Timeline Of Events In Microsoft's Malware-Related Seizure of No-IP's Domains

A Seizure Timeline
Microsoft obtained a court order last week that allowed it to seize control of 23 domains belonging to Vitalwerks Internet Solutions, a Reno, Nevada-based company founded in 1999 that runs No-IP.com, a popular free dynamic DNS service.
Microsoft convinced the court that No-IP wasn't doing enough to stop criminals from using the service to launch malware attacks on millions of Windows users. Microsoft said it's holding No-IP responsible for enabling criminals to spread the Bladabindi (NJrat) and Jenxcus (NJw0rm) malware.
No-IP alleges Microsoft's seizure caused outages for millions of legitimate websites and other users of the service. One SonicWall partner told CRN some customers that run security surveillance video solutions behind SonicWall firewalls suffered service outages.
Click through for a timeline of the events leading up to Microsoft's No-IP domain seizure along with the resulting impact.

June 19 -- Microsoft Files Restraining Order
Microsoft filed for an ex parte temporary restraining order from the U.S. District Court for Nevada against Vitalwerks Internet Solutions June 19. It also named in the restraining order two foreign nationals, Mohamed Benabdellah and Naser Al Mutairi for their roles in distributing malware to Windows users.
Microsoft said No-IP has become a go-to service for criminals looking to spread malware and control millions of PCs over the Internet.
"Our research revealed that out of all Dynamic DNS providers, No-IP domains are used 93 percent of the time for Bladabindi-Jenxcus infections, which are the most prevalent among the 245 different types of malware currently exploiting No-IP domains," Richard Domingues Boscovich, assistant general counsel in Microsoft's Digital Crimes Unit, said in a blog post.

June 26 -- Judge Grants Order
A judge granted Microsoft's request for a restraining order and transferred DNS authority for 23 free No-IP.com domains to Microsoft.
Boscovich said in the blog post that the transfer allows Microsoft to identify malicious traffic associated with No-IP.com and route it to its "sinkhole." Microsoft security researchers can then analyze and classify the threats and shut down the botnets associated with them.
Boscovich also said Microsoft will share this information with Internet Service Providers (ISPs) and global Computer Emergency Response Teams (CERTs) so they can use it to help clean up the damage caused by Bladabindi-Jenxcus and other malware.

June 30 -- Legitimate No-IP.com Users Begin Experiencing Outages
Microsoft intended to route 18,472 domains using No-IP's DNS services to its sinkhole, but its actions caused major collateral damage.
No-IP.com issued a statement claiming that "millions of innocent users" were hit with outages resulting from Microsoft's domain seizure, including some paying customers. The company made it clear the outages were not the result of a technical glitch on its end.
No-IP.com said Microsoft did not contact it before taking legal action to voice its concerns about the service, noting that the first communication it had with Microsoft was June 30.
"We have been in contact with Microsoft today. They claim that their intent is to only filter out the known bad hostnames in each seized domain, while continuing to allow the good hostnames to resolve. However, this is not happening. Apparently, the Microsoft infrastructure is not able to handle the billions of queries from our customers," No-IP.com said in the statement.
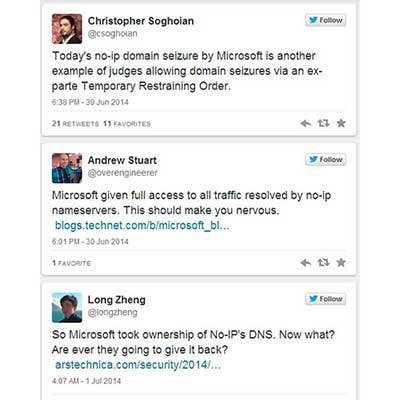
July 1 - Microsoft Comes Under Heavy Fire From Critics On Twitter
Many angry No-IP customers who'd been hit with outages vented their frustrations with Microsoft's actions on Twitter.
But it wasn't all vitriol, as well-known security and privacy commentators also weighed in with their thoughts on Microsoft's No-IP domain seizure.

July 1 -- No-IP.com Issues Affect Some SonicWall Customers
Some customers of SonicWall, a vendor of network security and content control hardware appliances, began experiencing outages related to Microsoft's No-IP.com domain seizure. Marc Harrison, president of Silicon East, a Manalapan, N.J.-based SonicWall partner, told CRN hundreds of his SonicWall customers were affected.
Some of these customers are apartment complexes that run security surveillance cameras behind SonicWall firewalls, using No-IP.com's dynamic DNS service to relay the video feeds, Harrison said.
SonicWall, which Dell acquired in 2012, supports No-IP.com and other dynamic DNS services in its products, and many of its customers use the services.

July 1 -- Microsoft Calls Outages Technical Glitch
Microsoft acknowledged that some legitimate No-IP customers were affected by what it described as a "technical error."
"Yesterday morning, Microsoft took steps to disrupt a cyber-attack that surreptitiously installed malware on millions of devices without their owners' knowledge through the abuse of No-IP, an Internet solutions service," David Finn, executive director and associate general counsel for Microsoft's Digital Crimes Unit, said in a statement.
"Due to a technical error, however, some customers whose devices were not infected by the malware experienced a temporary loss of service. As of 6 a.m. Pacific time today, all service was restored. We regret any inconvenience these customers experienced."

July 2 -- No-IP.com Provides Customer Update
Dan Durrer, No-IP.com owner and CEO, issued an update to customers explaining that it's working on a fix and would soon provide more information.
"We have been throwing everything we have at getting you back online with the least possible delay. For legal reasons, we have been restricted from reaching out to you, but we simply cannot stay quiet any longer. We are very close to a resolution and we will update you with more information as soon as we can," Durrer said in a statement.
Meanwhile, No-IP.com urges customers to share their thoughts and updates on Twitter using the #FreeNoIP hashtag.

July 2 -- No-IP.com Reports Some Hostnames Are Resolving
/**/ /**/
On Twitter, No-IP.com reported some hostnames began resolving. Services were not fully back to normal, but the company said they could be soon. It asked customers to tweet if their hostnames were resolving.
Meanwhile, Forbes reported records on the Domain Name System indicated Microsoft gave up control over many of the websites it had seized in its legal action. Microsoft declined to confirm this or comment on the matter to CRN.

Final Analysis: A Warning Shot Is Fired
Microsoft has been vilified in security circles for its handling of the No-IP.com situation, and there's no indication it won't continue to use the same tactics to go after cybercriminals.
This is the 10th such operation Microsoft's Digital Crimes Unit has conducted, and the third since the launch of the Microsoft Cybercrime Center last November, Boscovich said in the blog post.
"If free Dynamic DNS providers like No-IP exercise care and follow industry best practices, it will be more difficult for cybercriminals to operate anonymously and harder to victimize people online," Boscovich wrote. "Meanwhile, we will continue to take proactive measures to help protect our customers and hold malicious actors accountable for their actions."