on-premises Fortinet FortiAI appliance leverages self-learning deep neural networks (DNN) to speed threat remediation and handle time consuming, manual security analyst tasks. The FortiAI appliance automates investigations using DNN to identify the entire threat movement and uncover patient zero and all subsequent investigations in a sub-second, according to the company.
Through tailored threat intelligence, FortiAI learns new malware features as it adapts to new attacks instantaneously and reduces false positives. FortiAI’s self-learning artificial intelligence model does not require internet connectivity to learn and mature, enabling organizations with closed environments or stringent security policies to stay ahead of the threats.
Meanwhile, FortiAI’s Virtual Security Analyst embeds mature cybersecurity artificial intelligence directly into an organization’s network to deliver sub-second detection of advanced threats. As FortiAI’s artificial intelligence continues to mature, Fortinet said organizations benefit from having FortiAI’s Virtual Security Analyst transform and adapt threat protection and accelerate threat remediation.
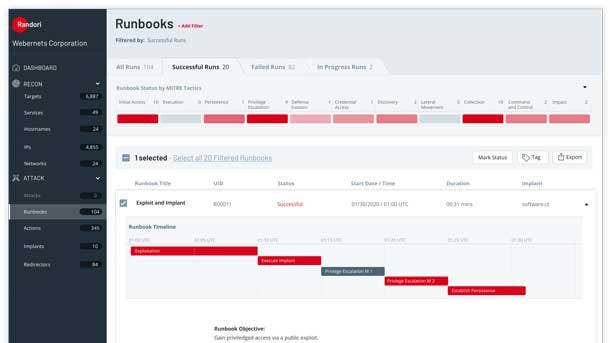
Randori Attack Platform
The Randori Attack Platform enables organizations to practice defending themselves against real-world attacks in a safe, cost-effective and continuous manner, helping them assess where and how they are most likely to be breached. Designed by offensive security experts, the platform mirrors today’s nation-state actors and criminal adversaries by emulating all stages of a real-world attack.
Combining hacker logic with automated surveillance, exploitation and attack tooling in a highly scalable platform, the Randori Attack Platform performs everything from reconnaissance to exfiltration. Unlike a simulation, which replays historical attacks inside artificial boundaries, Randori provides customers the ability to safely launch real-world attacks against their production assets.
The Randori Attack Platform identifies unexpected gaps in security defenses by testing them against real-world exploits and automated attack tooling, the company said. From there, the platform breaks down issues quickly, providing the insight security teams need to understand the promptly respond.
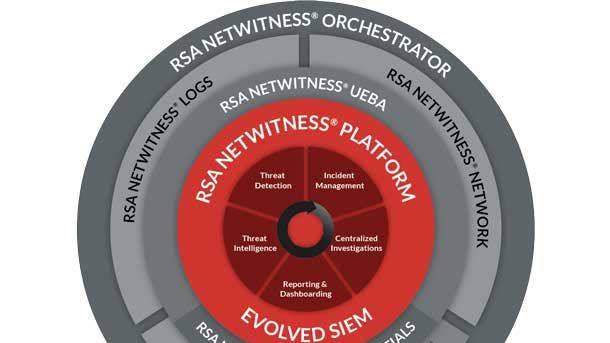
RSA NetWitness Platform
The latest version of the RSA NetWitness Platform includes functionality updates for automated network detection and response, user and entity behavior analytics (UEBA) and threat intelligence. The platform updates serve to eliminate false-positive threats and automatically improve response management, according to RSA Security.
The updates provide customers with an enhanced RSA NetWitness UEBA offering that leverages network metadata to accurately identify unknown threats. The company also unveiled new enhancements to the RSA NetWitness Orchestrator to deliver confidence that decisions are based on vetted, relevant threat intelligence.
With the latest edition of the RSA NetWitness Platform, the company said organizations can leverage machine learning to minimize blind spots in the threat landscape and accurately identify true threats while simultaneously improving incident response planning, management, and orchestration.
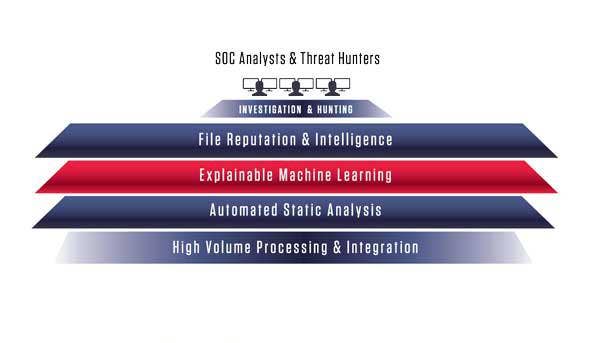
ReversingLabs Titanium Platform
New and enhanced capabilities for the ReversingLabs Titanium Platform deliver transparent and trusted malware insights that address the security skills gap. The platform includes new machine learning algorithm models, explainable classification and out-of the-box SIEM plug-ins, SOAR (Security Orchestration, Automation and Response) playbooks, and MITRE ATT&CK framework support.
The Titanium Platform introduces a new level of threat intelligence and delivers explainable insights and verification that better support humans in the incident response decision making process. The ReversingLabs platform provides transparent and context-aware diagnosis while automating manual threat research with results humans can interpret to take informed action on zero day threats.
Security operations teams using ReversingLabs Titanium Platform can automatically inspect, unpack, classify and verify threats in context with transparent and easy to understand results. By applying new machine learning algorithms to identify threat indicators, ReversingLabs said it enables security teams to more quickly and accurately identify and classify unknown threats.

Unisys TrustCheck
The Unisys TrustCheck Software-as-a-Service Platform helps organizations assess and communicate cyber risk in business terms, making it possible for organizations to measure the business impact of cyber risk and compare risk reduction scenarios on an ongoing basis. TrustCheck can help evaluate and understand financial exposure to cyber risk and making effective risk management decisions.
The platform leverages a cyber risk financial analytics application trusted to underwite billions of dollars of cyber risk, thereby bringing the financial rigor of the global insurance industry to enterprise cyber risk management. TrustCheck provides continuous access to a web-based portal with risk profile results and loss forecasts that are updated automatically as threat, industry risks and trends change during the year.
Meanwhile, TrustCheck’s new “Scenario Lab” module gives clients the ability to run configurable risk scenarios, refine them and compare the risk profile deltas to their existing baseline profiles. This enables the organization to make decisions in which the highest potential for risk reduction and financial loss reduction align, according to Unisys.
Fidelis Elevate
The latest release of Fidelis Elevate empowers security operations, threat hunting and incident responders through full visibility of the environment and attacker actions while ensuring the appropriate countermeasures. The platform is intended to empower security analysts to know their environment better than attackers and engage attackers prior to the point of impact, Fidelis said.
In the latest release, Fidelis extends the platform’s capabilities to enable security operations teams to move quickly and accurately detect threats and anomalous behavior while also allowing incident responders to remotely bring an endpoint to their fingertips. Fidelis maps the cyber terrain, including all managed and unmanaged assets, while also expanding the use of machine learning analytics.
Plus Fidelis Elevate provides Red Team and Blue Team simulations to visualize potential risk and attackers’ potential lateral movement opportunities between assets. These capabilities collectively provide cyber defenders with the critical insights to quickly detect, hunt and respond to threats at every step of an attack, according to Fidelis, keeping their business operations and data safe.

Sumo Logic Cloud SIEM Enterprise
Sumo Logic Cloud SIEM Enterprise provides automation to help security operations center (SOC) teams tame the growing number of unanalyzed security alerts and events, helping them bolster security and compliance. The new capabilities help identify and prioritize high fidelity threats and automate the analyst workflow, allowing SOC personnel to better manage real security events.
The offering by Sumo Logic modernizes security operations by automating the manual work for the security analyst, saving them time and enabling them to be more effective by focusing on higher-value security functions. The offering also provides insights and intelligence SOC teams can use to identify evidence of compromise and improve their ability to respond by understanding the impact of an attack.
Sumo Logic Cloud SIEM Enterprise enables customers to collect security data, better correlate the data with context, prioritize actionable insights, and automate analyst workflows to build and automate security operations from the cloud. And automated SOC analyst workflows can perform routine manual tasks including data collection, correlation and alert prioritization, according to Sumo Logic.
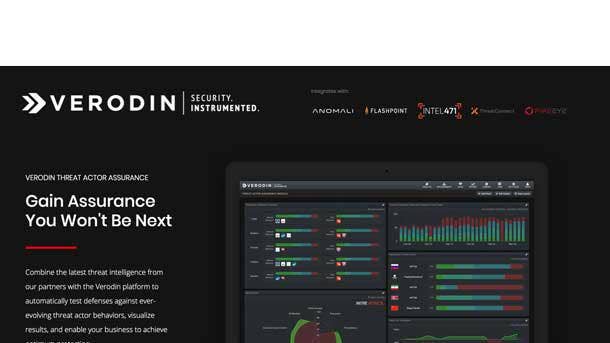
Verodin Threat Actor Assurance Module
The Verodin Threat Actor Assurance Module (TAAM) allows organizations to determine their ability to detect, block and alert based on the latest threat actors and their attack behaviors by seamless integrating threat intelligence into the Verodin platform. As a result, companies can visualize how their controls perform and implement improvements across enterprise technology, people and processes.
Verodin TAAM enables security teams to continuously validate and optimize their security program to avoid being in tomorrow’s news headlines, the company said. The module increases the value of organizations’ threat intelligence by directly connecting it to improvements in the effectiveness of security controls.
Companies can also bolster their security posture with additional reporting from Verodin TAAM that tracks improvements in protection as well as the deeper context on the adversaries behind the attacks. Moreover, Verodin TAAM continuously validates and optimizes security effectiveness, equipping IT leaders with the evidence needed to report on the effectiveness of their security program.

Devo Security Operations
Devo Security Operations combines critical security capabilities with auto enrichment, threat intelligence community collaborations, a central evidence locker, and a streamlined analyst workflow to scale security analyst effectiveness. The advanced analytics and streamlined workflow amplify analyst knowledge, Devo said, significantly reducing the time between detection and response.
The tool puts the data, context and intelligence needed to identify and investigate business-critical threats at analysts’ fingertips across the entire threat lifecycle, according to Devo. Devo Security Operations reduces analysts’ workflow from hours to minutes, the company said, keeping security operations centers (SOCs) ahead of even the most sophisticated adversaries.
Devo Security Operations provides a context-rich picture of entities, alerts and investigations without having to manually collect or query data, speeding the investigation process. The tool run queries across any volume of data, any number of sources, and any time horizon to proactively identify threats, according to Devo.
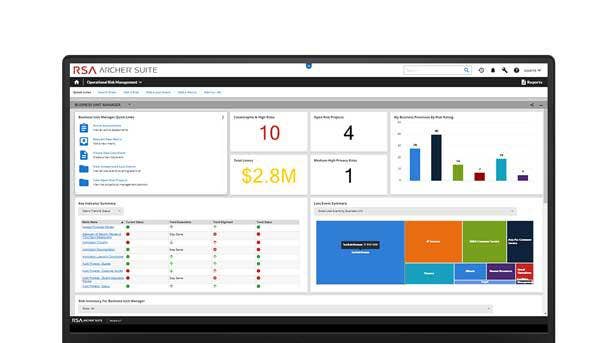
RSA Archer SaaS
RSA Archer SaaS provides organizations with the speed and agility of an integrated approach to managing risk delivered with the flexibility and scalability needed to navigate digital transformation and protect against loss while supporting strategic growth. The product makes it possible to implement the RSA Archer Suite in the cloud, delivering the rapid time to value associated with SaaS offerings.
RSA Archer SaaS allows organizations to comprehensively and proactively manage risk while lowering their total cost of ownership by removing the operational burden and expenditures associated with capital hardware and ongoing IT-related activities. The product offers quick time to value with the ability to stand up an instance in days or hours, as well as faster access to the latest features and functionality.
The tool also delivers the flexibility and scalability of the cloud to support organizations’ changing integrated risk management and business requirements, RSA said. RSA Archer SaaS is available now for all U.S. cloud customers, and will be made available to cloud users in Europe, the Middle East and Africa (EMEA) and Asia-Pacific later this year.

Fortinet FortiOS 6.4
Fortinet’s FortiOS 6.4 introduces new automation, scalability, performance and artificial intelligence capabilities through more than 350 new features that deliver full protection across the entire digital infrastructure. The operating system adds new features designed to support organizations’ digital innovation goals across the Fortinet Security Fabric and FortiGuard Labs.
FortiOS 6.4 secures and accelerates the network and user experience with a new intuitive SD-WAN orchestrator and granular application analytics to simplify and automate Secure SD-WAN deployments. The operating system also identifies and secures users and devices both on and off network through increased native device visibility through the integration of FortiNAC with the fabric topology map.
FortiOS 6.4 also enhances customers’ ability to secure and control cloud infrastructure and applications by offering increased Office 365 security coverage through integrations with FortiMail and FortiCASB. The operating system also automatically prevents, detects and responds to cyber threats with new threat detection and prevention capability at the endpoint with new anti-virus capabilities.
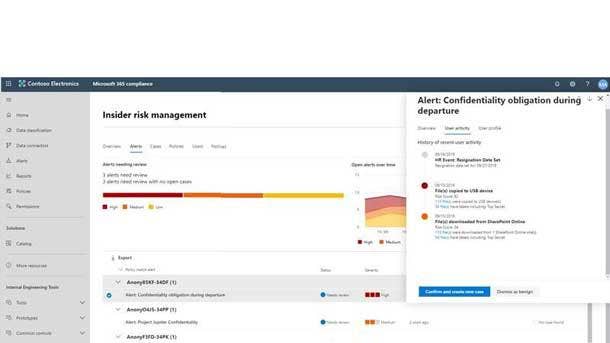
Microsoft Insider Risk Management
Microsoft Insider Risk Management offers CISOs and IT departments ways to identify, remediate and prevent insider risks to keep their organizations safe. By gathering signals from across Microsoft Office 365 and other third-party systems, Microsoft said Insider Risk Management can identify anomalies in user behavior and flag high-risk activities.
With privacy built in by design, Insider Risk Management leverages AI and machine learning to mitigate insider risks and better protect and govern the organization’s data. The machine learning in Insider Risk Management brings signals, sensitivity labels and content together in a single view, saving security teams time by allowing them to quickly make informed risk decisions and take action.
Insider Risk Management will be generally available to customers’ tenants in the coming days, according to Microsoft.

Gurucul Automated Intelligent Threat Hunting
Gurucul Automated Intelligent Threat Hunting uses artificial intelligence (AI) and machine learning to detect behaviors associated with cyber attacks and data breaches, while providing the most advanced capabilities for manual investigations. The company said it provides agentless, out-of-the-box integrations that collect, ingest and enrich data from disparate sources as massive scale.
Gurucul AI-enabled threat hunting capabilities apply advanced machine learning algorithms to assess a wide range of behavioral attributes to identify anomalies, outliers and indicators of compromise. It uses more than 1,600 pre-built cybersecurity and threat hunting models that cover the most commonly used cloud, IoT, business, infrastructure, database and network applications in the enterprise, Gurucul said.
The prebuilt threat libraries from Gurucul support a wide range of threat hunting use cases like insider threat detection, data exfiltration, phishing, endpoint forensics, malicious processes, ransomware detection, and network threat analytics. These prepacked libraries help analysts prioritize base activities and focus on the proactive investigation of new and unknown threat patterns using contextual data.

Spirent CyberFlood Data Breach Assessment
Spirent’s CyberFlood Data Breach Assessment Version 2.0 greatly expands network readiness testing by adding endpoint evaluation, incorporating evasion techniques and encrypted attacks used by attackers, and supporting MITRE ATT&CK and other frameworks. The release extends the flexibly deployable assessment from the perimeter and internal network security infrastructure all the way to endpoints.
The new version of CyberFlood Data Breach Assessment evaluates the security services and settings of Windows clients and servers using a simple agent, Spirent said. The release includes assessments for identifying evasion techniques and encrypted attacks used by attackers for command and control, exfiltration, and additional actions, according to the company.
CyberFlood Data Breach Assessment now supports frameworks for arranging and reporting on attack assessment exercises, including the increasingly popular MITRE ATT&CK framework. The tool supports additional security frameworks, and can augment those industry standards with its own methodology and reporting, providing a comprehensive assessment.
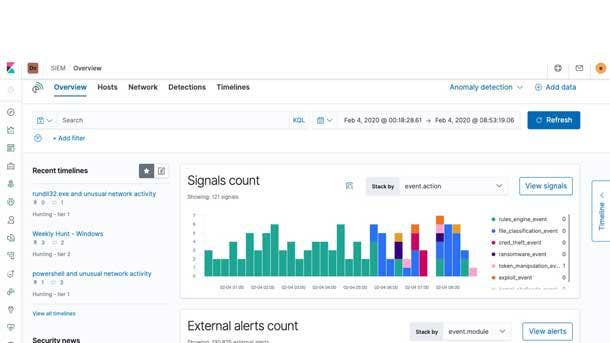
Elastic Security 7.6
Elastic Security 7.6 builds on the strengths of Elastic Endpoint Security and Elastic SIEM to deliver unparalleled visibility and threat protection through a unified interface. The release automates the centralized detection of threats in the SIEM app and enhances endpoint detection capabilities on Windows hosts, according to Elastic.
In addition, access to new data sources and improvements across the Elastic SIEM app further empower security practitioners to accelerate detection and response. Elastic Security 7.6 introduces a new SIEM detection engine to automate threat detection, minimizing mean time to detect and further reducing dwell time by surfacing threats that would otherwise be missed.
Elastic Security 7.6 delivers unprecedented levels of visibility and protection to Windows systems, which Elastic said are a major attack target due to their ubiquity and lenient user permissions model. The release deepens visibility into Windows activity and resiliently collects and enriches data from locations otherwise vulnerable to the evasion techniques of advanced threats, according to Elastic.

Panaseer Business Risk Perspectives
Panaseer Business Risks Perspectives will, for the first time, allow enterprises to continuously monitor total security risk, segmented to critical operations. The ability to continuously view risk across all security areas and asset types, personalized for any stakeholder, business process, or business function, paves the way for effective prioritization and remediation of an organization’s most critical risks.
Panaseer said customers can now use its platform to understand the security risks for any business function or process. The findings can be seen and reported within any preferred security framework such as NIST and CIS, according to Panaseer.
Technology powers all facets of business, but Panaseer said it had previously been hard to relate the technology’s security risks to different areas of a business. Risk usually stems from people, processes and technologies at a faster rate than can be addressed by security and risk teams, according to the company.

SaltStack Protect 6.2
SaltStack Protect 6.2 integrates infrastructure automation and configuration management with the Tenable.io vulnerability management tool for closed-loop vulnerability remediation. Integrating SaltStack infrastructure automation with the Tenable.io vulnerability management tool should help security and IT teams streamline vulnerability remediation, according to the company.
The integration between SaltStack and Tenable is expected to help speed security enforcement, reduce threats caused by imperfect infrastructure cyber hygiene, and allow security operations teams to effectively collaborate within an actionable, all-in-one vulnerability management and remediation platform.
Customers told SaltStack the integration between Protect 6.2 and Tenable.io simplifies the process of remediating infrastructure vulnerabilities at scale and drives notable efficiency in patch management and vulnerability remediation workflows.

SIRP Security Score
The SIRP Security Score calculates an organization’s security score based on several internal and external factors, enabling organizations to more effectively prioritize risks, make informed decisions faster and respond more quickly to incidents. The module enables organizations to optimize processes for threat respond and vulnerability management for improved organizational efficiency, the company said.
SIRP provides security teams with instant access to four powerful modules: incident management; threat intelligence; vulnerability management; and risk management. The SIRP Security Score module makes security data instantly actionable by fusing information from those modules and assessing the risk to the organization, according to the company.
The module uses machine learning algorithms to assess security data relevancy and calculate security scores, SIRP said, enabling organizations to prioritize risks, make better decisions faster and respond more effectively.

Farsight Security Information Exchange
Enhancements to Farsight Security’s flagship Security Information Exchange data-sharing platform are expected to help security professionals measurably improve their prevention, detection and response to the latest cyberattacks. The introduction of Newly Active Domains data and SIE Batch should make it easier for customers to consume real-time data through the Security Information Exchange platform.
Security Information Exchange has the industry’s first real-time DNS Intelligence data feed that reports domains as they resume activity on the internet after ten or more days of inactivity. This data is useful for detecting, blocking and investigating domains used by threat actors who get new or reused expired domains, establish a positive reputation for those domains, and then use them for malicious activity.

Netsurion EventTracker 9.3
Version 9.3 of the Netsurion EventTracker co-managed SIEM delivers SOC-as-a-Service by including the company’s 24/7 security operations center (SOC) and integrating with the MITRE ATT&CK framework. Adopting the ATT&CK framework within EventTracker should help improve threat hunting and standardize vocabulary, Netsurion said.
As a result, Netsurion said users benefit from better and more comprehensive discovery of attacks that are ongoing, giving users a detection and investigation advantage during the first critical moments when a problem has been discovered. And because it created a common taxonomy for describing patterns, ATT&CK makes it easier to share threat intelligence with consistency, accuracy and effectiveness.
The ATT&CK framework’s description of tactics and techniques allows defenders to identify relationships between individual observations and known campaign or threat actors, making it possible to block those tactics and enable more effective defense, detection, and remediation.