The 20 Coolest Cloud Security Vendors Of The 2021 Cloud 100
Here’s a look at 20 cloud security vendors that have developed tools and offerings to address the challenges associated with management, segmentation, compliance and governance in the cloud.

Adjusting To The New Normal
An increasing number of security breaches and cyberattacks coupled with a mandate to follow regulatory and data protection laws are expected to contribute to stratospheric growth in the cloud security space coming out of COVID-19. The widespread shift to work from home has driven rapid adoption of cloud solutions, creating the need for security measures that protect against cyberattacks.
Data stored in cloud servers is more vulnerable to cyberattacks than data stored in organization servers, and the decision by SMBs to shift data onto cloud servers has led to a larger attack surface for hackers. And governments around the world are investing in cloud computing delivery models and are working with the private sector to promote projects like smart city initiatives and smart transportation projects.
The global cloud security market is expected to achieve a compound annual growth rate (CAGR) of 14.7 percent over the next decade, going from $34.5 billion in 2020 to $68.5 billion in 2025, according to MarketsandMarkets. Asia-Pacific is expected to register the highest growth rate as SMBs in places like Australia, South Korea and Japan rapidly adopt cloud-based solutions to manage their enterprise data.
As part of CRN’s annual Cloud 100 list, here’s a look at 20 cloud security vendors that have taken on the management, segmentation, compliance and governance challenges in the space.

Aqua SecurityDror Davidoff
Co-Founder, CEO
Aqua Security in April debuted Dynamic Threat Analysis to defend container-based environments from sophisticated malware that can only be detected using dynamic analysis of a running container. Six months later, the company debuted new Kubernetes-native security capabilities to secure applications that run on Kubernetes across the development, deployment and runtime phases of the application life cycle.

Check Point Software Technologies
Gil Shwed
Founder, CEO
Check Point CloudGuard Connect has redefined SASE by making it easy to access corporate applications, SaaS and the internet for any user or branch, from any device, without compromising on security. The company’s June debut of CloudGuard Cloud Native Security unifies cloud security posture management, serverless and container protection, and threat intelligence to be managed in a single pane of glass.

CyberArkUdi Mokady
Founder, Chairman, CEO
CyberArk Privilege Cloud provides a simplified path to securely store, rotate and isolate credentials for both human and non-human users as well as monitor sessions and deliver scalable risk reduction to the business. And the CyberArk Alero SaaS offering combines into one zero trust access, biometric multi-factor authentication and just-in-time provisioning to provide visibility into remote vendor activities.

Forcepoint
Manny Rivelo
CEO
Forcepoint Cloud Security Gateway reduces the cost of owning software by bringing together secure web gateway, cloud access security broker and data loss protection capabilities into a single offering. Forcepoint Dynamic User Protection launched in September to empower security teams with real-time visibility into true risk behaviors of compromised and malicious users within hybrid cloud environments.
Fortinet
Ken Xie
Founder, Chairman, CEO
Fortinet last year upgraded its network processor for the first time since 2012 to provide the building block for hyperscale applications, delivering performance and fast connections across the board. The company stepped up its game around SASE by purchasing Opaq in July to strengthen distributed network protection from data centers and branch offices to remote users and Internet of Things devices.

GuardicorePavel Gurvich
President, CEO, Director
New Guardicore Centra Security Platform capabilities help security architects visualize, segment and protect cloud-native applications while reducing risk to mission-critical business applications through segmentation. The company’s Threat Intelligence Firewall hardens security profiles in complex cloud environments, identifying and blocking incoming and outgoing connections to known malicious IPs.

Imperva
Pam Murphy
CEO
Imperva Cloud Data Security was rolled out in July to give businesses visibility and compliance oversight for data hosted in a database-as-a-service (DBaaS), enabling compliance in minutes. The following month, the company’s Runtime Application Self-Protection (RASP) release was updated with architectural changes to secure dynamic cloud-native applications and ease deployment.

Lacework
Dan Hubbard
CEO
Lacework in August added active host vulnerability monitoring and CI/CD to allow DevOps and security teams to identify and prioritize active vulnerabilities in distributed systems at massive scale. The company in January closed a $525 million growth round to accelerate adoption among digital businesses that rely on Amazon Web Services, Microsoft Azure, Google Cloud Platform or Kubernetes.

McAfee
Peter Leav
President, CEO
McAfee’s Unified Cloud Edge means customers can define a single data protection or threat prevention policy and consistently apply the rules across the device, the network and the cloud. The company bolstered Unified Cloud Edge in October with first-of-its-kind integrated remote browser isolation technology, unified data loss prevention, and incident management across devices, networks, web and the cloud.

Mimecast
Peter Bauer
Co-Founder, CEO
Mimecast Browser Isolation protects users from credential harvesting or malicious downloads as the browsing session is executed and contained within the Mimecast cloud rather than on the user’s device. Mimecast Cloud Archive for Theta Lake arrived in September to streamline risk analysis and governance efforts to enable capture, retention, eDiscovery and risk detection across relevant productivity apps.

NetskopeSanjay Beri
Founder, CEO
Netskope in September unveiled the Cloud Threat Exchange to facilitate the ingestion, curation and real-time sharing of cloud threat intelligence across enterprise security enforcement points. The company hauled in $340 million last year from new investor Sequoia Capital Global Equities in a Series G funding round to address global demand and cement its leadership position in cloud-delivered security.

Palo Alto Networks
Nikesh Arora
Chairman, CEO
Palo Alto Networks agreed in March to buy SD-WAN player CloudGenix for $420 million to accelerate the on-boarding of remote branches and retail stores onto the company’s Prisma Access SASE platform. Eight months later, the company agreed to purchase attack surface management vendor Expanse for $800 million to gain visibility into exposed and untracked assets in customers’ ecosystems.

Proofpoint
Gary Steele
Chairman, CEO
Proofpoint in June rolled out a cloud-based ObserveIT Insider Threat Management platform to provide insider risk detection, faster incident response and broader visibility across user activity, data interaction and threat context. The updated platform delivers simplified and highly scalable cloud deployments for organizational agility and minimized time to value for resource-constrained cybersecurity teams.

QualysPhilippe Courtot
Chairman, CEO
Qualys Cloud Agent arrived on Google Cloud in May to provide customers with visibility into their workloads and virtual machines with a single click and essentially no software to install or maintain. The company moved into the endpoint detection and response market through its July purchase of Spell Security to boost Qualys’ endpoint behavior detection, threat hunting and malware research skills.

SaviyntAmit Saha
CEO
Saviynt in August updated its Intelligent Identity Platform to provide improved governance, analytics and access to privileged assets across enterprise applications and platforms including Google Cloud Platform. Two months later, the company expanded its integration with Microsoft Azure Active Directory to provide additional advanced identity governance scenarios for enterprise customers.

Sophos
Kris Hagerman
CEO
Sophos has been driving a transition to next-generation cybersecurity leveraging advanced capabilities in cloud, machine learning, APIs, automation and managed threat response to deliver enterprise-grade protection to any size company. Sophos last year began protecting Chrome OS users against unsuitable and malicious web content for the first time with its rebranded Intercept X for Mobile offering.

SysdigSuresh Vasudevan
CEO
Sysdig in March launched a repository of Prometheus exporters, dashboards and alerts to monitor any infrastructure, application and service in the cloud, providing documentation, suggested configurations and customer support. Then in July, Sysdig debuted a five-minute setup for the company’s Secure DevOps Platform to quickly deliver container and Kubernetes security and visibility with a SaaS-first offering.

Trend Micro
Eva Chen
CEO
Trend Micro Cloud One–Application Security launched in November to stop runtime attacks before they occur and help developers pinpoint vulnerabilities in their code that hackers could exploit. Then in January, Cloud One–Container Security debuted to help developers minimize application downtime across Kubernetes by easing the security of container builds, deployments and runtime workflows.

vArmourTimothy Eades
CEO
vArmour partnered with Tufin last year to help enterprises ensure they are secure across the public, private and hybrid cloud by gaining comprehensive intelligence into their application relationships. Then in October, the company teamed up with Okera to help joint customers reduce risk by understanding when users are accessing critical business applications and data across complex environments.

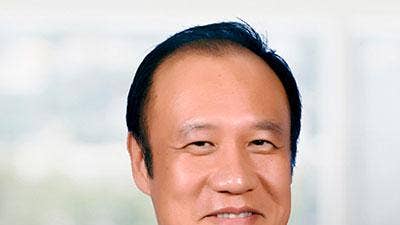
ZscalerJay Chaudhry
Founder, Chairman, CEO
Zscaler agreed in April to buy cloud security posture management startup Cloudneeti for $8.9 million to prevent and remediate application misconfigurations in the cloud. A month later, the U.S. Defense Innovation Unit (DIU) tapped Zscaler to provide zero trust access to protect DIU users and cloud services from cyberthreats no matter where personnel are working or what devices they are using.