The 10 Hottest Cybersecurity Products Of 2018 (So Far)
Securing The Future
Vendors spent 2018 advancing protection everywhere from the cloud and web to email and endpoint, debuting consoles that help centralized management and leveraging artificial intelligence and machine learning to automate processes and provide protection that's more customized to a particular user.
Enhancements to managing users and identities also were a major area of focus in the year, with advancements around continuous risk assessment as well as helping businesses identify instances where a password might not be necessary for logging in.
Seven of the top 10 cybersecurity products of 2018 came from companies based in the Bay Area, one came from a vendor based in Texas, and the remaining two stemmed from suppliers based abroad. Read on to learn how suppliers have gone about making their cybersecurity portfolio even more relevant to the channel.
(For more on the biggest news of 2018, check out "CRN's Tech Midyear In Review.").

Check Point CloudGuard
Check Point Software Technologies unveiled in February a family of cloud security products to address an increase in account hijacking and multivector attacks on cloud workloads and applications.
The San Carlos, Calif.-based platform security vendor said CloudGuard can protect enterprises against cyberattacks on cloud infrastructure workloads, as well as SaaS applications. CloudGuard integrates with IaaS cloud platforms and cloud-based SaaS providers to protect any cloud, service or application against sophisticated breaches, malware and zero-day attacks.
CloudGuard supports single-click SaaS deployment to help enterprises remain nimble and agile. In addition, dynamic policy updates and auto-provisioning allow for rapid scaling of IaaS cloud security that's in line with modern business requirements.
CrowdStrike Falcon X
CrowdStrike Falcon X was introduced in April to automate threat analysis and help deliver customized intelligence and Security Operations Center automation to large and small organizations.
The Sunnyvale, Calif.-based endpoint security vendor said Falcon X combines malware sandboxing, malware search and threat intelligence into an integrated offering that can perform comprehensive threat analysis in seconds instead of hours or days. The offering produces indicators of compromise for the threat that was actually encountered in the organization as well as all of its known variants.
Falcon X immediately shares indicators of compromise with other security tools like firewalls, gateways and security orchestration tools via APIs. The product also provides integrated threat intelligence alongside its security alerts to accelerate incident research, streamline the investigative process, and drive better security responses.

Forcepoint Dynamic Data Protection
Forcepoint Dynamic Data Protection was unveiled in April to continuously assess risk and automatically provide proportional enforcement that can be dialed up or down. This capability is enabled through human-centric behavior analytics that understand interactions with data across users, machines and accounts.
The Austin, Texas-based platform security vendor said the product applies an anonymous and continuously updated behavioral risk score to establish a baseline of ’normal’ behavior for each end user on a corporate or unmanaged network. Forcepoint's intelligent systems, informed by the individual risk assessment, then apply a range of security countermeasures to address the identified risk.
With the industry’s first automated enforcement capability that dynamically adapts, Forcepoint Dynamic Data Protection frees up security analysts to focus on higher-value activities.
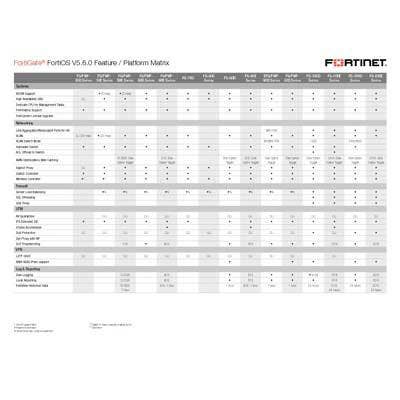
Fortinet FortiOS 6.0
Fortinet in February packed more than 200 new features and capabilities into FortiOS 6.0, the third generation of the Sunnyvale, Calif.-based company's security fabric. FortiOS 6.0 offers centralized management across the entire portfolio from a management analytics and SIEM perspective.
Fortinet's SD-WAN toolset looks at applications more than packets, leveraging path-aware intelligence to ensure customers are getting appropriate service to their most important applications. FortiOS 6.0 also expands the cloud connectors to include visibility into private clouds such as Cisco ACI and VMware NSX, public clouds such as Amazon Web Services and Microsoft Azure, and SaaS clouds such as Salesforce.com and Office 365.
Fortinet also introduced tagging in its FortiOS 6.0 release, enabling objects, interfaces, firewalls and devices to be marked using a color-coded system. From there, Fortinet would like users to be able to apply a broad policy to ensure unsecured mobile devices never have access to intellectual property.

Netskope For Web
Netskope in March introduced a web security tool that makes it possible for organizations to manage and protect SaaS, IaaS and web from a single platform.
The Los Altos, Calif.-based cloud security vendor said most legacy web security tools on the market today are application-focused and were built before the cloud was prevalent. As a result, they aren't focused on solving the challenges cloud brings to the table, such as detecting instances of Amazon Web Service in the enterprise or addressing data stored in AWS and Salesforce.
Unlike the existing heavy, appliance-focused web security tools, Netskope's web security offering is lightweight, cloud-compatible, and can decrypt at scale. Netskope's ability to handle both cloud and web security means that enterprises can make granular decisions in a single, cohesive policy framework without having to grapple with multiple interfaces.

Okta ThreatInsight
Okta in May leveraged device, IP and geolocation information to help businesses identify instances where a password might not be necessary for logging in.
The San Francisco-based identity management vendor said its algorithms learn people's behavior over time and can allow users to login without a password if they're in a familiar setting. But if the same employee attempts to log in from an unfamiliar setting, Okta will provide a security question and a second factor before granting access.
This ability is powered by Okta ThreatInsight, a new tool that looks at an IP address' reputation as well as where the request for access is coming from to determine whether it's malicious or safe, While other vendors also offer a password-less experience, they typically don't provide threat checks on the level of ThreatInsight.

SonicWall Capture Cloud Platform
The SonicWall Capture Cloud Platform debuted in April, tightly integrating security, management, analytics and real-time threat intelligence across the Milpitas, Calif-based company’s portfolio of network, email, mobile and cloud security products.
Machine-learning algorithms are used to analyze data and classify and block known malware before it can infect the network. Unknown files are sent to the SonicWall Capture Cloud Platform, where they are analyzed using hypervisor analysis, emulation and virtualization technology, blocking zero-day malware in near-real-time.
One of the cornerstones of the platform is the SonicWall Capture Security Center, which allows for the governing of SonicWall's security operations and services from a single pane of glass.

Sophos Intercept X
Sophos in January rolled out the latest version of its Intercept X anti-exploit application, incorporating deep-learning technology to boost malware detection rates.
The Oxfordshire, England-based platform security vendor said the new version of Intercept X would be the only product in the world to combine machine learning, malware and exploit blocking, and ransomware protections into a single offering. The new deep-learning capabilities come courtesy of Sophos's February 2017 acquisition of Invincea.
The addition of deep learning will make it possible for Intercept X to curate and label data even more accurately since it's now able to process hundreds of millions of samples rather than just tens of millions of samples. As a result, Intercept X will be able to make more accurate predictions at a faster rate with fewer false-positives as compared with traditional machine learning.

Symantec Targeted Attack Analytics
Symantec for the first time granted customers access to the threat detection technology used by its internal research team, making it easier to discover targeted attacks.
The Mountain View, Calif.-based platform security vendor said in April that Targeted Attack Analytics can look at all the machines in a single enterprise and collate the telemetry with the endpoints to verify if there's an active attack taking place inside the network. The company said the technology can detect more advanced attacks that get by traditional security offerings.
In addition to looking holistically across all devices to build a more concrete picture of what's going on, Symantec said Targeted Attack Analytics can alert users to incidents with absolute certainty, rather than simply indicating that there's the likelihood or a probability that something's taking place.
Trend Micro Writing Style DNA
Trend Micro Writing Style DNA was unveiled in April to sound the alarm when emails are suspected of impersonating an executive or other high-profile user as part of a Business Email Compromise (BEC) attack.
The Tokyo-based security vendor said its product uses artificial intelligence to "blueprint’ a user’s style of writing, employing more than 7,000 writing characteristics. When an email is suspected of impersonating a high-profile user, the style is compared to this trained AI model and a warning is sent to the implied sender, the recipient and the IT department.
Writing Style DNA provides authorship analysis to spot attackers who hijack legitimate domains and accounts to circumvent traditional filters. Executives can provide feedback on the flagged emails to improve detection and reduce false positives.