Top 10 Data Breaches Of 2014 That Got Lost In The Noise

Annual Review Of Top Data Breaches Exposes Hidden Gems
It may surprise you that the most significant data breaches of 2014 aren't giant retailers or the nation's top universities. Some hidden gems can be found in the nearly 800 documented data breaches this year. They don't have to register in the millions of exposed records to have a major impact on individuals and the breached organization.
These breaches are in organizations across various industry verticals. The details reveal that they often stem from small, but significant, errors that characterize a repeated pattern of failing to address or maintain basic security practices. And, perhaps more significantly, they expose a security industry secret: It doesn't take layers and layers of technology to protect corporate assets. Organizations can gain the most value by addressing vulnerabilities and configuration weaknesses, process failures and poorly implemented security appliances that often provide a false sense of security. CRN pulled together this list of significant data breaches in 2014 that were "lost in the noise."

10. Stolen Employee Credentials In Massive eBay Breach
State Attorneys General are still investigating the massive data breach disclosed by eBay in May, impacting all 145 million of its users. The company said attackers gained access to the account credentials of more than 100 employees, allowing unauthorized access into eBay's corporate network. "Working with law enforcement and leading security experts, the company is aggressively investigating the matter and applying the best forensics tools and practices to protect customers," the company said. The lapse forced eBay to prompt its users to change their passwords.

9. Security Flaw Exploited In Oregon Employment Agency Breach
A security vulnerability in the management information system where customers register for job-search help and other services led to a breach at the Oregon Employment Department, impacting more than 850,000 people. The agency said it shut down the application and repaired the vulnerability after it was informed of it via an anonymous tip in October. The agency also added encryption to protect Social Security numbers. The measures were taken within hours of being notified of the lapse. The anonymous tip indicated that attackers gained access to the system.
Criminals gained access to a database containing customers' names, encrypted passwords, email addresses, physical addresses, phone numbers and dates of birth between late February and early March. The intrusion wasn't detected until May, when the company spotted the compromised employee login credentials.

8. Web Application Vulnerability Exposes Government Data
Herndon, Va.-based enterprise software maker Deltek said the account credentials of 80,000 employees of federal contractors were stolen in a breach of its web application in March. As many as 25,000 credit and debit cards may have been exposed in the lapse, Deltek said. It confirmed the breach, indicating that the attack was against its GovWin IQ web application, which is designed to track federal, state and local contracting opportunities. Deltek said it fixed the vulnerability targeted in the attack, and bolstered its user name and password processes.

7. Data Breach Highlights Physical Security Requirements
Thieves broke into the offices of Los Angeles-based medical billing and collections agency Sutherland Healthcare Solutions in April and stole computers that included names, Social Security numbers, billing information and sensitive medical diagnosis data on more than 340,000 California residents. The Los Angeles Times said the firm was offering a $25,000 reward for information leading to the return of the eight computers containing the data, or the arrest and conviction of those responsible. The reward hasn't been paid out. Lawsuits that are still ongoing against Sutherland allege the company failed to encrypt the data stored in the computers, and didn't notify victims in a timely manner about the security incident.

6. Health-Care Breach Stems From Medicaid Dispute
The Texas department of Health and Human Services announced a breach in August impacting approximately 2 million people, following the termination of its relationship with Xerox, which it had for a decade. The organization said it awarded a new contract with Accenture to handle Medicaid payments, but it alleges in a lawsuit against Xerox that it failed to turn over computer equipment and paper records containing sensitive health-care billing records and diagnosis information. The state has been at odds with Xerox over alleged misappropriation of millions of Medicaid payments made for unnecessary orthodontic services. Xerox refuses to turn over the patient information while it defends itself against the state's lawsuit over the funding.
5. Internal Threats Exposed In IRS Breach
A U.S. Treasury Department Inspector General's report documents the failure of the Internal Revenue Service to conduct security checks against contractors it hired to conduct printing, document recovery, courier and interpreter services, despite those contractors having access to sensitive information. The report exposed an incident in which a CD containing the sensitive information of as many as 1.4 million U.S. taxpayers was accessed by a courier with a criminal record. The report recommends that the agency conduct background checks on contractors that gain access to sensitive, but unclassified, information.
4. Payroll Company Roiled By Attackers
An attack in April against Mechanicsburg, Pa.-based payroll management company Paytime Inc. resulted in the exposure of the personal data, including Social Security and bank account numbers of 233,000 people. It took the company weeks to discover that an intruder penetrated the company's systems. The attackers stole account credentials associated with the firm's Client Service Center. Following a forensics investigation, the company said it implemented intrusion detection and network monitoring over the critical payroll systems. Solution providers told CRN that the additional technology can be effective in bolstering threat detection, but to be fully effective, organizations must plan for proactive management and incident response activities associated with the security gear.
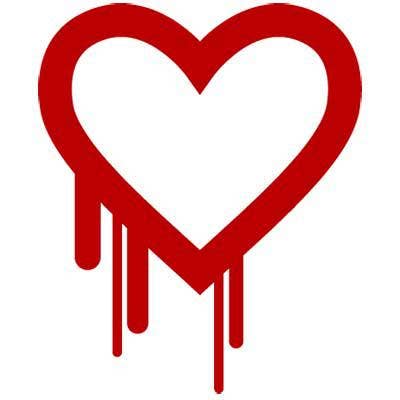
3. Heartbleed Associated With Massive Health-Care Breach
The Heartbleed OpenSSL vulnerability that forced networking vendors to rush out patches to customers is believed to have been at least partially the cause of a massive data breach at Community Health Systems Inc. The lapse was believed to have impacted up to 4.5 million patients. The company, which provides management, consulting and IT services for health-care providers, said its network was targeted by attackers in separate intrusions conducted in April and June. The lapse exposed patient names, Social Security numbers and other personal information.
David Kennedy, a security industry veteran and ethical hacker who heads Strongsville, Ohio-based TrustedSec, said the initial attack vector was a Juniper VPN, which was vulnerable to the Heartbleed flaw at the time.
2. Banking Trojan Costly For PA Plastics Manufacturer
A joint law enforcement and private-sector campaign in June took out the Gameover Zeus botnet and court documents filed by the U.S. Department of Justice associated with the takedown exposed a lengthy list of corporate data breaches that, until this year, had gone undocumented. One standout was Haysite Reinforced Plastics, an Erie, Pa.-based plastics manufacturer that was bilked out of more than $375,000 in October 2011. The Russian attackers, who are still at large, successfully infected several employee systems with the Zeus Trojan, and recognized that they got lucky, successfully infecting a system belonging to employees who had access to the company's coffers. Over a two-day period, they raided the company's bank account to the tune of $375,000. The attackers used social engineering to get the victims to install the malware, which could steal employee credentials or hijack their banking session and stealthily transfer the funds without the victim's knowledge.

1. Campaign Targeting U.S. Veterans
The Veterans of Foreign Wars of the U.S. announced a data breach of approximately 55,000 members of the organization in March. But the number of exposed records in this breach pales in contrast to the details that exposed the data in the first place. A targeted attack campaign, believed to have been carried out by a nation-state, used the VFW website to infect visitor systems. The attackers used a watering hole technique of identifying a legitimate website often visited by their targeted victims. The criminals then exploited a common website vulnerability, turning it into an attack platform. In the process, the attack exposed the user data contained in the underlying web server. The breach was investigated by security vendor FireEye and exposed an Adobe Flash zero-day vulnerability. FireEye traced the attack to a China-based group, which may have been seeking people who have access to military plans and contracts.