10 Emerging Cybersecurity Threats And Hacker Tactics In 2023
The cyberthreat landscape continues to evolve, with attackers continuing to adopt new tactics in response to numerous factors — including the success of endpoint security tools.

Emerging Threats
Perhaps it goes without saying, but in 2023, there’s no shortage of alarming trends in the area of cyberthreats. The MOVEit attacks have underscored the shift by some attackers aware from encryption-based ransomware, in favor of data theft and extortion-only. Many attackers are relying less and less on malware and more on exploiting tools such as remote monitoring and management (RMM), which are less likely to be caught by endpoint security products. Identity-based attacks using compromised credentials are continuing to surge for similar reasons, as a way to get around endpoint detection and response (EDR). Phishing and social engineering remain massive threats to organizations across the board.
[Related: The 10 Biggest Data Breaches of 2023 (So Far)]
But threats and hacker tactics also continue to evolve in 2023.“We’re seeing diversification relative to the type of attacks,” SonicWall CEO Bob VanKirk told CRN in a previous interview. Based on a number of factors, “threat actors are continuing to pivot,” he said.
In terms of emerging threats in 2023, attacks leveraging generative AI has gotten a lot of the attention (and yes, GenAI factors into the list that follows). But there’s been a lot more going on when it comes to the appearance of new hacker tactics this year. Security researchers have identified numerous emerging threat trends and new tactics across phishing and social engineering, data theft and extortion, ransomware and software supply chain attacks.
As part of CRN’s Cybersecurity Week 2023, we’ve compiled a sampling of the new threats and hacker tactics that have emerged over the past year. We’ve compiled the details from CRN interviews and posts by researchers and incident responders from Huntress, CrowdStrike, Zscaler, Mandiant, Microsoft, GuidePoint Security and Cisco Talos, among others.
What follows are 10 emerging cybersecurity threats and new hacker tactics to know about in 2023.

‘Leveling Up’ Invoice Fraud
Accounts payable fraud — in which an attacker poses as a vendor and sends an invoice to an intended victim with their own account number — is nothing new. Huntress researchers, however, have spotted a sneakier new take on the threat. In a number of cases, Huntress has seen attackers who’ve compromised an email account and then use creative tactics to do “very targeted fraud” with the account, Huntress Co-Founder and CEO Kyle Hanslovan told CRN. The way it works: Once inside the account, the attacker will set up rules to forward an incoming invoice to them, and then delete it, preventing the victim from receiving the real invoice, he said. Then, the attacker modifies the invoice to include their account number and sends it along to the victim, Hanslovan said.
“It’s just leveling up the game,” he said.”We’ve only had telemetry on this for two quarters, and we already found several dozen incidents. So the answer is, it must be common.”

Ransomware Broadens Scope, Adds New Tactics
In 2023, one emerging development in the cyberthreat sphere is that new ransomware groups have arisen as a result of gaining access to leaked source code and builders, according to researchers at Cisco Talos. This is notable not just because it means the arrival of additional players in the ransomware sphere, but also new types of players with a different focus area. Some of these new threat actors have actually been observed using ransomware leveraging the leaked code “to target individuals and smaller companies,” Talos researchers wrote in a recent blog.
Meanwhile, the FBI warned in September that a pair of new trends have emerged among ransomware-focused threat actors. In the first, threat groups are bringing “multiple ransomware attacks on the same victim in close date proximity,” according to the FBI advisory. The attacks have also included deployment of two different ransomware variants “in various combinations,” the FBI said. “This use of dual ransomware variants resulted in a combination of data encryption, exfiltration, and financial losses from ransom payments. Second ransomware attacks against an already compromised system could significantly harm victim entities.”
As for the second emerging trend identified by the FBI, ransomware threat actors have been served bringing new tactics around data destruction during attacks — with the deployment of wiper tools in an effort to pressure victims, the agency reported.

Minimally Disruptive Attacks
For some attackers who are just focusing on data theft and extortion rather than encryption, they’ve got a new tactic: Rather than maximizing disruption for victims, some attackers are seeking to minimize it, cyberthreat experts told CRN. This effortis part of an effort to rebrand themselves almost as security advisors, the experts said.
As bizarre as it may sound, “we’re seeing this ransomware threat landscape moving more and more towards ‘customer service,’” said Deepen Desai, global CISO and head of security research at Zscaler. Now, some threat actors are actually aiming to “provide the best experience” to victims, Desai said.
At GuidePoint Security, the incident response team has encountered multiple cases where attackers have told their victims, “‘we did you the favor of not encrypting your environment,’” said Mark Lance, vice president for DFIR and threat intelligence at GuidePoint.
Such attackers will then provide a “security audit report” outlining how to better secure a breached victim’s environment, Lance said. “They consider themselves [to be] basically providing a security consulting service.”

New Tactics For Data Leaks
In the case of some malicious actors focused on data theft and extortion, threatening to post the stolen data on the darkweb has served as the incentive for victims to meet the attackers’ payment demands. Most prominently, that was true of the Russian-speaking cybercrime group Clop, which was behind this year’s wide-ranging MOVEit attack campaign. Or rather, that was true initially: After apparently feeling the need to up the pressure on certain victims, Clop “has been trying different ways to get that info out,” said John Hammond, senior security researcher at Huntress. First, Clop began setting up leak sites on the clearweb — i.e. the open internet — but those turned out to be easily taken down. The group then began offering torrents of stolen data, which BleepingComputer reported have been more difficult to get removed due to their decentralized distribution system, as well as being faster to download.

Strange Bedfellows
There are many concerning elements of the recent high-profile attacks against casino operators MGM and Caesars Entertainment — including the reported use of social engineering by the hackers to trick an IT help desk into providing access in the MGM breach. But also among the unwelcome developments is the reported collaboration that has been behind the attacks: An alliance between young English-speaking hackers in the group known as Scattered Spider and Russian-speaking ransomware gang Alphv. According to security researchers, the teenage and young adult hackers of Scattered Spider utilized BlackCat ransomware that was provided by Alphv (a gang whose members have previously been affiliated with DarkSide, the group behind the Colonial Pipeline attack). While ransomware-as-a-service has been a growing trend for years in Eastern Europe, the alliance between teen hackers — which some reports say include members in the U.S. and U.K. — and Russian-speaking RaaS groups serves to expand the threat landscape in troubling new directions.

RaaS Comes To ESXi
Speaking of ransomware-as-a-service, researchers at CrowdStrike have shared details about how this year it has been extended to include RaaS targeting VMware’s popular ESXi hypervisor. “In April 2023, for example, CrowdStrike Intelligence identified a new RaaS program named MichaelKors, which provides affiliates with ransomware binaries targeting Windows and ESXi/Linux systems,” the researchers wrote in a blog. “Other RaaS platforms capable of targeting ESXi environments, such as Nevada ransomware, have also been launched.” The use of ESXi-specific RaaS platforms comes as the hypervisor continues to be an increasingly attractive target for cybercriminals, on account of a “lack of security tools, lack of adequate network segmentation of ESXi interfaces, and [in the wild] vulnerabilities for ESXi create a target-rich environment,” the CrowdStrike researchers wrote.

GenAI-Powered Threats
With the massive amount of discussion there’s been on the topic this year, it’s sometimes easy to forget that generative AI-powered cyberattacks still constitute a very new threat. Among the well-known security risks from GenAI is the boost it can give to malicious actors, such as hackers using OpenAI’s ChatGPT to craft more-convincing phishing emails.
Security researchers have also identified GenAI-powered chatbots that are specifically intended for use by malicious hackers and other criminals — including WormGPT, FraudGPT and DarkGPT.
But even ChatGPT itself can provide a significant aid to hackers, such as by improving grammar for non-native English speakers, researchers have noted. And there are no guardrails that could prevent ChatGPT from serving up many types of emails that could be exploited for social engineering — for instance, an email to your “uncle” that you haven’t talked to in years, said Mike Parkin, senior technical marketing engineer at Vulcan Cyber.
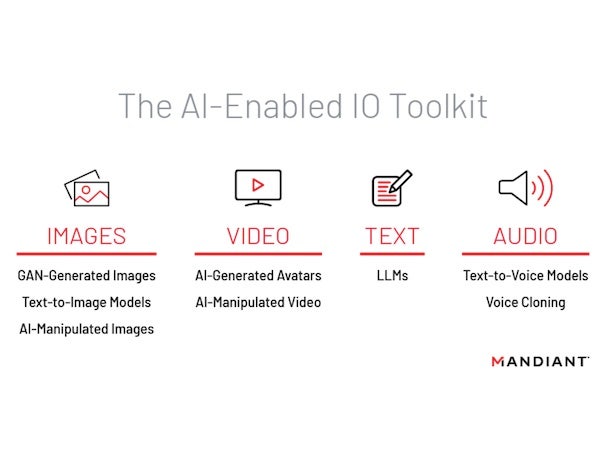
Deepfake Tooling
Elsewhere in the world of worrisome issues of AI, deepfakes have been viewed as a potential security threat for a while now — and in some reported cases, have succeeded at tricking victims into transferring funds. But a more recent development in this area is the reported availability of deepfake video creation software that has been designed for phishing. In mid-August, Mandiant researchers said that they’ve observed advertising in “underground forums” about this software, which is intended to help make malicious operations “seem more personal in nature through the use of deepfake capabilities.” It’s the first known case of “deepfake video technology designed and sold for phishing scams,” Bloomberg reported.
Meanwhile, audio deepfakes have had a moment in 2023 — in part thanks to the growing availability of voice-cloning software. Predictably, audio deepfakes are also being used in funds transfer scams. And as reported previously, the bigger threat in this sphere is that attackers may ultimately be able to achieve “real-time” voice deepfakes, allowing them to have their own voice converted into a cloned voice with minimal latency.
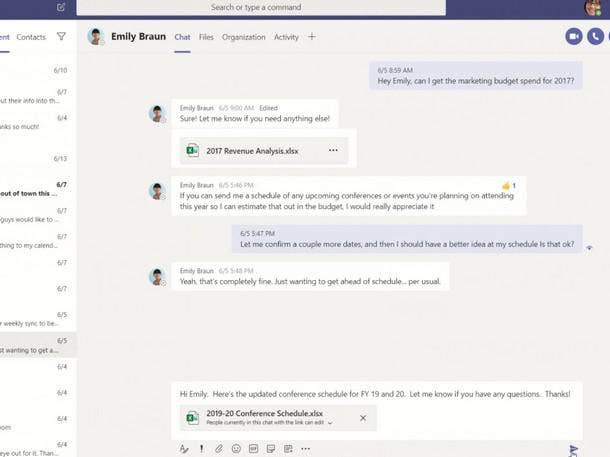
Teams-Enabled Phishing
Another impersonation threat that’s seen an uptick in 2023 involves Microsoft Teams, and the use of compromised Microsoft 365 accounts to carry out phishing attacks on the collaboration app. In August, Microsoft Threat Intelligence disclosed that the group behind the widely felt 2020 SolarWinds compromise has recently been behind a cyberattack campaign using Teams messages. The attackers use Teams messages “to send lures that attempt to steal credentials from a targeted organization by engaging a user and eliciting approval of multifactor authentication (MFA) prompts,” Microsoft researchers wrote. The group — previously tracked by Microsoft as Nobelium, and now tracked as Midnight Blizzard — is likely pursuing “specific espionage objectives” in the Teams-driven attacks, the researchers said.
In early September, meanwhile, Truesec disclosed that it had investigated a campaign involving the use of Teams phishing messages to distribute attachments that would install the DarkGate Loader malware, which can be used for malicious activities including ransomware deployment.
Also in September, Microsoft researchers shared that a cybercriminal group tracked as Storm-0324 has been “observed distributing payloads using an open-source tool to send phishing lures through Microsoft Teams chats.” The attacks, which are unrelated to the Midnight Blizzard campaign using Teams, are believed by Microsoft researchers to be aimed at gaining initial access — which can later be sold to other threat actors who’ll use the access for malicious activities such as ransomware deployment.

Double Supply Chain Attack
The compromise in March of 3CX, a widely used communications software maker, in some ways resembled the SolarWinds supply chain attack of 2020. But the 3CX attack has stood out from past software supply chain compromises in at least in one major respect: The 3CX campaign was made possible by an earlier supply chain attack, according to Mandiant. In the earlier compromise, attackers had tampered with a software package distributed by a financial software firm, Trading Technologies, Mandiant researchers disclosed. “This is the first time Mandiant has seen a software supply chain attack lead to another software supply chain attack,” researchers said in a post.
The 3CX attack was attributed by CrowdStrike, and later by Mandiant, to North Korea.
Nick Galea, founder and CEO of 3CX, said in a post that the company is committing to “harden our systems” in the wake of the “first-of-a-kind, cascading software-in-software supply chain attack.” Galea previously disclosed that it’s probable hundreds of thousands of customers did actually download the malicious version of the vendor’s VoIP phone system software.
However, researchers have noted that the 3CX compromise was caught in weeks rather than months — as had been the case with the SolarWinds attack — which appears to have limited the impact from the breach on 3CX and its end customers.