FBI Cybersecurity Security Expert Abagnale On The Real Cause Of Blockbuster Security Breaches And The Breakthrough Technology That Could Eliminate Passwords
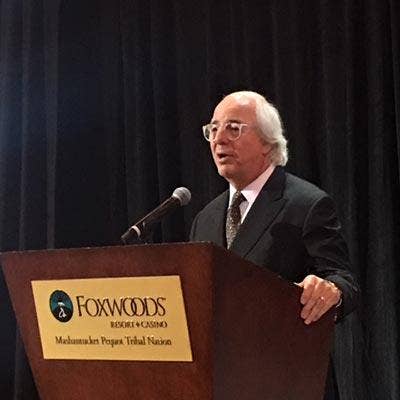
Abagnale Is Determined To Eliminate Passwords
Frank Abagnale, an FBI cybersecurity specialist and identity fraud expert, says passwords are an antiquated technology that should be shelved once and for all in favor of proven new identity authentication technology.
"I have said for years we have got to do away with passwords," said Abagnale, who singles out passwords as a weak link opening the door to identity fraud. "Passwords are the evil cause of all the problems we have. On top of that passwords are stagnant. They are a 1970 technology that is long past due."
Abagnale is an advisor and passionate advocate for technology developed by Trusona that eliminates the need for passwords with a secure authentication platform that was first developed for the CIA.
Trusona, in fact, was originally developed as a "very high-level security technology for (CIA) agents out in the field to send data back to the field office," said Abagnale. "The field office needed to know 100 percent that the person on the other end of the device was in fact their agent."

What are you are doing now?
I have been a consultant at the FBI for 41 years. I am still there. That is basically what I do. On the side I do some consulting work for private companies -- mainly in technology development. It has just been amazing over the last 40 years watching how crime has changed and how much easier it is to commit, and how much less risk there is of being caught and prosecuted.

What kind of experience have you add at the FBI with cyber-security breaches?
I have been an advisor on all the breaches back to the TJ Maxx breach 15 years ago including Home Depot, Target, Sony, Equifax. The one thing I have learned about breaches is every breach is the same. Every breach occurs because somebody in that company did something they weren't supposed to do or somebody in that company failed to do something that they were supposed to do. Hackers do not cause breaches. People do. All hackers do is look for a weak point.

What are some specific cases of those weak points?
I make my home in South Carolina. Three years ago someone hacked in and stole 3.8 million tax returns of the citizens of South Carolina. When the state revenue tax office was asked about it they said they did nothing wrong. I said to them: 'That would literally be impossible.'
After a couple of month investigation, it turned out an employee took a laptop home they shouldn’t have taken home, used it in an unrestricted area and of course a hacker got in and stole the tax returns. Our governor at the time, Nikki Haley -- who is now the ambassador to the UN- ordered every citizen of the State be provided one year of credit monitoring and the state would pick up the fee.
I didn't know the governor, but I sent her an email and told her that would be a waste of time and the taxpayer's money. People who steal mass data, warehouse that data for three to five years before they ever bring it to the surface.
First of all you already told the hacker that there is a year of credit monitoring so they are not going to do anything for a year. They simply wait two or three years and then they start using that information.

What has been the most egregious breach?
The worst breach in the last 15 years and this is going back to TJ Maxx -- one of the first breaches -- has to be Equifax. This was the credit bureau with your name, social security number and date of birth.
This is your name, social security number, date of birth. If I can become you it is only limited to my imagination what I can do as you.
What do you make of the Equifax breach?
This Equifax breach of 145 million -- which I believe is a lot more than that -- probably about 250 million -- because companies always come in with a low number first and eventually you find out it is a lot higher than that.
Those pieces of information from Equifax won't show up for two or three years. The difference is this: if I breach Home Depot or Target I am there to take credit card numbers and debit card information I have to get rid of that right away. That has an extremely short shelf life. But if I steal your name, social security number or date of birth, you can't change those. So the longer I hold it the more valuable it becomes when I go to use it.

What was the cause of the Equifax breach?
The breach was caused because Equifax didn't do what they were supposed to do. They didn't update their technology. They didn't fix their patches. Their sloppiness caused a hacker to access the data. So they were negligent.
Then they turn around and come out and say -- 'How do we make money off something that was real negative?' Well we will offer everyone in the world free credit monitoring service for one year. Consumers are petrified now because all their information has been stolen. So they are going to sign up for free credit monitoring which millions and millions of people did. Then a year from now Equifax will say -- Well none of that information has surfaced yet so we recommend you sign up for the service. So it is going to become a money generating thing. I thought that it was pretty unethical on their part.

What is the lesson from the Equifax breach?
Here is a breach that should have never occurred. Had the company been doing what they were supposed to do -- keeping their infrastructure safe -- this would not have happened.
If Microsoft tells you to put a patch on your computer or you will get malware, you shut your computer down and upgrade it and load the patch. It is simple stuff. For a company that big handling that much sensitive information not to be keeping their technology up to date is absurd.

What did you think of the Equifax response to the breach?
It is a real shame because the American consumer said 'Look I never gave you permission to have my information.' I didn't sign a piece of paper that said Equifax can store my name and date of birth. There were 10.9 million driver's licenses stolen from the Equifax breach.
That has your description, your home address, your date of birth. Those are gone. You want to at least say to those people -- you can freeze your credit or get credit monitoring the next three or four years for free. They never authorized that. Why should they be paying a fee for a mistake Equifax made? Even if you decide to freeze your credit in most states there is a fee charged by the credit bureau to freeze your credit. Then Equifax is saying if you want to freeze your credit we are going to have to charge you a fee. If you unfreeze it, there is a fee and then if you refreeze it again there is a fee. There should be no fee because it was not their fault that this occurred.

What was your personal experience with the Equifax breach?
My exposure is always as a consultant to the bureau. I have been teaching at the FBI Academy for 40 years. I simply work as an analyst. If they have a case like that they bring it in and say -- 'what do you think happened here? What do you think was going on here?'
Were you an analyst on the Equifax case?
Yes. I thought it was an open and shut case. Obviously they didn't update their infrastructure. They didn't fix their patches. So they allowed a hacker access into their account. Actually the hacker was there for a couple of months. But the hacker was determining what do I want? What do I really want to steal? What is the most beneficial to me? Even in those two or three months that the hacker was in those systems they should have caught that. But they didn't. Again it was their negligence that caused that breach to occur. Now you have a lot of people who have had their identities stolen.

Are the number of breaches increasing or decreasing?
Last year worldwide in 2016 we had 1,206 breaches amounting to 1.7 billion identities being stolen. We had to change that because as you know a few weeks ago the SEC, our Securities and Exchange Commission, admitted they had a breach in 2016 they didn't report. So we changed the number by one. Within a week following that Deloitte said they had a breach in 2016. So we had to change it again.
Fraud in the United States annually is over $900 billion a year and most of that obviously comes from the internet because most fraud now is done online.
How many breaches are not ever reported to the government or the FBI?
There are thousands and thousands of breaches that are not reported. Most companies don't want to report them. They try to hide them under the rug. They are only forced to report them when they are so big they have no alternative but to report them. Then they try to minimize it as much as they can.

What is the takeaway for companies with regard to all these breaches?
If I entrust you with my information, no matter who you are, whether you are an insurance company or a bank, if I entrust you with my personal information it is up to you to keep it safe. If you don't keep it safe and I get harmed because of your negligence -- something you do that causes it to happen -- then there should be recourse. I should have the right to sue you and recover damages. So companies need to be aware there is a risk by not taking care of this data. But a lot of companies don't put a lot of emphasis on this.
We have great technology out there but if you don't take advantage of it it is worthless. You can have all the technology in the world, but if companies fail to implement it because they don't want to spend the money or think -- 'This can't happen to me. I am a smaller business.' Look if you are holding information that belongs to other people and you are responsible for keeping their data you need to be doing everything you can possibly do to keep that information safe.
Why do the numbers always seem to rise on the number of people impacted by breaches?
Every breach is going to come in with the lowest possible number and then as time goes by slowly that number gets bigger and bigger and bigger. I never believe the first number as being the accurate number of how many people were affected.
You always find out about these later. When we had the office of personnel management breach the government said there were four million government employees and contractors with their information stolen. In the end, it was 22.1 million government employees. And they first said 1.1 million fingerprints (stolen) it turned out to be 5.6 million.

What is the difference between the digital banking landscape of today versus when you were forging checks?
What amazes me the most is that what I did 50 years ago is 4,000 times easier today than when I did it. That is because of technology.
Technology breeds crime. It always has and it always will. So there will always be people willing to use technology in a negative, self-serving way. To give you an example, 50 years ago for me to forge a check I had to spend eight months learning how to operate a Heidelberg printing press. That press 50 years ago cost $1 million. It was 90 feet long, 18 feet high and it required three journey man operators to operate it. I had to eliminate the other two operators. So I had to operate it by myself.
(Catch Me If You Can Director) Steven Spielberg showed that very well in the movie. He found a press just like the one I used. He realized from the story I had written that I had used scaffolding to bring myself up to the top of the press on both sides. Because I was a teenage boy I could run the length of that press and operate it by myself. But there were color separations. There were negatives. There was type setting. There were chemicals to make plates.

How easy it would be to forge checks today versus 50 years ago?
Today you basically go to a hotel room, open your laptop and look out the window. And if you see an ad for Delta Airlines you sit down at your laptop and bring up a diagram of a check with a security background in it blank. Then you go to Delta's website, capture their corporate logo in color, put it up in the left hand corner of the check with their corporate address, maybe put a Delta Jet in the background in color and screen it into the background of the check. Then you do a step and repeat putting Delta, Delta, Delta across the check. And in 15 minutes you have created a beautiful four color check. All you have to do is go down to the office supply store and buy check paper that has water marked security features and then print it out on an ink jet printer.

What are some of the other difference between the security landscape of today versus 50 years ago?
The other difference is we live in a world of way too much information. Back 50 years ago, you may have walked up to the press and said to me -- 'Frank -- are those your Pan Am checks you are printing? They are unbelievable. They are detailed. They are color. They are really sophisticated. But let me ask you this- how do you know where Pan Am banks?' My response would have been- 'I have no idea. I am just making up a bank's name.' Well how do you know what the account number is? 'I have no idea I am just making up a bunch of numbers? How do you know who is the authorized signer of the company?' I don't know that I am just making up a name.' Today all of that is just a phone call away.

So how would it work today if you were trying to get that information?
So if I were to call an airline right now and ask to speak to someone in accounts receivable and told them I'd like to pay an invoice and needed their wiring instructions they would tell me what street and in what city that bank is, the routing number, the account number, everything I need to make up the check.
I would go to the Bank's website, capture their corporate logo, put it down on the check and then I would call back and ask to speak to someone in corporate communications and when they came on I would ask- Would you be so kind to mail me a copy of your annual report. And then on page three there is a signature of the CEO, the CFO, the Treasurer, the Controller and then I would scan it on white glossy paper, black ink, camera ready art and put it on the check. The whole check thing has become a lot easier because of technology and that is why there is so much more of it (check fraud) today than when I was doing it.

What would be your medium of choice if you were committing fraud today?
It would certainly be the internet with the ability to steal from thousands of miles away. I would be doing the opposite of what criminals are doing in different countries. I would be in this country defrauding people in other countries where I don't have to worry about being apprehended and prosecuted. What we have today is the majority of crimes on the internet actually come from people in Russia, China, India. Even though we know who is doing it, we have the address where they are doing it, we don't have the ability to go arrest them, press charges against them and bring them back here.

How vulnerable is the federal government with regard to computer security?
To be honest with you the federal government is the worst. Medicaire and Medicaid lost $100 billion last year that was paid out in fraudulent claims. That is 10 percent of their combined budget in one year in fraud. We had the IRS pay out $5.8 billion in tax refunds to people who filed a return using somebody else's identity. Simple data analytics software would have caught most of that but the government doesn't use it. We had unemployment fraud of $7.7 billion.
Because the government has no board of directors and no interest in profit they basically don't do a lot to protect the infrastructure of our country or the 2,000 agencies that are involved in running our country. Consequently what has happened in the last couple of years is criminals have started to say- "Wait a minute who has all the money? The government. Who would be the easiest to defraud? The government.' So the government has become a huge target of criminals. It is the same for state, county and city government as well.
A major bank couldn't afford to lose $100 billion they would go broke, they would be out of business tomorrow. So they invest billions of dollars in technology to keep criminals out of their banks and they are constantly updating and doing a good job of trying to build a fence between them and the person trying to rip them off. But the government is not doing that. The government is the easier target. So the criminals go to the government.

What is the solution to the government security problem?
The government needs to wake up and start acting like a private business or private corporation spending the time and money to put in the technology to keep the criminals out. It's not that big a deal to do.
What kind of security work you have done as an advisor to the federal government?
I have had the opportunity to work during my career as an advisor always on behalf of the government. Back 20 years ago if the government was going to print a passport I worked as an advisor on putting the security features in the passport. If the Bureau of Engraving was going to do a change in the currency like back in 1996 I was involved as an advisor always looking at it as how would I defeat it and this is what you should do. I worked on a technology called the 41st parameter. It became a commercial product and Experian now has it.
How do you view passwords in the current security landscape?
I have said for years we have got to do away with passwords. Passwords are the evil cause of all the problems we have. On top of that passwords are stagnant. They are a 1970 technology that is long past due. Everyone in the world wants passwords to go away.
I'd like you to look at a technology called Trusona at Trusona.com. That is the world's first technology that totally eliminates the need for passwords. It is just an amazing technology.
When you go to the website there are all these videos that demo how it works. It is now being adopted by governments, financial institutions, corporations, and banks all over the world. I think within the next few years passwords will be gone.

What kind of guarantee is there for Trusona technology?
It is the only technology in the world insured by an A plus insurance company. If I bank with Goldman Sachs and I use Trusona on my phone to wire money it is automatically insured.
No insurance company has ever insured a verification system. Their insurance company for over two years took this to 25 labs around the world to try to have them defeat the technology and they weren't able to do that.
Banks that have adopted it have tested it for over 18 months internally to make sure there was no way for someone to get around it or defeat it. It has been tested and you are going to see it a lot more now as Microsoft pushes this out.

How was Trusona developed as a product?
Trusona -- which is funded by Microsoft and others- was originally developed as a very high level security technology for agents out in the field to send data back to the field office. The field office needed to know 100 percent that the person on the other end of the device was in fact their agent. That was level four security.
I got involved as an advisor because it was a government project. The CEO (Ori Eisen) -- the most brilliant man I ever met- also wants to do away with passwords.
The largest bank in Chile was having ATM fraud with about 31 percent of all transactions annually fraudulent. They were losing millions of dollars. Ori developed a technology that was a little box that went into the ATM machine. So when you used your ATM card, you would scan it, it would read the magnetic strip on the back but only the dots that make up the strip. There are no two magnetic strips that are the exactly alike in the world. Once it was scanned they were able to know that was your card. That brought the fraud down to less than one percent. He used that same concept for Trusona with level four security.

How can Trusona be used in current consumer environment?
If I pull up to a bank ATM machine all I have to do is take out my phone, press my thumb on the button and hold my phone up to the screen, up pops on the screen a QCR code, it is encrypted, it will only be there for 28 seconds and it will never repeat. When it pops up you point your phone at it, it recognizes you and you are in. That is all you do. There is no card and there is no password.
If you are in a hotel room and wanted to watch Netflix with your Netflix account, you would just pick up your phone, put your thumb down, hold it up to the screen and a QCR code would pop up and it would know it is you.
There no biometrics. Biometrics you can replay. I can send my finger prints and eye scan over the line but someone can capture it and replay the same thing back. There is no replay with Trusona.

What is the cost of Trusona for consumers?
For the consumer this is free. So if Netflix uses it you download the app. It takes 45 seconds to download the app. If a bank was going to use it for example they would integrate it into their account app. So it is really more of a business to business product, but for the consumer it is free.
With Trusona there are three levels. If you just want to get into Netflix, you just use your phone. If you needed to wire $1 million out of your bank account to another account then it would ask you for a second form of identification -- whatever you originally registered with them -- your driver's license or your Saks Fifth Avenue card and you would put a token in the bottom of your card and then you swipe the card.
It reads that from the original swipe when you registered the card. Even if someone knew everything you did they couldn't repeat it. They couldn't match the way you swipe. Trusona records movement and identifies who you are ahead of time.

How big a financial impact could Trusona have in the market?
If you take one of the top five banks in the United States they spend a minimum $6 million a month in their call centers resetting passwords. They are spending about $100 million a year resetting passwords.
They are the first ones in the world saying they need to get rid of passwords. They would save $100 million a year if there was no passwords.