The 10 Hottest New Cybersecurity Products Of 2020
The 10 cybersecurity products making noise in the market have emphasized workflow automation, downtime minimization and incident remediation to better safeguard endpoints, mobile devices, OT environments and containers.

Batten Down The Hatches
Vendors have spent 2020 advancing security everywhere from endpoints and mobile devices to OT environments and containers, debuting tools that bring SD-WAN to challenging operational environments or uncontrolled remote locations, protect inbound, outbound and east-west traffic between container trust zones, and safeguard users against unsuitable and malicious web content.
Enhancements to security operations and intelligence have been a major area of focus thus far in 2020, with advancements around automating workflows to speed detection and response, minimizing downtime and restoring business operations, and swiftly detecting and thwarting cyberattacks anywhere on the user’s network.
Seven of the 10 hottest cybersecurity products of 2020 came from companies based in California, two came from companies based in other parts of the United States, and one came from a company based abroad. Read on to learn how suppliers have gone about making their cybersecurity portfolio even more solution provider friendly.

Check Point Infinity SOC
Check Point Infinity SOC was launched in July to unify threat prevention, detection, investigation and remediation in a single platform and give customers security and operational efficiency. It uses AI-based incident analysis to filter millions of irrelevant logs and alerts, helping enterprise security teams expose and shut down cyber attacks with speed and precision.
The product automatically triages alerts to enable quicker response to critical attacks and offers single click remediation with a lightweight client on the infected host. Infinity SOC also prevents hackers from launching phishing campaigns against users by taking down lookalike corporate web and email domains.
Infinity SOC enables teams to quickly search for in-depth intelligence on any indicator of compromise, including global spread, attack timelines and patterns, malware DNA and deep-link searches on social media. The product can be deployed in minutes and avoids costly log storage and privacy concerns with a unique cloud-based event analysis that does not export and store event logs.
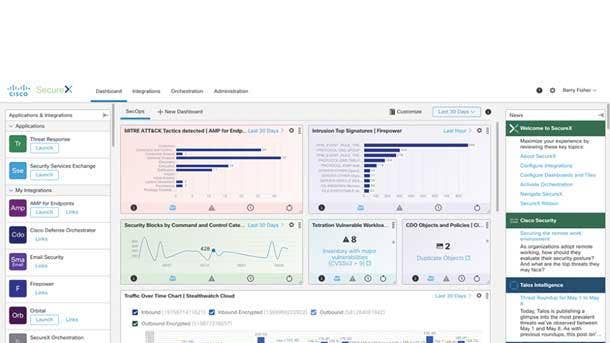
Cisco SecureX
Cisco SecureX was announced in February to provide more visibility across the entire security portfolio, delivering security analytics and automating workflows to speed threat detection and response. The platform unifies visibility across customers’ security portfolio in a cloud-native platform, delivering detection of unknown threats and policy violations via security analytics for more informed actions.
The platform automates common security workflows, including threat investigation and remediation, for more precise and efficient operations, according to Cisco. Cisco SecureX analyzes events and data across the enterprise, including from more than 150 million endpoints as well as network traffic from switches and routers, public clouds and private data center environments.
Within minutes, Cisco SecureX can identify who and what has been targeted and enable remediation using data enrichment across security products and threat intelligence feeds. The company said its new platform also brings the power of Cisco Talos threat analysts into the customer’s SOC to hunt for the latest threats.

CrowdStrike Endpoint Recovery Services
CrowdStrike Endpoint Recovery Services debuted in February and combines the power of the CrowdStrike Falcon platform, threat intelligence and real-time response to accelerate business recovery from cyber intrusions, the company said. The new service enables customers to rapidly mitigate security incidents and resume business operations with minimal interruptions, according to CrowdStrike.
CrowdStrike said Endpoint Recovery Services accelerates the standard life cycle of incident recovery, saving businesses from expensive downtime. Endpoint Recovery Services combines CrowdStrike Falcon, endpoint visibility from Threat Graph and experienced security analysts to ensure immediate attack disruption and comprehensive endpoint remediation, according to the company.
Endpoint Recovery Services stops attacks to minimize downtime and restores business operations without having to reimage or reissue endpoint devices, enabling customers to focus on recovering other critical business components. The initial phases of the service are focused on understanding the incident and deploying the Falcon platform without the need for on-premises visits or installations.

Cybereason XDR
Cybereason XDR launched in November and fuses endpoint telemetry with behavioral analytics to empower global enterprises to swiftly detect and thwart cyberattacks anywhere on their networks. The product makes it possible for defenders to pinpoint, understand and end any malicious operations across the entire IT stack regardless of if it’s on premises, mobile or in the cloud.
The product automatically surfaces anomalous network behavior and makes it easy to understand the full story behind any incident by tracking, analyzing and remediating every single action the attacker takes. Cybereason XDR correlates all attack activity and presents the intelligence as an intuitive malicious operations visualization that significantly decreases investigation and remediation periods.
Cybereason XDR recognizes the most subtle signs of compromise derived from across the whole of an organization’s network and delivers enhanced correlations across both Indicators of Compromise and Indicators of Behavior. The product also reduces mean time to respond with automated and guided one-click mitigation from a single console across all networks without the need to craft complex queries.

FireEye Mandiant Advantage: Threat Intelligence
FireEye’s Mandiant Advantage: Threat Intelligence combines Mandiant’s threat intelligence with data from the frontlines of its cyber incident response engagements, delivered via a management platform. With more than 300 intelligence analysts and researchers, and more than 200,000 hours in 2019 responding to breaches, Mandiant has unparalleled knowledge about attackers and the latest threats.
The SaaS offering debuted in October, and makes it possible for security defenders to access Mandiant’s insights faster and in ways never shared before. By extending their visibility into what’s happening across multiple Mandiant frontlines, customers can more easily prioritize the threats that matter to them most right now.
The company plans to introduce other Mandiant Advantage offerings to augment and automate global security teams with controls-agnostic, actionable breach, adversary, operational and machine intelligence data. Planned upcoming Mandiant Advantage offerings include Validation On Demand and Malware Analysis as a Service.

Fortinet FortiGate Rugged 60F
Fortinet in December introduced two new ruggedized products to its FortiGate 60 next-generation firewall for SD-WAN series -- the FortiGate Rugged 60F and FortiGate Rugged 60F with built-in LTE. The two appliances are intended to add integrated, advanced security and SD-WAN to operational technology (OT) networks in any location.
The two latest firewalls will let companies and partners bring SD-WAN to challenging operational environments or remote locations that aren’t controlled, accounting for factors such as ranging temperatures and vibrations or movement that can wreak havoc on IT gear that isn’t ruggedized. It works in the harshest of environments including oil rigs, electrical substations, and manufacturing floors.
The FortiGate Rugged 60F is designed for smaller OT sites and settings that require different mounting and power options than found in traditional IT wiring closets, Fortinet said. The FortiGate Rugged 60F with built-in LTE lets customers harness 3G and 4G cellular connectivity as an option. Once 5G is widely-available, Fortinet is planning another product to include this new form of cellular data connection.

McAfee MVision XDR
McAfee MVision XDR was unveiled in October and offers cloud-based advanced threat management with coverage across the attack lifecycle, prioritization to protect what matters, easy orchestration and efficient response. MVISION XDR improves security operations centers’ effectiveness with quick risk mitigation and delivers total cost of ownership for threat response with proactive threat analytics.
The product helps organizations proactively act on external threats that matter by allowing them to prioritize threats, predict if countermeasures will work and prescribe corrective actions. MVision XDR’s unified visibility and control across the endpoint, network and cloud makes it possible for analysts of any experience level to speed threat triage with their choice of automatic or AI-guided investigations.
MVision XDR’s unique data awareness allows for automatic prioritization of threats based on the risk and impact to the organization, with incidents assessed based on user, data classification, device, vulnerability and threat intelligence. The open and cloud-delivered security platform also simplifies integrations with external threat intelligence as well as existing SOC tools like ticketing systems.

Palo Alto Networks CN-Series
The Palo Alto Networks CN-Series debuted in June as a containerized version of the company’s firewall that was unveiled in June to help network security teams ensure they’re compliant in container environments, and enable security at DevOps speed by speeding up the integration and provisioning process, according to the company.
Kubernetes is red hot right now, and Palo Alto Networks wanted a containerized form factor as part of their firewall to ensure both security and compliance. The CN-Series firewalls leverage deep container context to protect inbound, outbound and east-west traffic between container trust zones along with other components of enterprise IT environments, according to Palo Alto Networks.
The CN-Series can be used to protect critical applications against known vulnerabilities as well as both known and unknown malware until patches can be applied to secure the underlying compute resource. Applications are protected with the CN-Series in on-premise data centers like Kubernetes and RedHat OpenShift as well as the Kubernetes service from each of the big public cloud providers, the firm said.
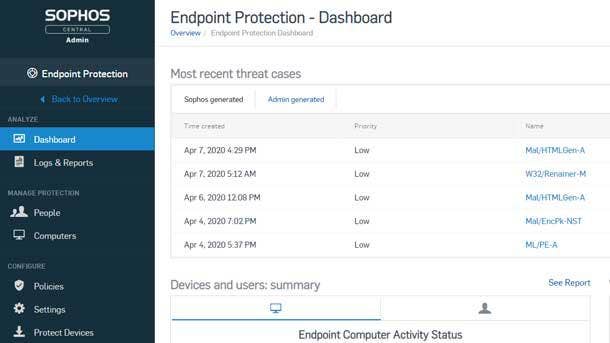
Sophos Intercept X For Mobile
Sophos in January began protecting Chrome OS users against unsuitable and malicious web content for the first time with its rebranded Intercept X for Mobile offering. The new mobile security capabilities will address the huge explosion of Chromebooks in the education space and the emerging opportunity in the health care and general corporate spaces as the devices move upmarket and become more feature-rich.
Intercept X for Mobile can now determine if apps installed by students or teachers on Chrome OS devices have malicious intent or operate unethically through tactics such as “fleeceware,” according to Sophos. Fleeceware excels at exploiting loopholes in the rules of Apple’s App Store or Google Play to evade detection but behave in an unethical or deceptive manner.
Intercept X for Mobile scours App Store libraries to identify malicious activity, the company said, looking for apps that have been side-loaded onto a mobile device or smartphones that have been jailbroken to install an application. As hackers adapt new techniques in the mobile space to evade detection, Sophos said it is employing machine learning to identify things the company has never seen before.

Tanium Risk
Tanium Risk was announced in November to give customers insight into how their endpoints are operating by providing them with a score that contextualizes how secure the company’s IT assets are. The tool will allow organizations to adjust their risk score by noting issues they don’t feel are worth the cost of remediating such as vulnerabilities behind a patched firewall.
Tanium has unique insight into everything that’s happening on the endpoint such as how many unpatched assets exist and where vulnerabilities are. Businesses have often overlooked unmanaged machines such as IoT devices – which can compromise 15-to-20 percent of all IT assets – since they’re not under the purview of patch management tools, which Tanium said introduces risk.
Down the road, Tanium hopes to be able to compare an organization’s risk score with that of peers who have a similar vertical focus or company size. The risk score has key metrics across operational, security and regulatory domains to assess business continuity, and also examines endpoint configuration and vulnerabilities as well as the mapping of technical controls to desired cybersecurity frameworks.