The 10 Biggest Cyber And Ransomware Attacks Of 2021
Technology, food production and critical infrastructure firms were hit with nearly $320 million of ransom demands in 2021, and reportedly paid the ransom in four of the year’s 10 largest cyber and ransomware attacks.

Fighting Back
The U.S. government has become more proactive in attempting to curtail ransomware, launching a program in July that offered rewards of up to $10 million for information on state-sponsored hackers participating in malicious activities against critical infrastructure. The U.S. government also launched a central hub that consolidates ransomware resources from all federal agencies, according to Emsisoft.
Still, 2021 saw a ransomware group issue the largest publicly known ransom demand to date following a monumental ransomware attack that impacted as many as 1,500 businesses. The groups behind two of the year’s most prolific ransomware attacks lied low or disappeared when the U.S. government was hot on their coattails, but resurfaced a few months later, operating in one case under a different name.
Victims of the 10 biggest cyber and ransomware attacks of 2021 were hit with ransom demands totaling nearly $320 million, and reportedly paid the ransom in at least four cases. Four of the largest ransomware victims are in the technology space, while the remaining span verticals from financial services, healthcare, and automobile manufacturing to food production, oil and gas, and chemical.
Four of the biggest ransomware attacks were carried out by REvil, two were executed by Darkside, while Conti, DoppelPaymer, LockBit, and Phoenix were responsible for one massive attack each. Three of the victims are based in the United States, two are in Ireland, two are in Taiwan, with one victim in Brazil, Germany, and South Korea, respectively. Here’s how the top ransomware attacks of 2021 played out.
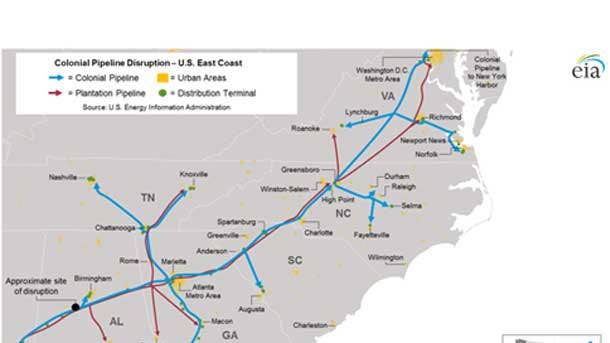
T-9. Colonial Pipeline
Ransom Paid: $4.4 Million
A May ransomware attack prompted Colonial Pipeline to shut down its 5,500-mile natural gas pipeline for five days, resulting in more than 10,000 gas stations across the Southeastern U.S. being out of fuel. Colonial Pipeline paid the Darkside ransomware group $4.4 million on May 8 with the hope of restoring operations on its pipeline sooner, although federal officials were able to seize back most of the ransom.
Colonial Pipeline paid the ransom in untraceable cryptocurrency within hours of the initial attack in exchange for a decrypting tool that could be used to restore its computer network. However, Darkside’s decryption tool was so slow that Colonial continued using its own backups to help restore the system, a source familiar with the company’s efforts told Bloomberg.
Law enforcement officials in June said they were able to track multiple transfers of Colonial’s ransom payment by reviewing the Bitcoin public ledger and identified $2.3 million of proceeds that had been transferred to a specific address. The Federal Bureau of Investigation was able to obtain the “private key”—the rough equivalent of a password—needed to seize assets from that specific Bitcoin address.

T-9. Brenntag
Ransom Paid: $4.4 Million
Chemical distributor Brenntag in May paid a $4.4 million ransom in Bitcoin to the Darkside ransomware gang to receive a decryptor for encrypted files and prevent the threat actors from publicly leaking stolen data. Brenntag suffered a ransomware attack that targeted their North America division, with the hackers encrypting devices on the network and stealing unencrypted files, BleepingComputer reported.
The Darkside ransomware group claimed to have stolen 150GB of Brenntag data during their attack. To prove their claims, the ransomware gang created a private data leak page containing a description of the types of data that were stolen and screenshots of some of the files. DarkSide initially demanded a $7.5 million ransom, but after negotiations cut the ransom to $4.4 million, BleepingComputer reported.
The DarkSide affiliate claims to have gotten access to Brenntag’s network after purchasing stolen credentials, BleepingComputer reported. However, the DarkSide affiliate does not know how the stolen credentials were originally obtained. Ransomware gangs and other threat actors commonly use dark web marketplace to purchase stolen credentials, especially those for remote desktop credentials.

8. JBS
Ransom Paid: $11 Million
JBS in June paid $11 million to the REvil ransomware operators who temporarily knocked out plants that process roughly one-fifth of the nation’s meat supply, the company’s chief executive said. The ransom payment, in bitcoin, was made to shield JBS meat plants from further disruption and to limit the potential impact on restaurants, grocery stores and farmers, according to The Wall Street Journal.
JBS learned of the attack when technology staff members noticed irregularities with the functioning of some servers. The company’s technology team began shutting down the meat supplier’s systems to slow the attack’s advance. JBS called in technology vendors that had previously worked with the company, as well as cybersecurity experts and consultants who began negotiating with the attackers.
JBS maintains secondary backups of all its data, which are encrypted, and the company brought back operations at its plants using those backup systems, The Wall Street Journal reported. While the company was making good progress, JBS’s technology experts cautioned the company that there was no guarantee that the hackers wouldn’t find another way to strike, according to The Wall Street Journal.

T-6. Kia Motors
Ransom Requested: $20 Million
Kia Motors America in February suffered a ransomware attack carried out by the DoppelPaymer gang, which demanded $20 million for a decryptor and not to leak stolen data. DoppelPaymer claimed that a "huge amount" of data was stolen, or exfiltrated, from Kia Motors America and that it would be released in two-to-three weeks if the company didn’t negotiate with the hackers, BleepingComputer reported.
Prior to the public ransom demand, Kia Motors America started experiencing a nationwide IT outage that affected their mobile UVO Link apps, phone services, payment systems, owner‘s portal, and internal sites used by dealerships. Similarly, Hyundai told Kia dealers that multiple systems were down including their internal dealer site, and services used by dealer technicians were affected as well.
Kia Motors America told BleepingComputer that they had seen no evidence that they have suffered a “ransomware” attack. Hyundai similarly said that they have no evidence of a ”ransomware” attack.

T-6. Ireland’s Health Service Executive (HSE)
Ransom Requested: $20 Million
Ireland’s health service, the HSE, said they are refusing to pay a $20 million ransom demand from the Conti ransomware gang after the hackers encrypted computers and disrupted the country’s health care. Ireland‘s publicly funded healthcare system shut down all of their IT systems in May after suffering a Conti ransomware attack, according to BleepingComputer.
The Conti gang claims to have stolen 700 GB of unencrypted files from the HSE like patient information and employee information, contracts, financial statements, payroll, and more. The IT outage led to widespread disruption in Ireland’s healthcare, causing limited access to diagnostics and medical records, transcription errors due to handwritten notes, and slow response times to healthcare visits.
“We‘re very clear we will not be paying any ransom or engaging in any of that sort of stuff,” Irish Prime Minister Micheál Martin said following Conti’s demand for $20 million.

5. CNA Financial
Ransom Paid: $40 Million
A March cyberattack that shut down systems at Chicago-based insurance giant CNA exposed the personal information of thousands of employees, contractors, and policyholders. More than 75,000 people were affected by the hack, which revealed names, personal identification, and Social Security numbers, according to a data breach notification filed with the Maine attorney general’s office in July.
The March attack caused a network disruption that affected certain systems, including corporate email, The Chicago Tribune reported. It also shut down the functionality of CNA’s website, reducing it to a static display. CNA told the Securities and Exchange Commission that its own insurance policies may not cover potential damages. The hack was carried out by the group Phoenix using Phoenix Locker malware.
The insurance giant paid the hackers $40 million in late March some two weeks after a trove of company data was stolen and CNA officials were locked out of their network, Bloomberg reported in May. The company initially ignored the hackers’ demands while pursuing options to recover their files without engaging with the criminals. But within a week, CNA decided to start negotiations with the hackers.

T-2: Quanta
Ransom Requested: $50 Million
REvil in April stole product blueprints from Apple supplier Quanta Computer and threatened to leak the files if Apple didn’t pay a ransom. The ransomware gang posted an extortion letter to Apple as well as some sample technical files on their dark web leak site, demanding that Apple pay by May 1 to prevent its stolen data from being leaked and noting that the ransom would double to $100 million on April 27.
By April 23, REvil had leaked more than a dozen schematics and diagrams of MacBook components on its dark web leak site, though there’s no indication that any of them were for new Apple products. In a negotiation chat on REvil’s payment site, REvil said that “drawings of all Apple devices and all personal data of employees and customers will be published” if Quanta didn’t begin negotiating a ransom.
Customers of Taiwan-based Quanta include Amazon, Apple, Cisco, Dell, Hewlett-Packard, Lenovo, and Microsoft, according to REvil’s ransom note. Quanta is the world’s second-largest original design manufacturer of laptops based on the number of ODM laptop units sold, behind only Compal, who was also targeted by ransomware in 2020.

T-2. Acer
Ransom Requested: $50 Million
REvil claimed in March that they had broken into and stolen unencrypted data from Taiwanese PC giant Acer. On their public leak site, the notorious ransomware group posted alleged images from Acer’s financial spreadsheets, bank balances, and bank communications. Acer wouldn’t comment on if it was hit by ransomware, the amount of ransom demanded, or if its Microsoft Exchange servers were struck.
In a conversation that started March 14, the attackers offered Acer a 20 percent discount if payment was made by March 17. In return, the REvil affiliate said they’d provide a decryptor, a vulnerability report, and the deletion of stolen files. But no payment was received, so the REvil affiliate behind the Acer attack demanded a $50 million ransom on March 19.
REvil also reportedly targeted a Microsoft Exchange server on Acer’s domain, according to Advanced Intelligence CEO Vitali Kremez. That represented an escalation in the massive campaign against Microsoft Exchange servers, which first came into the public eye March 3 when the Redmond, Wash.-based software giant disclosed four vulnerabilities in on-premises versions of Exchange.

T-2. Accenture
Ransom Requested: $50 Million
The Accenture ransomware attack was publicly revealed Aug. 11 and allegedly provided the LockBit ransomware group with sufficient data to breach some clients of Dublin, Ireland-based Accenture, No. 1 on the 2021 CRN Solution Provider 500. LockBit demanded a $50 million ransom payment to stop the leak of six terabytes of data they had allegedly stolen from Accenture.
VX-Underground, which claims to have the internet’s largest collection of malware source code, said that the LockBit ransomware group released 2,384 Accenture files for a brief time Aug. 11. In addition, Q6 Cyber found that the LockBit ransomware operators published more than 2,000 Accenture files to the Dark Web, including PowerPoint presentations, case studies, quotes, and so on.
Then in September, LockBit said they had taken advantage of credentials accessed during the Accenture attack to go after the consulting giant’s customers, compromising an airport that was using Accenture software and encrypting their systems. Accenture pushed back, telling CRN, “We have completed a thorough forensic review of documents on the attacked Accenture systems. This claim is false.”

1. Kaseya
Ransom Requested: $70 Million
The REvil gang in July pulled off one of the biggest ransomware heists, exploiting a flaw in Miami-based Kaseya’s on-premise VSA remote monitoring and management tool to compromise nearly 60 MSPs and encrypt the data and demand ransom payments from up to 1,500 of their end user customers. The hack allowed REvil to leverage VSA’s standard functionality and deploy ransomware to customer endpoints.
The attack left more than 36,000 MSPs without access to Kaseya‘s flagship VSA product for nearly 10 days as the company worked on a patch for the on-premises version of VSA and kept the more widely used SaaS version of VSA offline as a precautionary measure. REvil has made the largest ransom ask of all-time July 4, demanding $70 million to provide a universal decryptor to all victims of the cyberattack.
Nineteen days after the attack, Kaseya obtained the universal decryptor key without having to pay the ransom and set about helping compromised customers unlock ransomed files with the help of Emsisoft. In November, the Department of Justice arrested Ukrainian Yaroslav Vasinski for conducting the hack and charged Russian Yevginiy Polyanin with conspiracy to commit fraud in connection with the attack.