Q&A: Why Non-Security Vendors Think They Can Win The Security Platform Push

Jumping In The Ring
Many security vendors are looking to dominate the market with a platform-based approach. However, they aren't the only ones. Vendors outside the security space are also looking to jump on the security platform train, teaming up with security vendors to bring an integrated security approach to the enterprise. One recent example of that is a partnership between SAP National Security Services (SAP NS2) and CounterTack, under which the endpoint security company received an investment from NS2 and the two companies plan to integrate their technologies. The result is a growing security platform, centering on the SAP HANA technology. In an interview with CRN, SAP NS2 President Mark Testoni and CounterTack's vice president of marketing, Thomas Bain, talk about why the security platform of the future might not come from a security vendor after all.

You don't seem to think the security platform of the future has to come from a security company. Can you explain that?
Bain: We've seen a shift from where we were as recently as two years ago to where we are now. The platform approach to cyber right now is really interesting. You're starting to see it across the board a little bit more. But for us, what it means is we want to deliver not just endpoint security capabilities but more cybersecurity capabilities under one agent. We have this platform that customers can build on that fits into the current customer environment and maps to our users' workflow … For us, it's all about extensibility of capabilities, of breadth, of depth, and then being able to bring them in … We [already] have that footprint, and you can leverage the data that you're pulling on the behavioral side and on the in-memory side from our sensor for added capabilities. For us, it's really all about just delivering more capability to the customer, listening to them, and the alignment with SAP NS2 along the lines of HANA will really allow us to do that and to accelerate.

There's a lot of talk in security right now of companies trying to be the "security platform." Do you see yourselves as key to that?
Testoni: We think we have a racehorse that a lot of this can ride on. Obviously, there are others in this business that are playing for and trying to do this, but we think we have that kind of capacity on the backend. We're trying to enable these smaller, rising-up companies as part of that, so we will be there as part of the broader footprint in that landscape.

How does this security platform bring together disparate security technologies?
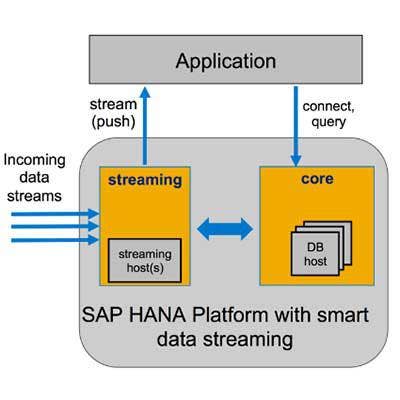
Testoni: The common denominator here is data. We have data and we're evolving these capabilities, from graph point analysis, machine learning, the portfolio of algorithms in those areas is rising dramatically. Since the common denominator is data, we view ourselves potentially as that data platform for companies, like CounterTack, to expand their footprint of delivery. Ultimately, all this is about data coming from various place and how quickly that data can be converted into information and action.
Bain: If the data is not actionable for the customer, it is not meaningful … More importantly, for our customers, it means they can do more, they can detect more, and most importantly they can respond to more threats.

How does SAP pair with security vendors? Talk about your investments with SAP NS2.
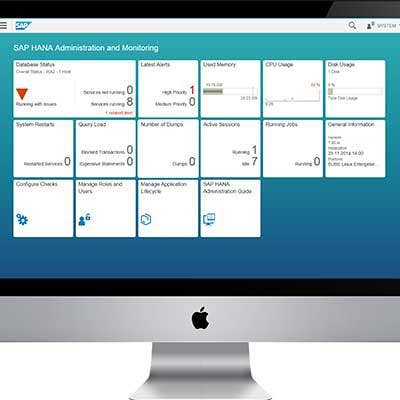
Testoni: We're looking to expand our technology capabilities, specifically our platform HANA, which is a real-time in-memory accelerator platform. We're looking for use cases that have a lot of applicability. That's where we focus a lot of investment activity: How do we find companies that have capabilities and use cases that make sense that can leverage our capability and create channels for us to sell more of our capability where it makes sense? We have invested in about half a dozen different companies now – some of them are publicly out there. We're very excited about the relationship here with CounterTack because the business they're in – endpoint management and cybersecurity – is such a big data problem. We feel like it's a perfect marriage and they have a perfect need because their business is expanding and the kinds of customers, the size of customers, and the data being created require the dynamics of a HANA and its capabilities. We've been engaged with them for quite a while. We're an investor in that latest round and on the other hand we've built a go-to-market relationship with them to where they will be reselling our capacity and capability and we will be supporting them.
How can HANA be applied to the endpoint security market?
Testoni: When you look at the cyber world overall, one of the biggest challenges we see is, first of all, users of all flavors are vulnerabilities, so endpoint management and those capabilities are really important. With IoT, we know they are only expanding in nature … We view CounterTack as a leader in this space and we see it as a natural pull-though to see the value of HANA in the management of solutions in cyber because of its ability to help manipulate, manage, and create analytics off of the data. That is critical for these types of solutions. We see the pull-through … This is also a focus we have had to find other channels. To grow our business, this is an important channel because of the demand in this particular segment of cyber.
How are analytics capabilities different coming from HANA, versus from the security solution itself?
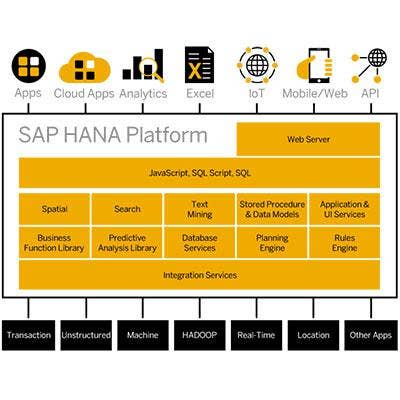
Testoni: Analytics is tossed around. The capacity and speed of HANA's database in real-time … that's obviously next-generation on the analytics side. Then, you couple that with the development of really three or four key cartridges that fit in there and really drive it to the next generation of analytics: machine learning, AI, graph-link analysis, the ability to link people, places, things, and activities that may not be apparent to the human mind, geospatial. These are all cartridges that come inherent in HANA and why we're excited about this, not only in the cyber realm but in places like law enforcement and intelligence, where there is a need to relate things. What HANA has done and what real-time database has done is made it easier to develop the old data warehouse much more rapidly … It's ultimately about velocity and volume and validating the data. What's changing is if you start looking at this, are we going to be able to more rapidly identify threats as they enter the space? Or can we predict activity that might be threats? These are the things that are coming in the future.

Talk about your investments in security companies; why are you investing and partnering rather than building security capabilities?
Testoni: What is driving [our investments in cybersecurity] is we think we are trying to become one of the key players in the management of the data underneath cyber solutions … It seems like all problems these days are just digitized big data problems. It's not from a lack of the data, it's a question of how quickly we can analyze it. That's why we focus, among other places, on this space with our investments. We can't build out all these capabilities ourselves -- nor do we want to – but we want to enable others to take their good ideas and make them faster and better and potentially be an integrated data platform on the backend for a lot of this stuff.
What does the SAP HANA platform add to the security vendor side?
Bain: For us, it's much more about growth and continuing down that path of innovation, rather than trying to go out and just do all kinds of things and advertise in every airport. We've been laser focused on solving customer problems, specifically from the standpoint of really bad threats … For us, we have always taken a different approach with the foundation being behaviorally based. We're looking at state changes within endpoint systems and really broad, scalable environments. That's really where we cut our teeth when we first came to market with our Sentinel product. We've shifted as of last RSA to the Endpoint Threat Platform and added more robust capabilities to it … With the new funding, we want to grow, we want to continue to expand, we want more partnerships like our SAP NS2 partnership, and it's all about growth, hiring, customer acquisition and being a good partner to our partners. The other side to this, too, is that we are really excited to be working with SAP NS2 because it opens up a massive ecosystem of both customers and technology breadth that we have not had previously. Those are the two key factors that go into this partnership that we're excited about.

What's the benefit to partners of a partnership like this?
Bain: What's really interesting about the SAP relationship and the SAP HANA platform is there are a lot of technologies in there that really align with technologies we've built into our Endpoint Threat Platform, stuff like machine learning, natural language processing, a lot of graphing … I think the net is that there are technologies together that we plug into our platform that already exist and are far advanced. There are other database technologies and big data technologies that align very well. I think that, from an integration standpoint, we're really excited about what the possibilities are for getting into the enterprise. If you look at any new technology that an enterprise customer is going to bring in, there is always going to be a little bit of an element of friction. We are totally focused on not just removing friction, but with the technology alignment that we are looking at a customer, saying "We can do this, we know what your goals are, and we can take this to a new level and let the best-of-breed technologies together take hold." I think that's what really excites us.

What are the opportunities to continue building on this platform?
Bain: It comes down to: What technologies do I have in place? How am I leveraging them? How are they integrated? How am I correlating that information so it is actionable across all these use cases? ... For us too, the partnership here is really a force multiplier for adding more use cases down the road. There are use cases that I guarantee we haven't even thought of yet.
Testoni: I would only add to that is looking in the future to unify data sets on a platform to be leveraged by a variety of capabilities. Then, there's also the possibility of open source. Today, the cyber world is often about who is attacking us? Where are the threats coming from? But, in the future can we start to look out into the open source and see activities that might drive to the next layer or the next set of threats? ... Unifying these capabilities on a platform like ours offers more potential to do those kinds of things … It offers a lot going downstream in the future for companies like CounterTack and others.