CRN Exclusive: Behind The Scenes At Symantec's Security Operations Center

Ground Zero In The Cybersecurity Fight
Fighting cyberthreats is no walk in the park. In an exclusive tour, CRN got an inside view into Symantec's Security Operations Center (SOC), where the security vendor tackles millions of pieces of malware every day. Based in Herndon, Va., the SOC was recently expanded in 2012 and houses state-of-the-art security technologies and personnel, including a live wall monitoring the latest threats, top-notch physical security and banners touting employee wins in the "CyberWar Games."
Keep reading for a behind-the-scenes look into what it takes to fight back against the "bad guys" every day.
Global Reach
This SOC in Herndon, Va., is one of four centers globally, with other locations in Sydney, Australia; India; the United Kingdom; and Japan. Symantec said it is building a "few more" right now. The company also operates 11 Security Response Centers around the world. The advantage of having centers around the world is that, in addition to allowing for 24/7 coverage, it allows for the security experts to gain more telemetry and intelligence based on local geographical location.

Physical Security
A SOC doesn't just need good cybersecurity, it also needs top-notch physical security. To enter the SOC, you need an authenticated badge and pass a corresponding biometric scan. Once you make it past the first steel door, you have to wait in a holding room for the door to close before being able to access the second door that leads to SOC itself.

Human Power
Across its centers globally, Symantec employs more than 500 security professionals that monitor and fight back against attackers 24 hours a day, 7 days a week. In this office alone, there are around 300 employees. The employees come to Symantec with backgrounds from government, machine learning, big data and analytics, hacking and more, and the security vendor invests heavily in training them using simulations and other techniques over the course of multiple months.
Using these cybersecurity capabilities, Symantec partners are able to augment or build their own managed services practice around the company's cybersecurity services.
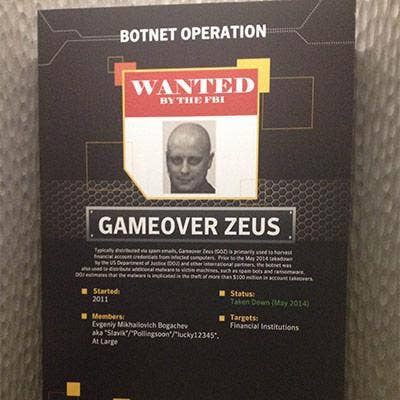
Latest Attack Groups
Symantec has posted some of the latest attack groups, with information on who they are and what attacks they are known for. Framed as "Wanted" posters, some of the attackers have been caught, while others are still at large.
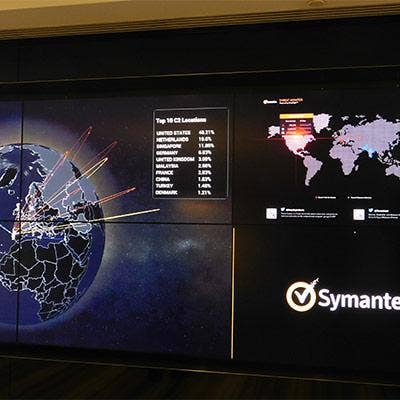
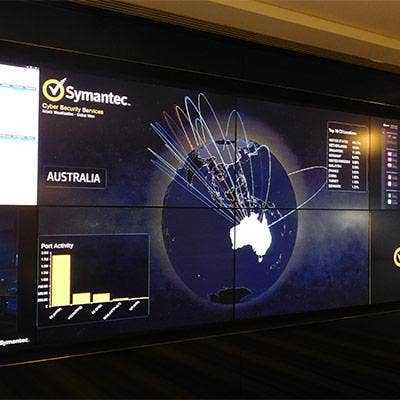
Monitoring Global Threats
In this SOC and others around the globe, Symantec sees up to 1 trillion event logs processed through its big data and analytics engine each day, with hundreds of thousands of active attacks happening. The company also sees up to 1 million pieces of malware each day. A very busy active map on the wall shows where the threats are coming from and heading at any moment. To monitor and respond to the threats, Symantec looks at its extensive intelligence, visibility and context to aggregate and triage incidents that need response.

CyberWar Games
For the past four years, Symantec has held what it calls "CyberWar Games" program, where it builds physical environments that emulate real-life critical businesses and invite all of its 20,000 employees (technical and not) to attack it. This year's environment was a hospital and previous years have included simulated business environments from the oil and gas industry, financial services and the public sector. In attacking the environment, the employees learn hacker tactics and discover new zero-day threats.
Kill Wall
The one area where CRN was not allowed to view is what Symantec calls its "Kill Wall." Behind the wall pictured, the Kill Wall highlights the names of companies at which Symantec was able to kill the attack and identify the attacker. While upward of 90 percent have not been publicized, they are all on the scale of the megabreaches that have hit the news in recent months and years, including Sony, Target, Home Depot and more. All Symantec offices have a Kill Wall in them and it is seen as a point of pride for employees. This particular SOC has around 30 companies on its wall.

Attack Geographies
An attacker users Command and Control (C2) servers as a home base for deployed malware to drop information gathered. At the SOC, Symantec broke down which geographies were seeing the most attacks generated, led by the U.S. and the Netherlands. The reason for the Netherlands landing so high up on the list is that it is the home for an ISP backbone that allows for a significant amount of anonymous traffic through proxies favored by hackers.

STAR Team
Housed on a different floor of the SOC is Symantec's STAR division, which stands for Security Technology And Response. This division is an added layer of security intelligence that mines Symantec systems across the Internet for malicious activity. In particular, the division handles Security Response, where it takes identified malicious activity and pushes updates out to clients to protect them against the issue.