The 2020 Tech Innovator Awards
The delivery of truly differentiated offerings that create opportunities for partners during this unprecedented period is the crowning achievement of our 2020 Tech Innovators.

Accelerating Innovation
In a year of unheard-of change and uncertainty, one thing has actually stayed pretty consistent: the acceleration of digital transformation. The pace already was speeding up prior to the COVID-19 pandemic, but the crisis has taken digital transformation efforts to heights that few would have thought achievable in such a short time. Powering this shift are innovative vendors in sectors across the IT industry—and the solution provider partners who bring these differentiated products and services to customers.
What counts as innovation in a year when the home environment has become the office and the classroom for countless people across North America? While most tech companies claim to have differentiated products that are relevant in the current crisis, not all truly deliver—or don’t do so in a way that creates opportunities for partners. To help with recognizing true channel-friendly innovation, the 2020 CRN Tech Innovator Awards honor products and services that offer both major advances in technology and partner growth opportunities—across areas including cloud, security, software, infrastructure and devices. The awards this year showcase trailblazing vendors in 48 categories, along with two Editor’s Choice awards for deserving products that didn’t fit elsewhere. The winners and finalists were chosen by CRN staff from among 388 applicants.
The delivery of truly differentiated offerings that create opportunities for partners during this unprecedented period is the crowning achievement of our 2020 Tech Innovators. CRN’s 2020 Tech Innovator winners and finalists appear on the following slides.

3-D Printers
Winner:
Markforged X7
The flagship industrial 3-D printer from Markforged, the X7, uses dual-nozzle printing technology and a laser micrometer to lay continuous fibers with high accuracy and print quality. Materials available with the X7 include carbon fiber, Kevlar and fiberglass, and the 3-D parts printed with the system are ideal for verticals such as automotive and aerospace. Recent enhancements to the Markforged X7 include the addition of Turbo Print capabilities, which double the printing speed without reducing quality. Bringing Turbo Print to the X7 has enabled expedited development schedules for manufacturers and, ultimately, a quicker time to market.
Finalist:
Formlabs Form 3B
Formlabs’ Form 3B desktop 3-D printer has been developed specifically for dental and medical professionals. Key benefits of the Form 3B include high-accuracy prints and reliability—as well as affordable material, validated workflows and dental-specific support and warranty. The Form 3B also comes paired with intuitive software.
Big Data Platforms
Winner:
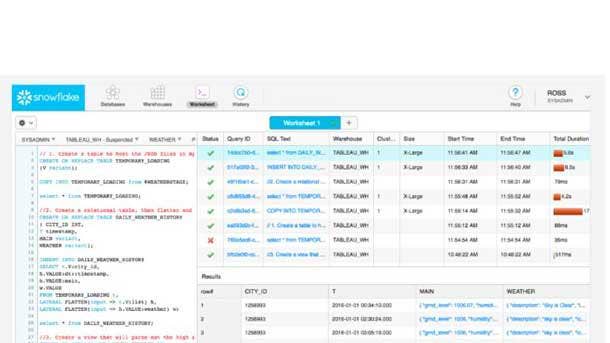
Snowflake Cloud Data Platform
Snowflake has expanded to become a broad-based cloud data platform provider, with services that touch on data engineering and data science tasks, data lake management and data sharing. The Snowflake Cloud Data Platform provides a centralized place for deriving business insight from big data via a data warehouse that was created for the cloud along with secure access to an entire network of data and a core architecture to support versatile data workloads. Recent updates to the Snowflake Cloud Data Platform include the new Snowsight analyst experience for executing queries and commands against Snowflake; Dynamic Data Masking to enable different views of data based on user permissions; and enhanced data protection through integration with third-party tokenization offerings.
Finalists:
Cloudera Data Platform
The Cloudera Data Platform is an integrated platform for data management and governance, providing self-service analytics and artificial intelligence applications across hybrid and multi-cloud environments. Applications that run on the platform include Cloudera Data Warehouse, Cloudera Machine Learning and Cloudera Data Hub.
Couchbase Cloud
Couchbase Cloud is the next-generation database from Couchbase, available as a fully managed Database as a Service running on Amazon Web Services. The offering is based on the Couchbase Server, a multipurpose NoSQL database that combines a high-performance, memory-first, globally replicating cluster architecture with key-value stores, a SQL-compatible query language and a schema-flexible JSON format.
Domino Data Science Platform
With its Domino Data Science Platform, Domino Data Lab offers a centralized platform for enterprises performing data science work. The platform enables everything from collaborative model development to training and deployment to life-cycle management—ultimately empowering data scientists to accelerate their innovation.

Business Intelligence and Analytics
Winner:
Google Looker 7
Looker Data Sciences, now a part of Google Cloud, debuted its Looker 7 business analytics platform in November 2019, offering new features and enhancements that integrate analytical insight with day-to-day tools and workflows. Looker 7 makes it easier to apply analytical insight and curated data from Looker to other applications, including through a closed-loop integration with the Slack collaboration application as well as third-party integrations with applications such as Box, Dropbox and Google Drive. In August, an update to Looker 7 added support for the complete Google Marketing Platform, upgrades for application builders and the general availability of Looker’s content marketplace.
Finalists:
Cisco AppDynamics
Recent enhancements to Cisco’s AppDynamics offering have included the introduction of the AppDynamics Experience Journey Map—a new view that provides users or partners with visibility into the path of an application, using data science algorithms that can pull out information in real time. The map shows user flows overlaid with performance and business metrics, which enables the identification of problems such as application bottlenecks.
Juniper Mist Premium Analytics Service
The Juniper Mist Premium Analytics includes network and location analytics to provide customers with comprehensive visibility into their network, as well as key insight about their business. The AI-powered solution is helping with the return to offices with uses such as journey mapping (identifying areas that will need sanitization) and proximity tracing (which can determine who has been in proximity to a worker who’s had a positive test result).
Promethium Data Navigation System
Promethium is addressing the challenges of self-service data discovery and self-service analytics with its Data Navigation System—a data context platform that uses machine-learning algorithms and natural language processing to rapidly provide users with the right data to answer the right question.
Cloud Data Protection/Disaster Recovery
Winner:
Veeam Availability Suite v10
With the much-anticipated version 10 of its flagship Availability Suite, Veeam has doubled down on automation and simplification while enhancing its already robust data protection and recovery capabilities. Veeam Availability Suite v10 brings more than 150 enhancements and new features including simplified protection via network-attached storage backup; automation of disaster recovery from data center outages (with the new Multi-VM Instant Recovery feature); improved ransomware protection through an updated S3 object storage integration, paired with immutable backups; and additional capabilities and support for platforms including HPE Primera and HPE StoreOnce, Nutanix AHV, Linux and MySQL.
Finalists:
Commvault - Metallic Backup and Recovery Solution
Metallic is a cloud-native portfolio of SaaS solutions for data backup and recovery, featuring all of the capabilities of Commvault’s trusted core technology baked in. Metallic provides users with flexibility by enabling them to keep a copy of their data on-premises for faster recovery, while still enjoying all the benefits of a SaaS-delivered cloud backup solution.
Datto SaaS Protection 2.5
Datto’s SaaS Protection 2.5 makes it easier for MSPs to rapidly on-board new Microsoft 365 and G Suite clients—simplifying the process while also protecting customer data. For Microsoft 365’s entire suite of services, Datto’s SaaS Protection 2.5 offering provides automatic backup, recovery and restore capabilities.
IBM Spectrum Protect Plus
IBM Spectrum Protect Plus is an enterprise-class data protection and cyber-resiliency offering that delivers capabilities for the protection and reuse of containers, VMs, databases and applications—in on-premises, hybrid cloud or Backup-as-a-Service environments. SLA-based policies provide consistent automation of the entire data protection process, including backup, replication, and secure data retention on-premises as well as in the cloud.
StorageCraft ShadowXafe
StorageCraft ShadowXafe delivers powerful system and data recovery options, enterprise-level scalability and a workflow optimized for management simplicity—all from the cloud-based OneSystem management platform. Through the management platform, users identify the workloads to protect and define backup and retention policies for each of those workloads based on SLA requirements.
Veritas NetBackup 8.3
Veritas significantly enhanced its cloud capabilities in its NetBackup 8.3 release—for instance, converging its NetBackup CloudCatalyst deduplication technology with its MSDP storage servers. The update also expanded the product’s ability to counter ransomware, including with built-in understanding of customers’ data immutability along with retention lock management.

Cloud Infrastructure-as-a-Service
Winner:
HPE GreenLake Cloud Services
Hewlett Packard Enterprise is out to deliver a cloud experience for applications and data across the hybrid estate with its GreenLake Cloud Services—bringing pay-per-use, self-service and scalability regardless of whether apps and data are on-premises, in colocation or at the edge. The offering covers everything from container management, storage and virtual machines to networking, compute and data protection while also providing preintegrated building blocks as well as a choice of configurations for its services. Included as part of the offering is HPE’s GreenLake Central, a portal that lets partners and customers centrally manage their hybrid environments while also doing complex cost, compliance and security analysis. HPE’s GreenLake Cloud Services ultimately enable—and accelerate—the modernization of apps and data wherever they are found.
Finalist:
AWS Outposts
Amazon Web Services, the largest public cloud platform by market share, brought its on-premises version of its public cloud into general availability last December, with the launch of AWS Outposts. The offering entails AWS installing and managing a server rack in its customers’ data centers, and addresses the needs of enterprises that must keep applications close to home. Outposts launched with AWS EC2 instances and EBS block storage, as well as two hosted container services, ECS and EKS. S3 storage on AWS Outposts became available in September. The first variant of Outposts is the “AWS native” option for customers that want to use the AWS APIs and control plane alongside their deployments in AWS regions. A second variant of AWS Outposts, for customers that want to use a VMware control plane is expected in 2020.
Cloud Migration
Winner:
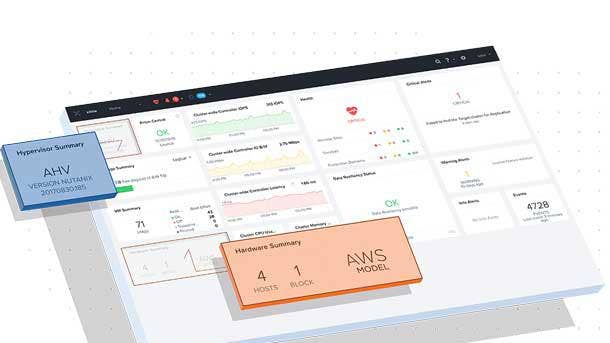
Nutanix Clusters On AWS
With the recent debut of its Nutanix Clusters on AWS offering, Nutanix brings its hybrid cloud infrastructure to Amazon Web Services, enabling accelerated digital transformation using a streamlined solution for moving applications and data into the cloud. Nutanix Clusters on AWS offers a unified cloud environment for creating, managing and orchestrating infrastructure, while enabling the move of legacy applications to the cloud without the need for rearchitecting the apps. Key elements include integration with the networking layer in AWS, as well as cost reduction through eliminating the need for every cloud environment to be managed by a different team.
Finalists:
BitTitan MigrationWiz
MigrationWiz is a SaaS offering for mailbox, document, public folder and Microsoft Teams migrations between a wide range of sources and destinations. Recently, BitTitan launched its new Hybrid Exchange Management capabilities in MigrationWiz to simplify migrations between on-premises Exchange servers and Microsoft 365.
Quest Software - Quest On Demand Migration
Quest On Demand Migration, an offering available within the Quest On Demand SaaS platform, automates complex, repetitive and error-prone steps in the tenant-to-tenant migration process. Organizations can reduce migration project costs and perform highly reliable and secure migrations while more easily moving Azure Active Directory, Exchange Online, SharePoint, Teams and OneDrive resources from one Office 365 tenant to another.

Cloud Tools And Management
Winner:
VMware CloudHealth
With powerful functionality for management and operation of multi-cloud environments, VMware’s CloudHealth enables optimized scaling of cloud infrastructure along with improved decision-making around everything from security to cost management. CloudHealth supports a broad set of environments including Amazon Web Services, Microsoft Azure, Google Cloud and Oracle Cloud as well as VMware, containers and bare-metal infrastructure. Partner-friendly enhancements have included the introduction of CloudHealth Savings Plan Recommendations, which allow MSPs to offer a comparison of all options for AWS Savings Plans. CloudHealth thus enables MSPs to guide a customer to the ideal Savings Plan choice based on the customer’s specific needs.
Finalists:
Cisco Intersight
With its Intersight platform, Cisco delivers life-cycle operations as a service, connecting technology domains (compute, storage, network, hyperconverged, cloud, virtualization and containers) across data center, edge and cloud. The offering also adds value by leveraging data to optimize development and deployment costs.
CloudBolt Cloud Management Platform v9
CloudBolt’s latest cloud management platform enables enterprise IT teams to rapidly provision, configure and manage hybrid cloud resources across more than 20 cloud providers. CloudBolt includes capabilities such as a unified orchestration platform; a self-service IT portal; and controls that empower IT teams to enforce cost, security and compliance for the delivery of cloud resources.
HashiCorp Terraform Cloud
HashiCorp Terraform Cloud offers a quick way to adopt the widely used Terraform multi-cloud provisioning product. Offered as a service, Terraform Cloud enables enterprise IT teams to shift to Terraform infrastructure as code for provisioning, compliance and operational consistency across cloud, data centers and third-party applications.
Volterra VoltStack
With VoltStack, Volterra offers a SaaS-based platform to deploy, secure and operate apps in the edge and across clouds. The platform consolidates multiple services across app clusters, while enabling zero-touch provisioning of infrastructure nodes, platform services and apps. VoltStack’s distributed control plane and standard Kubernetes APIs enable users to efficiently manage a large fleet of app clusters.

Collaboration Apps/Unified Communications
Winner:
Intermedia Unite
While collaboration and unified communications applications have boomed in 2020, the Intermedia Unite platform stands out by putting the needs of SMBs at the forefront and by integrating partner feedback into new updates. Intermedia Unite, which brings together a PBX phone system with chat, videoconferencing, file sharing and backup, provides its Unified- Communications-as-a-Service offering with simplified management capabilities and strong reliability, ideal for SMBs and the solution providers who serve them. And in response to partner input, Intermedia recently brought Contact Center as a Service to Unite as an integrated feature for the platform. The integration has added call handling and routing features that are geared toward small businesses without the complexity of contact center offerings meant for larger customers.
Finalists:
8x8 Voice for Microsoft Teams
8x8 Voice for Microsoft Teams is a cloud telephony solution for Teams environments that enables customers to scale and deliver “operate-from-anywhere” communications. Ultimately, 8x8 Voice for Microsoft Teams provides a voice offering that is easy for IT to administer while also keeping the usual Teams experience intact for end users.
Cisco WebEx
Cisco’s WebEx collaboration platform has featured enhancements such as the launch last year of the Webex Teams unified app. The app brings together calling, meetings, messaging and video device control, providing customers with a consistent experience regardless of how they join. Other recent updates to Webex have included new grid views, virtual backgrounds and blurring for backgrounds.
Nextiva Cospace
Cospace is Nextiva’s offering to help businesses navigate the shift to remote work. Cospace features HD voice and video, task management, file sharing, calendar management and chat—all designed with a simplified and user-friendly interface. Capabilities include video and audio meetings with up to 250 participants.
RingCentral Video
RingCentral Video seamlessly integrates video chat with RingCentral’s UCaaS platform, providing a comprehensive messaging, video and phone offering for businesses of all sizes. RingCentral enables users to easily switch between methods of communication without leaving the app, and the app can be accessed from any browser without the need for downloading it.
Zoom Phone
Available as an add-on to Zoom’s videoconferencing platform, Zoom Phone is a cloud phone system that supports inbound and outbound calling through the public switched telephone network. Zoom Phone offers integrated telephony features that enable customers to replace their existing PBX solution and ultimately consolidate all of their business communications and collaboration onto the Zoom platform.
Contact Center Apps
Winner:
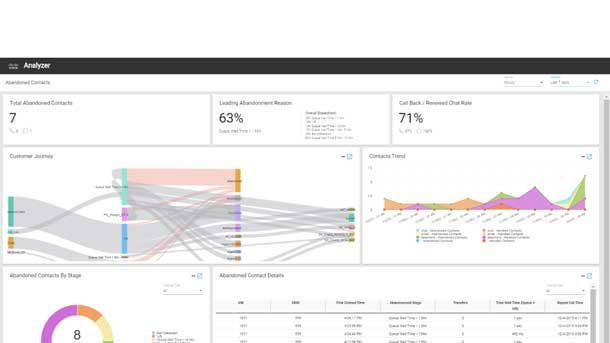
Cisco Webex Contact Center
With advanced capabilities leveraging artificial intelligence and machine learning, the Cisco Webex Contact Center enables enhanced customer experiences through greater speed and personalization. AI-driven capabilities include virtual agents (both voice and chat); real-time suggestions and guidance for agents; and call transcriptions and summaries. Integrated with enterprise-class calling, workforce optimization and data analytics, Cisco Webex Contact Center also offers interoperability with other Cisco products and cloud services via its multitenant cloud foundation. Meanwhile, partners and customers can develop customized features for Webex Contact Center, including AI features, through the availability of a set of APIs.
Finalists:
Avaya AI Virtual Agent
Avaya AI Virtual Agent integrates Google Cloud’s Contact Center AI technology to enable automation of simple tasks and free up employees. The offering leverages natural language understanding and conversational speech capabilities, and allows customers to deploy a single virtual agent across channels; capture customer context; and elevate the interaction to a live agent if needed.
CoreDial CoreNexa WFM
A workforce management module for CoreDial’s CoreNexa Contact Center solution, CoreNexa WFM allows businesses to manage both on-site and remote agents through cloud-based technology that is simple to deploy. The offering enables contact center administrators with capabilities for planning; monitoring and adjusting of agent schedules; tracking of adherence; and forecasting of incoming demand.
Edify Huddle
Edify Huddle brings together unified communications, contact center and communications platform functionality in a single, cloud-native software solution. The platform enables users to move easily among channels within one conversation, providing contact center agents with flexibility to solve problems faster and more completely from a centralized location.
Eleveo Workforce Management
Eleveo WFM is a cloud workforce management offering aimed at simplifying and improving forecasting and scheduling for contact centers and back-office teams. The offering provides automated integrations to Cisco Unified Contact Center Express APIs, while manual call history imports can be fully operational in less than a day.
Container Technology
Winner:
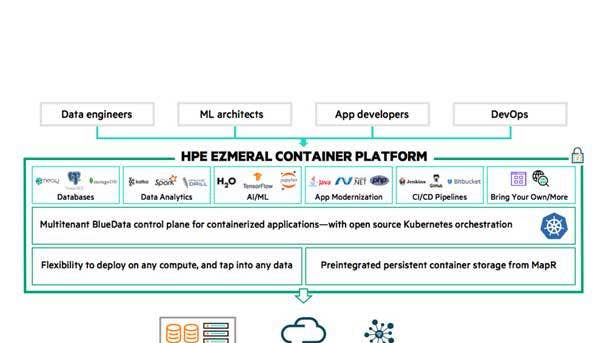
HPE Ezmeral
Hewlett Packard Enterprise recently unveiled Ezmeral as its new open-source, cloud-native Kubernetes container software. Ezmeral provides the Infrastructure-as-a-Service and Platform-as-a-Service offerings for partners and customers to build a new generation of intelligent applications that take advantage of the platform’s robust artificial intelligence and machine- learning capabilities. Major differentiators include Ezmeral’s ability to provide persistent storage through the MapR file system and the AI capabilities of HPE BlueData.That software is designed to run both stateful and stateless workloads, allowing HPE to provide the same cloud experience in a cloud-native or on-premises workload in the data center or in real time at the edge.
Finalists:
Diamanti Spektra 3.0
Diamanti Spektra 3.0 is a cloud-neutral Kubernetes management platform that breaks from legacy architectures to deliver simple and cost-effective solutions—both on-premises and in the cloud. Key capabilities in Spektra 3.0 include multicluster management across bare metal and public cloud, as well as integrated application deployment, migration and disaster recovery for stateful applications.
Red Hat OpenShift 4
Enhancements to Red Hat’s OpenShift 4 platform include the introduction of a developer-centric view of platform metrics and monitoring for application workloads; monitoring integration for Red Hat Operators; and cost management capabilities for assessing the costs and resources for specific applications across a hybrid cloud environment.
SentinelOne Workloads
Built for securing Kubernetes-orchestrated container workloads, SentinelOne Workloads offers autonomous runtime protection, detection and response. The offering protects containerized applications from unknown malware, zero-day threats and in-memory attacks in real time while automatically pinpointing the targets of the attacks.
Snyk Container
Snyk Container enables developers to easily find, fix and monitor vulnerabilities in containers and Kubernetes applications throughout the software development life cycle. The offering is designed to work with a range of container image operating systems and package managers, Kubernetes platforms and container registries.
Data Center Infrastructure
Winner:
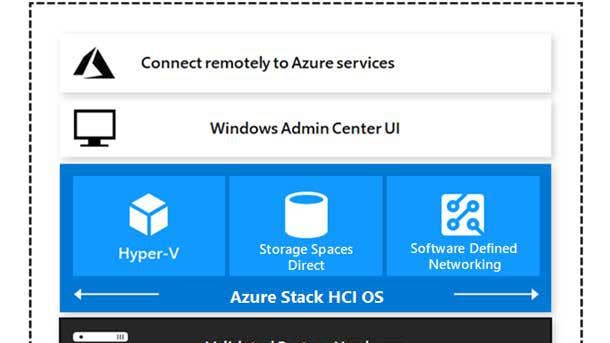
Microsoft Azure Stack HCI
Designed for customers who want to run virtualized applications on hyperconverged infrastructure, Microsoft’s Azure Stack HCI includes the company’s Hyper-V hypervisor, Storage Spaces Direct for storage virtualization and Azure Monitor to get a global view of system health. Customers can utilize Azure Monitor for containers to better understand the performance and health of clusters from infrastructure to application. Recent Azure Stack HCI enhancements include improved manageability through Windows Admin Center; integration with improved security; and day one support for Samsung’s Z-SSD, Intel Optane, AMD’s EPYC and Intel’s Xeon Scalable processors. Notably, Microsoft offers Azure Stack HCI on a variety of hardware from vendors including Asus, Cisco, Dell EMC, HPE, Lenovo and Western Digital.
Finalists:
Cyxtera Enterprise Bare Metal
Cyxtera’s Enterprise Bare Metal platform is a carrier-agnostic alternative to public cloud environments, offering comparable security, control and performance to dedicated colocation infrastructure in an on-demand model. The platform can substantially reduce dedicated infrastructure costs while boosting IT staff productivity with remote configuration and deployment features.
HPE Nimble Storage dHCI
With Nimble Storage dHCI, Hewlett Packard Enterprise delivers improved resiliency, performance and economics than traditional hyperconverged infrastructure. Data efficiency and independent scaling of compute and storage contribute to reduced costs with Nimble Storage dHCI, while the system features 99.9999 percent of data availability guaranteed and sub-millisecond latency.
Nutanix Remote IT Infrastructure Operations
Nutanix’s Remote IT Infrastructure Operations includes Nutanix Foundation Central, Insights and Life Cycle Manager—enabling IT teams to deploy, monitor, troubleshoot and upgrade their cloud infrastructure while working from anywhere. The offering can be used to deploy private cloud infrastructures on a global scale from a single interface, while also providing predictive health and automated support services.
Red Hat Enterprise Linux 8
For Red Hat Enterprise Linux 8—the widely used platform for bringing the Linux operating system into the enterprise—the platform has been redesigned for the era of hybrid cloud. New additions in Red Hat Enterprise Linux 8 include new intelligent management and monitoring capabilities via updates to Red Hat Insights; enhanced container tools; and a smoother user experience both for Linux experts and newcomers.

Data Management
Winner:
Commvault Hyperscale X
With its new HyperScale X appliance, Commvault delivers a simple, flexible data management offering for all workloads including containers, virtual machines and databases. HyperScale X is a scale-out appliance that enables numerous use cases, starting with its deployment as a storage appliance optimized for Commvault-focused workloads—particularly for Kubernetes containers. Importantly, HyperScale X provides new policy capabilities and integrations specific to Kubernetes—enabling Kubernetes containers to move between on-premises environments or between multiple clouds—while also offering disaster recovery and high availability.
Finalists:
BigID Data Intelligence Platform
The BigID Data Intelligence Platform combines “discovery-in-depth” capabilities (with more ways to discover and classify data); strong data coverage for all types of personal and sensitive data (both in data centers and the cloud, and at rest or in motion); and an extensible app framework that enables privacy, security and governance.
HYCU Protégé
HYCU Protégé provides simplified data management across both the public cloud and on-premises data centers. The offering features one-click cross-cloud migration, as well as disaster recovery and consolidated management for on-premises environments (Nutanix and VMware) and public cloud (Microsoft Azure and Google Cloud).
Igneous DataFlow
Igneous DataFlow provides the ability to move data between any tier and any location, using a vendor-agnostic offereing that is integrated with a full range of cloud storage platforms. The offering is capable of coordinating complex, high-speed data migrations—such as local NAS to cloud-based NAS—without impacting production workflows.
Information Builders Omni-Gen
With its Omni-Gen platform, Information Builders rapidly delivers data integration, data quality and master data management—substantially reducing the lengths of project times. Omni-Gen facilitates efficient integration and mastering of data by enabling collaboration between master data management experts and other roles within the company about business domains such as customer, location and supplier.
Komprise Intelligent Data Management For Multi-Cloud
For managing data across different clouds, Komprise Intelligent Data Management For Multi-Cloud provides analytics and visibility across on-premises storage and the cloud—enabling data to be moved to the right place at the right time, without changing user workflows. The offering also reveals how data is growing and being used on public clouds, and forecasts cost savings based on data life-cycle policies.

Display-Collaboration/Signage
Winner:
Samsung Electronics America Pro TV
Bringing together high-resolution display quality with lengthy operating time and simplified setup, Samsung Electronics America’s Pro TV is optimal for the needs of small businesses. Along with offering a range of display sizes of between 43 and 75 inches, Samsung’s Pro TV also can be customized with content that’s controlled from a mobile device, using the Samsung Business TV app. The app enables easy setup for the display, which features UHD resolution and vibrant picture quality. And when it comes to operating time, Samsung’s Pro TV supports extended usage of up to 16 hours a day, seven days a week.
Finalists:
Sharp Electronics Windows Collaboration Display
Sharp Electronics’ Windows Collaboration Display is a 70-inch, 4K/UHD display that includes a built-in microphone and 4K camera, along with an “IoT sensor hub” to help with providing high-quality audio and video. The display comes equipped with Microsoft tools including Microsoft Teams, Microsoft 365 and Microsoft Azure Digital Twins, and is also Skype for Business- certified.
Tripp Lite Mobile Interactive Display
Tripp Lite’s Mobile Interactive Display (model DMCSTP65CBP) is a 65-inch, 4K touch-screen display that enables high-quality collaboration, presentation and communication. The display comes with a 1,080p webcam and microphone, while other features include a durable mobile stand, rechargeable lithium-ion battery and compatibility with major operating systems.

Display-Monitor
Winner: HP S430c Curved Ultrawide Monitor
For power users seeking to take their productivity to the next level, HP Inc. offers its S430c Curved Ultrawide Monitor, featuring a huge 43.4-inch FHD screen that provides enhanced usability and aesthetics with its curved design. A number of additional features offer further improvement to the user experience, including connectivity to a PC with a single USB-C to USB-C cable; the ability to use the monitor either as two displays (with drag-and-drop functionality between the two) or as a single unified display; HP’s Device Bridge feature, which enables multitasking between connected macOS and Windows devices simultaneously; and a pop-up webcam that supports Windows Hello facial recognition for login.
Finalist:
ViewSonic VG1655 Portable Monitor
ViewSonic VG1655 Portable Monitor is a highly mobile display meant to be used as a complementary screen for users such as business travelers and remote workers. The 15.6-inch FHD display weighs less than 2 pounds while measuring less than an inch thick, while the monitor can be connected using a single USB-C cable for video, audio, data and 60W of power.

Edge Infrastructure
Winner:
Scale Computing HE150
With its HE150, Scale Computing provides a fully functional hyperconverged infrastructure offering aimed at serving smaller workload requirements. The HE150 is a compact-size, all-flash, NVMe storage-based compute appliance that can provide improved availability and power efficiency compared with 1U server offerings in edge environments. Notably, Scale Computing is leveraging Intel NUC mini PCs for the HE150 instead of traditional 1U servers. Key features for MSPs include highly available virtual machines that can be created in minutes; no single point of failure; multisite management; and self-healing machine intelligence. The HE150 also works seamlessly with Scale Computing’s HC3 virtualization platform.
Finalists:
APC by Schneider Electric - 6U Wall Mount EcoStruxure Micro Data Center
The 6U Wall Mount EcoStruxure Micro Data Center from APC by Schneider Electric is an edge computing offering that delivers high resiliency with a compact footprint. The micro data enables deployment of server and networking equipment at the edge without taking up any floor space, as it only extends 14 inches off the wall. Advanced security options include camera monitoring, keylock doors and intrusion detection.
Eaton MiniRaQ
The Eaton MiniRaQ is a vertical wall-mount rack enclosure for edge IT and power management equipment that’s capable of safely mounting equipment up to 35 inches in length as well as supporting up to 400 pounds. The system features a compact footprint for fitting into confined spaces, and the MiniRaQ is also compatible with a variety of Eaton UPS systems.
HPE Aruba ESP
The HPE Aruba ESP (Edge Services Platform) provides a cloud-native approach for unifying, automating and protecting edge environments. Core components include AIOps, zero-trust network security and a unified infrastructure for campus, data center, branch and remote workers. The platform continuously analyzes data across domains, identifies anomalies and self-optimizes, while providing visibility and security for unknown devices on the network.
Vertiv Liebert PSI5
With the Liebert PSI5 Lithium-Ion UPS, Vertiv is offering a single-phase uninterruptible power supply with lithium-ion batteries for the first time. The use of lithium-ion enables extended runtime and reduced maintenance, and the system is available in a compact 2U rackmount/tower convertible configuration—all of which make the Liebert PSI5 an ideal option for edge deployments.
IT/Application Automation
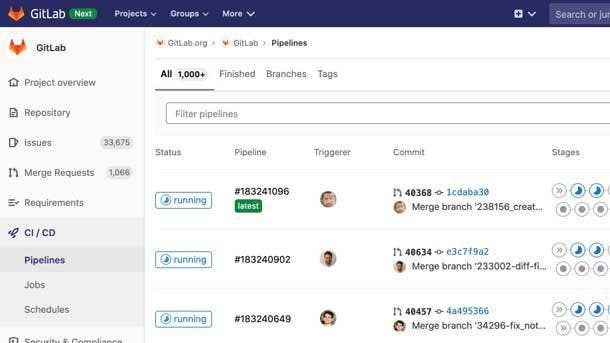
Winner: GitLab 13.0
Through providing a single application for the entirety of the DevOps life cycle, GitLab eliminates the need for third-party solutions and manual integration—dramatically reducing cycle time while lowering development costs. Earlier this year, GitLab rolled out its first formal channel program to enable partners to bring its DevOps platform to more customers while also complementing the platform with their own services, such as managed DevOps. For the GitLab 13.0 release, security and compliance updates include Responsible Disclosure (enabling authorized users to request Common Vulnerabilities and Exposures information from GitLab); Standalone Vulnerabilities (which rearchitects management of vulnerabilities); and security scanning (including through offering Static Application Security Testing for the .Net Framework).
Finalists:
Moogsoft Observability Cloud
The Moogsoft Observability Cloud applies artificial intelligence to IT operations data to bring automation to the incident management life cycle—providing IT Ops and DevOps teams with greater understanding and control of IT architecture, services and business applications. The platform automates the ingestion of data from complex toolstacks and correlates the data into actionable insight, enabling workflows to be improved and collaboration across teams to be automated.
Puppet 2019.8
With the 2019.8 release of the Puppet Enterprise continuous automation offering, enhancements include providing customers with access to the more than 6,000 modules available on the Puppet Forge repository. The modules can be used as building blocks to rapidly compose orchestration plans in the Puppet Enterprise console, enabling DevOps to quickly expand automation into more complex use cases.
Refactr Platform
The Refactr Platform enables cybersecurity teams to extend their automation capabilities beyond data ingestion and into adopting CI/CD (continuous integration or continuous delivery) practices, which are typically reserved for DevOps teams. The platform provides cybersecurity teams with capabilities to automate workflows such as meeting compliance requirements, conducting rapid incident response and configuring infrastructure and networks.
Robin Automation Platform
Targeted at 5G mobile operators and enterprises, the Robin Automation Platform provides a highly scalable offering to provisioning network capacity, automating service delivery and moving IT infrastructure toward a cloud-native architecture. The platform enables end-to-end automation for the deployment, scaling and life-cycle management of applications.

IT Infrastructure Monitoring
Winner: LogicMonitor
In a series of recent enhancements to its infrastructure monitoring platform for enterprises and MSPs, LogicMonitor has rolled out new AIOps capabilities to predict—and ultimately prevent—IT outages before they happen. Debuted last December, the AIOps early warning system received a major update in July that added support for rate of change and seasonality in its dynamic thresholds functionality. The update enables the LogicMonitor software to detect patterns and anomalies in performance (with the seasonality support) as well as detect anomalies within the rate that the metric values are changing at.
Finalists:
Cisco Data Center Assurance And Insights
Key capabilities of Cisco’s Data Center Assurance and Insights include prechange analysis, enabling an operator to verify the impact of changes before they are realized in the fabric; identification of potential security breaches ahead of time, allowing operators to take corrective measures to prevent vulnerabilities; and guaranteed reliability so that operators are notified of known issues that may affect the integrity of their network.
F5 Networks F5 Beacon
With F5 Beacon, F5 Networks provides a comprehensive view of applications across the enterprise using an easy-to-consume dashboard—with application models, health and performance metrics and actionable insight. As one core element, F5 Beacon ingests application telemetry data that is fused together from multiple, disparate integration sources.
New Relic One
With the recent update to New Relic One, the offering includes a telemetry data platform that provides a unified view of all telemetry data; full-stack observability, which consolidates all of New Relic’s monitoring products into an integrated platform; and applied intelligence that is delivered across New Relic One.
OpsRamp Platform
The OpsRamp IT operations management platform enables enterprise IT teams and MSps to get a better handle on their digital infrastructure through hybrid discovery and monitoring, event and incident management and remediation and automation—all powered by AIOps. The end result for IT is a unified view of infrastructure health for effectively maintaining business-critical services.
Sinefa Endpoint Agent
Sinefa’s Endpoint Agent software deploys on employee desktop and laptop PCs, automatically generating visibility via a SaaS web portal. The solution is aimed at IT teams that must support a major expansion of remote employees and call center workers, as well as MSPs seeking to build a monitoring as a service practice around supporting the new remote workforce.

Laptops
Winner: Dell Latitude 9510
Along with being a highly portable workhorse laptop, Dell’s Latitude 9510 stands out with a number of built-in AI capabilities. The notebook’s Intelligent Audio feature lets users configure their mic and speakers for the type of room they are in, while ExpressCharge learns how users use their PC and then adjusts policies to improve the battery life. Express Sign-In locks the notebook when users walk away and senses their proximity when they return—then automatically logs them in with Windows Hello facial recognition. On portability, the Latitude 9510 weighs just 3.3 pounds and sports a minimal-bezel design that makes it very compact for a 15-inch laptop.
Finalists:
Acer Chromebook C871
Acer’s Chromebook C871 includes a 12-inch display—with both touch screen and non-touch options available—and has a 3:2 aspect ratio for the display to give students more room for vertical viewing. The Chromebook C871 also meets MIL-STD-810G durability standards with features such as drop protection.
Dynabook Portégé X30L
Dynabook’s Portégé X30L stands out with a weight of just 1.92 pounds—which makes it the world’s lightest 13.3-inch notebook with 10th-generation Intel Core processors. The laptop supports up to an Intel Core i7-10710U processor and offers up to 14 hours of battery life.
HP Elite Dragonfly
HP’s Elite Dragonfly convertible features a fresh design paired with serious portability (with a starting weight of just 2.2 pounds) and battery life (up to 24.5 hours of battery life per charge). The design of the 13.3-inch notebook features a CNC-machined magnesium body and an iridescent “dragonfly blue” color.
Lenovo ThinkBook Plus
Part of Lenovo’s ThinkBook portfolio, which is aimed at small and midsize businesses, the ThinkBook Plus includes a unique 10.8-inch E Ink display on the top cover. The display can be used for taking notes or sketching with a digital stylus, as well as for getting emails and notifications.
Panasonic Toughbook FZ 55
Panasonic’s rugged Toughbook FZ 55 laptop offers a number of advances, including around battery life—with up to 40 hours available with an optional second battery. Meanwhile, the 14-inch laptop includes modular expansion packs that allow for a greater level of configurability for partners to meet the needs of end customers.

Mobile And IoT Management
Winner: Panasonic Productivity+
Panasonic recently debuted its Productivity+ suite of services, which can be leveraged by solution providers to help with serving the mobile computing needs of customers. As many organizations continue to run mission-critical applications on outdated platforms such as Windows CE and Windows Mobile, Productivity+ provides assistance with transitioning those crucial applications to Android—with capabilities that enable the rewriting of applications for Android. Other services that are part of Productivity+ include capabilities for configuring Android device settings and defining user access. Productivity+ provides crucial features to enable improved deployments of mobile devices in a variety of industries.
Finalists:
Addigy MDM Live
With MDM Live, Addigy delivers a mobile device management offering that enables IT administrators to keep track of every mobile device in their fleet in real time. IT admins receive instant visibility into mobile device inventory, procurement management and network security, while MDM Live provides alerts, monitoring and automated remediation needed for rapidly addressing issues.
SOTI Connect
SOTI Connect provides life-cycle management of IoT devices within an organization—including printers and limited access sensors—through a single point of control. The offering provides support for a variety of industrial and mobile printers and IoT-enabled sensors, delivering comprehensive management, automated monitoring and maintenance of an IoT-enabled device fleet.
Zebra FulfillmentEdge
Zebra’s FulfillmentEdge software augments and extends existing warehouse management systems by enabling dynamic workflows and routing mobile workers for picking, packing and put-away. FulfillmentEdge analyzes collected data and creates real-time workflows, which are then delivered as electronic tasks to mobile workers. The tasks contain visual directions showing the next pick location, with photos of the item, to ensure picking accuracy.
MSP Technology
Winner:
Liongard
With its platform for MSPs, Liongard empowers them with deep visibility into on-premises systems and applications, network devices and cloud services. The end result is faster on-boarding times and the ability to resolve customer issues more quickly. Key features of Liongard’s platform include automated documentation of the full customer environment; powerful reporting capabilities; automated alerts; and a central location for MSPs to view comprehensive system data. The platform also stands out by continually collecting data and offering historical timelines, allowing MSPs to turn back the clock to answer key questions about what took place in the past.
Finalists:
Acronis Cyber Protect Cloud
With Cyber Protect Cloud, Acronis integrates an array of tools for MSps into one central site—eliminating complexity and improving productivity and cyberprotection. The tools include backup, disaster recovery, advanced anti-malware and endpoint management solutions, and unifying them ultimately allows MSPs to make security a focal point of their offering to customers.
Axcient AirGap
Axcient’s AirGap helps MSPs to eliminate ransomware attacks through separating requests to delete data from the actual mechanics of data deletion. AirGap walls off data from all delete requests, places false positives in the system to deter repeat attempts and adds human controls to prevent accidental data loss.
Barracuda Message Bus
Barracuda Message Bus enables MSPs to integrate products with varying technologies such as SOAP and REST APIs; different location logic, including geographic sites versus server locations; and convert log files to alerts. MSPs can use the offering to simplify administration and integrate more quickly with security products.

Networking
Winner: SonicWall TZ570, TZ670 Series
Along with breaking new ground in the industry as the first firewalls in a desktop form factor with multi-Gigabit interfaces, SonicWall’s TZ570 and TZ670 Series next-generation firewalls bring an array of useful features and specs for enabling secure networks. Key capabilities include support for TLS 1.3 decryption and 5G; integrated support for SD-WAN; up to 10 ports and 256 GB of storage; optional PoE and Wi-Fi; and the ability to connect up to 1.5 million devices, representing a 900 percent increase. SonicWall’s TZ570 and TZ670 Series firewalls also feature simplified central management via a redesigned user interface on the included SonicOS 7.0 software.
Finalists:
CommScope Ruckus Analytics
CommScope recently unveiled Ruckus Analytics, a cloud subscription-based service built on a foundation of AI that offers network intelligence while simplifying service assurance for MSPs managing their customers’ environments. The service uses AI derived from Ruckus networking elements, including access points and switches, to classify issues based on severity.
Extreme Networks ExtremeCloud IQ
With its ExtremeCloud IQ application, Extreme Networks enables enhanced management of networks while delivering crucial intelligence and assurance. Key capabilities include full visibility into every user and device in a network, as well as unified policy management across devices and sites.
VMware NSX-T 3.0
VMware’s NSX-T 3.0 includes powerful offerings such as NSX Federation, which enables delivery of an operating model that is similar to cloud—for instance, by synchronizing policies and fault isolation zones across every location. That allows for containing network problems to just a single zone.
Zyxel Networks XS1930 Series
Zyxel Networks’ XS1930 Series switches provide multi-Gigabit performance, with port speeds from 100 Mbps to 10 Gbps over Ethernet. The series’ XS1930-12HP model can be used to support the demanding power requirements of Wi-Fi 6 access points, with the ability to deliver as much as 60W for each port.
Networking-SD-WAN
Winner:
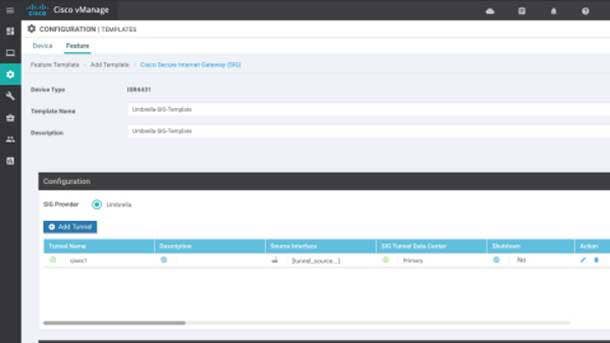
Cisco SASE
As Cisco continues building on its intent-based networking strategy, the company recently rolled out an offering that brings together cloud security and networking, enabling partners to move their customers toward a Secure Access Service Edge (SASE) architecture. The Cisco SASE offering features integration between Cisco’s flagship SD-WAN offering, powered by Viptela, and its cloud-based secure web gateway, Cisco Umbrella. The fully integrated SASE offering includes an SD-WAN dashboard that can be used to rapidly deploy Cisco Umbrella security across all sites and users. Partners can deliver protection against web attacks for thousands of customer sites within minutes, bringing cloud-native SD-WAN and security to workers whether they’re in the office or remote.
Finalists:
Aryaka SmartServices
With the SmartServices global managed SD-WAN platform, Aryaka offers features such as SmartManage for global orchestration and visibility; SmartConnect for connectivity that includes dedicated backbone, broadband internet and MPLS; SmartSecure for edge and cloud-based security; SmartOptimize for multisegment network and application optimization; SmartCloud for direct connectivity to the major cloud platforms; and SmartInsights for visibility, configuration management and SLA verification.
Barracuda CloudGen WAN
Barracuda CloudGen WAN enables use of the Microsoft Azure cloud platform and global network for their WAN as a global MPLS replacement—with speed, ease of use and comprehensive security all provided. CloudGen WAN is deployed as a SaaS service directly from the Azure Marketplace for as many regions as needed, and the service is administered in a central portal for all office locations and remote endpoints.
Fortinet Secure SD-WAN
Fortinet Secure SD-WAN is a networking and security offering that solves common application performance, visibility, cost and control challenges associated with multi-cloud deployments, through enabling SD-WAN across multiple clouds and regions. The offering enables a consistent network architecture leveraging SD-WAN capabilities between clouds, and empowers developers and enterprise IT to build a high-speed cloud-to-cloud network and security architecture—including more than 20 Gbps of IPsec performance.
Versa Secure SD-WAN
With Versa Secure SD-WAN, Versa Networks combines SD-WAN, security, scalable routing, multitenancy and analytics across branch offices, campuses, data centers and the cloud. The recent updates to the Versa Operating System include a simplified orchestration portal and enhanced security for work-from-home deployments.

Networking-Wireless
Winner:
CommScope Ruckus R750
CommScope’s Ruckus R750 access point is a high-performance offering for Wi-Fi 6 connectivity in dense environments. As one of the first access points to receive “Wi-Fi Certified 6” validation from the Wi-Fi Alliance, CommScope’s Ruckus R750 indoor access point provides a nearly 4X speed boost for devices compared with Wi-Fi 5. The dual-band access point is targeted at congested environments such as schools and hospitality veues and can manage up to 1,024 client connections at a time. Other key features include support for eight spatial streams (four each in 5GHz and 2.4GHz) and two wireless technologies in addition to Wi-Fi (Bluetooth Low Energy and Zigbee).
Finalists:
Cisco User Defined Networks
Targeted at shared wireless networks in multidwelling units, the Cisco User Defined Networks offering restricts traffic by creating a separate wireless network partition for each user and gives control to end users to manage their own devices through a mobile app.
Cradlepoint E3000 Series
With its E3000 Series, Cradlepoint is offering wireless edge routers for enterprise branch deployment that stand out by being optimized for 5G. Customers are enabled to deploy a wireless wide-area network using current LTE and Wi-Fi technology, with a smooth process for upgrading to 5G in the future.
WatchGuard AP225W
WatchGuard’s AP225W is a wall-plate access point designed to provide fast and secure Wi-Fi connectivity to organizations with high volumes of users at a single location. The AP225W features dual-concurrent 5GHz and 2.4GHz band radios and supports data rates up to 867 Mbps and 400 Mbps, respectively.
Zyxel WAX650S
The Zyxel WAX650S is a Wi-Fi 6 dual-radio access point intended for high-density SMB environments. The dual 4x4 MIMO access point provides a maximum data rate of 3,550 Mbps—2.4 Gbps in 5GHz and 1.15 Gbps in 2.4GHz—and can be remotely provisioned and managed using the Zyxel Nebula Cloud Management Platform.
Office Productivity Software
Winner:
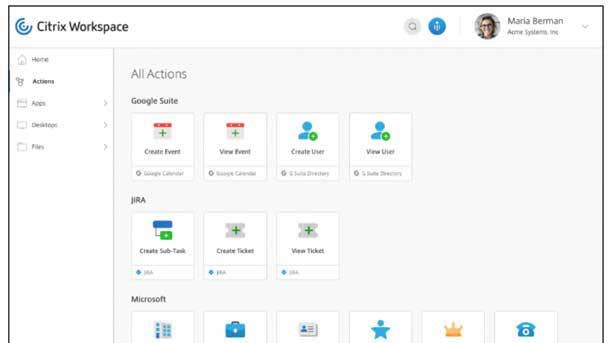
Citrix Workspace
With the aim of boosting employee engagement and productivity, Citrix Systems’ Workspace software enables workers to securely access applications wherever and however they need them. Recent enhancements to Citrix Workspace have included improved integrations through populating Workspace with “microapps”—integration with common cloud-based apps such as Salesforce, Concur, Microsoft applications and SAP. Using publicly available APIs for applications, the addition of microapps to Citrix Workspace enables employees to view information and take actions without needing to fully launch the application. By speeding up frequently performed tasks, microapps in Citrix Workspace allow for a more streamlined work routine.
Finalists:
Acumatica 2020R1
Acumatica 2020 R1 is a cloud ERP product that provides an integrated offering with accounting at the core. Integrated modules provide fixed asset tracking, deferred revenue, payroll, time and expenses and CRM, and more. Industry-specific editions include commerce, distribution, manufacturing, field service and construction.
Dropbox HelloSign
Dropbox HelloSign enables simplified and secure management of the eSignature process with the ability to set up documents for legally binding signatures through dragging and dropping appropriate fields; tracking of the document status with notifications; and safe storing of completed agreements in HelloSign or another cloud storage provider.
IGEL OS 11
IGEL OS is a Linux-based operating system that turns compatible devices into secure endpoints for connecting into virtualized environments, making the offering ideal for remote workers. Updates in IGEL OS 11.04 include optimizations for unified communications and collaboration apps, including enhanced support for Microsoft Teams, Zoom and Cisco WebEx.
Monday.com - Monday 2.0
Monday 2.0 from Monday.com is a “work operating system” that enables organizations to build custom workflow apps with a centralized platform for app creation, process management and project management. The offering provides platform features, or “work blocks,” that are used to build code-free workflow apps.
Power Management Technology
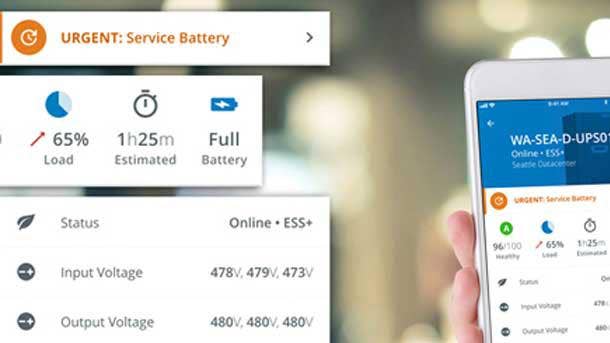
Winner:
Eaton PredictPulse
Eaton’s recent redesign of PredictPulse—its remote management service for power infrastructure—brings an improved user experience on mobile devices and the web, a new notification system and enhanced communications about device and location performance. Leveraging customer input, the rebuilt PredictPulse service offers a new mobile portal interface to better enable data center and IT managers to monitor power infrastructure health and respond to incidents while off-site. The newly added PulseScore feature, meanwhile, provides communications about the health of a customer’s uninterruptible power system overall. The additional features complement key PredictPulse capabilities such as providing analytics and recommendations for proactive management of power infrastructure.
Finalists:
APC by Schneider Electric Monitoring and Dispatch Services
With Monitoring and Dispatch Services, APC by Schneider Electric serves as a third party to manage the operations of distributed IT infrastructure. APC by Schneider Electric’s services include remote monitoring, troubleshooting and on-site remediation that is available as soon as the next business day.
CyberPower CP1500PFCLCD
CyberPower’s CP1500PFCLCD—a mini-tower sinewave UPS system—features a number of updates from past models. Those include the addition of a color LCD panel to quickly confirm alerts and status; a tilting screen for improved viewing when the UPS is placed in a lower location; and a USB-C charging port for accommodating portable devices.
Server Technology PRO3X
The PRO3X from Server Technology/Legrand is a hybrid rack PDU for powering data center applications of all sizes. Key features of the PRO3X include 2-in-1 High Density Outlet Technology (HDOT) Cx outlets, which standardize a single PDU for multiple applications thanks to the ability to act as a C13 or C19 outlet.
Vertiv Geist Combination Outlet C13 / C19
The Vertiv Geist Combination Outlet C13 / C19 is a 2-in-1 receptacle supporting C14 and C20 plug types in any outlet of the rack power distribution unit. This universal outlet allows for any mix of hardware power configurations, eliminating the need to preplan the number of outlets for each equipment type.

Print Technology
Winner: HP Workpath
HP Inc. is enabling partners to create apps that can improve business processes—and run on HP multifunction printers—with its cloud platform and developer ecosystem, HP Workpath. The apps are intended to help businesses streamline core workflows, and HP Workpath provides partners with ways to easily create new apps as well as install existing apps onto HP MFPs. Existing app capabilities include scanning documents and saving them into a shared folder in Microsoft Teams or Google Docs, as well as using Concur to scan receipts and submit expense reports. Meanwhile, using the cloud-based HP Command Center platform, partners can rapidly equip MFP devices for using HP Workpath apps.
Finalists:
Epson SureColor T5475
Epson’s SureColor T5475 is a compact wide-format wireless printer aimed at enhancing workgroup productivity. The printer is ideal for blueprints, line drawings and posters up to 36 inches, and can deliver A1/D-size prints in as little as 22 seconds. It’s also equipped with high-capacity 700 ml cartridges to provide more time between cartridge changes.
Lexmark Cloud Print Management
Lexmark Cloud Print Management enables partners to deliver a high level of optimization when it comes to print, eliminating the burden of printing infrastructure and manual on-site management. Partners also benefit from simplified installation and support for the offering across customers of all sizes.
Processors
Winner:
AMD EPYC, Second Generation
With the recent expansion of AMD’s second-generation EPYC processor family, the chipmaker is delivering massive performance for key markets including hyperconverged infrastructure, high-performance computing and relational databases. AMD’s expanded second-generation, 7-nanometer EPYC lineup adds three processors that feature boost frequencies of up to 3.9GHz and L3 caches reaching 256 MB. Previously, the highest boost frequency achieved by an EPYC Rome processor was 3.4GHz. The three new processors—the 24-core EPYC 7F72, the 16-core EPYC 7F52 and eight-core EPYC 7F32—are being supported by server platforms from Dell EMC, Hewlett Packard Enterprise and Supermicro. Ultimately, the expanded second-gen EPYC lineup provides significantly improved per-core performance for some of the highest-demand enterprise workloads.
Finalists:
Intel 10th Gen Core vPro
Intel’s recent launch of new 10th-generation vPro processors for laptops and desktop PCs has brought new silicon-level security capabilities for businesses. The processors include the first chips in the vPro lineup to require OEMs to enable Intel Hardware Shield, which protects the system underneath the operating system at the BIOS level. A key feature recently added to Intel Hardware Shield with vPro is an advanced threat detection capability that utilizes GPU resources, lowering the strain on the CPU when security programs are running. Meanwhile, the new processors come with support for Intel’s integrated Wi-Fi 6 (Gig+) technology, which offers new WPA3 security features for authentication and encryption while enabling four times greater capacity with Wi-Fi 6 access points.
Nvidia A100 Tensor Core GPU
Nvidia’s recently launched data center GPU, the A100, aims to revolutionize artificial intelligence by unifying training and inference into one architecture that vastly outperforms predecessor GPUs. For instance, the A100 can perform single-precision floating point math (FP32) for training workloads and eight-bit integer math (INT8) for inference 20 times faster than the V100 GPU that came out in 2017. The A100 also uses Nvidia’s third-generation Tensor Cores that come with a new TF32 For AI format, which enables single-precision floating point acceleration by compressing the number of bits needed to complete math equations.
Robotic Process Automation
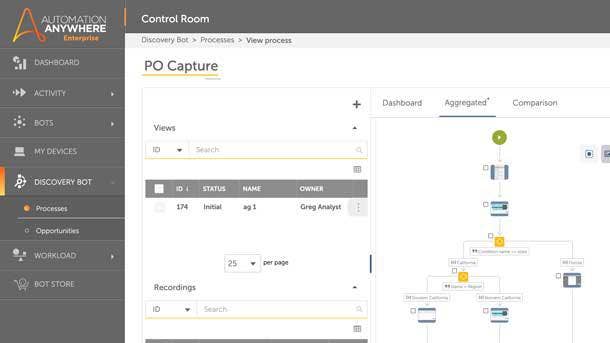
Winner:
Automation Anywhere Enterprise A2019
The Enterprise A2019 platform from Automation Anywhere brings robotic process automation (RPA) to customers in any environment—on-premises, public cloud or hybrid—while delivering a wide array of new features for enhanced and simplified RPA. The entirely web-based platform makes it easier to create bots thanks to an improved UX, which offers capabilities such as cross-platform scripting and in-line scripting. Users can also now leverage AI solutions—including natural language processing and computer vision—from third parties, while integrating the solutions via drag and drop into automation workflows. Plus, the Attended Automation 2.0 offering enables enhanced orchestration of work between humans and bots, accelerating and simplifying the automation of front-office tasks.
Finalists:
Kryon Full Cycle Automation-as-a-Service
Kryon’s Full-Cycle Automation-as-a-Service is a fully managed automation service that runs 24/7 in a private cloud or in a technology partner’s cloud infrastructure. Once deployed, the offering can create production-ready processes from scratch—tailored to each customer’s specifications—or organizations can also build their own automation processes by leveraging extensive software libraries.
UiPath Hyperautomation Platform
UiPath’s Hyperautomation Platform combines the company’s RPA offering with a full suite of cloud capabilities including process mining, analytics and AI. The platform provides the ability to use AI to analyze back-end systems and application logs; process document data more quickly; gain greater control and flexibility over attended bots via a new user interface; and centralize their automation initiatives.

Security-Cloud
Winner: Cisco Umbrella
With Cisco Umbrella, the company’s cloud-based security platform, users are protected from malicious internet destinations whether they’re inside or outside their company’s network. Cisco Umbrella accomplishes this by combining offerings cutting across secure web gateway, DNS-layer security, cloud-delivered firewall and Cloud Access Security Broker (CASB). Recent enhancements to Cisco Umbrella include integration with the company’s flagship SD-WAN offering, powered by Viptela, which helps enable businesses to move toward a Secure Access Service Edge architecture. Meanwhile, during the initial months of the COVID-19 pandemic, Cisco made its Umbrella offering available to new customers via a free license, while existing customers were enabled to exceed their user limit to support more remote employees.
Finalists:
Arctic Wolf Managed Cloud Monitoring
With Managed Cloud Monitoring, Arctic Wolf offers detection of cloud vulnerabilities, misconfigurations and attacks across all major cloud platforms as they occur. The offering includes unlimited access to the company’s Concierge Security Team for guidance around implementation and ongoing monitoring.
Bitglass Total Cloud Security Platform
Bitglass provides enablement for Secure Access Service Edge deployments with its Total Cloud Security Platform, integrating capabilities such as multimode CASB for comprehensive protection across any cloud or device; the SmartEdge secure web gateway, which decrypts and inspects traffic directly on user devices; and zero-trust network access that eliminates the necessity of VPN.
Forcepoint Cloud Security Gateway
For its Cloud Security Gateway—which combines secure web gateway with data-loss prevention and CASB—Forcepoint unifies policy enforcement via the centrally managed cloud service, while simplifying cloud security by providing the offering as a single SKU.
Guardicore Centra Version 5
Version 5 of Guardicore Centra brings protection for cloud-native applications, which includes Platform-as-a-Service and serverless computing. That provides control and visualizations for cloud-native apps from the same platform that secures apps running on virtual servers, bare-metal systems, Infrastructure-as-a-Service and containers.
McAfee MVision Cloud for Container Security
With MVision Cloud for Container Security, McAfee provides capabilities for comprehensively securing container workloads. Those include Cloud Security Posture Management (integrating configuration audit checks for containerized workloads); container vulnerability assessments (to identify vulnerabilities and warn developers of container weaknesses); and protection for containers at runtime (to ensure the integrity of core files and services).
Security-Data
Winner:
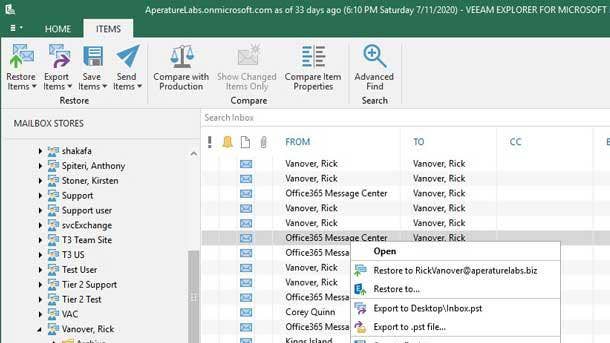
Veeam Backup For Microsoft Office 365 v4
While Microsoft provides resilient infrastructure for Office 365, customers are responsible for protecting the critical data that sits on top of it. Veeam enables partners and customers to do just that with its Backup for Microsoft Office 365 offering. With the version 4 update, key enhancements include an improved way to keep Office 365 data in Microsoft’s Azure cloud through direct integration with Azure Blob Storage. Also added in v4 are performance upgrades for SharePoint and OneDrive for Business backups; file-level recovery of Veeam backups and native snapshots; and capabilities to restore to any environment that’s supported by Veeam, including on-premises data centers.
Finalists:
Concentric Semantic Intelligence
Using natural language processing, the Concentric Semantic Intelligence offering enables security teams to detect risks and then remediate threats including incorrectly classified documents and inappropriate third-party access. The SaaS platform is agentless and does not require up-front development of rules or policies.
Datanchor Platform
Leveraging unique encryption methodology—which uses 256-bit AES to directly embed boundaries into data—the Datanchor Platform enables true zero-trust data security. Users are enabled to continue using their existing IT systems while safely supporting distributed workforces.
Fortanix Self Defending Key Management Service
With its Self-Defending Key Management Service, Fortanix offers a unified management approach covering encryption, keys, secrets and tokenization. The service, which spans multi-cloud infrastructures, provides cryptographic operations and life-cycle management such as key generation and key rotation.
McAfee Unified Cloud Edge
With features such as a single policy definition rule engine, McAfee’s Unified Cloud Edge makes it possible for organizations to define a single data protection or threat prevention policy, and have the rules applied consistently across the device, the network and the cloud.

Security-Email/Web
Winner:
Zix AppRiver Secure Modern Workplace
Zix has combined the security and compliance offering from its 2019 acquisition of AppRiver with its own to create a single platform that safeguards digital communication tools. The Zix AppRiver Secure Modern Workplace platform is a layer that wraps around Microsoft 365, offering detection and remediation of advanced email threats, modern data privacy and archiving for improved compliance and secure collaboration for employees. Key capabilities include monitoring for compromised email accounts on a continuous basis and centralized management of customer subscriptions. Secure Modern Workplace from Zix AppRiver ultimately enables customers to confidently migrate to the cloud, minimize business risk and accelerate their transformation efforts.
Finalists:
Cisco Cloud Mailbox Defense
Cisco’s Cloud Mailbox Defense offers a simplified method for deploying security for Office 365, ideal for organizations with smaller security and IT staffs. The offering leverages the Cisco Talos threat intelligence team to add an additional layer of security around blocking URLs and threat files.
CymaticONE with VADR
With its CymaticONE with VADR offering, Cymatic brings together client-side web application firewall defenses with a proprietary VADR (vulnerability, awareness, detection and response) engine. The result is delivery of continuous, real-time intelligence across locations, devices and users.
Mimecast Brand Exploit Protect
To halt impersonation of web and email domains, Mimecast Brand Exploit Protect offers detection and takedown services for malicious web sites. The offering uses machine learning and broad-based web searching to identify the brand exploits, then quickly remediates the exploits with its automated takedown service.
Skout Cybersecurity Work from Home Bundle
With its Work from Home Bundle, SkutT Cybersecurity combines email protection and Office 365 security monitoring with endpoint protection—integrated into a single dashboard and backed by the company’s 24-hour a day, seven-day-a-week Security Operations Center.
Veracode Security Labs
With its Veracode Security Labs code training platform, Veracode helps developers to enhance their secure coding skills using an interactive approach. The platform provides instruction on software vulnerabilities via editable live code and connectivity to real, container-based web apps.
Security-Endpoint
Winner:
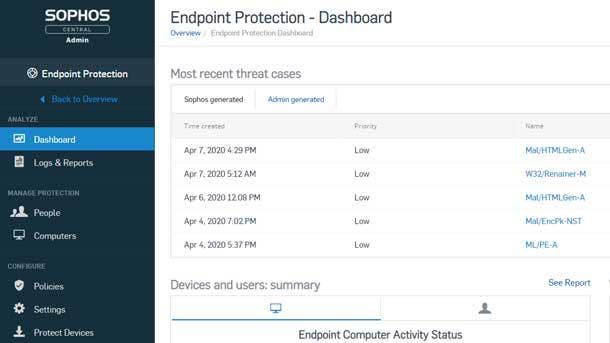
Sophos Intercept X
With a focus on helping security and IT teams to rapidly respond to endpoint threats, Sophos recently debuted a major upgrade to its Intercept X offering—including an update of the company’s Endpoint Detection and Response solution within several new versions of Intercept X. The updated EDR offering includes new capabilities such as Live Discover (for pinpointing activity and answering threat hunting questions) and Live Response (which enables remote response to endpoints via a command line interface). Separately, Sophos recently launched protection capabilities for Chrome OS users against unsuitable and malicious web content, with its rebranded Intercept X for Mobile offering.
Finalists:
Cybereason Defense Platform
Bringing together prevention, detection and response within a single lightweight agent, the Cybereason Defense Platform provides both signature and signature-less defense against malware. The platform thus prevents threats that are both known and unknown, while also using techniques such as deception to quash ransomware.
Malwarebytes Endpoint Detection And Response
Key capabilities of Malwarebytes’ Endpoint Detection and Response offering include guided UI (providing guided workflows and intuitive controls to enable efficient administration); threat activity replay (charting the spread of infection and analyzing outcomes for response and remediation outcomes); and a centralized partner dashboard (offering multitenant management and guided on-boarding).
McAfee MVision EDR
For its MVision EDR solution, McAfee recently launched new features including Automated AI-Guided Investigations, which offer improved guidance of customer investigations using internally generated machine learning and threat intelligence, and Advanced Analytics, which identify and prioritize suspicious behavior from contextually rich endpoint data.
Tanium as a Service
A “zero-infrastructure” endpoint security platform, Tanium as a Service leverages the company’s unique architecture for optimized remote management and securing of devices. The cloud-hosted and cloud-delivered offering brings intelligence to edge endpoints while combining capabilities around management, detection and response.
VMware Carbon Black Cloud
Aimed at providing consolidated and cloud-native endpoint protection, the VMware Carbon Black Cloud combines multiple powerful endpoint security features into a single, lightweight agent that is complemented by a console that is easy to operate.

Security-Identity And Access Management
Winner:
Okta Platform Services
Identity security firm Okta recently introduced its Okta Platform Services offering featuring a set of technologies at the core of its Okta Identity Cloud. The technologies that make up the offering include Okta Identity Engine, which provides authentication, authorization and registration flows that are customized and are context-based; Okta Directories, which runs the Okta Universal Directory and User Management, boosting both scalability and flexibility; Okta Integrations, which delivers access to anyone to build on top of Okta; and Okta Insights, with aggregation and analysis capabilities for Okta data, which are disseminated across key technologies.
Finalists:
Centrify Privileged Access Service 20.3
With the Centrify Privileged Access Service 20.3 release, key features include client-based password reconciliation, which forms a bonded trust with the password vault to ensure passwords are in sync; hyper-scalable privileged access service, which brings the availability and scalability of the cloud to an on-premises deployment; and delegated machine credentials, which inserts privileged access management into the DevOps pipeline.
Cisco Duo Device Health Application
The launch of the Duo Device Health Application provides the IT admin with deeper device context—in addition to other contextual factors such as user, network, location and application—to enforce granular, adaptive access policies. Meanwhile, the lightweight application performs health checks at the application level at the time of authentication, mitigating the risk of breach.
CyberArk Privileged Access Security Solution
Recent enhancements to CyberArk’s Privileged Access Security Solution incorporated multifactor authentication across the entire solution, delivering an AI-powered authentication experience that is risk-aware, intelligent and passwordless. CyberArk also introduced a broad set of just-in-time use cases to enable least privilege—regardless of user type, target system or environment—so that users only have the appropriate level of access for the time needed.
ForgeRock Identity Platform
With recent updates, ForgeRock expanded its passwordless authentication capabilities to include a username-less experience while simplifying the authentication process with an intelligent access tree framework—delivering user journeys out of the box with a drag-and-drop interface to fit a comprehensive set of business needs.
Kaseya - Passly by ID Agent
Passly, from Kaseya-owned ID Agent, combines multifactor authentication, single sign-on and password management—along with proprietary Dark Web monitoring, which can detect in real time if user credentials have been compromised and are for sale on the Dark Web. Passly ensures that employees have the right access to the right resources, from only approved devices and locations.

Security-Internet of Things
Winner:
WatchGuard Firebox T35-R
With its Firebox T35-R network security appliance, WatchGuard Technologies brings protection against threats such as malware and intrusions even in harsh environments located far beyond the data center—with features that provide ruggedization and strong performance. Main features include an IP64-rated industrial enclosure, delivering protection against splashes, dust and temperatures ranging from -40 degrees to 60 degrees Celsius; DC Power, with the ability to operate on 12v to 48v DC power; simplified, manageable and reliable site-to-site VPN connectivity; and enablement for key WatchGuard security offerings (without reduced network speeds) such as APT Blocker, DNSWatch, Threat Detection and Response, Gateway AntiVirus and Intrusion Prevention Service.
Finalists:
ExtraHop Reveal(x) 360
ExtraHop Reveal(x) 360 offers network detection and response for cloud-native security across edge IoT devices, data centers and cloud in a single solution. ExtraHop sensors deployed in locations including remote sites provide decryption and processing of network data, extracting records and de-identified metadata.
Forescout eyeSegment
Driven by the need to secure critical applications, mitigate increased exposure to IoT devices and limit the impact of threats across flat networks, Forescout eyeSegment enables organizations to accelerate network segmentation with a scalable approach. The offering provides rapid designing, planning and deployment of dynamic segmentation across the extended enterprise.
Microsoft - CyberX for Azure Security Center for IoT
CyberX’s API-level integration this year with Microsoft Azure Security Center for IoT enables clients to gain a unified view of security across all their managed and unmanaged IoT devices within Azure environments. The combination of CyberX’s agentless security platform and Azure Security Center for IoT provides comprehensive IoT device protection and zero-trust security, for battling threats to targets such as enterprise IoT and industrial IoT systems.

Security-Managed Detection And Response
Winner:
BitDefender Managed Detection and Response
BitDefender recently made its Managed Detection and Response offering available to MSP partners, bringing together Bitdefender’s detection and prevention engines with the company’s 24x7 security operation in Texas as a pairing that can be leveraged by MSPs. The offering provides network traffic analysis, endpoint protection and security analytics along with threat hunting from experienced analysts. Specific capabilities include a Human Risk Analytics module, which evaluates and reports on the risk that is associated with weak passwords, misconfiguration and employees; high-risk target-monitoring services, delivering protection from threats such as whale phishing (a phishing attack targeting prominent individuals) and business email compromise for key individuals such as executives; and dark web monitoring to uncover stolen customer data and detection of previous breaches.
Finalists:
Blackpoint Cyber SNAP Defense
Blackpoint Cyber’s SNAP Defense is a 24/7 Security Operations Center that offers real-time threat hunting, breach detection and the ability to take action and stop threats with a full response rather than just an alert. SNAP Defense detects hacker activity in the network and infrastructure and the SOC responds by disabling the network interface on the infected host.
BlueVoyant Managed Detection and Response for Microsoft Defender
BlueVoyant’s Managed Detection and Response integrates frontline expertise and comprehensive threat data analytics with Microsoft Defender Advanced Threat Protection, ultimately providing customized threat response and remediation in real time. BlueVoyant MDR helps Microsoft Defender ATP customers to defend against attacks that bypass preventative controls.
Open Systems Managed Detection and Response
Open Systems’ cloud-native Managed Detection and Response combines 24/7 monitoring, AI automation and the expertise of the company’s security engineers. The service eliminates the need for enterprises to add additional security engineers or to build and staff their own SOCs.
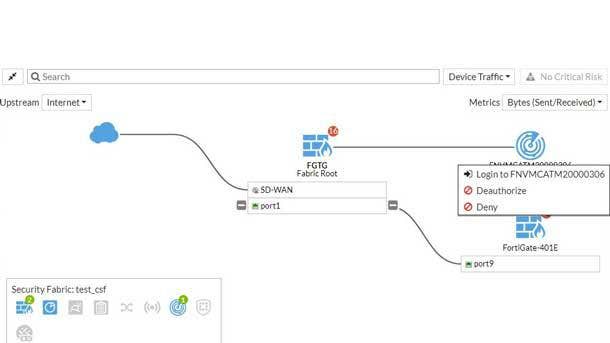
Security-Network
Winner:
Fortinet FortiOS 6.4
Fortinet debuted more than 350 new features on its FortiOS 6.4 operating system, including the addition of FortiNAC (Network Access Control) to the company’s topology map, making it easier to discover all of the IoT devices and endpoints within the Fortinet Security Fabric, as well as gain access to those systems using API technology. FortiNAC can now integrate with every single switch vendor, access point vendor and firewall vendor while providing powerful visibility. Meanwhile, Fortinet rolled out SD-WAN enhancements around application performance criteria, a new orchestration system inside FortiManager, and more analytics, reporting and monitoring inside FortiOS as part of the 6.4 release.
Finalists:
FireMon Automation
FireMon Automation is a network security policy automation platform, featuring a compute engine that can enable intent-based automation in order to fast track changes and ensure policy compliance. When the underlying network and segmentation changes, the Continuous Adaptive Enforcement computes and propagates the necessary policy changes in real time—increasing agility while eliminating manual effort and misconfiguration risk.
Infoblox NIOS 8.5
Infoblox NIOS 8.5 helps customers bridge to cloud network services to deliver enterprise-grade DDI (DNS, DHCP and IP address management) services across hybrid environments. The offering also unites data from BloxOne DDI, a cloud managed DDI offering for remote locations, and NIOS into a central location for complete visibility.
SonicWall Network Security Services Platform 15700
The SonicWall Network Security Services Platform 15700 delivers multiple high-speed interfaces, high-port density and threat protection at high throughput. Its multi-instance architecture supports multiple firewalls on a single appliance with dedicated resources, enabling administrators to run different software versions and configurations without the typical constraints of multitenancy architectures.
WatchGuard Firebox T80
WatchGuard’s new Firebox T80 is a high-performing tabletop appliance that offers optional port expansion modules for integrated fiber connectivity, so midmarket organizations and the MSPs that support them can adapt as connectivity needs change. The tool enables administering and enforcing of policy across extended networks, allowing organizations to bring full unified threat management to small and midsize environments.
Webroot DNS Protection
The Webroot DNS Protection is a filtering service that delivers a secured Internet connection to businesses, with capabilities to fully leverage DNS over HTTPS and its associated privacy benefits. The offering natively processes the encrypted Internet requests that use HTTPS to securely convey DNS requests to Webroot resolvers—preventing eavesdropping, manipulation or exploitation of the data.

Security-Risk Assessment And Management
Winner:
FireEye Mandiant Security Validation
With the Security Validation offering from FireEye’s Mandiant unit, the effectiveness of a customer’s security programs can be accurately measured on a daily basis—revealing a true picture of the customer’s security management technology. The Security Validation offering uses security instrumentation technology combined with threat intelligence and incident response data from the front lines. The result is that security teams are enabled to safely emulate real-world cyberattacks, delivering visibility into the performance of their security tools in protecting against a variety of attack behaviors. Customers can thus determine which improvements to invest in first on their cyberdefenses, as well as how to effectively—and quantifiably—communicate about their security risk.
Finalists:
AttackIQ Security Optimization Platform
The AttackIQ Security Optimization Platform offers continuous security control validation and enables security leaders to move to a strategic security program that delivers improved effectiveness and efficiency. The platform also enables risk and security practitioners to continuously assess and improve critical security controls within their production environment.
BitSight Attack Surface Analytics
BitSight Attack Surface Analytics enables organizations to continuously discover the assets, applications and devices that make up their digital footprint; assess current risk exposure; and take action to reduce risk. The solution ultimately provides a comprehensive view of an organization’s assets and risk.
CyberGRX Control Framework Mapping
CyberGRX Control Framework Mapping offers a vendor risk module that can take standard inputs and then deliver custom results. The platform enables mapping of organizations’ customized controls or standard framework to a CyberGRX vendor risk assessment—delivering a comprehensive view of vendor risk.
McAfee Total Protection For Data Loss Prevention
Key capabilities in McAfee’s Total Protection For Data Loss Prevention offering include device-to-cloud DLP, allowing admins to rapidly connect and synchronize on-premises DLP and cloud DLP policies; capture technology that aids forensic analysis of data loss events and provides visibility into how data is being used; and flexible end-user classification, which alleviates administrative burden and increases end-user data protection awareness.
SecurityScorecard Atlas
SecurityScorecard Atlas is a centralized platform that leverages machine learning to automate the cybersecurity questionnaire exchange process for senders and receivers, making it faster and more accurate. Atlas instantly maps cybersecurity ratings data to individual responses, providing a 360-degree view of risk.
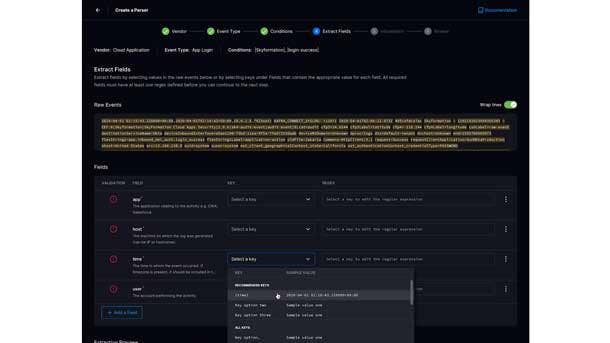
Security-SIEM/Security Analytics
Winner:
Exabeam Cloud Platform
In the security information and event management (SIEM) space, the new Exabeam Cloud Platform stands out through enabling continual improvement of the security posture within a security team. The Exabeam Cloud Platform accomplishes this by accelerating the way that teams provision and consume new content, apps and tools within security management. For security leaders, the Exabeam Cloud Platform can also speed up the implementation of new use cases in security, enabling quicker detection, investigation and response in the event of an attack. Key capabilities of the platform include user and entity behavior analytics, integration with 250 products, data graphing and cloud storage.
Finalists:
Devo Security Operations
Devo Security Operations scales the effectiveness of security analysts by bringing together auto enrichment capabilities, collaborations in threat intelligence communities and a central evidence locker—along with a workflow for analysts that is highly streamlined. The offering ultimately serves to amplify analyst knowledge, significantly reducing the time between detection and response.
Netsurion EventTracker v9.2
For its cloud-based EventTracker managed security service and threat protection platform, Netsurion brings together SIEM with User and Entity Behavior Analytics, AI and machine learning capabilities, compliance support and a 24/7 Security Operations Center. Netsurion combines artificial and human intelligence for a cohesive, cost-effective approach to threat detection.
Perch Security - Perch SIEM
Perch Security offers a co-managed threat detection and response platform, with SIEM and a 24/7 Security Operations Center based in the U.S.—enabling MSPs to add affordable managed threat detection and SIEM to their offering with quick setup, multitenancy and a full suite of integrations.
Securonix SearchMore
With SearchMore, Securonix augments the ability of security operations teams to proactively detect and respond to threats that bypass preventative and detective controls. SearchMore delivers community-driven threat hunting and provides the ability to search on real-time streaming data, as well as long-term data.
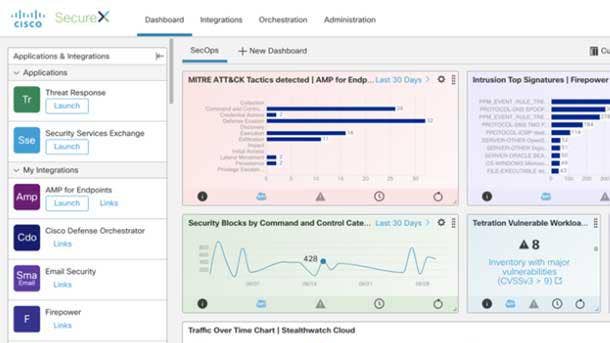
Security-Threat Intelligence/Incident Response
Winner:
Cisco SecureX
With its recently launched SecureX platform, Cisco delivers enhanced security visibility using powerful analytics and automation—accelerating threat detection and response. The cloud-native platform enables broad visibility of security environments at a customer, while deploying analytics to improve the detection of policy violations and unknown threats. The offering also helps to make operations more efficient through the automation of typical security workflows, such as threat investigation and remediation. The Cisco SecureX platform has the capability to analyze data and events from more than 150 million endpoints—along with traffic from networking infrastructure, private data centers and the public cloud—to rapidly identify the targets of cyberattacks, ultimately enabling remediation measures.
Finalists:
Flashpoint Compromised Credentials Monitoring
Flashpoint’s Compromised Credentials Monitoring offering provides advanced monitoring for exposure of compromised credentials. The offering uses technology that rapidly collects and processes data and credentials and then enables organizations to access the most up-to-date breach data and receive notifications as soon as compromised credentials have been identified.
Fortinet FortiAI
Fortinet’s FortiAI on-premises appliance leverages self-learning deep neural networks to accelerate threat remediation. Key capabilities include a virtual security analyst that embeds advanced cybersecurity AI—developed by Fortinet’s FortiGuard Labs—directly into an organization’s network to deliver rapid detection of threats.
Sophos Managed Threat Response
Sophos Managed Threat Response integrates with the company’s protection capabilities to ensure security teams end up dealing with the most important alerts. The standard offering provides detection and response capabilities, while an advanced offering includes asset discovery and a dedicated threat response lead—as well as connectors to all the threat data coming from locations other than the endpoint.
Tenable.ot 3.7
Tenable.ot 3.7 identifies and prioritizes threats with capabilities such as 360-degree visibility into an organization’s attack surface; threat detection and mitigation via identifying policy violations, detecting anomalous behaviors and tracking signatures for potential high-risk events; and adaptive assessment that provides insight and situational awareness about infrastructure systems.
Watchguard Threat Detection and Response
WatchGuard Threat Detection and Response is a collection of advanced malware defense tools that correlate threat indicators from Firebox appliances and endpoint Host Sensors to stop known, unknown and evasive threats. One key component, ThreatSync, continuously collects and correlates threat event data, then analyzes it against threat intelligence feeds and assigns a rank based on threat severity.
Servers
Winner:
HPE ProLiant MicroServer Gen10 Plus
Hewlett Packard Enterprise recently introduced its newest MicroServer—the HPE ProLiant MicroServer Gen10 Plus—designed to meet the needs of small businesses and the solution providers who serve them. With a size similar to a textbook and a weight of just 10 pounds, the system is about one-third of the size of existing server offerings in the market and yet still manages to offer twice the performance of its predecessor server. The system can be provisioned with powerful Intel Xeon E processors, or with less expensive Pentium chips, and includes HPE’s silicon root of trust technology that protects the system down to the firmware. Meanwhile, at the request of channel partners, the ProLiant MicroServer Gen10 Plus comes equipped with Integrated Lights Out (iLO) technology that for the first time allows partners to monetize associated remote management services.
Finalists:
Bamboo Systems B1000N Series
The recently launched B1000N Series uses Bamboo Systems’ new system architecture, Bamboo PANDA (Parallel Arm Node Designed Architecture). PANDA-based servers such as the B1000N Series leverage methodologies that power modern microservices-based workloads, in order to minimize energy consumption while also delivering impressive density for high-throughput computing.
MemVerge Memory Machine
Targeted for data-intensive applications, the MemVerge Memory Machine combines persistent memory with “big memory” software. The Memory Machine software virtualizes DRAM and persistent memory, then provides access to persistent memory without changes to applications; makes persistent memory run at least as fast as DRAM; and introduces memory data services such as snapshots, replication and instant recovery.
PhoenixNAP FlexServers
With FlexServers, IaaS provider PhoenixNAP delivers a dedicated server offering that allows for vertical scaling of second-gen Intel Xeon Scalable processors to varying performance levels with one reboot. Because no hardware or software changes are required to adjust the CPU configuration, the offering enables both strong performance and cost efficiency.
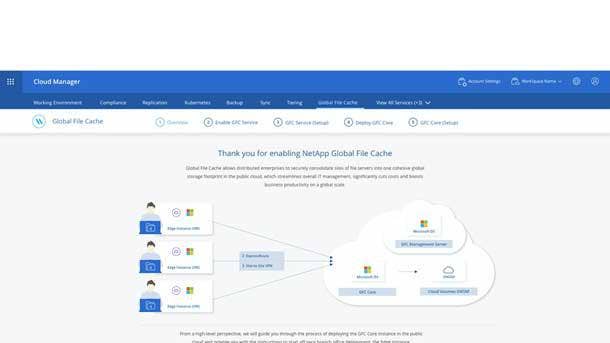
Storage-Cloud
Winner:
NetApp Global File Cache
The NetApp Global File Cache enables the consolidation of an organization’s numerous distributed file servers into a single, centralized location in the cloud. The data can then be managed and made available to users from that central location—streamlining the organization’s infrastructure, reducing cyberthreats (through shrinking potential attack vectors) and enabling a major reduction in cost. Key differentiators for NetApp’s Global File Cache include the use of technology layers such as global namespace representation and intelligent caching to provide strong performance to all users, even those in distant locations, avoiding the need for replicating and synchronizing data based on a central copy.
Finalists:
Panzura CloudFS 8
With the eighth-generation release of Panzura’s global cloud file system, Panzura CloudFS 8 adds cloud mirroring, allowing companies to simultaneously write data to two separate cloud object stores, doubling cloud availability. In addition, Panzura Mobile now provides enterprise file sync and share that enables secure sharing from the live file system, negating the need to replicate data.
Qumulo Shift for Amazon S3
Qumulo Shift for Amazon S3 is a native cloud service that enables organizations to fully leverage their unstructured data. Qumulo Shift moves file data from any Qumulo on-premises or public cloud file system into Amazon S3. The offering also transforms file data to object in an open format, making it accessible to applications and services designed for Amazon S3.
Wasabi Reserved Capacity Storage
Cloud storage provider Wasabi provides a hot storage offering that is about one-fifth the price of Amazon S3 storage, but faster. The company’s Reserved Capacity Storage pricing model lets customers purchase a reserved amount of cloud storage for a fixed price for one, three or five years.

Storage-Enterprise
Winner:
HPE Primera
With a recent update to its Primera storage system, Hewlett Packard Enterprise has beefed up the embedded InfoSight AI capabilities of the system so that it can now take dynamic action to automatically resolve storage management issues. HPE Primera, which guarantees customers 100 percent uptime, has gone beyond predictive analytics to take direct actions that optimize resource utilization, dramatically improving storage performance for customers. Prior to the update, storage administrators would have to act on the AI-based recommendations of the system. The recent Primera enhancements are enabling new levels of agility for customers, who can now spend less time managing and tuning mission-critical storage infrastructure.
Finalists:
Dell EMC PowerScale
Dell Technologies’ recently launched PowerScale storage line enables channel partners to attack the edge through native public cloud integrations; software that can tag, track, analyze and report on unstructured data; and a 1U platform capable of scaling from 11 TB to 60 PB of raw capacity.
IBM FlashSystem 9200
IBM’s FlashSystem 9200 offers three to four times the performance and 17 times the rack density of the company’s FlashSystem A9000 line—but at a price that is 40 percent to 60 percent less expensive, depending on configuration.
Infinidat InfiniBox
Infinidat InfiniBox provides petabytes of capacity with 100 percent data availability, along with certified integration with leading applications. The company also is providing capacity on-demand for InfiniBox—with cloud-like elastic pricing that enables 3X to 5X more capacity than paid for, and growth immediately when needed.
Synology SA3200D
Synology’s SA3200DSA3200D is an active-passive dual controller storage unit that’s targeted for uses including high-availability file storage and sync and disaster recovery. The system features 12 bays for configurable RAID storage along with whole system redundancy.
Vast Data Universal Storage Version 3
With Version 3 of its Universal Storage architecture, Vast Data has rolled out more than 20 new features including support for Windows and MacOS applications, cloud data replication and native encryption. The updates allow enterprises to combine all-flash performance with archive economics and scale.
Storage-Midrange
Winner:
Dell EMC PowerStore
With its new midrange all-flash PowerStore offering, Dell EMC is meeting the challenges of continually expanding workloads using a unique scale-up, scale-out architecture that’s based on container technology. Featuring built-in machine learning and automation, PowerStore is a programmable infrastructure that dramatically improves everything from application development to deployment. The offering includes VMware integration and support for orchestration frameworks including Ansible, VMware vRealize Orchestrator and Kubernetes. PowerStore’s machine-learning engine brings optimized performance and reduced cost through automation of processes such as initial volume placement and load balancing. Meanwhile, improved flexibility around deployment is enabled through Dell’s new PowerStoreOS container-based architecture.
Finalists:
Hitachi Vantara Virtual Storage Platform E990
The Virtual Storage Platform E990 expands the Hitachi Vantara portfolio and offers future-proofing through bringing all-flash NVMe enterprise storage to midrange enterprise companies. The E990 offers 100 percent data availability, low cost per IOPS and flexibility in consumption models.
IBM FlashSystem 7200
IBM’s FlashSystem 7200 allows clients to choose FlashCore Modules, industry-standard NVMe drives and/or Storage Class Memory drives to deliver massive performance—with up to 9.2 million IOPS and latency of 70 microseconds. Target customers are those needing midrange enterprise storage for AI-enhanced applications and hybrid cloud architectures that require higher levels of performance.

Storage-SMB
Winner: Dell EMC PowerVault
The Dell EMC PowerVault ME4 Series is a block storage array that delivers powerful features in a simplified, affordable offering to small and midsize businesses. The PowerVault ME4 offers easy deployment—with the ability to configure and provision the system in just 15 minutes—and numerous software capabilities such as Distributed RAID and auto-tiering. Updates to the PowerVault ME4 over its predecessor system include a 4X increase in IOPS; double the back-end connectivity; and the introduction of expanded capacity. The system is able to offer 16 TB in hard drive space with the ability to scale up to 4 PB in a 15U rack space, improving storage density by 25 percent.
Finalist:
IBM FlashSystem 5000 and 5100
Standout features of the IBM FlashSystem 5000 and 5100 include Easy Tier, which uses AI to detect storage usage patterns by workloads and automatically moves data among tiers of storage, optimizing the use of different media with differing price and performance characteristics.
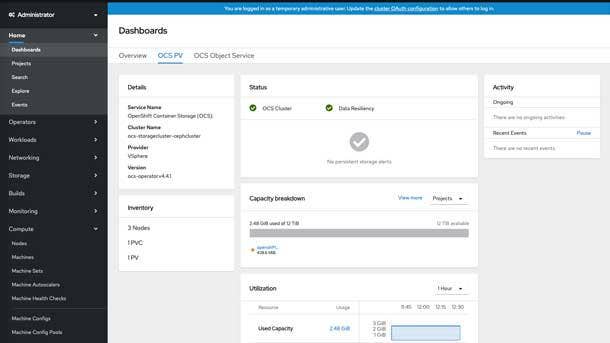
Storage-Software-Defined
Winner:
IBM Storage Suite For IBM Cloud Paks
As an all-inclusive suite of software-defined storage offerings, the IBM Storage Suite for IBM Cloud Paks covers data resources for everything from file to object to block. The suite provides an out-of-the-box storage layer for simplified setup and is highly flexible with support for Kubernetes and Red Hat OpenShift along with IBM Cloud Paks. The offering also provides strong performance at any scale—and for every workload. Ultimately, the IBM Storage Suite for IBM Cloud Paks brings increased reliability, flexibility and performance while accelerating a customer’s shift to the cloud.
Finalists:
DataCore vFilO
DataCore vFilO provides a scale-out global file system—which simplifies data access across diverse NAS appliances, file servers and object stores—through assimilating data under a global namespace. Regardless of where the data is stored, as long as it’s available under the global namespace, vFilO enables the data to be retrieved rapidly.
Lightbits LightOS 2.0
Lightbits LightOS 2.0 is a software-defined block storage offering that delivers high-performance, scale-out and redundant NVMe/TCP storage that performs like local flash. LightOS also brings features more often associated with SAN such as thin provisioning, compression and selectable redundancy levels.

Tablets
Winner:
Samsung Galaxy Tab Active Pro
With the rugged Galaxy Tab Active Pro, Samsung is doubling down on its development of business-friendly Android devices. Updates for the Galaxy Tab Active Pro include a larger display at 10.1 inches versus 8 inches on the prior model in the series, along with expanded battery life at 16 hours compared with 11 hours previously. Another new addition is support for DeX, Samsung’s feature that lets users access an Android desktop on an external screen by plugging in their Galaxy device. The Galaxy Tab Active Pro also offers useful features such as the ability to operate the tablet with gloves; strong durability and water resistance; and eFOTA (enterprise firmware over-the-air) management to ensure continuous security and control.
Finalist:
Panasonic Toughbook FZ A3
Key features of Panasonic’s Toughbook A3 include support for both 4G LTE and for FirstNet, a wireless network dedicated to first responder and public safety users. The configurability of the 10.1-inch rugged Android tablet is also notable, with options to add a 1-D/2-D barcode scanner, an insertable smart card reader and a second USB-A port.
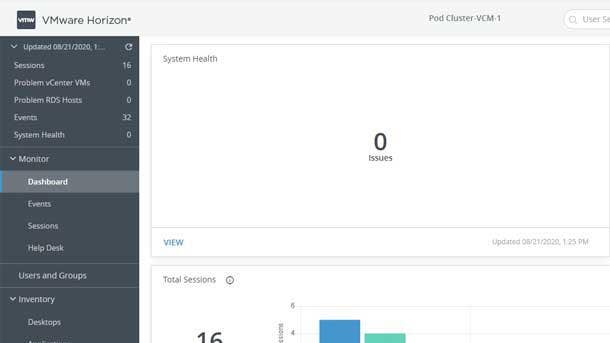
Virtual Desktop Infrastructure
Winner:
VMware Horizon 8
The surge in demand for virtual desktop infrastructure (VDI) has only accelerated the development for leading offerings in the market, such as VMware’s Horizon. With Horizon 8, VMware has rolled out a variety of new capabilities including increased deployment options for hybrid and multi-cloud environments, enabling more flexibility and choice for customers. Other enhancements in VMware Horizon 8 include the introduction of Instant Clone capabilities, which enable provisioning of instant clones without a requirement for a parent virtual machine; new RESTful APIs to assist with automating capabilities such as monitoring and management; and support for unified communications and collaboration, delivering experiences that are made for Microsoft Teams, Cisco Webex and Zoom.
Finalists:
Nerdio Manager for WVD
With Nerdio Manager for WVD, IT professionals can automatically deploy, manage and optimize Microsoft Windows Virtual Desktop environments—and do so rapidly. Nerdio Manager for WVD
can create new Windows Virtual Desktop environments or layer on top of existing WVD deployments, all without disruption or vendor lock-in.
NetApp Virtual Desktop Service
NetApp’s Virtual Desktop Service automates the deployment, management and optimization of virtual desktop infrastructure across an organization’s entire global footprint. Capabilities include automated provisioning of cloud infrastructure, session hosts and applications—slashing the time and costs of configuring workspaces.

Workspace And Collaboration Devices
Winner:
Lenovo ThinkSmart View
As the need for remote conferencing continues to soar, Lenovo’s ThinkSmart View serves as a dedicated device for Microsoft Teams calls, freeing up users’ PCs during meetings. The compact desktop device comes with an 8-inch touch screen, along with built-in speakers and microphones for participating in Teams videoconferencing and audio calls. Other key features of the ThinkSmart View include easy one-touch meeting launches, a mic mute button and Bluetooth connectivity. In addition, the device offers security protections such as a built-in camera shutter and device locking with a four-digit PIN when not in use.
Finalists:
Dell Mobile Adapter Speakerphone - MH3021P
Aimed at remote and mobile professionals, the Dell Mobile Adapter Speakerphone (MH3021P) is the world’s first USB-C multiport adapter with integrated speakerphone—providing a full connectivity and conferencing offering in a compact size. The included microphone features noise-cancellation and echo reduction, while ports include HDMI, USB-C and two USB-A ports that offer up to 10-Gbps data transfer.
IGEL UD3
The IGEL UD3 is an endpoint device that enables optimal use of virtualized and cloud workspaces, including for multimedia and unified communications. The UD3 is powered by the AMD Ryzen Embedded R1505G processor with Radeon Vega 3 Graphics—providing strong performance as well as maximized energy efficiency. In addition, UD3 security is supported through the inclusion of hardware-based protections built into the AMD processor itself.
Olea Kiosks - Irvine Temperature Screening Kiosk
With its Irvine Temperature Screening Kiosk, Olea Kiosks is aiming to enable the safe return of workers and guests to businesses. The kiosk provides temperature screening with contactless operation and fast results, and the offering uses a 22-inch Android tablet that can be repurposed for use with other applications later on.
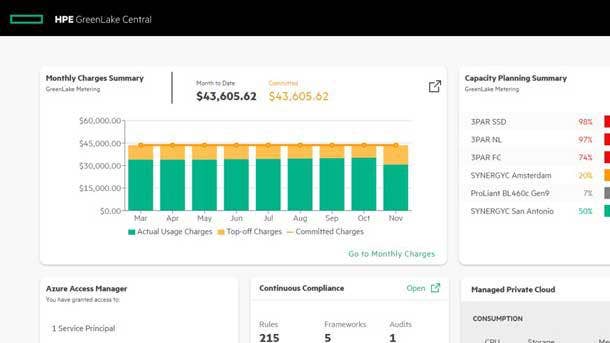
Editor’s Choice
HPE GreenLake Central
Launched into general availability earlier this year by Hewlett Packard Enterprise, GreenLake Central is HPE’s self-service portal that enables centralized management of hybrid environments. GreenLake Central empowers partners and customers to perform complex cost and compliance analysis—all across the HPE GreenLake pay-per-use private cloud, AWS, Microsoft Azure and Google Cloud. For example, a chief security officer or chief compliance officer has the ability to ensure GDPR, PCI and HIPAA compliance across environments using GreenLake Central’s compliance metrics and remediation recommendations. Meanwhile, when it comes to enabling cost control, GreenLake Central provides aggregated cost data across environments in a single-pane-of-glass management portal.

Editor’s Choice
Samsung Galaxy XCover Pro
As a smartphone designed specifically for workers, Samsung’s Galaxy XCover Pro is ruggedized for usage on the go and in the field with IP68 water and dust resistance, along with protection against drops and conditions such as high humidity and altitude. The device can be easily charged in a dock (without the need for cables) thanks to included support for pogo pin charging. The 6.3-inch phone has a 4,050 mAh battery that enables more than a day’s worth of usage, and the battery can also be replaced with a spare. Meanwhile, the phone’s display can be used with gloves—and the device also includes the new walkie talkie feature of Microsoft Teams, featuring programmable keys that enable the push-to-talk capabilities.