30 Hot New Cybersecurity Products Announced At RSA Conference 2019
From blockchain implementation testing and identifying suspicious users in real-time to hunting for advanced threats on mobile devices, here's a look at 30 key security offerings unveiled at the RSA Conference this year.

The Best And Brightest In Security
Vendors are taking advantage of RSA Conference 2019's bright spotlight to launch new offerings, features, platforms and tools that will set the stage for months and years to come. For the more than 600 exhibitors typically found at RSA, the gathering provides an opportunity to promote new products and highlight shifts in strategy to an audience of more than 42,000.
Some of the more common areas for product innovation this year include application security, cloud security, risk and compliance, and web security. CRN broke out the two most popular areas for new product development – network and endpoint security, and orchestration, incident response and threat intelligence – into their own standalone slideshows.
From blockchain implementation testing to identifying suspicious users in real-time to hunting for advanced threats on mobile devices, here's a look at 30 key security offerings announced at RSA Conference 2019.

IBM X-Force Red Blockchain Testing Service
The IBM X-Force Red Blockchain Testing Service will evaluate the entire implementation process including chain code, public key infrastructure and hyperledgers. It will also test the backend processes, applications and physical hardware used to control access to and management of the blockchain networks.
IBM X-Force Red will evaluate how permissions to access and add information to the blockchain are administered, including password policies, susceptibility to brute force attacks, and the implementation of two-factor authentication. The team will also test for the secure creation, management, and distribution of digital certificates and keys associated with the blockchain network.
Common libraries and component dependency hacking can be tested by X-Force Red during design and implementation to ensure secure dependency signatures and a trust build pipeline. And while smart contracts allow for trustless execution of agreements by parties on the blockchain, IBM said proper penetration testing can still find exploitable flaws in those agreements.
CylancePERSONA
CylancePERSONA combines continuous biometric behavior and user conduct monitoring to identify suspicious users in real-time to prevent compromises. Its sensors are able to detect and score both malicious and anomalous conduct.
The tool monitors user activity and calculates a Cylance Trust Score; if the user trust score drops below a given threshold, step-up authentication action or suspension can be automatically initiated. CylancePERSONA continuously monitors user behavior with real-time detection of suspicious keyword and mouse actions that could indicate an imposter.
The offering provides real-time monitoring of user actions with instant identification of anomalous user activity to indicate a possible remote account takeover. CylancePERSONA is also able to interrupt user activity automatically upon detection of anomalous or suspicious actions with responses such as user logoff, suspended processes, and step-up authentication.

CrowdStrike Falcon for Mobile
CrowdStrike Falcon for Mobile enables security teams to hunt for advanced threats on mobile devices, providing unprecedented visibility into malicious, unwanted, or accidental access to sensitive corporate data, while protecting user privacy and avoiding any impact on device performance.
With Falcon for Mobile, security teams have real-time visibility into the health and security posture of mobile devices in their organization, and are able to immediately identify vulnerable devices. Organizations can for the first time perform proactive threat hunting on mobile devices, leveraging new telemetry types such as mobile network activity, clipboard actions, and peripheral monitoring.
Falcon for Mobile provides enhanced monitoring of enterprise application behavior on Android, giving security teams unprecedented visibility into data that allows them to more quickly uncover malicious activity. And telemetry from traditional endpoints is presented alongside telemetry from mobile devices in a single interface to enable rapid, comprehensive security incident investigations.

Microsoft Azure Sentinel
Azure Sentinel aims to stand out from other SIEM (security information and event management) tools by leveraging the scalability and flexibility of the cloud and by tapping artificial intelligence to reduce cyberthreat noise.
The launch comes at a time when massive volumes of data have created issues for security professionals, who are often too overwhelmed by alerts to focus on solving complex security problems, according to Microsoft. Early partners working with Azure Sentinel include Accenture, Insight and New Signature, Microsoft disclosed.
The use of AI in Azure Sentinel has helped to enable a 90-percent reduction in "alert fatigue" among early users, wrote Ann Johnson, corporate vice president for cybersecurity at Microsoft, in a blog post. Organizations can bring data into Azure Sentinel from Office 365 for free, where it can be analyzed alongside the organization's other security data, Johnson said.

SonicWall Cloud App Security 2.0
SonicWall Cloud App Security 2.0 provides real-time protection for business-critical SaaS applications to thwart never-before-seen malware variants, targeted phishing attacks, and account takeover due to compromised credentials and data loss. It supports Microsoft Office 365, G Suite, Box and Dropbox.
The products integrate with the Capture ATP sandbox service to identify and mitigate malicious malware or files stores in SaaS offerings such as OneDrive and SharePoint. This extends SonicWall's automated breach detection and prevention capabilities into sanctioned SaaS environments, making it possible for monitor user-to-cloud and cloud-to-cloud traffic to identify unapproved cloud applications.
Cloud App Security 2.0 also includes machine-learning anti-phishing capabilities that are trained to catch malicious emails missed by the built-in security controls of cloud email platforms, SonicWall said.
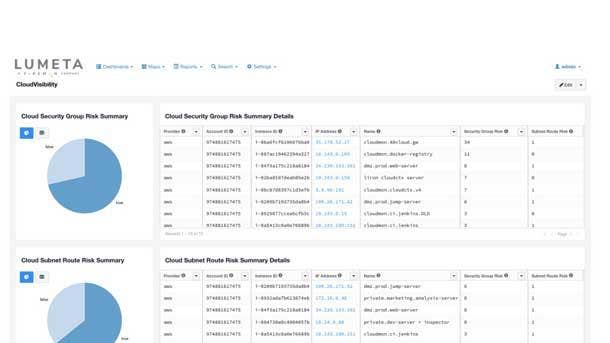
FireMon Lumeta CloudVisibility
Lumeta CloudVisibility introduces real-time infrastructure visibility, change monitoring and leak-path detection for enterprises in any phase of their cloud migration, regardless of cloud platform. The platform supports physical, virtual, software-defined, on-premise and hybrid cloud environments.
The product is built for large enterprises that require seamless visibility of assets into the cloud. It allows for multi-cloud, multi-account visibility, rolls up centrally into security operations, and is capable of attributing silos of cloud accounts and resources to the proper owner.
Lumeta CloudVisibility can expose and remediate hidden sources of risk with extensive visualization and visual analytics capabilities. Specifically, FireMon said the product can rank and prioritize high-risk cloud instances, determine by which path cloud assets attach to the enterprise, and determine leak paths from cloud infrastructure to the internet.
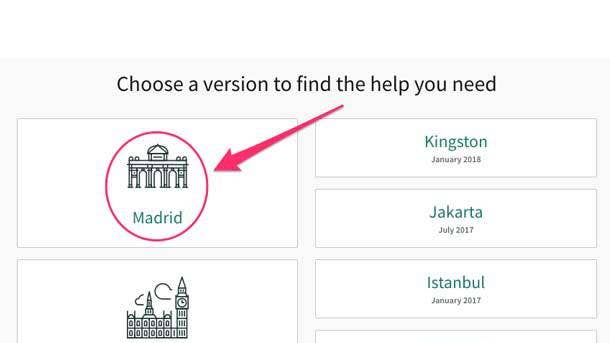
ServiceNow Now Platform Madrid Release
The Now Platform enables organizations to respond more quickly to security incidents, vulnerabilities and enterprise risk through a combination of exploit enrichment and continuous risk monitoring.
The platform's exploit enrichment tool enhances vulnerability prioritization with known exploit intelligence. The feature aggregates information from multiple sources, prioritizes vulnerabilities associated with an exploit, and incorporates the findings into the dashboard and risk score.
The continuous risk monitoring feature, meanwhile, is focused on quickly identifying high impact vulnerabilities based on ramifications for the business, ServiceNow said. The Now Platform ingests vulnerability data, identifies vulnerabilities and generates issues in real-time by looking at key risk indicators, and automatically updates its role-based dynamic dashboards.
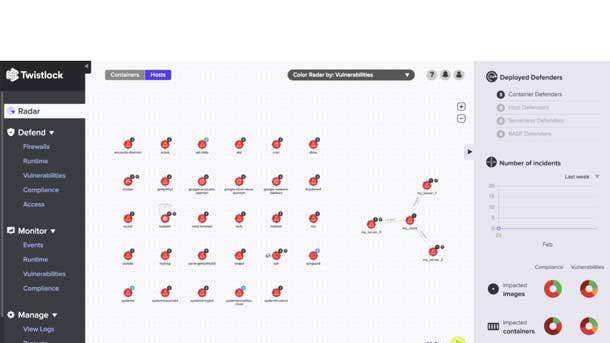
Twistlock 19.03
Twistlock 19.03 is the first comprehensive cloud native security platform to protect across hosts, containers, and serverless environments in a single product that's API enabled. It covers all workloads regardless of what underlying compute technology powers them.
The platform includes a distributed firewall that stresses automated learning and workload awareness to provide micro-segmentation of apps in a least privilege connectivity mesh. File integrity monitoring, meanwhile, allows host file systems to be watched for specific changes to directories and files.
Twistlock 19.03 also keeps a self-managed, high performance local log of forensic activity and selectively forwards this data to the Console if there's an incident. The platform also allows organizations to define discrete runtime behaviors such as preventing local access to cloud provider metadata or running processes within specific parameters.

BitSight Peer Analytics
BitSight Peer Analytics provides security and risk leaders unprecedented visibility into the relative performance of their security programs against their peers and sector. This makes it possible for companies to set achievable security performance improvement goals, effectively allocate limited resources, and efficiently prioritize security efforts.
The offering provides security leaders with real-time access to broad, deep, meaningful and objective data and metrics on industry-wide security and peer-level performance across multiple categories of vulnerabilities and incidents. The tool allows customers to compare themselves to groups of hundreds of even thousands of companies based on industry, sub-industry, company size, and other benchmarks.
Peer Analytics helps organizations uncover the factors that most significantly affect their industry's security performance standard and pinpoint the biggest discrepancies with their peers. It also allows organizations to confidently distribute limited resources and prioritize security team efforts for the greatest impact on security performance improvement.

Tripwire Penetration Testing And Industrial Cybersecurity Assessments
Tripwire's Penetration Testing Assessment leverages highly-skilled cybersecurity experts who discover and exploit vulnerabilities in an organization's IT environment, while the Industrial Cybersecurity Assessment takes into account the operational technology requirements of utility, manufacturing, oil and gas, and critical infrastructure operators.
The Penetration Testing Assessment examines how authentication and data traffic flows throughout the network to establish the roles of various systems. It also examines how communication moves between a system and its users, providing the information needed to design protective control mechanisms.
To identify exposure in industrial environments, Tripwire said its team of security professionals review data from automated vulnerability scanners, proprietary tools and manual assessments. Vulnerabilities and then manually validated in order to determine if it represents actual exposure, how that could impact systems on the network, and if mitigating factors or prerequisites may inhibit exploitation.

Synopsys Polaris Software Integrity Platform
The Synopsys Polaris Software Integrity Platform simplifies and enables comprehensive application security from developer to deployment. It allows team to detect and remediate vulnerabilities earlier in software development, integrate and automate security analysis throughout the software development lifecycle, and manage application security risks across the entire application portfolio.
The platform helps developers remediate security vulnerabilities earlier in development when it's more efficient and cost-effective, Synopsys said. It also enables developers to address vulnerabilities while they are coding, therefore producing a more secure codebase prior to checking it into their repository.
The cloud-based central server of the Polaris Software Integrity Platform provides the flexibility to manage deployments, initiate security scans, analyze results, and coordinate remediation activities. It also helps security teams view application security risk holistically with consolidated reports and interactive dashboards that combine information from multiple security analysis engines.

Unisys Stealth(identity) 2.0
Unisys Stealth(identity) 2.0 automates the process of biometric enrollment and provides configurable APIs for integrating biometric authentication across physical and digital channels, including mobile devices.
The product strengthens defense against identity fraud by established trusted identities of individuals across multiple physical and digital channels, Unisys said. It also provides comprehensive control of biometric management processes as well as the flexibility to adapt to and leverage advancements in technology to consistently stay ahead of fraudsters.
Through automation, Stealth(identity) clients can process enrollments without manual intervention, including tasks like biometric quality checks and identity-proofing prior to enrollment. Plus configurable authentication workflows and APIs allow integration of biometric authentication for applications such as password-free online transactions and self-service kiosks at airports and border crossings.

Ericom Shield
The latest version of Ericom Shield uses sophisticated algorithms, URL filtering capabilities and smart business logic to eradicate phishing, business email compromise, and other social engineering attacks before they can impact the user and the organization.
The company's phishing protection delivers a safe, phishing-free browsing experience to users. It also empowers security administrators to choose from among a range of responses when a suspicious phishing attack has been detected, based on the threat probability level as well as established organizational policies.
For instance, a warning may be issued to and acknowledged by users before they can continue to the suspected phishing site. Alternatively, users may be allowed to proceed to the website using 'Read-Only' mode, which prevents them from entering information on the website using their keyboard or via the browser's copy-paste function.
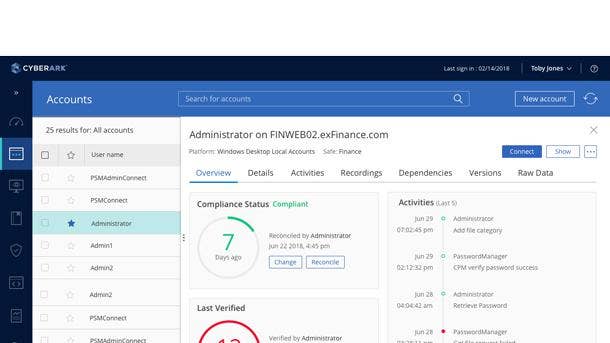
CyberArk Privileged Access Security Solution v10.8
The CyberArk Privileged Access Security Solution v10.8 is the first-of-its-kind to automate detection, alerting and response for unmanaged and potentially-risky AWS accounts. The version also features industry-leading Just-in-Time capabilities that deliver flexible user access to cloud-based or on-premises Windows systems.
Organizations using CyberArk's offering can now track AWS credentials everywhere they're created as they're created, speeding up the on-boarding process for those unmanaged accounts. The tool can also send prioritized alerts for potentially risky behavior in the cloud such as activities that bypass the vault, Access Key theft or mismanagement.
Customers can now streamline the deployment of the CyberArk Privledged Access Security Solution to AWS for all core components including vaulting, session management and threat analytics. The release also features a new ability for the administrator to configure the amount of access time granted to Windows systems, whether cloud-based or on-premises.

Veridium InMotion
Veridium InMotion takes advantage of user behavior analysis to better protect users' identities and prevent malicious activity. It increases the reliability of native biometrics for all authentication by pairing behavioral data captured on smartphones with users' biometrics, making it more difficult for malicious actors to spoof their fingerprints or faces to gain access to corporate accounts.
The product collects information from smartphone motion sensors when the user initiates biometrics authentication. It requires just 10 authentications to get a baseline for most users.
Once a pattern of authentication is established, Veridium will rate the authentication with a confidence score. Based on risk factors, a low confidence score can initiate step-up authentication via text, email or phone. In high risk scenarios, Veridium said a low confidence score and multiple failed attempts could initiate the blocking of a user completely.

CyberBit SCADAShield Mobile
SCADAShield Mobile enables on-demand audits and provides asset discovery, threat detection and vulnerability assessment for use cases ranging from on-site compliance audits to understanding the security posture of an Industrial Control System (ICS) network during an emergency.
The product supports a wide range of OT protocols and monitors a multitude of ICS networks including oil and gas, utilities, power generation and distribution, smart buildings, and airports. It immediately reveals critical issues such as misconfigured or unpatched devices, unencrypted communications, vulnerabilities and potential threats within the network.
SCADAShield Mobile is housed in a 27-pound, water resistant suitcase small enough to stow in the cabin of an airplane, CyberBit said. It is designed for first responders, service providers, auditors and critical infrastructure network managers to passively monitor ICS network traffic.
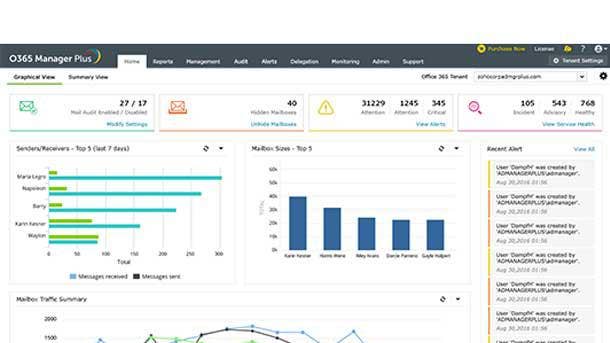
ManageEngine O365 Manager Plus
The latest version of O365 Manager Plus notifies users administrators when official emails contain personally identifiable information, classified information, or malicious content that may jeopardize the compliance and security of the enterprise.
O365 Manager Plus can now identify emails with personal and classified information in near real-time, according to ManageEngine. It also identifies all emails with attachments and notifies IT admins since they are one of the most common ways to deliver malware to end user systems.
The tool also analyzes internet message headers to better identify phishing emails sent by an attacker masquerading as a legitimate person, ManageEngine said. The headers provide technical details on the actual sender's email address, the platform used to compose the email, and the servers it has passed through.
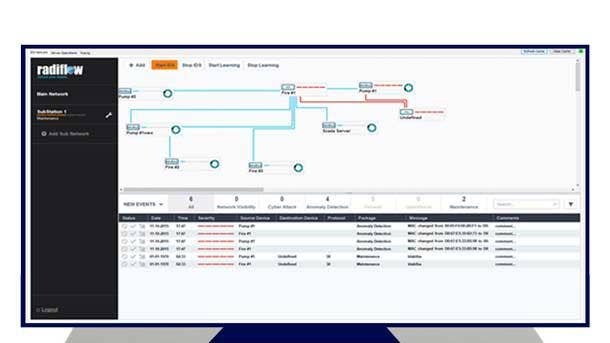
Radiflow iSID Industrial Threat Detection Solution
The new version of Radiflow's iSID industrial threat detection tool has added a dedicated risk analysis module that automates vulnerability mapping and assessment procedures. The new risk analytics module dynamically evaluates vulnerabilities according to the classification of attacker profiles and defense strategies for protecting specific functionalities and operational processes.
iSID dynamically calculates a risk and exploitability score for each device on the OT network based on the attacker models and defined defense strategies. The product also identifies the most critical attack vectors using these scores.
The scoring and mapping capabilities will make it possible for security analysts and risk managers to prioritize workloads based on the specific context of their OT networks as well as the impact on the business operations of the organization, according to Radiflow.

SafeGuard Cyber Discover
SafeGuard Cyber's new detection capability adds real-time, cross-channel analysis to proactive scans across the digital landscape, including deep web sites, the dark web, and the social internet. The new capabilities provide security professionals with a holistic view of actionable threat intelligence to digital channels, an area of expanding risks and priority for security teams.
The new Discover capability gives clients enhanced visibility into critical channels, helps them prioritize risks, and helps them easily and quickly respond to multi-vector threats, according to SafeGuard Cyber.
Discover is enhanced by Threat Cortes, SafeGuard Cyber's proprietary decision engine, which is powered by machine learning. Threat Cortex was designed to give CISO's SOC teams a simple way to receive actionable threat intelligence.

Cyxtera AppGate SDP IoT Connector
The AppGate SDP IoT Connector leverages the core principles of ZeroTrust to secure unmanaged devices, restrict lateral movement and reduce an organization's attack surface. It provides granular control of how and when devices connect to a network, as well as which network resources they can connect to.
IoT Connector is a part of AppGate, a unified security platform that enforces consistent access policies across user devices, servers, and IoT devices to shore up vulnerabilities across all network touch points.
AppGate Connector is a gateway between connectd IoT devices and the network. Devices make access requests to the AppGate Controller, and the platform sends an authentication challenge and then evaluates credentials and applies access policies based on the user, environment and location.
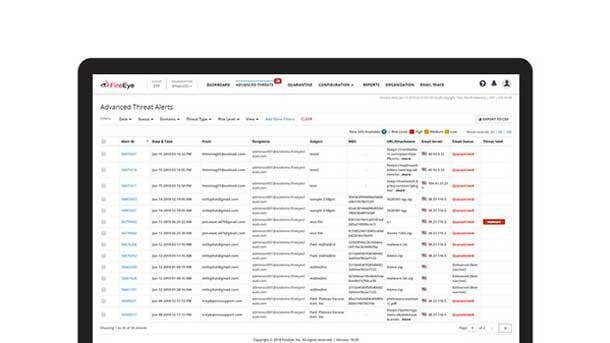
FireEye Secure Email Gateway
FireEye Email Security now provides full secure email gateway functionality, blocking inbound and outbound malware, phishing URLs, impersonation techniques, and spam.
In addition to standard secure email gateway capabilities such as antivirus, anti-spam and signature-based anti-malware, FireEye Email Security is designed to better protect customers with threat intelligence gathered from the frontlines. The company uses information from its incident response engagements and network of security researchers to continually improve the product.
FireEye Email Security addresses both display name and header spoofing using actionable tools, while email-specific threat intelligence serves as the basis for the broad toolset that leads to quicker detection. The company said the product can detect and block inbound and outbound advanced threat other tools miss.

Armor Platform
The Armor Platform is a combination of wearable GPS, biometric hardware, and patent-pending cryptographic and blockchain-enabled middleware intended to remove the complexity around identity governance.
The platform from Armor Scientific authenticates and authorizes users without the need for a username, password, or any other personal information. It enables users and devices to be added as a node to an assurance domain powered by cryptographic keys and a blockchain ledge.
The Armor Platform also protects access, allowing activity once the consensus of multiple other nodes has been reached. And the company relies on artificial intelligence and machine learning-powered risk awareness to learn how users work, ensuring that geospatial, behavioral and digital interactions are context-aware.

ISARA Radiate Quantum-safe Toolkit
The ISARA Radiate Quantum-safe Toolkit makes it easier to test and implement crypto-agility and quantum-safe cryptography directly into existing systems to better protect IT infrastructure from emerging threats.
ISARA said its technology enables migration to quantum-safe cryptography that's seamless and cost-effective with a standards-based approach incorporating the cryptographic agility recommended by the National Institute of Standards and Technology (NIST).
The toolkit has been updated to include a list consisting of the most promising algorithms from Round 2 of NIST's ongoing post-quantum standardization process. ISARA said Radiate is built for developers and includes tools to simplify the integration of quantum-safe cryptography into products.
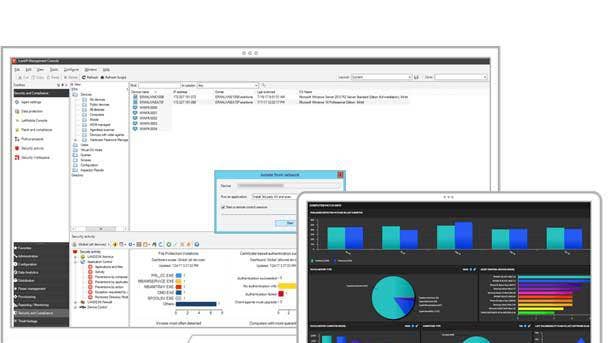
Ivanti Security Controls
Ivanti Security Controls offers comprehensive patch management for operating systems and third-party applications on physical and virtual servers and desktops. It also enables dynamic whitelisting and granular privilege management from a single management console.
The tool discovers online and offline workstations and servers, scans for missing patches, and deploys them where needed. The agentless technology for Windows systems minimizes the impact on system workloads, while options agent policies can also be applied for greater flexibility and patch accuracy.
Ivanti Security Controls supports third-party vulnerability assessments regardless of vendor, and identities the patches that relate to the Common Vulnerabilities and Exposures (CVEs). Plus controlled and authorized access to applications, services and components is enabled without extensive list management or constraining users, according to Ivanti.

Sophos Mobile Security With Microsoft Intune
Microsoft Intune customers running Sophos Mobile Security 9.0 are now able to configure access control fed by the latest mobile device threat information, enabling employees to work and access data securely from any device or location while maintaining corporate compliance.
Running on Microsoft Azure, the Sophos integration will enable IT administrators to configure individual device usage policies within Microsoft Intune to enable employees to be productive and work from the devices and application they prefer, while ensuring corporate data compliance.
If an individual endpoint is compromised, Sophos said administrators will have access to detailed security insights from Sophos Mobile Secure to enable them to more effectively decide when to lockdown an individual endpoint and deny access to corporate data. Sophos Mobile Security runs on both Android and iOS devices, and can share threat details with Microsoft to provide additional context.

Spirent CyberFlood Data Breach Assessment
CyberFlood Data Breach Assessment enables security operations and IT teams to validate security on production networks by delivering continuous automated assessment of security and data loss prevention policies using up-to-date threat intelligence.
Organizations using CyberFlood can assess their ability to stop data breaches, cyberattacks, and malware infections without requiring attack expertise or impacting internal IT team resources. And unlike simulation-based data breach validation tools, the CyberFlood offering accurately assesses an organization's security posture by emulating real-world attack, malware and DLP scenarios.
With this latest release of CyberFlood, customers can extend their in-house security teams by selecting optional services bundles from Spirent SecurityLabs’ professional services team. Specifically, customers can capitalize on Sprient's expertise in vulnerability scanning and penetration testing services to support deployment and management of the company's unique assessment solution.

Tripwire for DevOps
The new vulnerability scanning and compliance functionality of Tripwire for DevOps includes additional container registries and Amazon Machine Image types. As a result, Tripwire said more of the tools and processes used by organizations to integrate security into DevOps are supported.
Tripwire for DevOps has expanded its support to include: the Google Container Registry; the Quay.io remote registry; Docker registry HTTP API V2; the Amazon elastic container registry, and Windows and Linux Amazon Machine Image types.
Tripwire for DevOps provides configuration assessment and vulnerability management in containers across the DevOps lifecycle, according to the company. By fully automating the assessment of container images in the continuous pipeline and dynamically testing live instances of application containers in an isolated, cloud-based sandbox, Tripwire for DevOps can ensure that defined security standards are met.

Fortanix Enclave Development Platform
The Enclave Development Platform (EDP) allows developers to leverage Rust's built-in functionalities to help create more secure applications. It is an open-source software development kit that uses state-of-the-art security properties of the Rust language and Intel SGX to deliver a more secure application development platform.
The Fortanix EDP is fully integrated with the Rust compiler, which allows developers to immediately use new features, including non-lexical lifetimes, futures and async/await syntax, and improved compile-time speeds. The platform's open source licensing allows developers to build and sell or distribute the secure applications they create.
Rust extends the protection used by multiple Fortune 100 companies to developer environment, according to Fortanix. The company said developers are looking for solutions that deliver deterministic security since systems are always under attack.

Symantec Integrated Cyber Defense
Symantec has infused its Integrated Cyber Defense (ICD) platform with new capabilities related to shared intelligence and shared management across multiple technology components.
The platform security vendor said the ICD Exchange will make it easier for other software providers such as Box, ServiceNow, Microsoft and Anomali to quickly integrate and obtain more guidance around the data they can use from Symantec, according to Art Gilliland, EVP and GM enterprise products.
The ICD Exchange standardized APIs, Gilliland said, making it possible for technology partners to develop and deliver value to customers faster. With the ICD Exchange, Gilliland said products and systems from different vendors end up using the same language to understand what's happening in an environment.

Farsight Security DNSDB Community Edition
DNSDB Community Edition provides threat hunters, incident responders and other security professionals with actionable insights on IP addresses, domain names and other Internet infrastructure identifiers critical to an investigation.
Starting with a single suspicious domain or IP address, security professionals can query DNDSB Community Edition to find related DNS digital artifacts, from name servers to other IP addresses or domain names, to map an adversary's malicious infrastructure.
This entry-level version of the company's flagship product is free, and offers a subset of the full enterprise version of the product. Farsight DNSDM is the world's largest historical passive DNS database, with more than 100 billion DNS records.