Malware Where? Cyberattack On The Storage Industry
New CyberAttack Impacts Storage Everywhere, And No One's Talking About It
When Kaspersky Lab reported on Feb. 16 that the Equation Group, which some in the industry say appears to be tied to the National Security Agency, had inserted malware into the firmware of the IT industry's best-known brands of hard drives, attention was focused on the security implications of the cyberattack.
Left out of the discussion, however, was the potential impact on the data center, where nearly every PC, server and storage system contains one to thousands of hard drives, each of which is a potential traitor waiting to grab, hide and send to someone even encrypted data.
Storage and server vendors for now are essentially saying they haven't heard anything about the alleged spying.
But the ripple effects of this new cyberattack could spread far and wide.

Hacking Hard Drive Firmware
The Equation Group is the first organization known to have reprogrammed hard drive firmware. It did so on hard drives from a dozen popular brands.
In rewriting the hard drive's operating system in the firmware, the Equation Group was able to add software that created an invisible and persistent hidden area. That hidden space can be used to secretly save data "exfiltrated" from a user’s storage system for later retrieval by hackers. Kaspersky also said it could be used to capture an encryption password.
The cyberattack also ensures that the malware can survive a disk format and an operating system re-installation, and essentially "resurrect" itself forever.

Long Time Coming
The Equation Group may have started developing cyberattack technologies as long ago as 1996, Kaspersky reported.
The hard drive firmware cyberattack appears to have been in development since at least 2006. That's when, according to one of the NSA records leaked by Edward Snowden, an organization called the "Persistence Division" secretly sent out a requirement for an intern to work on a "Covert Storage Product."
The requirement called for someone to "create a covert storage product that is enabled from a hard drive firmware modification. The idea would be to modify the firmware of a particular hard drive so that it normally only recognizes, say, half of its available space," according to the leaked records.

How To Get Rid Of The Hack: A Hammer
Given that the malware is hidden in hard disk firmware, is unscannable and cannot be deleted, several media outlets suggested the only way to ensure the malware is eliminated is to destroy the drive.
However, given that a PC may have more than one hard drive, a server two to dozens of drives, and storage arrays hundreds and thousands of drives, that would potentially require a disassembly line with lots of hammers. And after the drives are destroyed, where will the data sit?
For now, there appears to be no practical way to combat the malware.
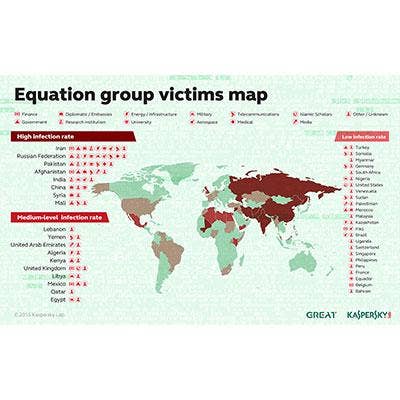
Geography And The Chance Of Being Targeted
The hacks of the Equation Group appear to vary by geography or, more specifically, by geopolitical issues, according to a map Kaspersky published showing where the victims of the attack are located.
While users based in the U.S. faced a low infection rate, and most users in Western Europe saw low or no infection rates, users in such countries as Iran, Russia, Pakistan, Afghanistan, India, China, Syria and Mali experienced high infection rates.

What Are Storage Vendors Doing?
For now, storage vendors have put on a public face of sticking their heads in the sand. The two largest hard drive vendors, Seagate and Western Digital, both said in statements that, prior to the Kaspersky revelations, they had no knowledge of such a cyberattack, and that they are putting in place measures to protect data integrity.
EMC and Hewlett-Packard issued statements to CRN saying they were unaware of such cyberattacks, while other major storage vendors did not offer even such a basic statement.
Pandora's Box Is Now Open
Concerns about the possibility that an agency like the NSA could quietly install undetectable malware in the firmware of hard drives was first highlighted by online tech news source MIT Technology Review, which reported that such a capability was actually demonstrated in 2013 and 2014 with both hard drives and USB sticks.)
"That raises the prospect that multiple national intelligence agencies -- and perhaps even groups without government backing -- could be using the technique. Few, if any, security researchers are on the lookout for such attacks because they are essentially invisible," MIT Technology Review reported.