10 Big Things To Know About Zero Trust Security In 2023
It’s complicated and confusing, and the potential pitfalls are rampant. But many experts believe zero trust is also the key to fixing cybersecurity.

The Zero Trust Shift
It’s one of the biggest trends in cybersecurity, and also one of the hardest to define. Regardless, zero trust continues to grow as a priority for many organizations amid intensifying cyberthreats. What’s happened in 2023, however, is that zero trust has started to get real — with many organizations now actually starting to implement a new cybersecurity strategy based on zero trust principles. And that has revealed a lot.
[Related: Netskope, Zscaler, Palo Alto Networks Lead Gartner’s SSE Magic Quadrant For 2023]
For instance, nearly a fourth of security and IT leaders reported struggling to get buy-in from other departments around zero trust, according to a CyberRisk Alliance survey. Gartner research, meanwhile, found that just 10 percent of large enterprises are on track to have a “mature and measurable zero-trust program” in place by 2026.
In other words, zero trust is not going to happen overnight.
Still, a wide array of organizations are on the path. When it comes to zero trust, “we’re moving from marketing hype into reality,” said John Watts, vice president and analyst at Gartner, in an interview. Among other things, that means that businesses are starting to encounter some of the inevitable pitfalls.
As part of CRN’s Cybersecurity Week 2023, we’re diving into some of those stumbling blocks, while also highlighting where some of the opportunities are for solution and service providers. We’re also looking at some of the areas of debate — including around what counts as zero trust, whether public cloud can support zero trust and whether that’s even still the best term. We’ve included insights from executives at key industry players in the space including Netskope, Zscaler, CrowdStrike, Illumio and Cloudflare, as well as from security solution providers such as Optiv.
Stopping Hackers
While a brief definition for zero trust can prove challenging, as mentioned, the ultimate goal of it is less so: Zero trust, according to many experts, is the ideal architecture for thwarting hackers in today’s threat environment. Following the principles of zero trust means implementing more ways to verify users really are who they claim to be, and adding measures to ensure malicious actors won’t get far even if they thwart initial defenses.
A variety of security tools have come to embody the idea. Those include identity authentication and authorization tools, especially those that ensure users can’t access more than they need to for their role, known as “least-privileged access.”
Another piece of the puzzle is deploying a modern remote access platform—known as ZTNA (zero trust network access)—which is considered a more secure replacement for VPN. A third element that’s useful for zero trust, micro-segmentation, can prevent a breach from spreading across an organization’s environment.
Trust No One
If there is a snappy definition of zero trust, it’s probably this often-repeated phrase: “Never trust, always verify.” That motto derives from the original 2010 paper on zero trust by John Kindervag, then a Forrester analyst, who coined the term “zero trust” and described the key principles of the concept. Kindervag, who is now chief evangelist at zero-trust segmentation vendor Illumio, continues to advocate for the core principles of zero trust that he outlined more than a decade ago. But in an interview with CRN, Kindervag said he has no illusions about how serious of an undertaking zero trust can be.
“Every zero trust environment has to be tailor-made for the [resource] you’re protecting. So you can’t just say, ‘I’m going to roll out this technology or roll out that technology, the way we used to, and maybe hope that I’m going to [achieve zero trust],’” he said. “I know that a lot of people want to do that, because it feels like that’s the ‘easy button.’ But there’s no easy button.”
What follows are 10 big things to know about zero trust security in 2023.

It’s Kind Of A Big Deal
In recent years, zero trust has taken hold as something of a unifying approach for cybersecurity — the high bar that everyone, more or less, should be working toward reaching. The security chaos that resulted from the shift to distributed workplaces gets a lot of credit. So does President Biden’s Executive Order on Improving the Nation’s Cybersecurity from 2021 (“The Federal Government must … advance toward Zero Trust Architecture,” it says in one of the document’s 11 references to zero trust).
The industry-wide push for zero trust is especially noteworthy, however, because of how unprecedented it is in cybersecurity. “I think before in cyber, we’ve been really piecemeal in our implementation of security,” said Max Shier, CISO at security solution and service provider Optiv. “I don’t know if we’ve really looked at it in its holistic nature, like we do now when it comes to zero trust.” Ultimately, zero trust is a comprehensive security program and architecture, he said.
“Whereas before, you may have said, ‘Well, I need my firewall. So let’s look at those and implement firewall rules. I need my endpoint protection, so let’s look at that,’” Shier said. Security tools have “always been segmented and siloed off from each other. It never really has been looked at in a comprehensive manner like this, and as granular as this.”

Many Organizations Go Too Big
With a large number of organizations now pursuing a strategy to get them to a zero trust posture, John Kindervag has a piece of advice: Don’t be in a rush. Yes, the cyberthreats are serious — but zero trust is not a single project that you can do all at once, said Kindervag, the former Forrester analyst who coined the term zero trust. “The No. 1 thing that people stumble with, and the biggest issue, is they try to go too big, too fast,” said Kindervag, who is now chief evangelist at zero-trust segmentation vendor Illumio. “They try to do it for their entire company, or their entire organization, and you can’t scale it that way. Cybersecurity is a massive problem. What zero trust does is it breaks it down into bite-sized, manageable chunks.”
So where’s the best place to start? While there’s a variety of opinions on the right answer to that, Kindervag believes that organizations should start with putting zero-trust protections around their most important or sensitive data or IT systems. For instance, these protections — which he refers to as “protect surfaces” — might go around an electronic medical record system if you’re a health-care provider, or around key applications that use sensitive data, he said. Essential IT services such as DNS or Active Directory are also a good candidate to be prioritized for zero-trust protections, Kindervag said.

ZTNA Is Not The Whole Thing
For those who haven’t already heard this a hundred times: No, there isn’t any one single product or technology that can single-handedly deliver zero trust. That includes ZTNA, or zero-trust network access — an offering that is sometimes conflated with zero trust, probably because of the name. In truth, ZTNA is only one part of the equation. That’s not to downplay its potential usefulness: ZTNA can be a massive improvement on security for organizations that swap out their dated VPN-based remote access system for the technology. When it comes to providing remote access to a company’s applications and data, ZTNA differs from VPN because it considers other pieces of context before granting access, such as location and security health of the user’s device. ZTNA also has the advantage of being able to connect users directly to the resources they need, rather than depositing them on a corporate network where jumping to other IT systems might be possible.
Top providers of ZTNA include Gartner’s three “leaders” in the area of SSE (security service edge) — Netskope, Zscaler and Palo Alto Networks. SSE combines with ZTNA with other capabilities for secure remote access, and is also a component of a SASE (secure access service edge) platform.
During an interview, Netskope Co-Founder and CEO Sanjay Beri (pictured) said that his company’s recently introduced ZTNA Next offering is a “full” replacement for VPNs — in part because it “truly doesn’t give people network access.” The technology “gives them access to only what they need,” Beri said.

There’s Disagreement Over What Counts
When it comes to zero trust, the debate continues to rage over what technologies actually qualify for the category. Among the most-outspoken industry leaders on the subject is Zscaler CEO Jay Chaudhry (pictured), whose company also ranks among the most synonymous with the zero trust concept. In Chaudhry’s view, for a technology to be considered “zero trust,” it must function independently of an organization’s network. VPNs, then, obviously cannot be zero trust, he says. Neither can firewalls, according to Chaudhry — though that hasn’t stopped some vendors from trying to claim otherwise. But perhaps his most contentious argument is that even SASE, which Zscaler helps to enable, is a bit suspect.
“With SASE, I think Gartner says it’s SD-WAN plus SSE,” Chaudhry said in an interview. However, “SD-WAN is anti-zero trust. SD-WAN says, ‘Once you get on a network, you can go anywhere on the network.’ Zero trust says, ‘Sorry, I’ll only connect to your application.’”
Zscaler does support vendors that provide SD-WAN, he noted. “If my customer is doing SD-WAN, we support that, we integrate. But we are not [doing SD-WAN],” Chaudhry said. “I’ve always said we won’t build SD-WAN, and we won’t buy SD-WAN.”

The Term Has A Low Approval Rating
As I’ve written about previously, security professionals are not in love with the term “zero trust.” The frequent misapplication of the term in vendor pitches is part of the problem — but only part. According to Cloudflare CEO Matthew Prince (pictured), the more important problem with the term “zero trust” is that it fails to convey the tremendous value of the concept it embodies. And that value, Prince said, is to give back control over their security to organizations that are lacking it.
“I think we’re still, as an industry, searching for exactly what the right term is,” he said in an interview.
While speaking with CISOs or CIOs, “zero trust is one of those things where I still get tons of eyerolls,” Prince said. “But when I say, ‘What we can deliver to you is total control over how your organization uses your network, and how information flows to and from your network’ — that’s something that is causing customer after customer to say, ‘I need that right now.’”
Ultimately, “maybe a better term for zero trust is ‘total control,’” he said.

MSPs Really Need It
While all organizations can gain benefits from pursuing a zero trust security posture as a goal, MSPs have some unique reasons for needing to make it a priority. First and foremost, MSPs continue to be a massive target for hackers, who are seeking to compromise their systems — such as remote monitoring and management (RMM) — in order to acquire access to their end customers. Earlier this year, the Cybersecurity and Infrastructure Security Agency warned that the malicious use of RMM tools continued to pose a major threat, including to MSPs — pointing to a “widespread” cyberattack campaign from last fall that leveraged the RMM platforms ScreenConnect (now known as ConnectWise Control) and AnyDesk. More recently, in August, CrowdStrike threat hunters reported a 312-percent jump in abuse of RMM platforms by attackers, year-over-year.
“Rather than deploying tools that are going to trip the EDR, they’re going to use an RMM tool, because those are tools that are less alerting to the security team,” Adam Meyers, head of Counter Adversary Operations at CrowdStrike, said in an interview. “Many organizations use them internally already. It’s how they blend in and hide better. The whole goal is to create more space to operate and a longer time to operate. And this is how they do that.”
Getting to more of a zero-trust posture may seem like a source of additional pressure on already-overtaxed MSPs. “It’s one of those things where it’s going to cause some heartburn for a lot of MSPs because a lot people don’t know how to manage it or understand it,” said Roddy Bergeron, CISO at Enterprise Data Concepts, an MSP with offices in New Orleans and Lafayette, La. However, according to Bergeron, zero trust is “something that we’re going to have to learn and adapt to—100 percent.”

ThreatLocker CEO Danny Jenkins
There’s A Massive Channel Opportunity
With so many organizations interested in zero trust, or already pursuing a strategy around it, solution and service providers have a huge opportunity for growth. For smaller service providers, that might initially include bringing MSP-friendly products that are based on zero trust principles such as ThreatLocker’s endpoint protection platform. For larger solution and service providers, zero trust can serve as an opportunity to help customers overhaul their whole approach to security and IT — with numerous ways to add value and generate revenue.
Ultimately, solution and providers are crucial when it comes to enabling zero trust for customers because they’re in a unique position. Few others know all the pieces the way they do, allowing them to look at a customer’s tools and environments as comprehensively as zero trust demands.
“Every company is trying to leverage zero trust right now,” Optiv’s Shier said. “And I think companies like Optiv or other service providers are in a unique position right now [because] you could leverage us, the service provider, to do 90 percent of the work that you need.”

The Public Cloud May Pose A Problem
When it comes to public cloud platforms, there are some under-discussed difficulties around implementing zero trust. That’s according to John Roese, global chief technology officer at Dell Technologies, which is charting a different course from most in terms of seeking to make zero trust a reality. Dell has developed a private cloud offering that brings together numerous technologies and capabilities in an effort to replicate Department of Defense-approved zero trust architecture. However, while Dell is confident that “you can build a zero trust private cloud, it doesn’t mean you can make a public cloud zero trust,” Roese said in an interview.
“To do zero trust, you have to be able to see every component and be able to attest that it is in fact trustworthy,” he said. “You quite frankly have a very difficult problem to solve when doing this [in the] public cloud.”
The Ideal Level Of Investment Will Vary
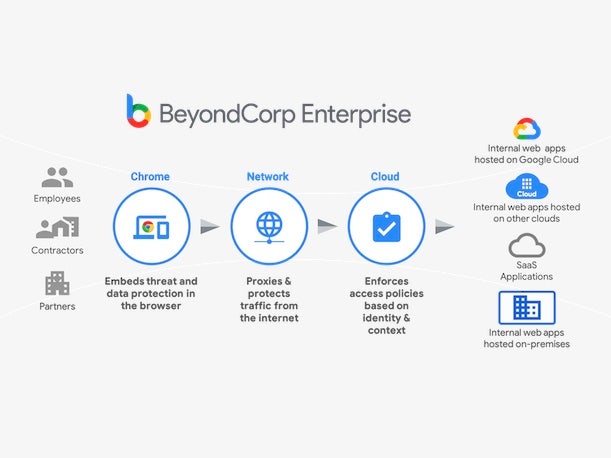
The march toward zero trust that we see today kicked off in 2009, in the wake of the China-attributed “Aurora” attacks on Google. The massive cyberattack prompted the company to begin its BeyondCorp initiative, seen as the first major zero trust implementation. Most businesses are not Google, however, and may not need to invest as heavily or go as far with zero trust as the tech giant did. The ideal level of investment in zero trust will vary, depending on the needs and goals of each organization, said John Watts, vice president and analyst at Gartner.
For example, a mid-sized company “might achieve some of their goals just by implementing some point solutions in reducing some of the primary risks that they have,” Watts said. “They might be able to take services running on the internet, put them behind a firewall for access, so nobody can just scan and exploit them. That’s a positive for zero trust, and it reduces risk.”
Businesses should pinpoint the “clear primary risks” that they aim to address with zero trust, which they can often tackle incrementally, with standalone tools that aren’t necessarily part of a sweeping zero trust platform, he said.“You don’t need to have the biggest strategy in the world with [major] investments to do that,” Watts said.
“Depending on the organization, smaller ones may just say, ’Hey, I’m going to replace my VPN with ZTNA, and I’m going to try to get more granular on my controls. Maybe I don’t get to this highest level of maturity — maybe I never get to micro-segmentation.’ That’s probably fine,” he said. “That probably reduces their primary risk.”

There’s Lots Of Other Important Stuff, Too
Arguably, the campaign to get businesses to care about adopting zero trust may have been a little too successful. With all of the hype about zero trust in recent years, there’s now a tendency among some businesses to “over-invest and put too much focus on it,” Gartner’s Watts said.
As a result, some businesses run the risk of neglecting other things they need to do to protect themselves — issues that zero trust can’t help with, he said. It bears keeping in mind, Watts said, that “zero trust doesn’t address all of the threats of an organization.”
For instance, organizations today are doing more and more with offering externally facing applications and services. “They’re expanding your attack surface,” he said. “But not all of those can be behind a zero trust control.”
Another prime example is software supply chain attacks, such as the compromise of the SolarWinds Orion network monitoring platform in 2020. Zero trust could potentially help to prevent attackers from initially infecting an application’s code. But if a threat actor succeeds at compromising an application that gets distributed to customers as an update, like in the SolarWinds attack, “zero trust doesn’t solve that problem,” Watts said.
“That’s all a trusted process typically,” he said. “And that thing running in your environment is in a spot where you trust its activity, because you installed it and manage it.”